What's new arround internet
| Src | Date (GMT) | Titre | Description | Tags | Stories | Notes |
| 2022-08-23 07:50:00 | Google Uncovers Tool Used by Iranian Hackers to Steal Data from Email Accounts (lien direct) | The Iranian government-backed actor known as Charming Kitten has added a new tool to its malware arsenal that allows it to retrieve user data from Gmail, Yahoo!, and Microsoft Outlook accounts. Dubbed HYPERSCRAPE by Google Threat Analysis Group (TAG), the actively in-development malicious software is said to have been used against less than two dozen accounts in Iran, with the oldest known | Malware Tool Threat Conference | Yahoo APT 35 | ||
| 2022-08-22 20:30:34 | Metasploit Creator Renames His Startup and IT Discovery Tool Rumble to \'runZero\' (lien direct) | HD Moore's company has rebranded its IT, IoT, and OT asset discovery tool as the platform rapidly evolves. | Tool | |||
| 2022-08-22 14:00:00 | Threat Actor Deploys Raven Storm Tool to Perform DDoS Attacks (lien direct) | The malware is reportedly capable of server takedown, Wi-Fi attacks and application layer attacks | Malware Tool | |||
| 2022-08-22 13:30:00 | How Qualys Reduces Risk and Enables Tool Consolidation (lien direct) | Sumedh Thakar, CEO of Qualys, explains how moving to a cloud-based asset management platform can simplify their strategies and improve overall security. | Tool | |||
| 2022-08-20 13:00:00 | Janet Jackson\'s \'Rhythm Nation\' Can Crash Old Hard Drives (lien direct) | Plus: The Twilio hack snags a reporter, a new tool to check for spyware, and the Canadian weed pipeline gets hit by a cyberattack. | Hack Tool | |||
| 2022-08-18 18:34:08 | China\'s APT41 Embraces Baffling Approach for Dropping Cobalt Strike Payload (lien direct) | The state-sponsored threat actor has switched up its tactics, also adding an automated SQL-injection tool to its bag of tricks for initial access. | Tool Threat | APT 41 | ||
| 2022-08-18 11:45:45 | USB “Rubber Ducky” Attack Tool (lien direct) | The USB Rubber Ducky is getting better and better. Already, previous versions of the Rubber Ducky could carry out attacks like creating a fake Windows pop-up box to harvest a user’s login credentials or causing Chrome to send all saved passwords to an attacker’s webserver. But these attacks had to be carefully crafted for specific operating systems and software versions and lacked the flexibility to work across platforms. The newest Rubber Ducky aims to overcome these limitations. It ships with a major upgrade to the DuckyScript programming language, which is used to create the commands that the Rubber Ducky will enter into a target machine. While previous versions were mostly limited to writing keystroke sequences, DuckyScript 3.0 is a feature-rich language, letting users write functions, store variables, and use logic flow controls (i.e., if this… then that)... | Tool | |||
| 2022-08-17 22:15:08 | CVE-2022-2869 (lien direct) | libtiff's tiffcrop tool has a uint32_t underflow which leads to out of bounds read and write in the extractContigSamples8bits routine. An attacker who supplies a crafted file to tiffcrop could trigger this flaw, most likely by tricking a user into opening the crafted file with tiffcrop. Triggering this flaw could cause a crash or potentially further exploitation. | Tool Guideline | |||
| 2022-08-17 10:00:00 | A pragmatic approach to risk management & resilience (lien direct) | Cybersecurity starts with the ability to recognize your cyber risk. We will explore several topics related to taking a practical approach to managing risk and achieving cyber resilience. This is a blog series with collective thoughts from Bindu Sundaresan, Director AT&T Cybersecurity, and Nick Simmons, AVP, Cybersecurity. Cybercrime has become increasingly frequent, complex, and costly, posing a risk to all businesses regardless of size. How do you plan to respond when falling victim to a breach? Would you know who to call, how to react, or what to tell your employees, customers, and media? Could your organization absorb the potential financial and reputational impact of a lawsuit? The answer cannot be, "we store everything in the cloud, so we are good." Who owns the risk? Could your brand's image survive? What is acceptable, and how do you know your current plan will suffice? What more could your company do to understand better and manage the risk? These questions are all top of mind and need to be addressed from an overall business perspective. This blog summarizes the fundamental steps and offers suggestions to understand, manage, and respond to risk. Beyond technology, focus on risk and resilience It can be easy to deploy security technology and think you've mitigated risk to your business. Unfortunately, technology investment is no guarantee of protection against the latest threats. It is critical to take a risk-based approach to security, meaning leaders must identify and focus on specific elements of cyber risk to decrease enterprise risk. Specifically, the many components of cyber risk must be understood and prioritized for enterprise cybersecurity efforts. Organizations are increasingly aiming to shift from cybersecurity to cyber resilience, and the following recommendations can help forge this path: Understand the threats Measure the potential financial impact of cyber exposures compared to the company's risk appetite level; and Proactively manage cyber risks with clear action plans based on their capabilities and capacities to protect against cybercrime Risk-based approach Cyber resiliency requires a risk-based approach, accomplishing two critical things at once. First, it designates risk reduction as the primary goal, enabling the organization to prioritize investment, including implementation-related problem solving based squarely on a cyber program's effectiveness at reducing risk. Second, the program distills top management's risk-reduction targets into pragmatic implementation programs with precise alignment from senior executives to the front line. Following the risk-based approach, a company will no longer "build the control everywhere"; rather, the focus will be on building the appropriate controls for the worst vulnerabilities to defeat the most significant threats that target the business' most critical areas. The risk-based approach to cybersecurity is thus ultimately interactive and a dynamic tool to support strategic decision-making. Focused on business value, utilizing a common language among the interested parties, and directly linking enterprise risks to controls, the approach helps translate executive decisions about risk reduction into control implementation. The power of the risk-based approach to optimize risk reduction at any level of investment is enhanced by its flexibility, adjusting to an evolving risk-appetite strategy as needed. A risk-based approach recognizes that there are no perfect security solutions. Still, those that strategically balance security, scalability, access, usability, and cost can ultimately provide the best long-term protection against an evolving adversary. Fundamentally, risk transformation changes security strategy from an outside-in perspective, where external threats and regulations drive strategy, to an | Ransomware Data Breach Tool Vulnerability Threat Patching Guideline | |||
| 2022-08-16 15:30:00 | Healthcare Provider Issues Warning After Tracking Pixels Leak Patient Data (lien direct) | The leak was caused by incorrect configurations of an online tracking tool from Meta | Tool | |||
| 2022-08-16 15:06:00 | Anomali Cyber Watch: Ransomware Module Added to SOVA Android Trojan, Bitter APT Targets Mobile Phones with Dracarys, China-Sponsored TA428 Deploys Six Backdoors at Once, and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: Android, APT, China, Cyberespionage, India, Malspam, Ransomware, Spearphishing, and Vulnerabilities. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
APT-C-35: New Windows Framework Revealed
(published: August 11, 2022)
The DoNot Team (APT-C-35) are India-sponsored actors active since at least 2016. Morphisec Labs researchers discovered a new Windows framework used by the group in its campaign targeting Pakistani government and defense departments. The attack starts with a spearphishing RTF attachment. If opened in a Microsoft Office application, it downloads a malicious remote template. After the victim enables editing (macroses) a multi-stage framework deployment starts. It includes two shellcode stages followed by main DLL that, based on victim fingerprinting, downloads a custom set of additional information-stealing modules.
