What's new arround internet
| Src | Date (GMT) | Titre | Description | Tags | Stories | Notes |
| 2021-04-21 19:08:01 | Inside Effective EDR Evaluation Testing (lien direct) |
 Periodically, I receive requests from customers asking for explanations on why this particular technique or that one doesn't generate a Malop™ in the Cybereason Defense Platform. Such questions illustrate that there is still a great deal of education to be done on the nature of EDR across much of the security industry.
Periodically, I receive requests from customers asking for explanations on why this particular technique or that one doesn't generate a Malop™ in the Cybereason Defense Platform. Such questions illustrate that there is still a great deal of education to be done on the nature of EDR across much of the security industry. |
||||
| 2021-04-21 14:16:50 | CISO Stories Podcast: He Fought the FTC Over a Breach and Won (lien direct) |
 Hopefully, you won't ever have to hire a lawyer to defend yourself against a government regulator. So what happens when the Federal Trade Commission or other powerful body baselessly accuses your company of wrongdoing where a data breach is concerned?
Hopefully, you won't ever have to hire a lawyer to defend yourself against a government regulator. So what happens when the Federal Trade Commission or other powerful body baselessly accuses your company of wrongdoing where a data breach is concerned? |
Data Breach | |||
| 2021-04-20 17:05:14 | Cybereason Excels in 2020 MITRE Engenuity ATT&CK Evaluations (lien direct) |
 The results of the latest ATT&CK Evaluation, conducted by MITRE Engenuity, are out! Our Cybereason Defense Platform was evaluated on its ability to prevent and detect advanced attacks, achieving 100% coverage for prevention of Windows and Linux-based threats, and 98% technique visibility across the 54 advanced attack techniques applied in testing. The MITRE Evaluation validates Cybereason's future-ready attack protection, and superior prevention, detection and response capabilities.
The results of the latest ATT&CK Evaluation, conducted by MITRE Engenuity, are out! Our Cybereason Defense Platform was evaluated on its ability to prevent and detect advanced attacks, achieving 100% coverage for prevention of Windows and Linux-based threats, and 98% technique visibility across the 54 advanced attack techniques applied in testing. The MITRE Evaluation validates Cybereason's future-ready attack protection, and superior prevention, detection and response capabilities. |
||||
| 2021-04-20 12:39:19 | Malicious Life Podcast: Shutting Down the Internet in 30 Minutes (lien direct) |
 Chris Wysopal (aka WeldPond), cybersecurity pioneer and one of L0pht's founding members, talks about the group's 1998 testimony in the Senate, how they used shaming to force corporations to secure their software, and the (not so fortunate) consequences of the acquisition by @stake - check it out...
Chris Wysopal (aka WeldPond), cybersecurity pioneer and one of L0pht's founding members, talks about the group's 1998 testimony in the Senate, how they used shaming to force corporations to secure their software, and the (not so fortunate) consequences of the acquisition by @stake - check it out... |
||||
| 2021-04-19 13:25:54 | Ransomware Decoded: Preventing Modern Ransomware Attacks (lien direct) |
 Many types of malware silently persist on the network, move laterally, communicate with their C2, or obfuscate their behaviors to prevent detection. In contrast to this, traditional ransomware was all about coming in with a big splash and causing immediate damage.
Many types of malware silently persist on the network, move laterally, communicate with their C2, or obfuscate their behaviors to prevent detection. In contrast to this, traditional ransomware was all about coming in with a big splash and causing immediate damage. |
Ransomware Malware | |||
| 2021-04-16 13:59:20 | Cybereason and MassCyberCenter Partner to Mentor College Students (lien direct) |
 Cybereason is pleased to announce that it has joined with the MassCyberCenter at the MassTech Collaborative and other Massachusetts companies to mentor college students from 14 schools across the state. Cybereason has three on-staff mentors, including: Sam Curry, Chief Security Officer, Lodrina Cherne, Principal Security Advocate and Maggie MacAlpine, Security Strategist.
