What's new arround internet
| Src | Date (GMT) | Titre | Description | Tags | Stories | Notes |
| 2021-08-11 12:47:11 | CISO Stories Podcast: Hacking Your Way Into Cybersecurity (lien direct) |
 Kerissa Varma is Group Chief Information Security Officer of Old Mutual Limited, one of the largest financial services organizations on the African continent. Kerissa joins the show to discuss the cybersecurity skills shortage and her initiative to recruit brilliant minds from across an array of fields who have skill sets applicable to cybersecurity, but they might not even know it - check it out...
Kerissa Varma is Group Chief Information Security Officer of Old Mutual Limited, one of the largest financial services organizations on the African continent. Kerissa joins the show to discuss the cybersecurity skills shortage and her initiative to recruit brilliant minds from across an array of fields who have skill sets applicable to cybersecurity, but they might not even know it - check it out... |
||||
| 2021-08-10 18:17:00 | Webinar: REvil Ransomware - Pick Your Path (lien direct) |
 Today's ransomware actors are operating to devastating effect as evidenced by the Colonial Pipeline and JBS attacks, showing that a successful attack can disrupt any business.
Today's ransomware actors are operating to devastating effect as evidenced by the Colonial Pipeline and JBS attacks, showing that a successful attack can disrupt any business. |
Ransomware | |||
| 2021-08-10 12:56:59 | Who Are the Main Targets of Ransomware Attacks? (lien direct) |
 In our ransomware report, titled Ransomware: The True Cost to Business, 81% of respondents indicated that they are highly or very concerned about the risk of ransomware attacks. That's not a surprise given the growing ransomware threat.
In our ransomware report, titled Ransomware: The True Cost to Business, 81% of respondents indicated that they are highly or very concerned about the risk of ransomware attacks. That's not a surprise given the growing ransomware threat. |
Ransomware | |||
| 2021-08-09 12:18:15 | XDR: The Next Step in Threat Detection and Response (lien direct) |
 The global EDR market (Endpoint Detection and Response) is growing rapidly. The Transparency Market Research team predicted that this market will increase at a CAGR of about 21% in the next decade, reported Help Net Security. If it happens, this growth will help the global EDR market surpass a valuation of $13.8 billion by 2030.
The global EDR market (Endpoint Detection and Response) is growing rapidly. The Transparency Market Research team predicted that this market will increase at a CAGR of about 21% in the next decade, reported Help Net Security. If it happens, this growth will help the global EDR market surpass a valuation of $13.8 billion by 2030. |
Threat | |||
| 2021-08-09 12:04:26 | Malicious Life Podcast: The Jester - Hacktivist for Good (lien direct) |
 The Jester is a patriotic, pro-American Hacktivist that since 2010 has waged a personal cyberwar against an array of targets he considers to be “the bad guys.” But detractors have insinuated that some of the Jester's operations were little more than internet sleight-of-hand. So, who is The Jester and what can we make of his reported exploits? Check it out…
The Jester is a patriotic, pro-American Hacktivist that since 2010 has waged a personal cyberwar against an array of targets he considers to be “the bad guys.” But detractors have insinuated that some of the Jester's operations were little more than internet sleight-of-hand. So, who is The Jester and what can we make of his reported exploits? Check it out… |
||||
| 2021-08-06 16:32:00 | \'DeadRinger\' Reveals Pervasive Cyber Espionage Campaign (lien direct) |
 In the summer of 2019, our researchers discovered a massive malicious campaign against telecommunications providers that we dubbed Operation Soft Cell. This week, our researchers revealed details of more pervasive attacks against telecommunications providers. The DeadRinger report reveals a cyber espionage campaign out of China targeting providers in Southeast Asia.
In the summer of 2019, our researchers discovered a massive malicious campaign against telecommunications providers that we dubbed Operation Soft Cell. This week, our researchers revealed details of more pervasive attacks against telecommunications providers. The DeadRinger report reveals a cyber espionage campaign out of China targeting providers in Southeast Asia. |
||||
| 2021-08-05 12:55:48 | CISO Stories Podcast: Managing the Security Product Salesperson (lien direct) |
 CISOs are approached frequently by salespersons seeking to sell products that are supposed to reduce risk. How should a CISO manage these relationships? Kevin Morrison, CISO at Alaska Air Group, joins the podcast to discuss strategies for dealing with salespeople and selecting the best products for the organization - check it out...