Analyst Comment: The described DoNot Team framework is pretty unique in its customisation, fingerprinting, and module implementation. At the same time, the general theme of spearphishing attachment that asks the targeted user to enable editing is not new and can be mitigated by anti-phishing training and Microsoft Office settings hardening.
MITRE ATT&CK: [MITRE ATT&CK] Phishing - T1566 | [MITRE ATT&CK] Virtualization/Sandbox Evasion - T1497 | [MITRE ATT&CK] Template Injection - T1221 | [MITRE ATT&CK] User Execution - T1204 | [MITRE ATT&CK] Ingress Tool Transfer - T1105 | [MITRE ATT&CK] Obfuscated Files or Information - T1027 | [MITRE ATT&CK] Deobfuscate/Decode Files or Information - T1140 | [MITRE ATT&CK] Scheduled Task - T1053 | [MITRE ATT&CK] System Information Discovery - T1082 | [MITRE ATT&CK] Input Capture - T1056 | [MITRE ATT&CK] Screen Capture - T1113 | [MITRE ATT&CK] Data from Local System - T1005 | [MITRE ATT&CK] Data from Removable Media - T1025 | [MITRE ATT&CK] Data from Network Shared Drive - T1039 | [MITRE ATT&CK] Credentials from Password Stores - T1555 | [MITRE ATT&CK] Data Staged - T1074 | [MITRE ATT&CK] Command and Scripting Interpreter - T1059
Tags: APT-C-35, DoNot Team, APT, India, source-country:IN, Government, Military, Pakistan, target-country:PK, Windows
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
APT-C-35: New Windows Framework Revealed
(published: August 11, 2022)
The DoNot Team (APT-C-35) are India-sponsored actors active since at least 2016. Morphisec Labs researchers discovered a new Windows framework used by the group in its campaign targeting Pakistani government and defense departments. The attack starts with a spearphishing RTF attachment. If opened in a Microsoft Office application, it downloads a malicious remote template. After the victim enables editing (macroses) a multi-stage framework deployment starts. It includes two shellcode stages followed by main DLL that, based on victim fingerprinting, downloads a custom set of additional information-stealing modules.
Analyst Comment: The described DoNot Team framework is pretty unique in its customisation, fingerprinting, and module implementation. At the same time, the general theme of spearphishing attachment that asks the targeted user to enable editing is not new and can be mitigated by anti-phishing training and Microsoft Office settings hardening.
MITRE ATT&CK: [MITRE ATT&CK] Phishing - T1566 | [MITRE ATT&CK] Virtualization/Sandbox Evasion - T1497 | [MITRE ATT&CK] Template Injection - T1221 | [MITRE ATT&CK] User Execution - T1204 | [MITRE ATT&CK] Ingress Tool Transfer - T1105 | [MITRE ATT&CK] Obfuscated Files or Information - T1027 | [MITRE ATT&CK] Deobfuscate/Decode Files or Information - T1140 | [MITRE ATT&CK] Scheduled Task - T1053 | [MITRE ATT&CK] System Information Discovery - T1082 | [MITRE ATT&CK] Input Capture - T1056 | [MITRE ATT&CK] Screen Capture - T1113 | [MITRE ATT&CK] Data from Local System - T1005 | [MITRE ATT&CK] Data from Removable Media - T1025 | [MITRE ATT&CK] Data from Network Shared Drive - T1039 | [MITRE ATT&CK] Credentials from Password Stores - T1555 | [MITRE ATT&CK] Data Staged - T1074 | [MITRE ATT&CK] Command and Scripting Interpreter - T1059
Tags: APT-C-35, DoNot Team, APT, India, source-country:IN, Government, Military, Pakistan, target-country:PK, Windows |
Ransomware Malware Tool Vulnerability Threat Guideline Medical | APT 38 | ||
| 2022-08-16 10:03:51 | Vulnerability Spotlight: Three vulnerabilities in HDF5 file format could lead to remote code execution (lien direct) |  Dave McDaniel of Cisco Talos discovered these vulnerabilities. Blog by Jon Munshaw. Cisco Talos recently discovered three vulnerabilities in a library that works with the HDF5 file format that could allow an attacker to execute remote code on a targeted device. These issues arise in the libhdf5 gif2h5 tool that's normally used to convert a GIF file to the HDF5 format, commonly used to store large amounts of numerical data. An attacker could exploit these vulnerabilities by tricking a user into opening a specially crafted, malicious file. TALOS-2022-1485 (CVE-2022-25972) and TALOS-2022-1486 (CVE-2022-25942) are out-of-bounds write vulnerabilities in the gif2h5 tool that trigger a specific crash, opening the door for code execution from the adversary. TALOS-2022-1487 (CVE-2022-26061) works similarly but is a heap-based buffer overflow vulnerability. Cisco Talos is disclosing these vulnerabilities despite no official fix from HDF5 in adherence to the 90-day deadline outlined in Cisco's vulnerability disclosure policy. Dave McDaniel of Cisco Talos discovered these vulnerabilities. Blog by Jon Munshaw. Cisco Talos recently discovered three vulnerabilities in a library that works with the HDF5 file format that could allow an attacker to execute remote code on a targeted device. These issues arise in the libhdf5 gif2h5 tool that's normally used to convert a GIF file to the HDF5 format, commonly used to store large amounts of numerical data. An attacker could exploit these vulnerabilities by tricking a user into opening a specially crafted, malicious file. TALOS-2022-1485 (CVE-2022-25972) and TALOS-2022-1486 (CVE-2022-25942) are out-of-bounds write vulnerabilities in the gif2h5 tool that trigger a specific crash, opening the door for code execution from the adversary. TALOS-2022-1487 (CVE-2022-26061) works similarly but is a heap-based buffer overflow vulnerability. Cisco Talos is disclosing these vulnerabilities despite no official fix from HDF5 in adherence to the 90-day deadline outlined in Cisco's vulnerability disclosure policy. |
Tool Vulnerability | |||
| 2022-08-12 21:00:00 | Anti-tracking tool tells you if you\'re being followed (lien direct) | >Categories: NewsCategories: PrivacyAt Black Hat, a cybersecurity expert presented an anti-stalking tool they made for a friend. (Read more...) | Tool | |||
| 2022-08-11 06:54:45 | InfoStealer Script Based on Curl and NSudo, (Thu, Aug 11th) (lien direct) | If sudo[1] is a well known tool used daily by most UNIX system administrators, NSudo[2] remains less below the radar. This is a tool running on Microsoft Windows which allows you to execute processes with different access tokens and privileges like: | Tool | |||
| 2022-08-10 14:14:08 | Why robotexts are scammers\' favorite new tool (lien direct) | Technology meant to limit robocalls has pushed scammers toward SMS-based attacks, which experts say can be even more dangerous. | Tool | |||
| 2022-08-10 13:10:00 | Sensitive data in the cloud gets new automated remediation tool from BigID (lien direct) | Data intelligence company BigID announced this week at the Black Hat conference in Las Vegas that it has rolled out new features for its privacy and data protection platform, allowing users to programmatically restrict access to sensitive cloud-based information when it's under threat.BigID's core product, its Data Intelligence platform, already boasts numerous capabilities focused on the privacy, organization and discovery of a company's data. The new features announced this week build on that framework, allowing IT staff to automatically lock down access to sensitive information tagged as having open or overprivileged access in the big three public cloud platforms.To read this article in full, please click here | Tool | |||