Cybereason is pleased to announce that it has joined with the MassCyberCenter at the MassTech Collaborative and other Massachusetts companies to mentor college students from 14 schools across the state. Cybereason has three on-staff mentors, including: Sam Curry, Chief Security Officer, Lodrina Cherne, Principal Security Advocate and Maggie MacAlpine, Security Strategist. |
||||
| 2021-04-15 18:02:25 | MITRE ATT&CK Evaluations - Unpacking the Emulation (lien direct) |
 If you've been researching MITRE ATT&CK and aligning your security program maturity measurement to it, you're likely excited for this year's ATT&CK evaluation from MITRE Engenuity, which tests security vendors' ability to quickly detect and stop tactics and techniques used by today's threat actors.
If you've been researching MITRE ATT&CK and aligning your security program maturity measurement to it, you're likely excited for this year's ATT&CK evaluation from MITRE Engenuity, which tests security vendors' ability to quickly detect and stop tactics and techniques used by today's threat actors. |
Threat | |||
| 2021-04-15 13:13:18 | CISO Stories Podcast: Is There a Magic Security Control List? (lien direct) |
 Never in history has the cyber defender had access to so many technologies and tools to defend our companies. This has created a “Fog of More,” making the choices difficult to manage.
This week's guest is Tony Sager, a 35-year NSA software vulnerability analyst and executive, and the innovator of community-based controls sharing. Sager discusses how the CIS Controls can be used effectively to manage your environment - check it out...
Never in history has the cyber defender had access to so many technologies and tools to defend our companies. This has created a “Fog of More,” making the choices difficult to manage.
This week's guest is Tony Sager, a 35-year NSA software vulnerability analyst and executive, and the innovator of community-based controls sharing. Sager discusses how the CIS Controls can be used effectively to manage your environment - check it out... |
Vulnerability | |||
| 2021-04-14 18:47:09 | Biden Admin Takes Action to Defend Electric Utilities Against Cyberattacks (lien direct) |
 We live in a world of insecurity where malicious actors have for too long enjoyed an advantage over defenders charged with protecting their organization's networks from cyberattacks. Nowhere is that more evident than with critical infrastructure providers who are facing a constant barrage of attacks from motivated cybercriminals and well-funded state-sponsored actors.
We live in a world of insecurity where malicious actors have for too long enjoyed an advantage over defenders charged with protecting their organization's networks from cyberattacks. Nowhere is that more evident than with critical infrastructure providers who are facing a constant barrage of attacks from motivated cybercriminals and well-funded state-sponsored actors. |
||||
| 2021-04-14 13:01:39 | Rise of Double-Extortion Shines Spotlight on Ransomware Prevention (lien direct) |
 Double extortion is a tactic employed by some ransomware gangs. It begins when a crypto-malware strain steals information stored on a victim's machine before launching its encryption routine.
Double extortion is a tactic employed by some ransomware gangs. It begins when a crypto-malware strain steals information stored on a victim's machine before launching its encryption routine. |
Ransomware | |||
| 2021-04-13 13:42:55 | Malicious Life Podcast: The Story of LØpht Heavy Industries, Part 2 (lien direct) |
 In the early days, the L0pht crew tinkered with technology they already had laying around or could find dumpster-diving. But things change, of course. By the end of the '90s many of the L0pht hackers had quit their day jobs and incorporated under the name “L0pht Heavy Industries” while moving into a nicer space, the “new L0pht.”
In the early days, the L0pht crew tinkered with technology they already had laying around or could find dumpster-diving. But things change, of course. By the end of the '90s many of the L0pht hackers had quit their day jobs and incorporated under the name “L0pht Heavy Industries” while moving into a nicer space, the “new L0pht.” |
||||
| 2021-04-12 02:50:19 | Five Clear Steps to Enhance SecOps with MITRE ATT@CK (lien direct) |
 A skyrocketing number of alerts, limited security talent, and millions of new malware strains daily have made security a seemingly insurmountable task.
