What's new arround internet
| Src | Date (GMT) | Titre | Description | Tags | Stories | Notes |
| 2021-06-08 20:14:43 | DOJ Recovers $2.3M in Bitcoin Ransom Paid by Colonial Pipeline (lien direct) |
 Investigators recovered $2.3 million in bitcoin paid by the Colonial Pipeline Company to DarkSide following a ransomware attack in early May. On June 7, the Department of Justice (DOJ) revealed that law enforcement agencies had been tracking transfers of bitcoin when they spotted the movement of 63.7 bitcoins associated with the Colonial Pipeline Company's ransom payment.
Investigators recovered $2.3 million in bitcoin paid by the Colonial Pipeline Company to DarkSide following a ransomware attack in early May. On June 7, the Department of Justice (DOJ) revealed that law enforcement agencies had been tracking transfers of bitcoin when they spotted the movement of 63.7 bitcoins associated with the Colonial Pipeline Company's ransom payment. |
||||
| 2021-06-08 18:47:33 | Webinar: Live Ransomware Attack Simulation (lien direct) |
 If you're concerned about ransomware, whether it's beating REvil or DarkSide, stopping data exfiltration, or preventing the latest trend of double extortion, this session is for you!
Join us for a live ransomware attack simulation, where we'll discuss the latest attack trends, walk through a multi-stage ransomware attack.
If you're concerned about ransomware, whether it's beating REvil or DarkSide, stopping data exfiltration, or preventing the latest trend of double extortion, this session is for you!
Join us for a live ransomware attack simulation, where we'll discuss the latest attack trends, walk through a multi-stage ransomware attack. |
Ransomware | |||
| 2021-06-08 13:25:12 | Malicious Life Podcast: Inside the DarkSide Colonial Pipeline Attack (lien direct) |
 On Friday, May 7th, 2021, Colonial Pipeline suffered a cyberattack that forced the company to shut down its operations. As a result, gasoline outages were reported across the U.S. East Coast.
On Friday, May 7th, 2021, Colonial Pipeline suffered a cyberattack that forced the company to shut down its operations. As a result, gasoline outages were reported across the U.S. East Coast. |
||||
| 2021-06-07 12:14:36 | Market Drivers for XDR and MSSP Service Opportunities (lien direct) |
 In my last article, we looked at how to define Extended Detection and Response (XDR) solutions from an MSSP perspective and where it fits in as part of an overall Managed Detection and Response (MDR) service offering.
In my last article, we looked at how to define Extended Detection and Response (XDR) solutions from an MSSP perspective and where it fits in as part of an overall Managed Detection and Response (MDR) service offering. |
||||
| 2021-06-03 12:56:16 | CISO Stories Podcast: CISOs Cross the Bridge to the Cloud (lien direct) |
 Today, most organizations have moved some or all of their workloads to the cloud.This migration provides opportunities of scale, flexibility and speed, but the data moves further away from the physical control of the organization.
Today, most organizations have moved some or all of their workloads to the cloud.This migration provides opportunities of scale, flexibility and speed, but the data moves further away from the physical control of the organization. |
||||
| 2021-06-02 18:46:55 | Cybereason vs. REvil Ransomware (lien direct) |
 According to reports, meatpacking giant JBS was hit with a serious attack reportedly involving REvil ransomware, shutting down a good portion of the company's production capabilities and threatening to create supply chain disruptions and sharp cost of goods increases.
According to reports, meatpacking giant JBS was hit with a serious attack reportedly involving REvil ransomware, shutting down a good portion of the company's production capabilities and threatening to create supply chain disruptions and sharp cost of goods increases. |
Ransomware | |||
| 2021-06-02 12:01:43 | Cybereason Joins with MITRE Engenuity\'s Center for Threat-Informed Defense (lien direct) |
 Cybereason is excited to announce that it is now a research sponsor of the Center for Threat-Informed Defense, allowing collaboration on applied research and development to improve cyber defenses at scale for the global security community.
Cybereason is excited to announce that it is now a research sponsor of the Center for Threat-Informed Defense, allowing collaboration on applied research and development to improve cyber defenses at scale for the global security community. |
||||
| 2021-06-01 16:53:30 | SolarWinds Threat Actors Behind New Email Attack Campaign (lien direct) |
 The threat actors behind last year's SolarWinds supply chain attack have launched a new email attack campaign aimed at organizations around the world. This attack wave attracted the attention of the Microsoft Threat Intelligence Center (MSTIC) on May 25.
The threat actors behind last year's SolarWinds supply chain attack have launched a new email attack campaign aimed at organizations around the world. This attack wave attracted the attention of the Microsoft Threat Intelligence Center (MSTIC) on May 25. |
Threat | |||
| 2021-06-01 12:51:20 | The Line in the Sand: How We Respond Today Impacts Our Security Tomorrow (lien direct) |
 In the past few months, we've faced massive attacks with SolarWinds and the HAFNIUM attacks targeting Microsoft Exchange, followed by the unprecedented ransomware attack by DarkSide that crippled US critical infrastructure. It is time to ask ourselves again, what is really going on? More importantly, the time has come for the United States government to do some soul searching on why defenses have failed and how we can prevent similar attacks in the future.