| 2022-08-10 11:45:56 | Microsoft Patch Tuesday Fixed 0-day Arbitrary Code Execution Vulnerability (CVE-2022-34713) (lien direct) | Microsoft has released 141 security fixes for this month's August 2022 release. Besides the usual security fixes, there was a zero-day of note:CVE-2022-34713: This is a vulnerability in Microsoft Support Diagnostic Tool (MSDT). Microsoft confirmed in their advisory that the vulnerability was exploited in the wild as a zero-day. CVE-2022-34713 is an arbitrary code execution (ACE) vulnerability, which requires user interaction. As such an user need to open a specifically crafted file or visit a specially designed Web site to be exploited. This has a CVSS score of 7.8 and is rated important.Why is this Significant?This is significant as Microsoft observed CVE-2022-34713 was exploited as a 0-day in the wild. Because the exploitation requires user interaction, an attacker likely uses social engineering to get users to open a specifically crafted file or visit a specially designed Web site for exploitation.How Widespread is the Attack that Leverages CVE-2022-34713?At this time, there is no information available as to how widespread the attack is. However, since the vulnerability was publicly disclosed, attacks that leverage CVE-2022-34713 may increase.Also, a similar vulnerability in MSDT (CVE-2022-30190, also known as Follina) that was patched in June 2022 by Microsoft is widely exploited in the wild. This is another indicator that likelihood of CVE-2022-34713 exploitation will likely increase.FortiGuard Labs previously released a Threat Signal for CVE-2022-30190 (Follina). See the Appendix for a link to "Follina: 0-day Windows MSDT Vulnerability (CVE-2022-30190) Exploited In The Wild".Is there Any Other Vulnerability in the August Patch Tuesday that Requires Attention?Microsoft also released a patch for another vulnerability in MSDT (CVE-2022-35743). While the vulnerability was not reported nor observed to have been exploited in the wild, the Microsoft advisory states that exploitation is likely to occur. As such a patch for CVE-2022-35743 should also be applied as soon as possible. This has a CVSS score of 7.8 and is rated important.Has Microsoft Released Security Advisories for CVE-2022-34713?Yes, Microsoft has issued an advisory for the vulnerability. See the Appendix for a link to "CVE-2022-34713: Microsoft Windows Support Diagnostic Tool (MSDT) Remote Code Execution Vulnerability".Has Microsoft Released a Patch for CVE-2022-34713?Yes, Microsoft has released a patch for CVE-2022-34713 on August 9th, 2022 as part of regular MS Tuesday for the month.What is the Status of Coverage?FortiGuard Labs is investigating coverage, and will update this threat signal once any relevant updates are available. | Tool Vulnerability Threat | |||
| 2022-08-10 07:00:00 | (Déjà vu) capa v4: couler un .net plus large capa v4: casting a wider .NET (lien direct) |
Nous sommes ravis d'annoncer la version 4.0 de CAPA avec la prise en charge de l'analyse des exécutables .NET.Cet outil open source identifie automatiquement les capacités des programmes à l'aide d'un ensemble de règles extensible.L'outil prend en charge à la fois le triage de logiciels malveillants et l'ingénierie inverse de plongée profonde.Si vous n'avez pas entendu parler de CAPA auparavant ou si vous avez besoin d'un rafraîchissement, consultez notre Premier article de blog .Vous pouvez télécharger des binaires autonomes CAPA V4.0 à partir des Project \ Project \\ 's Page de libération Et vérifiez le code source sur github .
CAPA 4.0 ajoute de nouvelles fonctionnalités majeures qui étendent sa capacité à analyser et à raisonner sur les programmes.Ce billet de blog couvre
We are excited to announce version 4.0 of capa with support for analyzing .NET executables. This open-source tool automatically identifies capabilities in programs using an extensible rule set. The tool supports both malware triage and deep dive reverse engineering. If you have not heard of capa before, or need a refresher, check out our first blog post. You can download capa v4.0 standalone binaries from the project\'s release page and checkout the source code on GitHub. capa 4.0 adds major new features that extends its ability to analyze and reason about programs. This blog post covers |
Malware Tool | ★★★★ | ||
| 2022-08-09 23:12:13 | (Déjà vu) Microsoft Issues Patches for 121 Flaws, Including Zero-Day Under Active Attack (lien direct) | As many as 121 new security flaws were patched by Microsoft as part of its Patch Tuesday updates for the month of August, which also includes a fix for a Support Diagnostic Tool vulnerability that the company said is being actively exploited in the wild. Of the 121 bugs, 17 are rated Critical, 102 are rated Important, one is rated Moderate, and one is rated Low in severity. Two of the issues | Tool Vulnerability | ★★★★ | ||
| 2022-08-09 23:01:10 | Microsoft Patch Tuesday, August 2022 Edition (lien direct) | Microsoft today released updates to fix a record 141 security vulnerabilities in its Windows operating systems and related software. Once again, Microsoft is patching a zero-day vulnerability in the Microsoft Support Diagnostics Tool (MSDT), a service built into Windows. Redmond also addressed multiple flaws in Exchange Server - including one that was disclosed publicly prior to today - and it is urging organizations that use Exchange for email to update as soon as possible and to enable additional protections. | Tool Vulnerability Patching | |||
| 2022-08-09 20:25:07 | Microsoft Patches Zero-Day Actively Exploited in the Wild (lien direct) | The computing giant issued a massive Patch Tuesday update, including a pair of remote execution flaws in the Microsoft Support Diagnostic Tool (MSDT) after attackers used one of the vulnerabilities in a zero-day exploit. | Tool | |||
| 2022-08-09 20:15:11 | CVE-2022-34713 (lien direct) | Microsoft Windows Support Diagnostic Tool (MSDT) Remote Code Execution Vulnerability. This CVE ID is unique from CVE-2022-35743. | Tool | |||
| 2022-08-09 17:12:16 | Researchers Debut Fresh RCE Vector for Common Google API Tool (lien direct) | The finding exposes the danger of older, unpatched bugs, which plague at least 4.5 million devices. | Tool | |||