A skyrocketing number of alerts, limited security talent, and millions of new malware strains daily have made security a seemingly insurmountable task. |
Malware | |||
| 2021-04-08 14:28:16 | CISO Stories Podcast: Doing Security Before Security Was a Career Path (lien direct) |
 Special guest Petri Kuivala, CISO at NXP Semiconductors, recounts his journey from municipal police officer to cybercrimes unit investigator to Chief Information Security Officer during the early days when security was largely an afterthought - check it out...
Special guest Petri Kuivala, CISO at NXP Semiconductors, recounts his journey from municipal police officer to cybercrimes unit investigator to Chief Information Security Officer during the early days when security was largely an afterthought - check it out... |
||||
| 2021-04-07 13:19:32 | The Cybereason Difference: Introduction to the Malop (lien direct) |
 Welcome to the April edition of our series The Cybereason Difference (inaugural post here). Each post of this series explores a unique way that Cybereason empowers defenders.
Welcome to the April edition of our series The Cybereason Difference (inaugural post here). Each post of this series explores a unique way that Cybereason empowers defenders. |
||||
| 2021-04-06 14:27:20 | Malicious Life Podcast: The Story of L0pht Heavy Industries, Part 1 (lien direct) |
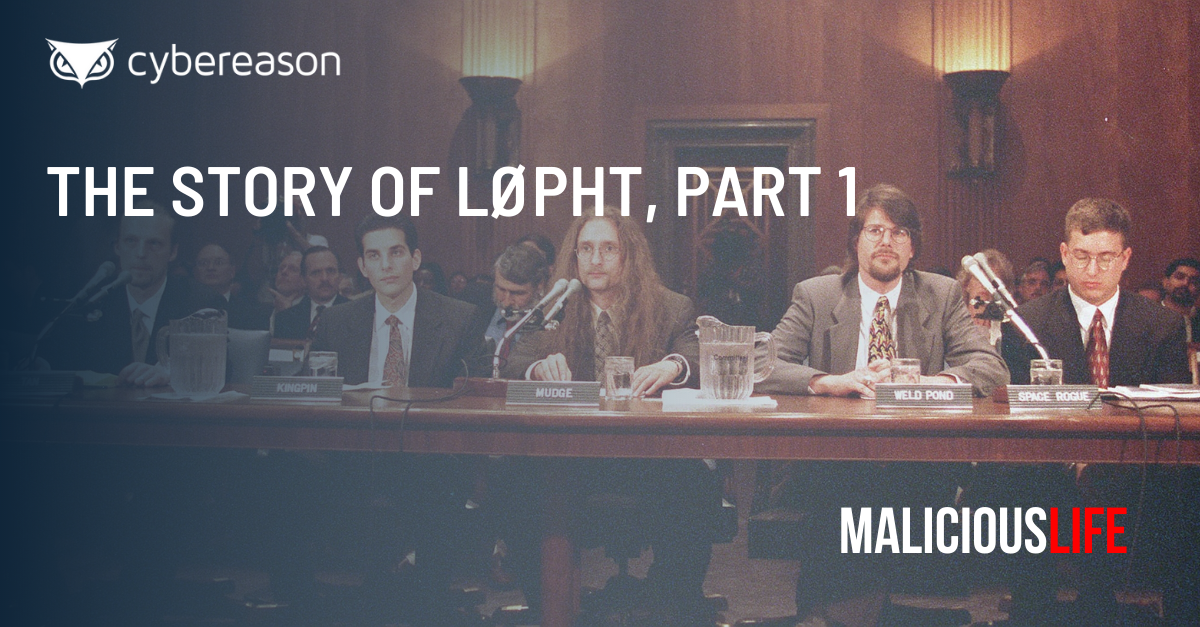 'L0pht', or 'L0pht Heavy Industries' was one of the most influential hacker collectives of the '90s: its members were even invited to testify in front of the Congress on the current state of Internet security.