CISOs are approached frequently by salespersons seeking to sell products that are supposed to reduce risk. How should a CISO manage these relationships? Kevin Morrison, CISO at Alaska Air Group, joins the podcast to discuss strategies for dealing with salespeople and selecting the best products for the organization - check it out... |
||||
| 2021-08-04 12:37:12 | Partners in Crime: How Ransomware Gangs Are Working Together (lien direct) |
 By now, it's clear that paying the ransom won't necessarily help ransomware victims to recover their data. Paying up also doesn't guarantee that victims will be safe from secondary attacks. According to our ransomware report, 80% of organizations that opted to pay a ransom demand ended up suffering another attack. Nearly half (46%) of those victims said they believed that the same attackers had infected them again, while 34% felt that it might have been someone else.
By now, it's clear that paying the ransom won't necessarily help ransomware victims to recover their data. Paying up also doesn't guarantee that victims will be safe from secondary attacks. According to our ransomware report, 80% of organizations that opted to pay a ransom demand ended up suffering another attack. Nearly half (46%) of those victims said they believed that the same attackers had infected them again, while 34% felt that it might have been someone else. |
Ransomware | |||
| 2021-08-03 04:03:00 | DeadRinger: Exposing Chinese Threat Actors Targeting Major Telcos (lien direct) |
 Following the discovery of Hafnium attacks targeting Microsoft Exchange vulnerabilities, the Cybereason Nocturnus and Incident Response teams proactively hunted for various threat actors trying to leverage similar techniques in-the-wild. In the beginning of 2021, the Cybereason Nocturnus Team investigated clusters of intrusions detected targeting the telecommunications industry across Southeast Asia. During the investigation, three clusters of activity were identified and showed significant connections to known threat actors, all suspected to be operating on behalf of Chinese state interests.
The report comes on the heels of the Biden administration's public rebuke of China's Ministry of State Security for the recent HAFNIUM attacks that exploited vulnerabilities in unpatched Microsoft Exchange Servers and put thousands of organizations worldwide at risk. Exploitation of these same vulnerabilities were central to the success of the attacks detailed in this research.
Following the discovery of Hafnium attacks targeting Microsoft Exchange vulnerabilities, the Cybereason Nocturnus and Incident Response teams proactively hunted for various threat actors trying to leverage similar techniques in-the-wild. In the beginning of 2021, the Cybereason Nocturnus Team investigated clusters of intrusions detected targeting the telecommunications industry across Southeast Asia. During the investigation, three clusters of activity were identified and showed significant connections to known threat actors, all suspected to be operating on behalf of Chinese state interests.