| 2022-08-09 16:44:37 | Microsoft Patch Tuesday for August 2022 - Snort rules and prominent vulnerabilities (lien direct) |  By Jon Munshaw and Vanja Svajcer.Microsoft released its monthly security update Tuesday, disclosing more than 120 vulnerabilities across its line of products and software, the most in a single Patch Tuesday in four months. This batch of updates also includes a fix for a new vulnerability in the Microsoft Windows Support Diagnostic Tool (MSDT) that's actively being exploited in the wild, according to Microsoft. MSDT was already the target of the so-called “Follina” zero-day vulnerability in June. In all, August's Patch Tuesday includes 15 critical vulnerabilities and a single low- and moderate-severity issue. The remainder is classified as “important.” Two of the important vulnerabilities CVE-2022-35743 and CVE-2022-34713 are remote code execution vulnerabilities in MSDT. However, only CVE-2022-34713 has been exploited in the wild and Microsoft considers it “more likely” to be exploited. Microsoft Exchange Server contains two critical elevation of privilege vulnerabilities, CVE-2022-21980 and CVE-2022-24477. An attacker could exploit this vulnerability by tricking a target into visiting a malicious, attacker-hosted server or website. In addition to applying the patch released today, potentially affected users should enable Extended Protection on vulnerable versions of the server. The Windows Point-to-Point Tunneling Protocol is also vulnerable to three critical vulnerabilities. Two of them, CVE-2022-35744 and CVE-2022-30133, could allow an attacker to execute remote code on an RAS server machine. The other, CVE-2022-35747, could lead to a denial-of-service condition. CVE-2022-35744 has a CVSS severity score of 9.8 out of 10, one of the highest-rated vulnerabilities this month. An attacker could exploit these vulnerabilities by communicating via Port 1723. Affected users can render these issues unexploitable by blocking that port, though it runs the risk of disrupting other legitimate communications. Another critical code execution vulnerability, CVE-2022-35804, affects the SMB Client and Server and the way the protocol handles specific requests. An attacker could exploit this on the SMB Client by config By Jon Munshaw and Vanja Svajcer.Microsoft released its monthly security update Tuesday, disclosing more than 120 vulnerabilities across its line of products and software, the most in a single Patch Tuesday in four months. This batch of updates also includes a fix for a new vulnerability in the Microsoft Windows Support Diagnostic Tool (MSDT) that's actively being exploited in the wild, according to Microsoft. MSDT was already the target of the so-called “Follina” zero-day vulnerability in June. In all, August's Patch Tuesday includes 15 critical vulnerabilities and a single low- and moderate-severity issue. The remainder is classified as “important.” Two of the important vulnerabilities CVE-2022-35743 and CVE-2022-34713 are remote code execution vulnerabilities in MSDT. However, only CVE-2022-34713 has been exploited in the wild and Microsoft considers it “more likely” to be exploited. Microsoft Exchange Server contains two critical elevation of privilege vulnerabilities, CVE-2022-21980 and CVE-2022-24477. An attacker could exploit this vulnerability by tricking a target into visiting a malicious, attacker-hosted server or website. In addition to applying the patch released today, potentially affected users should enable Extended Protection on vulnerable versions of the server. The Windows Point-to-Point Tunneling Protocol is also vulnerable to three critical vulnerabilities. Two of them, CVE-2022-35744 and CVE-2022-30133, could allow an attacker to execute remote code on an RAS server machine. The other, CVE-2022-35747, could lead to a denial-of-service condition. CVE-2022-35744 has a CVSS severity score of 9.8 out of 10, one of the highest-rated vulnerabilities this month. An attacker could exploit these vulnerabilities by communicating via Port 1723. Affected users can render these issues unexploitable by blocking that port, though it runs the risk of disrupting other legitimate communications. Another critical code execution vulnerability, CVE-2022-35804, affects the SMB Client and Server and the way the protocol handles specific requests. An attacker could exploit this on the SMB Client by config |
Tool Vulnerability Guideline | ★★★★ | ||
| 2022-08-09 15:01:00 | Anomali Cyber Watch: RapperBot Persists on SSH Servers, Manjusaka Attack Framework Tested in China, BlackCat/DarkSide Ransom Energy Again, and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: APT, Botnet, China, Data breach, DDoS, Phishing, Ransomware, and Taiwan. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
So RapperBot, What Ya Bruting For?
(published: August 3, 2022)
RapperBot, a new Internet of things (IoT) botnet, is rapidly evolving despite appearing in the wild just two months ago (June 2022). Fortinet researchers discovered that RapperBot heavily reuses parts of the Mirai source code, but changed the attack vector (brute-forcing SSH instead of Telnet), command and control (C2) protocol, and added persistence capabilities. RapperBot maintains remote access by adding the attacker's public key to ~/.ssh/authorized_keys. The latest RapperBot samples also started adding the root user "suhelper” to /etc/passwd and /etc/shadow/, and continue to add the root user account every hour. Top targeted IPs were from Taiwan, USA, and South Korea, in that order. RapperBot has basic DDoS capabilities such as UDP and TCP STOMP flood copied from Mirai source code.
Analyst Comment: Despite sharing a significant amount of source code with Mirai variants, RapperBot appears to be developed by a persistent actor and not a novice motivated by notoriety. It is possible that the actors will add new impact functionality after the RapperBot botnet grows substantially. SSH server administrators should adhere to secure password practices. It is also important to note that simply restarting the device, changing SSH credentials or even disabling SSH password authentication does not remove the RapperBot infection.
MITRE ATT&CK: [MITRE ATT&CK] Valid Accounts - T1078 | [MITRE ATT&CK] Obfuscated Files or Information - T1027 | [MITRE ATT&CK] Deobfuscate/Decode Files or Information - T1140 | [MITRE ATT&CK] Network Denial of Service - T1498 | [MITRE ATT&CK] Account Manipulation - T1098 | [MITRE ATT&CK] Create Account - T1136 | [MITRE ATT&CK] Scheduled Task - T1053
Tags: RapperBot, Taiwan, target-country:TW, USA, target-country:US, South Korea, target-country:KR, SSH brute force, DDoS, IoT, ARM, MIPS, SPARC, x86, Linux, UDP flood, TCP STOMP, port:4343, port:4344, port:4345, port:48109, Mirai
Woody RAT: A New Feature-Rich Malware Spotted in the Wild
(published: August 3, 2022)
Malwarebytes researchers have identified a new Remote Access Trojan (RAT) dubbed Woody Rat. It has been used by unidentified attackers for at least one year targeting Russian organizations in the aerospace industry. Two kinds of spearphishing attachment were used. Initially, Woody Rat was delivered via archived executable with double extension .DOC.EXE. More recently, the attackers switched to Microsoft Office documents leveraging the Follina (CVE-2022-30190) vulnerability. Woody Ra
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
So RapperBot, What Ya Bruting For?