'L0pht', or 'L0pht Heavy Industries' was one of the most influential hacker collectives of the '90s: its members were even invited to testify in front of the Congress on the current state of Internet security. |
||||
| 2021-04-06 13:39:57 | Cybereason Empowers Partners with North American MSSP Program Expansion (lien direct) |
 Cybereason is pleased to announce expansion of the North American channel with the launch of the Managed Security Services Provider (MSSP) Program. The program will support current and future partners by enhancing revenue streams through improved efficacy in detection and response services they offer to their clients.
Cybereason is pleased to announce expansion of the North American channel with the launch of the Managed Security Services Provider (MSSP) Program. The program will support current and future partners by enhancing revenue streams through improved efficacy in detection and response services they offer to their clients. |
||||
| 2021-04-05 21:23:44 | Personal Info for More Than Half a Billion Facebook Users Leaked Online (lien direct) |
 Someone leaked the phone numbers and personal information for over half a billion Facebook users online. Alon Gal, CTO at cybercrime intelligence firm Hudson Rock, tweeted out that someone had dumped hundreds of millions of Facebook records onto a hacking forum:
Someone leaked the phone numbers and personal information for over half a billion Facebook users online. Alon Gal, CTO at cybercrime intelligence firm Hudson Rock, tweeted out that someone had dumped hundreds of millions of Facebook records onto a hacking forum: |
||||
| 2021-04-05 17:01:42 | Ransomware Defense: Three Implementations Every Security Team Needs (lien direct) |
 Few will be shocked to hear that ransomware attacks are continuing to accelerate at a torrid pace - but the more concerning trend is the effectiveness of ransomware at creating chaos and paralyzing business operations.
Few will be shocked to hear that ransomware attacks are continuing to accelerate at a torrid pace - but the more concerning trend is the effectiveness of ransomware at creating chaos and paralyzing business operations. |
Ransomware | |||
| 2021-04-01 18:41:06 | CISO Stories Podcast: The Colonoscopy of CyberSecurity (lien direct) |
 The information and cybersecurity industry has no shortage of regulations, and many organizations simply rundown the list of requirements, load them into an excel spreadsheet and check the boxes to demonstrate they are in compliance. But is being compliant the same as being secure?
Join this podcast with special guest Lee Parrish who shares an analogy that illustrates why being compliant is not the same as being secure, and how we can change an organization's orientation to keep the focus on security - check it out...
The information and cybersecurity industry has no shortage of regulations, and many organizations simply rundown the list of requirements, load them into an excel spreadsheet and check the boxes to demonstrate they are in compliance. But is being compliant the same as being secure?
Join this podcast with special guest Lee Parrish who shares an analogy that illustrates why being compliant is not the same as being secure, and how we can change an organization's orientation to keep the focus on security - check it out... |
||||
| 2021-04-01 14:02:27 | Cybereason vs. DarkSide Ransomware (lien direct) |
 DarkSide is a relatively new ransomware strain that made its first appearance in August 2020. DarkSide follows the RaaS (ransomware-as-a-service) model, and, according to Hack Forums, the DarkSide team recently made an announcement that DarkSide 2.0 has been released. According to the group, it is equipped with the fastest encryption speed on the market, and even includes Windows and Linux versions.
DarkSide is a relatively new ransomware strain that made its first appearance in August 2020. DarkSide follows the RaaS (ransomware-as-a-service) model, and, according to Hack Forums, the DarkSide team recently made an announcement that DarkSide 2.0 has been released. According to the group, it is equipped with the fastest encryption speed on the market, and even includes Windows and Linux versions. |
Ransomware Hack | |||
| 2021-03-31 19:10:25 | Whistleblower Accuses Ubiquiti of Downplaying Major Data Breach (lien direct) |
 A security professional who assisted Ubiquiti in its response to a data breach accused the Internet-of-Things (IoT) device vendor of having downplayed the incident's severity.
A security professional who assisted Ubiquiti in its response to a data breach accused the Internet-of-Things (IoT) device vendor of having downplayed the incident's severity. |
Data Breach | |||
| 2021-03-31 16:34:21 | FBI Pegs 2020 Cybercrime Costs at $4 Billion - Actual Losses Likely Higher (lien direct) |
 Cybercrime cost the American public over $4 billion in reported losses over the course of 2020, according to the FBI. In its Internet Crime Report 2020, the FBI's Internet Crime Complaint Center (IC3) revealed that it had received 791,790 complaints of digital crime in 2020.