In the past few months, we've faced massive attacks with SolarWinds and the HAFNIUM attacks targeting Microsoft Exchange, followed by the unprecedented ransomware attack by DarkSide that crippled US critical infrastructure. It is time to ask ourselves again, what is really going on? More importantly, the time has come for the United States government to do some soul searching on why defenses have failed and how we can prevent similar attacks in the future. |
Ransomware | |||
| 2021-06-01 12:13:07 | Malicious Life Podcast: China\'s Unrestricted Cyberwarfare Part 2 (lien direct) |
 In China's Unrestricted Cyberwarfare Part 1 we explored the story of two Chinese military officers, veterans of the semi-conflict with Taiwan, who helped shape the role of cyber in modern warfare in China and beyond with special guest Lieutenant Colonel, USMC (retired) Bill Hagestad, a leading international authority on cyberwarfare and Chinese cyber operations and capabilities specifically.
In China's Unrestricted Cyberwarfare Part 1 we explored the story of two Chinese military officers, veterans of the semi-conflict with Taiwan, who helped shape the role of cyber in modern warfare in China and beyond with special guest Lieutenant Colonel, USMC (retired) Bill Hagestad, a leading international authority on cyberwarfare and Chinese cyber operations and capabilities specifically. |
Guideline | |||
| 2021-05-27 12:51:11 | XDR: Moving Beyond the Limits of SIEM and SOAR (lien direct) |
 Organizations around the world are under siege from cyberattacks, and they need tools that can protect against malware, exploits, and increasingly sophisticated attacks on both devices and users. SIEM, SOAR and EDR technologies all have their benefits, but organizations with mature security programs are looking to move beyond the limits of these offerings - that's where the advent of XDR comes into play.
Organizations around the world are under siege from cyberattacks, and they need tools that can protect against malware, exploits, and increasingly sophisticated attacks on both devices and users. SIEM, SOAR and EDR technologies all have their benefits, but organizations with mature security programs are looking to move beyond the limits of these offerings - that's where the advent of XDR comes into play. |
||||
| 2021-05-26 12:52:12 | Ransomware Trends: Six Notable Ransomware Attacks from 2021 (lien direct) |
 The security community witnessed triple-digit growth in the number of publicly disclosed ransomware incidents in 2020. As noted in a previous blog post on Five Things You Need to Know About Ransomware Attacks, ransomware attacks grew 715% in H1 2020 compared to the first half of the previous year. Ransomware incidents for 2020 overall increased by more than 150%.
The security community witnessed triple-digit growth in the number of publicly disclosed ransomware incidents in 2020. As noted in a previous blog post on Five Things You Need to Know About Ransomware Attacks, ransomware attacks grew 715% in H1 2020 compared to the first half of the previous year. Ransomware incidents for 2020 overall increased by more than 150%. |
Ransomware | |||
| 2021-05-25 13:19:15 | Cybereason Makes Big Debut on CNBC 2021 Disruptor 50 List (lien direct) |
 The Cybereason team is thrilled to have been named to the CNBC 2021 Disruptor 50 list of the most disruptive privately-held global companies. Cybereason debuted in the #32 spot and is one of only two cybersecurity companies on the list. Cybereason was chosen from a record number of nearly 1,600 nominations.
The Cybereason team is thrilled to have been named to the CNBC 2021 Disruptor 50 list of the most disruptive privately-held global companies. Cybereason debuted in the #32 spot and is one of only two cybersecurity companies on the list. Cybereason was chosen from a record number of nearly 1,600 nominations. |
||||
| 2021-05-25 12:29:32 | CISO Stories Podcast: Five Critical Elements for Protecting the Right Assets (lien direct) |
 We have limited investment dollars and therefore must ensure we are protecting the right assets. The practical side of determining “what” needs to be protected and “how” is a convoluted maze of academics, taxonomies, frameworks, and inconsistent approaches.
We have limited investment dollars and therefore must ensure we are protecting the right assets. The practical side of determining “what” needs to be protected and “how” is a convoluted maze of academics, taxonomies, frameworks, and inconsistent approaches. |
||||
| 2021-05-25 12:23:45 | New Cybersecurity Executive Order: Will It Have Impact? (lien direct) |
 The state of the threat landscape in general, and incidents like the recent ransomware attack against Colonial Pipeline demand that we take immediate action to improve cybersecurity defenses. The recent executive order (EO) on cybersecurity from President Biden is a bold step in the right direction.