(published: August 3, 2022)
RapperBot, a new Internet of things (IoT) botnet, is rapidly evolving despite appearing in the wild just two months ago (June 2022). Fortinet researchers discovered that RapperBot heavily reuses parts of the Mirai source code, but changed the attack vector (brute-forcing SSH instead of Telnet), command and control (C2) protocol, and added persistence capabilities. RapperBot maintains remote access by adding the attacker's public key to ~/.ssh/authorized_keys. The latest RapperBot samples also started adding the root user "suhelper” to /etc/passwd and /etc/shadow/, and continue to add the root user account every hour. Top targeted IPs were from Taiwan, USA, and South Korea, in that order. RapperBot has basic DDoS capabilities such as UDP and TCP STOMP flood copied from Mirai source code.
Analyst Comment: Despite sharing a significant amount of source code with Mirai variants, RapperBot appears to be developed by a persistent actor and not a novice motivated by notoriety. It is possible that the actors will add new impact functionality after the RapperBot botnet grows substantially. SSH server administrators should adhere to secure password practices. It is also important to note that simply restarting the device, changing SSH credentials or even disabling SSH password authentication does not remove the RapperBot infection.
MITRE ATT&CK: [MITRE ATT&CK] Valid Accounts - T1078 | [MITRE ATT&CK] Obfuscated Files or Information - T1027 | [MITRE ATT&CK] Deobfuscate/Decode Files or Information - T1140 | [MITRE ATT&CK] Network Denial of Service - T1498 | [MITRE ATT&CK] Account Manipulation - T1098 | [MITRE ATT&CK] Create Account - T1136 | [MITRE ATT&CK] Scheduled Task - T1053
Tags: RapperBot, Taiwan, target-country:TW, USA, target-country:US, South Korea, target-country:KR, SSH brute force, DDoS, IoT, ARM, MIPS, SPARC, x86, Linux, UDP flood, TCP STOMP, port:4343, port:4344, port:4345, port:48109, Mirai
Woody RAT: A New Feature-Rich Malware Spotted in the Wild
(published: August 3, 2022)
Malwarebytes researchers have identified a new Remote Access Trojan (RAT) dubbed Woody Rat. It has been used by unidentified attackers for at least one year targeting Russian organizations in the aerospace industry. Two kinds of spearphishing attachment were used. Initially, Woody Rat was delivered via archived executable with double extension .DOC.EXE. More recently, the attackers switched to Microsoft Office documents leveraging the Follina (CVE-2022-30190) vulnerability. Woody Ra |
Ransomware Malware Tool Vulnerability Threat | |||
| 2022-08-09 11:11:31 | More tools don\'t equal a stronger SOC (lien direct) | >Logpoint's latest release helps analysts integrate their tech stack and combines many capabilities in a single tool to help reduce the number of cybersecurity toolsby Gitte Gade, Product Marketing ManagerWith the development of new technology, the number of tools added to the list for security analysts keeps increasing. A study by ESG found that 40% [...] | Tool | |||
| 2022-08-08 07:00:00 | KMSpico explained: No, KMS is not "kill Microsoft" (lien direct) | >Categories: ExplainedA hack tool called KMSPico is hailed as the go-to tool when it comes to activiating Windows. But is it safe? (Read more...) | Hack Tool | |||
| 2022-08-07 07:00:00 | Comment scanner des QRCode depuis le Terminal Linux ? (lien direct) | Si vous travaillez essentiellement sur PC Linux et que vous n’avez de smartphone sous la main pour scanner un éventuel QRCode, j’ai ce qu’il vous faut. Il s’agit d’un petit tool qui s’appelle Qrscan et qui permet au choix d’utiliser la webcam de votre PC pour scanner un QRCode sur … Suite | Tool | |||
| 2022-08-04 14:00:00 | Hackers deploy new ransomware tool in attacks on Albanian government websites (lien direct) | >The hackers linked to the Iranian government claimed to have attacked Albania for hosting an opposition group conference. | Ransomware Tool | |||
| 2022-08-04 13:34:26 | Protect domain-joined computer passwords with Windows\' Local Administrator Password Solution (lien direct) | Windows finally includes a tool to manage local admin passwords, but admins will still need to do some work to make it useful. | Tool | |||
| 2022-08-04 08:00:13 | Attackers leveraging Dark Utilities "C2aaS" platform in malware campaigns (lien direct) |  By Edmund Brumaghin, Azim Khodjibaev and Matt Thaxton, with contributions from Arnaud Zobec.Executive SummaryDark Utilities, released in early 2022, is a platform that provides full-featured C2 capabilities to adversaries.It is marketed as a means to enable remote access, command execution, distributed denial-of-service (DDoS) attacks and cryptocurrency mining operations on infected systems.Payloads provided by the platform support Windows, Linux and Python-based implementations and are hosted within the Interplanetary File System (IPFS), making them resilient to content moderation or law enforcement intervention.Since its initial release, we've observed malware samples in the wild leveraging it to facilitate remote access and cryptocurrency mining.What is "Dark Utilities?"In early 2022, a new C2 platform called "Dark Utilities" was established, offering a variety of services such as remote system access, DDoS capabilities and cryptocurrency mining. The operators of the service also established Discord and Telegram communities where they provide technical support and assistance for customers on the platform. By Edmund Brumaghin, Azim Khodjibaev and Matt Thaxton, with contributions from Arnaud Zobec.Executive SummaryDark Utilities, released in early 2022, is a platform that provides full-featured C2 capabilities to adversaries.It is marketed as a means to enable remote access, command execution, distributed denial-of-service (DDoS) attacks and cryptocurrency mining operations on infected systems.Payloads provided by the platform support Windows, Linux and Python-based implementations and are hosted within the Interplanetary File System (IPFS), making them resilient to content moderation or law enforcement intervention.Since its initial release, we've observed malware samples in the wild leveraging it to facilitate remote access and cryptocurrency mining.What is "Dark Utilities?"In early 2022, a new C2 platform called "Dark Utilities" was established, offering a variety of services such as remote system access, DDoS capabilities and cryptocurrency mining. The operators of the service also established Discord and Telegram communities where they provide technical support and assistance for customers on the platform. 