Cybercrime cost the American public over $4 billion in reported losses over the course of 2020, according to the FBI. In its Internet Crime Report 2020, the FBI's Internet Crime Complaint Center (IC3) revealed that it had received 791,790 complaints of digital crime in 2020. |
||||
| 2021-03-30 17:26:15 | DearCry Ransomware and the HAFNIUM Attacks – What You Need to Know (lien direct) |
 The widespread HAFNIUM attacks were just the beginning of the problems stemming from multiple vulnerabilities in Microsoft's Exchange offering that were recently disclosed. According to Bleeping Computer, users began submitting new ransomware attack reports to the ID-Ransomware identification site on March 9 that site creator Michael Gillespie later determined had likely originated on Microsoft Exchange servers.
The widespread HAFNIUM attacks were just the beginning of the problems stemming from multiple vulnerabilities in Microsoft's Exchange offering that were recently disclosed. According to Bleeping Computer, users began submitting new ransomware attack reports to the ID-Ransomware identification site on March 9 that site creator Michael Gillespie later determined had likely originated on Microsoft Exchange servers. |
Ransomware | |||
| 2021-03-29 13:08:15 | Why Healthcare Security Requires an Operation-Centric Approach (lien direct) |
 The healthcare industry is getting much more attention than normal right now. COVID-19 has disrupted business operations and turned lives upside down around the world as everyone struggles to get the pandemic under control.
The healthcare industry is getting much more attention than normal right now. COVID-19 has disrupted business operations and turned lives upside down around the world as everyone struggles to get the pandemic under control. |
||||
| 2021-03-26 14:48:04 | CISO Stories Podcast: Going All-In on a Career in Security (lien direct) |
 Mauro Israel, CISO at BIOOOS, discusses his colorful background and how he – like so many others in the security field – came to discover his true calling late in life and was able to apply his wide range of knowledge and experience to the role of CISO in the healthcare field - check it out..
Mauro Israel, CISO at BIOOOS, discusses his colorful background and how he – like so many others in the security field – came to discover his true calling late in life and was able to apply his wide range of knowledge and experience to the role of CISO in the healthcare field - check it out.. |
||||
| 2021-03-24 14:36:34 | Cybereason Named a Strong Performer in Forrester Wave for MDR (lien direct) |
 The Cybereason Managed Detection and Response (MDR) service offering has been named a Strong Performer in the Forrester Wave™: Managed Detection and Response, Q1 2021 report.
The Cybereason Managed Detection and Response (MDR) service offering has been named a Strong Performer in the Forrester Wave™: Managed Detection and Response, Q1 2021 report. |
||||
| 2021-03-23 18:00:09 | Malicious Life Podcast: Inside the HAFNIUM Microsoft Exchange Attacks (lien direct) |
 The recent HAFNIUM attacks hit tens of thousands of organizations' Microsoft Exchange servers around the globe. Now, an array of other threat actors are leveraging the residual webshells on victim systems to launch new attacks against organizations who thought patching the Microsoft vulnerabilities would have been enough to be protected.
The recent HAFNIUM attacks hit tens of thousands of organizations' Microsoft Exchange servers around the globe. Now, an array of other threat actors are leveraging the residual webshells on victim systems to launch new attacks against organizations who thought patching the Microsoft vulnerabilities would have been enough to be protected. |
Threat Patching | |||
| 2021-03-23 16:54:20 | Sodinokibi/REvil Ransomware Gang Hit Acer with $50M Ransom Demand (lien direct) |
 The Sodinokibi/REvil ransomware gang has reportedly infected Taiwanese multinational electronics corporation Acer and demanded a ransom of $50 million. Those responsible for the Sodinokibi ransomware strain announced on their data leaks website that they had breached the computer giant.