The state of the threat landscape in general, and incidents like the recent ransomware attack against Colonial Pipeline demand that we take immediate action to improve cybersecurity defenses. The recent executive order (EO) on cybersecurity from President Biden is a bold step in the right direction. |
Threat | |||
| 2021-05-24 20:59:01 | Record Setting $40M Ransom Paid to Attackers (lien direct) |
 CNA, one of the largest U.S. commercial and casualty insurance companies, reportedly met a $40 million ransom demand after suffering a ransomware infection earlier in the year. As of this writing, that's the largest ransom demand ever reported to have been paid by a company following a ransomware attack.
CNA, one of the largest U.S. commercial and casualty insurance companies, reportedly met a $40 million ransom demand after suffering a ransomware infection earlier in the year. As of this writing, that's the largest ransom demand ever reported to have been paid by a company following a ransomware attack. |
Ransomware | |||
| 2021-05-24 12:03:41 | (Déjà vu) Malicious Life Podcast: The Untold Story of the RSA Breach Part 2 (lien direct) |
 In March of 2011, security vendor RSA was the target of an attack that compromised sensitive data related to the company's flagship SecureID product, a solution that was in-use by thousands of high-profile clients around the world including the U.S. government and an array of U.S. defense contractors.
The company's leadership knew they had been breached in a sophisticated APT-style attack, but it was unknown whether the attackers had gained access to the cryptographic keys needed to decrypt sensitive client data.
In this second episode (listen to Part 1 here) of the Malicious Life Podcast, host Ran Levy is joined by two former RSA executives who were integral to the company's incident response at the time of the attacks and only recently were released from a 10-year NDA that barred them from discussing the incident.
For the first time, they elaborate in detail on how the events unfolded and share the untold story behind one of the most impactful attacks of all time - check it out...
In March of 2011, security vendor RSA was the target of an attack that compromised sensitive data related to the company's flagship SecureID product, a solution that was in-use by thousands of high-profile clients around the world including the U.S. government and an array of U.S. defense contractors.
The company's leadership knew they had been breached in a sophisticated APT-style attack, but it was unknown whether the attackers had gained access to the cryptographic keys needed to decrypt sensitive client data.
In this second episode (listen to Part 1 here) of the Malicious Life Podcast, host Ran Levy is joined by two former RSA executives who were integral to the company's incident response at the time of the attacks and only recently were released from a 10-year NDA that barred them from discussing the incident.
For the first time, they elaborate in detail on how the events unfolded and share the untold story behind one of the most impactful attacks of all time - check it out... |
Guideline | |||
| 2021-05-21 13:02:13 | Webinar: XDR or EDR: How Should Your SOC Choose? (lien direct) |
 If you have doubts in your organisation's ability to identify and defeat modern attackers, you're not alone. We're living in a world where IT infrastructure, attacker trends, and workspace norms are constantly shifting, so it's especially challenging to build a solid security foundation with tested best practices.
Companies are struggling to prove effective cybersecurity due to a lack of visibility, a shortage of skilled staff, and challenges matching today's accelerated business pace.
If you have doubts in your organisation's ability to identify and defeat modern attackers, you're not alone. We're living in a world where IT infrastructure, attacker trends, and workspace norms are constantly shifting, so it's especially challenging to build a solid security foundation with tested best practices.
Companies are struggling to prove effective cybersecurity due to a lack of visibility, a shortage of skilled staff, and challenges matching today's accelerated business pace. |
||||
| 2021-05-20 10:07:14 | Malicious Life Podcast: The Untold Story of the RSA Breach Part 1 (lien direct) |
 In March of 2011, security vendor RSA was the target of an attack that compromised sensitive data related to the company's flagship SecureID product. The solution was in-use by thousands of high-profile clients around the world, including the U.S. government and an array of U.S. defense contractors.
The company's leadership knew they had been breached in a sophisticated APT-style attack, but it was unknown whether the attackers had gained access to the cryptographic keys needed to decrypt sensitive client data.
In this special episode of the Malicious Life Podcast, host Ran Levy is joined by two former RSA executives who were integral to the company's incident response at the time of the attacks and only recently were released from a 10-year NDA that barred them from discussing the incident. For the first time, they elaborate in detail on how the events unfolded and share the untold story behind one of the most impactful attacks of all time.
Ran also talks with Wired Magazine's Andy Greenberg who provides some context on why the RSA breach was such a watershed moment for the security industry. Check out Andy's deep dive on the RSA breach with additional interviews, including thoughts from former RSA CEO Art Coviello.
In March of 2011, security vendor RSA was the target of an attack that compromised sensitive data related to the company's flagship SecureID product. The solution was in-use by thousands of high-profile clients around the world, including the U.S. government and an array of U.S. defense contractors.
The company's leadership knew they had been breached in a sophisticated APT-style attack, but it was unknown whether the attackers had gained access to the cryptographic keys needed to decrypt sensitive client data.
In this special episode of the Malicious Life Podcast, host Ran Levy is joined by two former RSA executives who were integral to the company's incident response at the time of the attacks and only recently were released from a 10-year NDA that barred them from discussing the incident. For the first time, they elaborate in detail on how the events unfolded and share the untold story behind one of the most impactful attacks of all time.