The report comes on the heels of the Biden administration's public rebuke of China's Ministry of State Security for the recent HAFNIUM attacks that exploited vulnerabilities in unpatched Microsoft Exchange Servers and put thousands of organizations worldwide at risk. Exploitation of these same vulnerabilities were central to the success of the attacks detailed in this research. |
Threat | |||
| 2021-08-03 04:00:17 | Webinar: DeadRinger - Exposing Chinese Threat Actors Targeting Major Telcos (lien direct) |
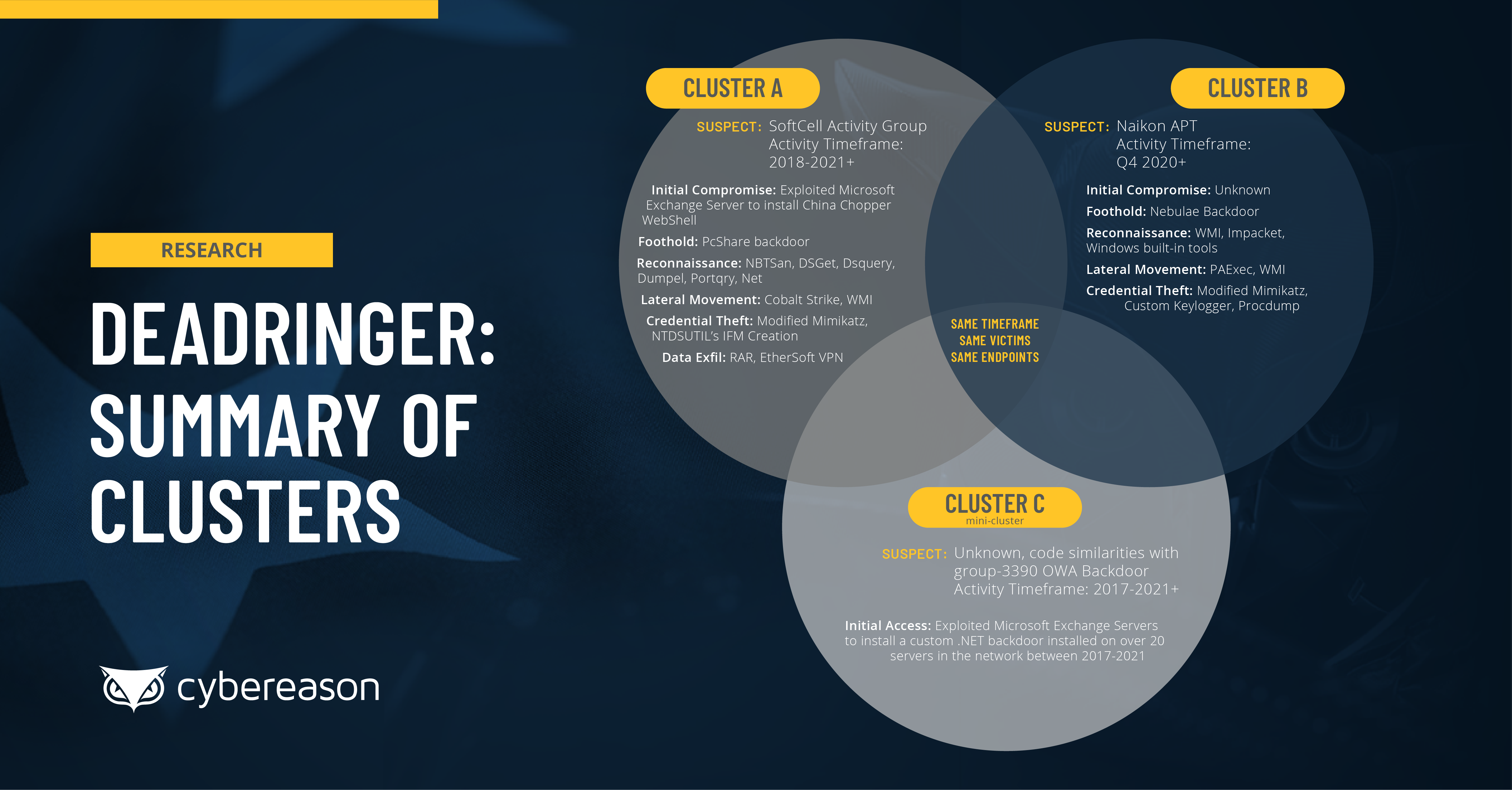 The Cybereason Nocturnus Research Team recently released a major threat intelligence research report titled DeadRinger: Exposing Chinese Threat Actors Targeting Major Telcos, which details the discovery of several previously unidentified attack campaigns targeting the telecommunications industry across Southeast Asia, where several clusters of attack activity were identified and assessed to be the work of several prominent APT groups who are known to conduct operations aligned with the interests of the Chinese government.