The Sodinokibi/REvil ransomware gang has reportedly infected Taiwanese multinational electronics corporation Acer and demanded a ransom of $50 million. Those responsible for the Sodinokibi ransomware strain announced on their data leaks website that they had breached the computer giant. |
Ransomware | |||
| 2021-03-22 13:08:36 | Malicious Life Podcast: Inside NotPetya, Part 2 (lien direct) |
 Many of you may have already heard of Amit Serper: he was the first researcher to tackle NotPetya and provide a solution when he was Principal Security Researcher at Cybereason back in 2017.
Many of you may have already heard of Amit Serper: he was the first researcher to tackle NotPetya and provide a solution when he was Principal Security Researcher at Cybereason back in 2017. |
NotPetya NotPetya | |||
| 2021-03-18 15:27:30 | HAFNIUM Response: Cybereason is Dedicated to Defending Our Customers (lien direct) |
 It was recently disclosed that Microsoft Exchange offerings were severely compromised in nation-state sponsored operations by the threat group known as HAFNIUM. This incident has potentially affected tens-of-thousands of public and private organizations across the globe.
It was recently disclosed that Microsoft Exchange offerings were severely compromised in nation-state sponsored operations by the threat group known as HAFNIUM. This incident has potentially affected tens-of-thousands of public and private organizations across the globe. |
Threat | |||
| 2021-03-18 10:04:34 | Cybereason Exposes Campaign Targeting US Taxpayers with NetWire and Remcos Malware (lien direct) |
 Over the past year, the Cybereason Nocturnus Team has observed various trends among cyber criminals and nation-state groups leveraging various global events such as COVID-19 and other topical themes and trending issues as phishing content to lure their victims into installing their malware of choice.
Over the past year, the Cybereason Nocturnus Team has observed various trends among cyber criminals and nation-state groups leveraging various global events such as COVID-19 and other topical themes and trending issues as phishing content to lure their victims into installing their malware of choice. |
Malware | |||
| 2021-03-17 13:00:00 | CISO Stories Podcast: Is Cybersecurity ROI Necessary? (lien direct) |
 Business units are often challenged to demonstrate ROI on their spend for various initiatives. Why should the information security department be any different?
Business units are often challenged to demonstrate ROI on their spend for various initiatives. Why should the information security department be any different? |
||||
| 2021-03-16 16:03:52 | Security CEO Roundtable: Restoring Our National Cybersecurity (lien direct) |
 Now that President Biden has proposed the allocation of $10 Billion for cyber security and IT modernization, what specifically should the federal government focus on to restore confidence in our national cyber security defense posture?
Now that President Biden has proposed the allocation of $10 Billion for cyber security and IT modernization, what specifically should the federal government focus on to restore confidence in our national cyber security defense posture? |
||||
| 2021-03-16 14:09:52 | Webinar: Protecting Against IT Infrastructure Attacks from HAFNIUM to SolarWinds (lien direct) |
 Attackers have proven time and again they are willing to innovate in nefarious ways to breach your defenses - as seen with the most recent headlines around the recent Microsoft Exchange and SolarWinds attacks.
Attackers have proven time and again they are willing to innovate in nefarious ways to breach your defenses - as seen with the most recent headlines around the recent Microsoft Exchange and SolarWinds attacks. |
||||
| 2021-03-15 13:00:00 | SolarWinds Attacks Recovery Effort Could Take U.S. Government 18 Months (lien direct) |
 The U.S. government could take up to 18 months in its efforts to recover from the SolarWinds supply chain attack, explained the U.S. Cybersecurity & Infrastructure Security Agency (CISA).
The U.S. government could take up to 18 months in its efforts to recover from the SolarWinds supply chain attack, explained the U.S. Cybersecurity & Infrastructure Security Agency (CISA). |
||||
| 2021-03-12 16:31:30 | Webinar: The State of Ransomware (lien direct) |
 Ransomware continues to evolve and despite what many in the industry had thought was a lull in the use of ransomware by cyber criminals; it hasn't gone away and has returned with a vengeance.