Ran also talks with Wired Magazine's Andy Greenberg who provides some context on why the RSA breach was such a watershed moment for the security industry. Check out Andy's deep dive on the RSA breach with additional interviews, including thoughts from former RSA CEO Art Coviello. |
Guideline | |||
| 2021-05-19 14:49:53 | Cybereason Experts Take Center Stage at RSA Conference 2021 (lien direct) |
 Cybereason is excited to announce that Chief Information Security Officer Israel Barak and Principal Security Advocate Lodrina Cherne are taking center stage at the RSA Conference on Thursday, May 21, in two speaking sessions.
Cybereason is excited to announce that Chief Information Security Officer Israel Barak and Principal Security Advocate Lodrina Cherne are taking center stage at the RSA Conference on Thursday, May 21, in two speaking sessions. |
||||
| 2021-05-19 13:52:17 | SC Awards Europe: Cybereason Named Finalist for Best Endpoint Security (lien direct) |
 Cybereason is excited to announce it was named a finalist in the Best Endpoint Security category of the 2021 SC Awards Europe competition. Winners will be announced June 8, 2021. Earlier this year, Cybereason was named a finalist for Best Enterprise Security product with SC Awards U.S.
Cybereason is excited to announce it was named a finalist in the Best Endpoint Security category of the 2021 SC Awards Europe competition. Winners will be announced June 8, 2021. Earlier this year, Cybereason was named a finalist for Best Enterprise Security product with SC Awards U.S. |
||||
| 2021-05-19 12:44:56 | Evaluating XDR Against EDR, SIEM and SOAR Solutions (lien direct) |
 XDR, shorthand for the emerging Extended Detection and Response solution offerings, has quickly established itself as one of the best options for defending the modern enterprise IT infrastructure against cyberattacks. But many are still trying to wrap their minds around XDR and where exactly it fits compared to other established solutions like SIEM, SOAR, and EDR.
XDR, shorthand for the emerging Extended Detection and Response solution offerings, has quickly established itself as one of the best options for defending the modern enterprise IT infrastructure against cyberattacks. But many are still trying to wrap their minds around XDR and where exactly it fits compared to other established solutions like SIEM, SOAR, and EDR. |
||||
| 2021-05-18 12:46:12 | Unpacking the Gartner Critical Capabilities Research (lien direct) |
 The importance of third-party research and testing cannot be overstated in the current security marketscape. Important details for consideration when evaluating a solution to onboard for detection and response can be obscure and difficult to clearly understand. Vendors will always position themselves in as positive of a light as possible, which can lead to frustration and head-scratching during the evaluation process.
The importance of third-party research and testing cannot be overstated in the current security marketscape. Important details for consideration when evaluating a solution to onboard for detection and response can be obscure and difficult to clearly understand. Vendors will always position themselves in as positive of a light as possible, which can lead to frustration and head-scratching during the evaluation process. |
Guideline | |||
| 2021-05-18 12:42:37 | CISO Stories Podcast: Passion for Solving Problems is Key to Security (lien direct) |
 Will Lin, founding team member at ForgePoint Capital and co-creator of the CISO community Security Tinkerers, discusses his passion for technology and how it led him to a career helping security companies launch, as well as his work supporting CISOs through collaboration and knowledge sharing - check it out...
Will Lin, founding team member at ForgePoint Capital and co-creator of the CISO community Security Tinkerers, discusses his passion for technology and how it led him to a career helping security companies launch, as well as his work supporting CISOs through collaboration and knowledge sharing - check it out... |
||||
| 2021-05-17 13:48:43 | DarkSide Gang and the New Golden Age of Piracy (lien direct) |
 Late on Friday May 7, 2021, Colonial Pipeline, the company that runs the largest gasoline pipeline in the US, shut down operations following a ransomware attack on their systems. It later emerged that a relatively new ransomware-as-a-service criminal organization known as DarkSide was behind the attack - but there was a twist.
Late on Friday May 7, 2021, Colonial Pipeline, the company that runs the largest gasoline pipeline in the US, shut down operations following a ransomware attack on their systems. It later emerged that a relatively new ransomware-as-a-service criminal organization known as DarkSide was behind the attack - but there was a twist. |
Ransomware | |||
| 2021-05-14 20:21:22 | Solving the Ransomware Crisis (lien direct) |
 Ransomware attacks are trivial to execute and there is little, if any, risk and no penalties for the attackers. As a victim, there are no good choices once an organization is hit by ransomware. You can ignore the ransom demand and restore your data from backups and take your chances with the risk of data exposure. At the same time, the reality is that it doesn't pay to pay--it is not a guarantee that you will get all of the data back in a usable state.
In addition, when you pay the ransom you are essentially funding these criminals who are acting as terrorists. The chances are that you are funding additional research and development of the next exploit or ransomware variant, so paying the ransom just makes the problem bigger.