The Cybereason Nocturnus Research Team recently released a major threat intelligence research report titled DeadRinger: Exposing Chinese Threat Actors Targeting Major Telcos, which details the discovery of several previously unidentified attack campaigns targeting the telecommunications industry across Southeast Asia, where several clusters of attack activity were identified and assessed to be the work of several prominent APT groups who are known to conduct operations aligned with the interests of the Chinese government. |
Threat | |||
| 2021-08-02 12:07:17 | (Déjà vu) What the Growing Costs of a Data Breach Means for the Business (lien direct) |
 A recent global research report conducted by Cybereason, titled Ransomware: The True Cost to Business, revealed that the vast majority of organizations that have suffered a ransomware attack have experienced significant impact to the business, including loss of revenue, damage to the organization's brand, unplanned workforce reductions, and little in the way of relief from cyber insurance policies.
An esteemed panel of subject matter experts will examine the research findings and discuss how organizations can better prepare to defend against and respond to a ransomware attack, and the full on-demand webinar can be found here.
Recently, IBM came out with its Cost of a Data Breach Report 2021. This publication synthesizes the Ponemon Institute's research of 537 breaches that affected 17 different industries and that occurred across 17 countries and regions. It also draws on nearly 3,500 interviews to understand how much those breaches cost organizations and what decision makers are doing to better defend against security incidents going forward.
A recent global research report conducted by Cybereason, titled Ransomware: The True Cost to Business, revealed that the vast majority of organizations that have suffered a ransomware attack have experienced significant impact to the business, including loss of revenue, damage to the organization's brand, unplanned workforce reductions, and little in the way of relief from cyber insurance policies.
An esteemed panel of subject matter experts will examine the research findings and discuss how organizations can better prepare to defend against and respond to a ransomware attack, and the full on-demand webinar can be found here.
Recently, IBM came out with its Cost of a Data Breach Report 2021. This publication synthesizes the Ponemon Institute's research of 537 breaches that affected 17 different industries and that occurred across 17 countries and regions. It also draws on nearly 3,500 interviews to understand how much those breaches cost organizations and what decision makers are doing to better defend against security incidents going forward. |
Ransomware Data Breach | |||
| 2021-08-02 12:04:49 | Malicious Life Podcast: The State of Credit Card Security (lien direct) |
 In 2005, when Albert Gonzalez was hacking his way into the networks of many retail chains in the US (listen to Part 1, Part 2 and Part 3), credit cards were still very insecure: magnetic stripes and signed receipts did little to stop smart hackers such as Gonzalez and his crew.
In 2005, when Albert Gonzalez was hacking his way into the networks of many retail chains in the US (listen to Part 1, Part 2 and Part 3), credit cards were still very insecure: magnetic stripes and signed receipts did little to stop smart hackers such as Gonzalez and his crew. |
||||
| 2021-07-30 20:20:45 | (Déjà vu) CISO Stories Podcast: Ransomware Attacks and the True Cost to Business (lien direct) |
 A recent global research report conducted by Cybereason, titled Ransomware: The True Cost to Business, revealed that the vast majority of organizations that have suffered a ransomware attack have experienced significant impact to the business, including loss of revenue, damage to the organization's brand, unplanned workforce reductions, and little in the way of relief from cyber insurance policies.
A recent global research report conducted by Cybereason, titled Ransomware: The True Cost to Business, revealed that the vast majority of organizations that have suffered a ransomware attack have experienced significant impact to the business, including loss of revenue, damage to the organization's brand, unplanned workforce reductions, and little in the way of relief from cyber insurance policies. |
Ransomware | |||
| 2021-07-29 13:45:07 | Cybereason Offers Comprehensive Visibility and Protection for Diverse Systems (lien direct) |
 As enterprise technical infrastructures become more complex, managing them grows increasingly difficult. Protection against the growing problem of cybercrime also remains a key aspect for anyone involved in IT management. Cybersecurity considerations are especially critical for organizations involved in Customer Experience Automation and CRM, such as my company ActiveCampaign.
As enterprise technical infrastructures become more complex, managing them grows increasingly difficult. Protection against the growing problem of cybercrime also remains a key aspect for anyone involved in IT management. Cybersecurity considerations are especially critical for organizations involved in Customer Experience Automation and CRM, such as my company ActiveCampaign. |
||||
| 2021-07-28 12:33:28 | CISO Stories Podcast: Developing Secure Agile Code Quickly is Very Achievable (lien direct) |
 Speed to market is the mantra of software development today. This does not mean that a process is not followed, it means that an iterative approach to software development produces code changes and usable code much faster.