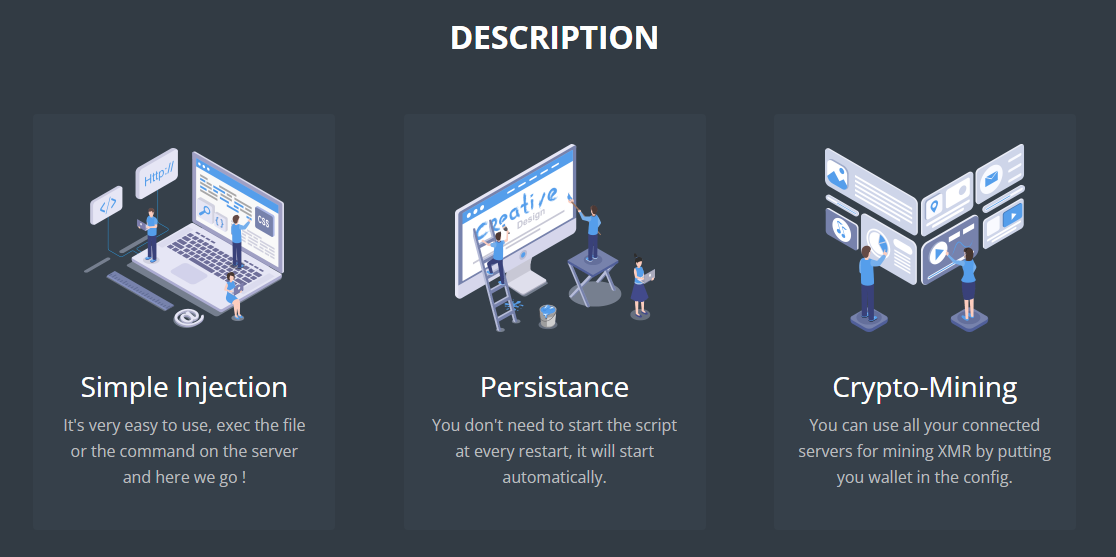 Dark Utilities provides payloads consisting of code that is executed on victim systems, allowing them to be registered with the service and establish a command and control (C2) communications channel. The platform currently supports Windows, Linux and Python-based payloads, allowing adversaries to target multiple architectures without requiring significant development resources. During our analysis, we observed efforts underway to expand OS and system architecture support as the platform continues to see ongoing develo Dark Utilities provides payloads consisting of code that is executed on victim systems, allowing them to be registered with the service and establish a command and control (C2) communications channel. The platform currently supports Windows, Linux and Python-based payloads, allowing adversaries to target multiple architectures without requiring significant development resources. During our analysis, we observed efforts underway to expand OS and system architecture support as the platform continues to see ongoing develo |
Spam Malware Hack Tool Threat Guideline | APT 19 | ||
| 2022-08-04 05:55:40 | New Woody RAT Malware Being Used to Target Russian Organizations (lien direct) | An unknown threat actor has been targeting Russian entities with a newly discovered remote access trojan called Woody RAT for at least a year as part of a spear-phishing campaign. The advanced custom backdoor is said to be delivered via either of two methods: archive files and Microsoft Office documents leveraging the now-patched "Follina" support diagnostic tool vulnerability (CVE-2022-30190) | Malware Tool Vulnerability Threat | ★★★★★ | ||
| 2022-08-03 17:15:45 | Manjusaka, a new attack tool similar to Sliver and Cobalt Strike (lien direct) | >Researchers spotted a Chinese threat actors using a new offensive framework called Manjusaka which is similar to Cobalt Strike. Talos researchers observed a Chinese threat actor using a new offensive framework called Manjusaka (which can be translated to “cow flower” from the Simplified Chinese writing) that is similar to Sliver and Cobalt Strike tools. The […] | Tool Threat | |||
| 2022-08-03 07:19:00 | Qualys adds external attack management capability to cloud security platform (lien direct) | Cloud security and compliance software company Qualys on Wednesday announced it is adding external attack surface management (EASM) capabilities to the Qualys Cloud Platform.The new capability will be integrated into Qualys CSAM (cybersecurity asset management) 2.0, an inventory monitoring and resolution tool to help security teams gain visibility into previously unknown internet-facing assets.“Achieving full asset visibility remains one of cybersecurity's most elusive goals,” said Sumedh Thakar, Qualys CEO, in a press release. ”CyberSecurity Asset Management 2.0 solves this by providing both the holistic, external attacker-level and internal view of the attack surface to address the increased threat landscape comprehensively.”To read this article in full, please click here | Tool Threat | |||
| 2022-08-03 02:00:00 | Tips to prevent RDP and other remote attacks on Microsoft networks (lien direct) | One long-favored way that ransomware enters your system is through Microsoft's Remote Desktop Protocol (RDP) attacks. Years ago when we used Microsoft's Terminal Services (from which RDP evolved) for shared remote access inside or outside of an office, attackers would use a tool called TSGrinder. It would first review a network for Terminal Services traffic on port 3389. Then attackers would use tools to guess the password to gain network access. They would go after administrator accounts first. Even if we changed the administrator account name or moved the Terminal Services protocol to another port, attackers would often sniff the TCP/IP traffic and identify where it was moved to.To read this article in full, please click here | Ransomware Tool | |||
| 2022-08-02 19:31:09 | Axis Raises the Bar With Modern-Day ZTNA Service that Boasts Hyper-Intelligence, Simplicity, and 350 Global Edges (lien direct) | Launches industry's first ZTNA Migration Tool and ZTNA Buyback Program, setting the stage for migration away from ZTNA 1.0. | Tool | |||
| 2022-08-02 15:17:00 | Anomali Cyber Watch: Velvet Chollima Steals Emails from Browsers, Austrian Mercenary Leverages Zero-Days, China-Sponsored Group Uses CosmicStrand UEFI Firmware Rootkit, and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: APT, Cyber mercenaries, Phishing, Rootkits, Spyware, and Vulnerabilities. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
SharpTongue Deploys Clever Mail-Stealing Browser Extension “SHARPEXT”
(published: July 28, 2022)
Volexity researchers discovered SharpExt, a new malicious browser app used by the North-Korea sponsored Velvet Chollima (Kimsuky, SharpTongue, Thallium) group. SharpExt inspects and exfiltrates data from a victim's webmail (AOL or Gmail) account as they browse it. Velvet Chollima continues to add new features to the app, the latest known version (3.0) supports three browsers: Microsoft Edge, Google Chrome, and Whale, the latter almost exclusively used in South Korea. Following the initial compromise, Velvet Chollima deploy SharpExt and to avoid warning the victim they manually exfiltrate settings files to change the settings and generate a valid "super_mac" security check value. They also hide the newly opened DevTools window and any other warning windows such as a warning regarding extensions running in developer mode.
Analyst Comment: Velvet Chollima is known for its tactic of deploying malicious browser extensions, but in the past it was concentrating on stealing credentials instead of emails. The group continues aggressive cyberespionage campaigns exfiltrating military and industrial technologies from Europe, South Korea, and the US. Network defenders should monitor for suspicious instances of PowerShell execution, as well as for traffic to and from known Velvet Chollima infrastructure (available in Anomali Match).