Organizations that pay the ransom also risk putting a bullseye on their backs-making themselves attractive targets for future ransomware attacks because they have established that they're willing to pay. The only good option is to avoid having your data stolen or encrypted in the first place, which is why it needs to be a global priority to solve this crisis.
Ransomware attacks are trivial to execute and there is little, if any, risk and no penalties for the attackers. As a victim, there are no good choices once an organization is hit by ransomware. You can ignore the ransom demand and restore your data from backups and take your chances with the risk of data exposure. At the same time, the reality is that it doesn't pay to pay--it is not a guarantee that you will get all of the data back in a usable state.
In addition, when you pay the ransom you are essentially funding these criminals who are acting as terrorists. The chances are that you are funding additional research and development of the next exploit or ransomware variant, so paying the ransom just makes the problem bigger.
Organizations that pay the ransom also risk putting a bullseye on their backs-making themselves attractive targets for future ransomware attacks because they have established that they're willing to pay. The only good option is to avoid having your data stolen or encrypted in the first place, which is why it needs to be a global priority to solve this crisis. |
Ransomware | |||
| 2021-05-14 18:46:10 | Webinar: Future-Proofing Security Programs in 2021 and Beyond (lien direct) |
 2020 was a year of learning, with surges in ransomware, nation states infecting supply chains from Solar Winds to Microsoft, and radical new work models that might presage a “new normal.”
2020 was a year of learning, with surges in ransomware, nation states infecting supply chains from Solar Winds to Microsoft, and radical new work models that might presage a “new normal.” |
||||
| 2021-05-13 13:27:11 | CISO Stories Podcast: Effective Health Care Security is More Than HIPAA (lien direct) |
 Healthcare security today is extremely complex due to the integrated clinical systems and connected community networks. As well, no longer are the medical records stored with a single provider.
Healthcare security today is extremely complex due to the integrated clinical systems and connected community networks. As well, no longer are the medical records stored with a single provider. |
||||
| 2021-05-12 13:27:30 | Ransomware Attacks are Evolving – Is Your SOC Ready? (lien direct) |
 Ransomware actors are known to innovate on a regular basis, and these past few years have seen an acceleration in the evolution of tactics and techniques designed to make the attacks more effective.
Ransomware actors are known to innovate on a regular basis, and these past few years have seen an acceleration in the evolution of tactics and techniques designed to make the attacks more effective. |
||||
| 2021-05-11 22:19:35 | Webinar: Cybereason vs. DarkSide Ransomware (lien direct) |
 Colonial Pipeline was recently the victim of a devastating attack that shut down U.S. operations across the East Coast, threatening an already tenuous economic recovery effort. This attack against critical infrastructure by the DarkSide Ransomware gang highlights the urgent need for better ransomware prevention, detection and response.
Colonial Pipeline was recently the victim of a devastating attack that shut down U.S. operations across the East Coast, threatening an already tenuous economic recovery effort. This attack against critical infrastructure by the DarkSide Ransomware gang highlights the urgent need for better ransomware prevention, detection and response. |
Ransomware | |||
| 2021-05-11 13:35:53 | Malicious Life Podcast: Creating BSides - A Grassroots Security Conference (lien direct) |
 Security BSides - or just 'BSides' for those in the know - is the first grassroots, DIY, open security conference in the world, and has grown to more than 650 events in more than 50 countries.
Security BSides - or just 'BSides' for those in the know - is the first grassroots, DIY, open security conference in the world, and has grown to more than 650 events in more than 50 countries. |
||||
| 2021-05-10 19:57:09 | Inside the DarkSide Ransomware Attack on Colonial Pipeline (lien direct) |
 On May 8, the Colonial Pipeline Company announced that it had fallen victim to a ransomware attack a day earlier. The pipeline operations include transporting 100 million gallons of fuel daily to meet the needs of consumers across the entire eastern seaboard of the U.S. from Texas to New York, according to the website of the refined products pipeline company.
On May 8, the Colonial Pipeline Company announced that it had fallen victim to a ransomware attack a day earlier. The pipeline operations include transporting 100 million gallons of fuel daily to meet the needs of consumers across the entire eastern seaboard of the U.S. from Texas to New York, according to the website of the refined products pipeline company. |
Ransomware | |||
| 2021-05-10 13:05:02 | Defining XDR from an MSSP Perspective (lien direct) |
 If you're not entirely clear on what Extended Detection and Response (XDR) is, you wouldn't be alone. Most understand it as the evolution of Endpoint Detection and Response (EDR) that covers the areas of the attack surface beyond the endpoint, including assets like cloud workloads, containers, and user identities.
If you're not entirely clear on what Extended Detection and Response (XDR) is, you wouldn't be alone. Most understand it as the evolution of Endpoint Detection and Response (EDR) that covers the areas of the attack surface beyond the endpoint, including assets like cloud workloads, containers, and user identities. |
||||
| 2021-05-06 15:18:49 | The Cybereason Advantage: Why Cybereason Was Named A Visionary in the 2021 Gartner Magic Quadrant for EPP (lien direct) |
 The Cybereason team is excited to announce that Gartner has named Cybereason a Visionary in the 2021 Gartner Magic Quadrant for Endpoint Protection Platforms. This is Cybereason's first recognition in this influential industry report, and we believe our placement in the Visionary Quadrant is because of the value and future-readiness of the Cybereason Defense Platform and the superior endpoint protection (EPP) and extended detection and response (XDR) functionality that it delivers.