Ransomware continues to evolve and despite what many in the industry had thought was a lull in the use of ransomware by cyber criminals; it hasn't gone away and has returned with a vengeance. |
Ransomware | |||
| 2021-03-12 15:15:23 | International Women\'s Day: Why Be Daring? (lien direct) |
 International Women's Day always makes me reflect about my career path and decisions, and I wonder if just the fact that I'm a woman makes them interesting. I hope not.
International Women's Day always makes me reflect about my career path and decisions, and I wonder if just the fact that I'm a woman makes them interesting. I hope not. |
||||
| 2021-03-11 17:36:05 | Live Feeds of 150K Surveillance Cameras Compromised in Verkada Breach (lien direct) |
 Digital attackers compromised the live feeds of 150,000 surveillance cameras made by enterprise security camera system manufacturer Verkada. According to Bloomberg News, a hacking collective that calls itself “Advanced Persistent Threat 69420” gained access to Verkada by misusing a “Super Admin” account at the company.
Digital attackers compromised the live feeds of 150,000 surveillance cameras made by enterprise security camera system manufacturer Verkada. According to Bloomberg News, a hacking collective that calls itself “Advanced Persistent Threat 69420” gained access to Verkada by misusing a “Super Admin” account at the company. |
Threat | |||
| 2021-03-11 13:38:02 | International Women\'s Day: Girls Should Never Give Up (lien direct) |
 “What do you want to be one day, Jean?”
“What do you want to be one day, Jean?” |
||||
| 2021-03-10 15:00:00 | CISO Stories Podcast: Your Job is to Make Cybersecurity Simple (lien direct) |
 The CISO position in some organizations is relatively new, but the role has actually been evolving over the past 25 years - ever since Citibank named the first CISO, Steve Katz, in 1995. Join this podcast to learn how Steve navigated the early days of security and the changes he sees in the role today...
The CISO position in some organizations is relatively new, but the role has actually been evolving over the past 25 years - ever since Citibank named the first CISO, Steve Katz, in 1995. Join this podcast to learn how Steve navigated the early days of security and the changes he sees in the role today... |
||||
| 2021-03-10 14:00:00 | International Women\'s Day: “Win as One” Takes True Commitment to Diversity (lien direct) |
 “As a woman...” I haven't really used that phrase for very long. Eight years ago, I came out as a transgender woman, very late in life. And even today I find myself fighting forty years of my own preconceived notions of what I had to be in order to say those words.
“As a woman...” I haven't really used that phrase for very long. Eight years ago, I came out as a transgender woman, very late in life. And even today I find myself fighting forty years of my own preconceived notions of what I had to be in order to say those words. |
||||
| 2021-03-09 15:00:00 | International Women\'s Day: Culture Add Over Culture Fit as a Catalyst for Diversity (lien direct) |
 Having worked in Human Resources my entire career, the notion of Culture Fit became near and dear to me throughout my career. Leadership teams would comment on needing to hire those who were a Culture Fit, hiring managers would request it, and recruiters would screen hundreds of candidates to try to ensure the people they presented truly fit the company's culture.
Having worked in Human Resources my entire career, the notion of Culture Fit became near and dear to me throughout my career. Leadership teams would comment on needing to hire those who were a Culture Fit, hiring managers would request it, and recruiters would screen hundreds of candidates to try to ensure the people they presented truly fit the company's culture. |
Guideline | |||
| 2021-03-09 14:00:00 | Cybereason Expands in the DACH Region with Bechtle AG Partnership (lien direct) |
 Cybereason is pleased to announce a strategic partnership with Bechtle AG to facilitate expansion across the DACH region of Germany, Austria and Switzerland to better protect enterprises against sophisticated cyber attacks on endpoints and everywhere in their networks.