MITRE ATT&CK: [MITRE ATT&CK] Browser Extensions - T1176 | [MITRE ATT&CK] Email Collection - T1114 | [MITRE ATT&CK] Command and Scripting Interpreter - T1059 | [MITRE ATT&CK] Hide Artifacts - T1564
Tags: SharpExt, Velvet Chollima, Kimsuky, SharpTongue, Thallium, APT, North Korea, source-country:KP, South Korea, target-country:KR, USA, target-country:US, target-region:Europe, AOL, Gmail, Edge, Chrome, Whale, PowerShell, VBS, Browser extension
Untangling KNOTWEED: European Private-Sector Offensive Actor Using 0-Day Exploits
(published: July 27, 2022)
Microsoft researchers detail activity of DSIRF, Austrian private-sector offensive actor (PSOA). In 2021, this actor, tracked as Knotweed, used four Windows and Adobe 0-day exploits. In 2022, DSIRF was exploiting another Adobe Reader vulnerability, CVE-2022-22047, which was patched in July 2022. DSIRF attacks rely on their malware toolset called Subzero. The initial downloader shellcode is executed from either the exploit chains or malicious Excel documents. It downloads a JPG image file with extra encrypted data, extracts, decrypts and loads to the memory the Corelump memory-only infostealer. For persistence, Corelump creates trojanized copies of legitimate Windows DLLs that se
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
SharpTongue Deploys Clever Mail-Stealing Browser Extension “SHARPEXT”
(published: July 28, 2022)
Volexity researchers discovered SharpExt, a new malicious browser app used by the North-Korea sponsored Velvet Chollima (Kimsuky, SharpTongue, Thallium) group. SharpExt inspects and exfiltrates data from a victim's webmail (AOL or Gmail) account as they browse it. Velvet Chollima continues to add new features to the app, the latest known version (3.0) supports three browsers: Microsoft Edge, Google Chrome, and Whale, the latter almost exclusively used in South Korea. Following the initial compromise, Velvet Chollima deploy SharpExt and to avoid warning the victim they manually exfiltrate settings files to change the settings and generate a valid "super_mac" security check value. They also hide the newly opened DevTools window and any other warning windows such as a warning regarding extensions running in developer mode.
Analyst Comment: Velvet Chollima is known for its tactic of deploying malicious browser extensions, but in the past it was concentrating on stealing credentials instead of emails. The group continues aggressive cyberespionage campaigns exfiltrating military and industrial technologies from Europe, South Korea, and the US. Network defenders should monitor for suspicious instances of PowerShell execution, as well as for traffic to and from known Velvet Chollima infrastructure (available in Anomali Match).
MITRE ATT&CK: [MITRE ATT&CK] Browser Extensions - T1176 | [MITRE ATT&CK] Email Collection - T1114 | [MITRE ATT&CK] Command and Scripting Interpreter - T1059 | [MITRE ATT&CK] Hide Artifacts - T1564
Tags: SharpExt, Velvet Chollima, Kimsuky, SharpTongue, Thallium, APT, North Korea, source-country:KP, South Korea, target-country:KR, USA, target-country:US, target-region:Europe, AOL, Gmail, Edge, Chrome, Whale, PowerShell, VBS, Browser extension
Untangling KNOTWEED: European Private-Sector Offensive Actor Using 0-Day Exploits
(published: July 27, 2022)
Microsoft researchers detail activity of DSIRF, Austrian private-sector offensive actor (PSOA). In 2021, this actor, tracked as Knotweed, used four Windows and Adobe 0-day exploits. In 2022, DSIRF was exploiting another Adobe Reader vulnerability, CVE-2022-22047, which was patched in July 2022. DSIRF attacks rely on their malware toolset called Subzero. The initial downloader shellcode is executed from either the exploit chains or malicious Excel documents. It downloads a JPG image file with extra encrypted data, extracts, decrypts and loads to the memory the Corelump memory-only infostealer. For persistence, Corelump creates trojanized copies of legitimate Windows DLLs that se |
Malware Tool Vulnerability Threat Patching Guideline Cloud | APT 37 APT 28 | ||
| 2022-08-02 12:30:55 | LockBit 3.0 affiliate sideloads Cobalt Strike through Windows Defender (lien direct) | >An affiliate of the LockBit 3.0 RaaS operation has been abusing the Windows Defender command-line tool to deploy Cobalt Strike payloads. During a recent investigation, SentinelOne researchers observed threat actors associated with the LockBit 3.0 ransomware-as-a-service (RaaS) operation abusing the Windows Defender command line tool MpCmdRun.exe to decrypt and load Cobalt Strike payloads. The attackers initially compromise the target […] | Tool Threat | |||
| 2022-08-02 09:00:00 | Microsoft announces new external attack surface audit tool (lien direct) | Microsoft has announced a new security product allowing security teams to spot Internet-exposed resources in their organization's environment that attackers could use to breach their networks. [...] | Tool | |||
| 2022-08-02 01:07:34 | LockBit Ransomware Abuses Windows Defender to Deploy Cobalt Strike Payload (lien direct) | A threat actor associated with the LockBit 3.0 ransomware-as-a-service (RaaS) operation has been observed abusing the Windows Defender command-line tool to decrypt and load Cobalt Strike payloads. According to a report published by SentinelOne last week, the incident occurred after obtaining initial access via the Log4Shell vulnerability against an unpatched VMware Horizon Server. "Once initial | Ransomware Tool Threat | |||
| 2022-08-01 20:15:08 | CVE-2022-31188 (lien direct) | CVAT is an opensource interactive video and image annotation tool for computer vision. Versions prior to 2.0.0 were found to be subject to a Server-side request forgery (SSRF) vulnerability. Validation has been added to urls used in the affected code path in version 2.0.0. Users are advised to upgrade. There are no known workarounds for this issue. | Tool | ★★ | ||
| 2022-07-31 23:31:03 | Australian Hacker Charged with Creating, Selling Spyware to Cyber Criminals (lien direct) | A 24-year-old Australian national has been charged for his purported role in the creation and sale of spyware for use by domestic violence perpetrators and child sex offenders. Jacob Wayne John Keen, who currently resides at Frankston, Melbourne, is said to have created the remote access trojan (RAT) when he was 15, in addition to working as the administrator for the tool from 2013 until its | Tool | |||
| 2022-07-30 14:53:14 | LockBit Operators Abusing Microsoft Defender To Load Cobalt Strike Beacon (lien direct) | >Researchers from the cybersecurity company, SentinelOne have discovered that Microsoft's Windows Defender is being abused by a threat actor associated with the LockBit 3.0 ransomware operation to load Cobalt Strike beacons onto potentially compromised systems and evade EDR and AV detection tools. The researchers found that Microsoft Defender's command line tool “MpCmdRun.exe” was abused to […] | Ransomware Tool Threat | |||