The Cybereason team is excited to announce that Gartner has named Cybereason a Visionary in the 2021 Gartner Magic Quadrant for Endpoint Protection Platforms. This is Cybereason's first recognition in this influential industry report, and we believe our placement in the Visionary Quadrant is because of the value and future-readiness of the Cybereason Defense Platform and the superior endpoint protection (EPP) and extended detection and response (XDR) functionality that it delivers. |
||||
| 2021-05-06 13:22:43 | CISO Stories Podcast: Stop Reporting Useless Security Metrics! (lien direct) |
 All disciplines need to be able to demonstrate added value and track the ability to improve upon current practices. The board, technical management, auditors, and engineers may each need a different view of the security initiatives performed.
All disciplines need to be able to demonstrate added value and track the ability to improve upon current practices. The board, technical management, auditors, and engineers may each need a different view of the security initiatives performed. |
||||
| 2021-05-05 13:10:23 | Three Keys to a Reliable Ransomware Defense Strategy (lien direct) |
 As we noted in a previous blog post, ransomware attacks are becoming more frequent and more costly. Reports reveal that there were 304 million ransomware attacks in 2020 - 62% more than the total number of ransomware attacks for 2019. The estimated cost of those incidents increased from $11.5 billion to $20 billion during that same time period. Average ransom costs also rose from $5,900 to $8,100 between those two years, with associated downtime losses growing from $141,000 to $283,000.
As we noted in a previous blog post, ransomware attacks are becoming more frequent and more costly. Reports reveal that there were 304 million ransomware attacks in 2020 - 62% more than the total number of ransomware attacks for 2019. The estimated cost of those incidents increased from $11.5 billion to $20 billion during that same time period. Average ransom costs also rose from $5,900 to $8,100 between those two years, with associated downtime losses growing from $141,000 to $283,000. |
Ransomware | |||
| 2021-05-04 12:05:16 | Malicious Life Podcast: China\'s Unrestricted Cyberwarfare Part 1 (lien direct) |
 Back in the 1990s, cyberwarfare was a word rarely used in the West - and definitely unheard of in China, which was just taking its first steps on the Internet. Two Chinese military officers, veterans of the semi-conflict with Taiwan, helped shape the role of cyber in modern warfare in China and beyond.
Back in the 1990s, cyberwarfare was a word rarely used in the West - and definitely unheard of in China, which was just taking its first steps on the Internet. Two Chinese military officers, veterans of the semi-conflict with Taiwan, helped shape the role of cyber in modern warfare in China and beyond. |
||||
| 2021-05-03 12:58:32 | Securing the Financial Sector Now and Into the Future with XDR (lien direct) |
 Figuring out if your organization is under attack is typically a time-consuming, labor-intensive affair. Analysts must gather data across multiple security tools and perform careful analysis, a process that can take hours, days, or weeks. Unfortunately, time is the most precious resource when responding to incidents. The longer adversaries linger in an IT environment, the longer they have to deploy footholds, move to other machines, and access more data.
Figuring out if your organization is under attack is typically a time-consuming, labor-intensive affair. Analysts must gather data across multiple security tools and perform careful analysis, a process that can take hours, days, or weeks. Unfortunately, time is the most precious resource when responding to incidents. The longer adversaries linger in an IT environment, the longer they have to deploy footholds, move to other machines, and access more data. |
||||
| 2021-04-30 12:20:47 | 100 Days Down, 1,360 Days of Nation-State Cybersecurity Threats to Go (lien direct) |
 This week marks the milestone of the Biden Administration's first 100 days. It is somewhat arbitrary to expect an incoming president to achieve significant progress in just 100 days, or to judge success or failure based on such a small span of time.
However, it does provide a glimpse into the vision and direction of the administration, and so far it seems like President Biden is preparing to address the growing cybersecurity threat from our adversaries.
This week marks the milestone of the Biden Administration's first 100 days. It is somewhat arbitrary to expect an incoming president to achieve significant progress in just 100 days, or to judge success or failure based on such a small span of time.
However, it does provide a glimpse into the vision and direction of the administration, and so far it seems like President Biden is preparing to address the growing cybersecurity threat from our adversaries. |
Threat | |||
| 2021-04-30 12:11:34 | PortDoor: New Chinese APT Backdoor Attack Targets Russian Defense Sector (lien direct) |
 The Cybereason Nocturnus Team has been tracking recent developments in the RoyalRoad weaponizer, also known as the 8.t Dropper/RTF exploit builder. Over the years, this tool has become a part of the arsenal of several Chinese-related threat actors such as Tick, Tonto Team and TA428, all of which employ RoyalRoad regularly for spear-phishing in targeted attacks against high-value targets.