Cybereason is pleased to announce a strategic partnership with Bechtle AG to facilitate expansion across the DACH region of Germany, Austria and Switzerland to better protect enterprises against sophisticated cyber attacks on endpoints and everywhere in their networks. |
||||
| 2021-03-08 20:27:29 | HAFNIUM and SolarWinds Attacks Highlight Lack of Accountability (lien direct) | On the heels of the SolarWinds supply chain attacks, organizations are again scrambling to assess the impact of a recently disclosed attack attributed to the Chinese state-sponsored HAFNIUM APT group that targets vulnerabilities in Microsoft Exchange servers with two zero-day exploits. Perhaps it's time we accept that there's a war going on, and that this war is being fought on the backs of commercial companies who are targeted by sophisticated, military-grade offensive campaigns. | ||||
| 2021-03-08 14:00:00 | International Women\'s Day: UbU and Lead Like a Girl (lien direct) |
 Rewind to 2012: Sheryl Sandberg's Lean In had just been published, pushing women to stop sitting back and start taking more risks. Amy Cuddy had just come out with her “Power Pose” TED Talk telling women that posing like Superwoman for two minutes can make you feel more powerful.
Rewind to 2012: Sheryl Sandberg's Lean In had just been published, pushing women to stop sitting back and start taking more risks. Amy Cuddy had just come out with her “Power Pose” TED Talk telling women that posing like Superwoman for two minutes can make you feel more powerful. |
Guideline | |||
| 2021-03-04 14:00:00 | CISO Stories Podcast: …and Other Useless Security Constructs (lien direct) |
 Bob Bigman, former CISO for the CIA, simplifies the conversation by slaughtering some of the industry's most sacred cows like risk tolerance as a key driver for security programs - check it out…
Bob Bigman, former CISO for the CIA, simplifies the conversation by slaughtering some of the industry's most sacred cows like risk tolerance as a key driver for security programs - check it out… |
||||
| 2021-03-03 14:00:00 | Malicious Life Podcast: Inside NotPetya, Part 1 (lien direct) |
 On June 28th, 2017, millions of Ukrainians were celebrating Constitution Day. Their national holiday turned into a nightmare, as tens of thousands of computers all over the country were infected by mysterious malware. By that afternoon, the cyber-pandemic was already going global.
On June 28th, 2017, millions of Ukrainians were celebrating Constitution Day. Their national holiday turned into a nightmare, as tens of thousands of computers all over the country were infected by mysterious malware. By that afternoon, the cyber-pandemic was already going global. |
NotPetya | |||
| 2021-03-02 14:29:11 | Defender Spotlight: Keith Barros, Seton Hall University (lien direct) |
 Top-tier defender Keith Barros of Seton Hall University discusses the successes SHU has achieved with a deployment of Cybereason solutions to secure endpoints and ramp-up students to Level1 Analyst level performance.
Top-tier defender Keith Barros of Seton Hall University discusses the successes SHU has achieved with a deployment of Cybereason solutions to secure endpoints and ramp-up students to Level1 Analyst level performance. |
||||
| 2021-03-01 14:00:00 | CISO Stories Podcast: Without Building a CISO EQ, You May Be On Your Own (lien direct) |
 The CISO must interact with many different groups within the company. These groups differ in the amount of business acumen and technical depth necessary. The CISO must have self-awareness of how to approach each of these different types of stakeholders, as well as ensuring appropriate self-care is taken to limit burnout, stress and anxiety.
The CISO must interact with many different groups within the company. These groups differ in the amount of business acumen and technical depth necessary. The CISO must have self-awareness of how to approach each of these different types of stakeholders, as well as ensuring appropriate self-care is taken to limit burnout, stress and anxiety. |
||||
| 2021-02-25 14:00:00 | CISO Stories Podcast: Doing Privacy Right vs. Doing Privacy Rights (lien direct) |
 Eric Schmidt (CEO Google 2001-2007) famously noted that his company's policy was to get 'right up to the creepy line and not cross it.' The closer an organization can get to this imaginary line, the greater the profit maximization. When does this become an invasion of privacy?
Eric Schmidt (CEO Google 2001-2007) famously noted that his company's policy was to get 'right up to the creepy line and not cross it.' The closer an organization can get to this imaginary line, the greater the profit maximization. When does this become an invasion of privacy? |
To see everything:
Our RSS (filtrered)