Speed to market is the mantra of software development today. This does not mean that a process is not followed, it means that an iterative approach to software development produces code changes and usable code much faster. |
||||
| 2021-07-27 12:56:20 | The XDR Advantage: Eliminate Dwell Time and Gain Visibility (lien direct) |
 The average cost of a data breach in 2020 was $3.86 million, according to IBM. It was even more expensive for certain entities. Indeed, that cost rose to $8.64 million when attackers succeeded in breaching an organization located in the United States. It was the same story in the healthcare industry, with the cost of data breaches climbing to $7.13 million for affected entities.
The average cost of a data breach in 2020 was $3.86 million, according to IBM. It was even more expensive for certain entities. Indeed, that cost rose to $8.64 million when attackers succeeded in breaching an organization located in the United States. It was the same story in the healthcare industry, with the cost of data breaches climbing to $7.13 million for affected entities.
|
Data Breach | |||
| 2021-07-26 12:01:59 | Malicious Life Podcast: The Life and Exploits of Albert Gonzales Part 3 (lien direct) |
 In this third installment of the series (Part 1, Part 2), we come back to the story in early 2007 when a Secret Service agent operating out of San Diego takes a flight halfway across the world. He's going to meet with Europe's most prolific stolen credit card salesman. It is this meeting that will be the beginning of the end for Albert Gonzalez and his 'All Star' crew of hackers, international businessmen and mules.
In this third installment of the series (Part 1, Part 2), we come back to the story in early 2007 when a Secret Service agent operating out of San Diego takes a flight halfway across the world. He's going to meet with Europe's most prolific stolen credit card salesman. It is this meeting that will be the beginning of the end for Albert Gonzalez and his 'All Star' crew of hackers, international businessmen and mules. |
||||
| 2021-07-22 13:06:52 | CISO Stories Podcast: Protecting the Crown Jewels (lien direct) |
 The crown jewels are those assets representing the highest value to the organization and deserve the greatest investment to protect. Join this podcast with special guest Steve Durbin, Chief Executive at ISF, to learn the importance of protecting these assets throughout the information life cycle - check it out...
The crown jewels are those assets representing the highest value to the organization and deserve the greatest investment to protect. Join this podcast with special guest Steve Durbin, Chief Executive at ISF, to learn the importance of protecting these assets throughout the information life cycle - check it out... |
||||
| 2021-07-22 12:00:00 | Cybereason and CYDERES Partner to Deliver Managed Detection and Response (lien direct) |
 Cybereason is thrilled to announce a strategic partnership with CYDERES, the security-as-a-service division of Fishtech Group and a Top 25 MSSP, to bring enhanced Managed Detection and Response (MDR) to our current and future managed security customers.
Cybereason is thrilled to announce a strategic partnership with CYDERES, the security-as-a-service division of Fishtech Group and a Top 25 MSSP, to bring enhanced Managed Detection and Response (MDR) to our current and future managed security customers. |
||||
| 2021-07-21 20:34:32 | Everything Cybereason at the Black Hat 2021 Virtual Conference (lien direct) |
 The Cybereason team is excited to have you join us at Black Hat 2021 on August 4th from 8:30AM to 5PM PST, and on August 5th from 8:30AM to 4PM PST! Stop by the “virtual” Cybereason booth and automatically be entered to win a Sonos Roam Speaker and other great freebies!
The Cybereason team is excited to have you join us at Black Hat 2021 on August 4th from 8:30AM to 5PM PST, and on August 5th from 8:30AM to 4PM PST! Stop by the “virtual” Cybereason booth and automatically be entered to win a Sonos Roam Speaker and other great freebies! |
||||
| 2021-07-21 13:43:27 | Three Ransomware Attacks that Upped the Ante (lien direct) |
 Concern surrounding ransomware attacks is high in the security industry. In our recent global research report titled Ransomware: The True Cost to Business, we found that 81% of the 1,200+ cybersecurity professionals we surveyed were highly or very concerned about the risk of ransomware.