The Cybereason Nocturnus Team has been tracking recent developments in the RoyalRoad weaponizer, also known as the 8.t Dropper/RTF exploit builder. Over the years, this tool has become a part of the arsenal of several Chinese-related threat actors such as Tick, Tonto Team and TA428, all of which employ RoyalRoad regularly for spear-phishing in targeted attacks against high-value targets. |
Threat Tool | |||
| 2021-04-29 12:38:50 | CISO Stories Podcast: Necessity is the Mother of Security (lien direct) |
 Tatu Ylönen, SSH founder and inventor of Secure Shell, discusses the genesis for the protocol and his keen interest in the application of technological solutions to fundamental cybersecurity challenges - check it out...
Tatu Ylönen, SSH founder and inventor of Secure Shell, discusses the genesis for the protocol and his keen interest in the application of technological solutions to fundamental cybersecurity challenges - check it out... |
★★ | |||
| 2021-04-28 13:54:57 | Webinar: The Current State and Future Challenges of Security (lien direct) |
 Join Ed Amoroso, CEO of TAG Cyber and Sam Curry, CSO of Cybereason as they discuss pre-COVID-19 trends, discontinuities, and the outlook based on recent events and challenges in the security industry. Supply Chain weaknesses, Ransomware, the “new normal” going forward, the evolution of the MITRE framework and more are all fair game.
Join Ed Amoroso, CEO of TAG Cyber and Sam Curry, CSO of Cybereason as they discuss pre-COVID-19 trends, discontinuities, and the outlook based on recent events and challenges in the security industry. Supply Chain weaknesses, Ransomware, the “new normal” going forward, the evolution of the MITRE framework and more are all fair game. |
||||
| 2021-04-28 12:59:38 | Five Things You Need to Know About Ransomware Attacks (lien direct) |
 The digital threat landscape as a whole is constantly changing and evolving. That can make it difficult to keep track of new developments for specific threats like ransomware. Don't worry though, Cybereason has got you covered.
The digital threat landscape as a whole is constantly changing and evolving. That can make it difficult to keep track of new developments for specific threats like ransomware. Don't worry though, Cybereason has got you covered. |
Threat Ransomware | |||
| 2021-04-27 14:52:51 | Cybereason vs. Avaddon Ransomware (lien direct) |
 Over the last few months, the Cybereason Nocturnus Team has been tracking the activity of the Avaddon Ransomware. It has been active since June 2020 and is operating with the Ransomware-as-a-Service (RaaS) and double extortion models, targeting sectors such as healthcare. Avaddon is distributed via malspam campaigns, where the victim is being lured to download the malware loader.
Over the last few months, the Cybereason Nocturnus Team has been tracking the activity of the Avaddon Ransomware. It has been active since June 2020 and is operating with the Ransomware-as-a-Service (RaaS) and double extortion models, targeting sectors such as healthcare. Avaddon is distributed via malspam campaigns, where the victim is being lured to download the malware loader. |
Ransomware Malware | |||
| 2021-04-27 13:08:29 | Malicious Life Podcast: Can Nuclear Power Plants Be Hacked? (lien direct) |
 Andrew Ginter, VP of Industrial Security at Waterfall Security Solutions, dives into cybersecurity challenges for Nuclear facilities - how secure are modern nuclear power plants from cyber attacks? Check it out...
Andrew Ginter, VP of Industrial Security at Waterfall Security Solutions, dives into cybersecurity challenges for Nuclear facilities - how secure are modern nuclear power plants from cyber attacks? Check it out... |
||||
| 2021-04-26 12:05:22 | Integrating Endpoint and Mobile Device Security (lien direct) |
 Enterprise teams are advised in this report to integrate their traditional and next-generation endpoint security protections with emerging mobile security safeguards.
Enterprise teams are advised in this report to integrate their traditional and next-generation endpoint security protections with emerging mobile security safeguards. |
||||
| 2021-04-22 19:27:46 | HAFNIUM Exploits Live On (lien direct) |
 The Prometei Botnet is not new. Like most malware and exploits, it continues to adapt and change over time. What is concerning is what is happening now. Our latest research demonstrates how Prometei has evolved and reveals that current versions of Prometei are now exploiting some of the vulnerabilities in Microsoft Exchange that were part of the recent HAFNIUM attacks. We will continue to deal with lingering effects from these specific Microsoft Exchange vulnerabilities, but-more importantly-we will continue to deal with vulnerabilities in general and that requires a better approach to cybersecurity.