| 2022-07-27 21:58:53 | We\'re likely only seeing \'the tip of the iceberg\' of Pegasus spyware use against the US (lien direct) | House intel chair raises snoop tool concerns as Google and others call for greater crack down Google and internet rights groups have called on Congress to weigh in on spyware, asking for sanctions and increased enforcement against so-called legit surveillanceware makers.… | Tool | |||
| 2022-07-27 18:49:47 | Multiple Windows, Adobe Zero-Days Anchor Knotweed Commercial Spyware (lien direct) | Microsoft flagged the company's Subzero tool set as on offer to unscrupulous governments and shady business interests. | Tool | |||
| 2022-07-27 14:00:00 | The Great BizApp Hack: Cyber-Risks in Your Everyday Business Applications (lien direct) | IT admins can lock some of the obvious open doors in business applications, but system visibility is key. Build automatic monitoring defenses and adopt a Git-like tool so you can "version" your business apps to restore prior states. | Tool | |||
| 2022-07-27 12:57:00 | BrandPost: How a Cybersecurity Program Can Counter Configuration Drift (lien direct) | Once your organization is secured, you'll need to ensure that your environment doesn't stray from its protected state. Configuration drift may be inevitable, but you can leverage best practices to minimize its consequences.Why does configuration drift occur? Whether by choice or chance, change happens in IT environments. Software updates roll out, ad hoc decisions take effect, end users change settings, and new systems come in. When these decisions are made in haste, security considerations can be incomplete or missing altogether.Even if systems were secure to start with, the once-hardened IT environments develop “gaps” over time. It's not always easy to keep track of the changes that can lead to configuration drift. You'll need a management tool that provides you with a big (and granular) picture so that your team can effectively monitor and remedy the situation.To read this article in full, please click here | Tool Guideline | |||
| 2022-07-26 17:10:00 | Anomali Cyber Watch: Cozy Bear Abuses Google Drive API, Complex Lightning Framework Targets Linux, Google Ads Hide Fraudulent Redirects, and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: APT, Bots, China, Linux, Malspam, Mobil, Russia, and Spearhishing. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Lightning Framework: New Undetected “Swiss Army Knife” Linux Malware
(published: July 21, 2022)
Intezer researchers discovered a new Linux malware called Lightning Framework (Lightning). It is a modular framework able to install multiple types of rootkits and to run various plugins. Lightning has passive and active capabilities for communication with the threat actor, including opening up SSH service via an OpenSSH daemon, and a polymorphic command and control (C2) configuration. Lightning is a newly discovered threat, and there is no information about its use in the wild and the actors behind it.
Analyst Comment: Defenders should block known Lightning indicators. Monitor for file creation based on the Lightning naming convention.
MITRE ATT&CK: [MITRE ATT&CK] Logon Scripts - T1037 | [MITRE ATT&CK] Account Manipulation - T1098 | [MITRE ATT&CK] Obfuscated Files or Information - T1027 | [MITRE ATT&CK] Deobfuscate/Decode Files or Information - T1140 | [MITRE ATT&CK] Hide Artifacts - T1564 | [MITRE ATT&CK] Masquerading - T1036 | [MITRE ATT&CK] Rootkit - T1014 | [MITRE ATT&CK] Indicator Removal on Host - T1070 | [MITRE ATT&CK] File and Directory Discovery - T1083 | [MITRE ATT&CK] Network Service Scanning - T1046 | [MITRE ATT&CK] Network Sniffing - T1040 | [MITRE ATT&CK] System Information Discovery - T1082 | [MITRE ATT&CK] Data Encoding - T1132 | [MITRE ATT&CK] Standard Non-Application Layer Protocol - T1095 | [MITRE ATT&CK] Proxy - T1090 | [MITRE ATT&CK] Exfiltration Over C2 Channel - T1041
Tags: Lightning Framework, Linux, Lightning.Downloader, Lightning.Core, Typosquatting, Masquerading, Timestomping, Port:33229
Google Ads Lead to Major Malvertising Campaign
(published: July 20, 2022)
Malwarebytes researchers discovered a malvertising campaign abusing Google Search advertisements for popular keywords such as “amazon,” “fac
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Lightning Framework: New Undetected “Swiss Army Knife” Linux Malware
(published: July 21, 2022)
Intezer researchers discovered a new Linux malware called Lightning Framework (Lightning). It is a modular framework able to install multiple types of rootkits and to run various plugins. Lightning has passive and active capabilities for communication with the threat actor, including opening up SSH service via an OpenSSH daemon, and a polymorphic command and control (C2) configuration. Lightning is a newly discovered threat, and there is no information about its use in the wild and the actors behind it.
Analyst Comment: Defenders should block known Lightning indicators. Monitor for file creation based on the Lightning naming convention.
MITRE ATT&CK: [MITRE ATT&CK] Logon Scripts - T1037 | [MITRE ATT&CK] Account Manipulation - T1098 | [MITRE ATT&CK] Obfuscated Files or Information - T1027 | [MITRE ATT&CK] Deobfuscate/Decode Files or Information - T1140 | [MITRE ATT&CK] Hide Artifacts - T1564 | [MITRE ATT&CK] Masquerading - T1036 | [MITRE ATT&CK] Rootkit - T1014 | [MITRE ATT&CK] Indicator Removal on Host - T1070 | [MITRE ATT&CK] File and Directory Discovery - T1083 | [MITRE ATT&CK] Network Service Scanning - T1046 | [MITRE ATT&CK] Network Sniffing - T1040 | [MITRE ATT&CK] System Information Discovery - T1082 | [MITRE ATT&CK] Data Encoding - T1132 | [MITRE ATT&CK] Standard Non-Application Layer Protocol - T1095 | [MITRE ATT&CK] Proxy - T1090 | [MITRE ATT&CK] Exfiltration Over C2 Channel - T1041
Tags: Lightning Framework, Linux, Lightning.Downloader, Lightning.Core, Typosquatting, Masquerading, Timestomping, Port:33229
Google Ads Lead to Major Malvertising Campaign
(published: July 20, 2022)
Malwarebytes researchers discovered a malvertising campaign abusing Google Search advertisements for popular keywords such as “amazon,” “fac |
Malware Tool Threat Guideline | APT 29 | ||
| 2022-07-26 09:07:19 | Hitting ransomware for six: marking the anniversary of a valuable cybercrime tool (lien direct) | >For the past six years, a free project has helped ransomware victims to avoid paying criminals or suffering prolonged recovery times. Today marks the sixth anniversary of Europol's No More Ransom initiative. During the last decade, the threat of ransomware has ratcheted steadily upwards. Criminals are targeting organisations of all sizes across various industries, crippling ... | Ransomware Tool Threat | ★★★★ | ||
| 2022-07-26 00:00:00 | Better Together: AWS and Trend Micro (lien direct) | This post relays the latest threat detection tool innovation of AWS - Amazon GuardDuty Malware Protection. This tool works closely with Trend Micro cloud solutions, providing another valuable layer of defense in our fight against a shared adversary. | Malware Tool Threat |
To see everything:
Our RSS (filtrered)