Concern surrounding ransomware attacks is high in the security industry. In our recent global research report titled Ransomware: The True Cost to Business, we found that 81% of the 1,200+ cybersecurity professionals we surveyed were highly or very concerned about the risk of ransomware. |
Ransomware | |||
| 2021-07-20 09:00:00 | Cybereason Enhances XDR Offering with empow Acquisition (lien direct) |
 Today's targeted attacks increasingly take aim at multiple devices and users simultaneously while employing a range of tactics, techniques and procedures (TTPs). To further complicate the work of the defender, traditional security solutions are alert-centric, generating an ever-growing volume of notifications that lack context and fail to correlate to one another even if part of the same attack. This alert-centric, siloed approach gives attackers ample opportunity to hide in the seams, which makes hunting, tracking and eliminating attackers all but impossible.
Today's targeted attacks increasingly take aim at multiple devices and users simultaneously while employing a range of tactics, techniques and procedures (TTPs). To further complicate the work of the defender, traditional security solutions are alert-centric, generating an ever-growing volume of notifications that lack context and fail to correlate to one another even if part of the same attack. This alert-centric, siloed approach gives attackers ample opportunity to hide in the seams, which makes hunting, tracking and eliminating attackers all but impossible. |
||||
| 2021-07-19 12:04:11 | Malicious Life Podcast: Dave Kennedy on the History of DerbyCon (lien direct) |
 DerbyCon was conceived with the notion that it was going to be all about making the security community a family. Dave Kennedy, one of the founders of DerbyCon, talks about the unique vibe of the conference, his fear of clowns, and why he'll never listen to a Busta Rhymes album again - check it out…
DerbyCon was conceived with the notion that it was going to be all about making the security community a family. Dave Kennedy, one of the founders of DerbyCon, talks about the unique vibe of the conference, his fear of clowns, and why he'll never listen to a Busta Rhymes album again - check it out… |
||||
| 2021-07-15 12:15:00 | Cybereason vs. Prometheus Ransomware (lien direct) | Prometheus is a relatively new variant of the Thanos ransomware that is operated independently by the Prometheus group, and was first observed in February of 2021. In just a short period of time, Prometheus caused a lot of damage, and breached over 40 companies. | Ransomware | |||
| 2021-07-15 12:00:00 | CISO Stories Podcast: Always be a Student - Always be Learning (lien direct) |
 Phil Attfield, CEO and founder at Sequitur Labs, discusses his engineering roots and the natural curiosity that led him to developing software tools and in-house products for modeling, synthesis and verification of telecom and network equipment hardware at Nortel.
Phil Attfield, CEO and founder at Sequitur Labs, discusses his engineering roots and the natural curiosity that led him to developing software tools and in-house products for modeling, synthesis and verification of telecom and network equipment hardware at Nortel. |
||||
| 2021-07-14 12:46:09 | Cybereason Extends Global Leadership in XDR with $275 Million in Crossover Financing (lien direct) |
 The first half of 2021 has seen explosive growth for our company, and the tremendous momentum we are enjoying is just the beginning of what will prove to be a momentous year for the entire Cybereason team.
The first half of 2021 has seen explosive growth for our company, and the tremendous momentum we are enjoying is just the beginning of what will prove to be a momentous year for the entire Cybereason team. |
Guideline | |||
| 2021-07-13 12:58:13 | Cybereason Launches Global Defenders League Partner Program (lien direct) |
 The Cybereason team is excited to announce the launch of the Cybereason Defenders League, a Global Partner community, designed to reward the cybersecurity industry's most trusted advisors and solution providers by increasing their margins and profitability. Members of this program will gain access to award-winning technology and services to help end users stop cyber attacks.
The Cybereason team is excited to announce the launch of the Cybereason Defenders League, a Global Partner community, designed to reward the cybersecurity industry's most trusted advisors and solution providers by increasing their margins and profitability. Members of this program will gain access to award-winning technology and services to help end users stop cyber attacks. |
||||
| 2021-07-12 18:56:52 | CISO Roundtable: Ransomware Attacks and the True Cost to Business (lien direct) |
 A recent global research report conducted by Cybereason, titled Ransomware: The True Cost to Business, revealed that the vast majority of organizations that have suffered a ransomware attack have experienced significant impact to the business, including loss of revenue, damage to the organization's brand, unplanned workforce reductions, and little in the way of relief from cyber insurance policies.