The Prometei Botnet is not new. Like most malware and exploits, it continues to adapt and change over time. What is concerning is what is happening now. Our latest research demonstrates how Prometei has evolved and reveals that current versions of Prometei are now exploiting some of the vulnerabilities in Microsoft Exchange that were part of the recent HAFNIUM attacks. We will continue to deal with lingering effects from these specific Microsoft Exchange vulnerabilities, but-more importantly-we will continue to deal with vulnerabilities in general and that requires a better approach to cybersecurity. |
Malware | |||
| 2021-04-22 13:03:55 | Sodinokibi Ransomware Gang Extorts Apple Through Supply Chain Attack (lien direct) |
 The Sodinokibi ransomware gang is trying to extort Apple following an attack against one of the tech giant's business partners. According to Bloomberg News, someone using the moniker “Unknown” announced on April 18 that the Sodinokibi/REvil gang was about to disclose their “largest attack ever.”
The Sodinokibi ransomware gang is trying to extort Apple following an attack against one of the tech giant's business partners. According to Bloomberg News, someone using the moniker “Unknown” announced on April 18 that the Sodinokibi/REvil gang was about to disclose their “largest attack ever.” |
Ransomware | |||
| 2021-04-22 03:55:00 | Prometei Botnet Exploiting Microsoft Exchange Vulnerabilities (lien direct) |
 Recently, the Cybereason Nocturnus Team responded to several incident response (IR) cases involving infections of the Prometei Botnet against companies in North America, observing that the attackers exploited recently published Microsoft Exchange vulnerabilities (CVE-2021-27065 and CVE-2021-26858) in order to penetrate the network and install malware.
Recently, the Cybereason Nocturnus Team responded to several incident response (IR) cases involving infections of the Prometei Botnet against companies in North America, observing that the attackers exploited recently published Microsoft Exchange vulnerabilities (CVE-2021-27065 and CVE-2021-26858) in order to penetrate the network and install malware. |
||||
| 2021-04-21 20:58:41 | MITRE ATT&CK: Cybereason Dominates the Competition (lien direct) |
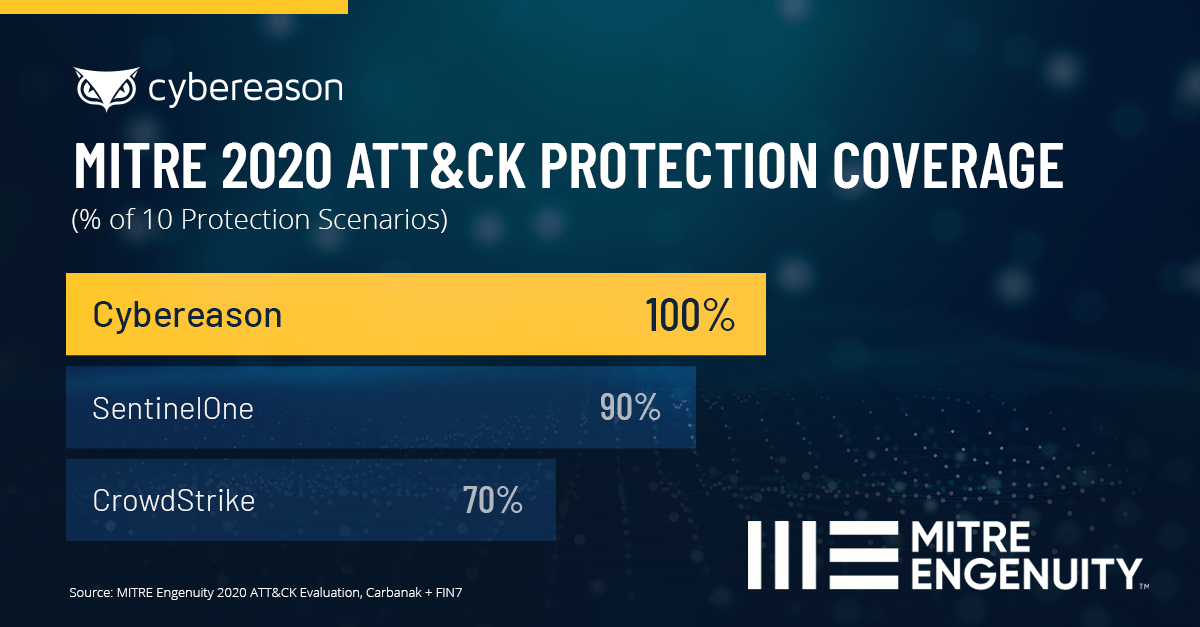 The long-awaited 2020 MITRE ATT&CK evaluations are out! With the MITRE ATT&CK framework now being the standard by which Defenders can measure the effectiveness of various solutions in tracking adversary behavior, cyber vendors are cherry-picking results from this latest testing round and spinning up clever interpretations of the data in their favor. At Cybereason, we are proud to let the test results speak for themselves.
The long-awaited 2020 MITRE ATT&CK evaluations are out! With the MITRE ATT&CK framework now being the standard by which Defenders can measure the effectiveness of various solutions in tracking adversary behavior, cyber vendors are cherry-picking results from this latest testing round and spinning up clever interpretations of the data in their favor. At Cybereason, we are proud to let the test results speak for themselves. |