A recent global research report conducted by Cybereason, titled Ransomware: The True Cost to Business, revealed that the vast majority of organizations that have suffered a ransomware attack have experienced significant impact to the business, including loss of revenue, damage to the organization's brand, unplanned workforce reductions, and little in the way of relief from cyber insurance policies. |
Ransomware | |||
| 2021-07-12 12:06:30 | Malicious Life Podcast: The Life and Exploits of Albert Gonzales Part 2 (lien direct) |
 In this second installment of the series (listen to Albert Gonzales Part 1 here), Gonzales is working with the Secret Service and apparently doing an outstanding job. He was such a good employee, in fact, that they had him doing seminars for staff and speaking at government-run conferences. At one point he met personally with the (then) Director of the Secret Service where Gonzales gave a presentation and even got to shake the Director's hand.
In this second installment of the series (listen to Albert Gonzales Part 1 here), Gonzales is working with the Secret Service and apparently doing an outstanding job. He was such a good employee, in fact, that they had him doing seminars for staff and speaking at government-run conferences. At one point he met personally with the (then) Director of the Secret Service where Gonzales gave a presentation and even got to shake the Director's hand. |
||||
| 2021-07-11 20:30:00 | Cybereason and Doosan Corp Partner to Secure APAC Enterprises (lien direct) |
 Cybereason is excited to announce a partnership with South Korean multinational conglomerate and Global Fortune 2000 leader the Doosan Corporation (Doosan Digital Innovation, or DDI) to protect enterprises from sophisticated cyberattacks on endpoints and across their networks.
Cybereason is excited to announce a partnership with South Korean multinational conglomerate and Global Fortune 2000 leader the Doosan Corporation (Doosan Digital Innovation, or DDI) to protect enterprises from sophisticated cyberattacks on endpoints and across their networks. |
Guideline | |||
| 2021-07-09 14:32:29 | Summer Webinar Series with CSO Sam Curry (lien direct) |
 Join Cybereason CSO Sam Curry for this webinar series where he revisits some of the cybersecurity highlights of the first half of 2021, from the SolarWinds supply chain attacks to DarkSide and other major ransomware operations.
In this series, Sam covers not just the problems confronting defenders so far this year but also the state of play for major ransomware operations, as well as a look at emerging solutions like XDR (Extended Detection and Response) that are designed to reverse the adversary advantage and return the high ground to the defenders.
Register now for one or all of this fascinating summer webinar series:
Join Cybereason CSO Sam Curry for this webinar series where he revisits some of the cybersecurity highlights of the first half of 2021, from the SolarWinds supply chain attacks to DarkSide and other major ransomware operations.
In this series, Sam covers not just the problems confronting defenders so far this year but also the state of play for major ransomware operations, as well as a look at emerging solutions like XDR (Extended Detection and Response) that are designed to reverse the adversary advantage and return the high ground to the defenders.
Register now for one or all of this fascinating summer webinar series: |
Ransomware | |||
| 2021-07-08 13:29:54 | CISO Stories Podcast: CISO Business Enablement - Getting to Yes (lien direct) |
 The CISO is often in a position where vulnerabilities are known and implementing a solution may result in an insecure posture. Should the CISO say 'no we can't do that' or 'figure out how to make it happen'?
The CISO is often in a position where vulnerabilities are known and implementing a solution may result in an insecure posture. Should the CISO say 'no we can't do that' or 'figure out how to make it happen'? |
||||
| 2021-07-07 20:27:43 | REvil Ransomware Attacks: Implications for Kaseya, MSPs and Businesses (lien direct) |
 In some ways, the ransomware attack involving Kaseya is a perfectly logical extension of everything we've seen since the end of last year with the disclosure of the SolarWinds attacks: the merger of supply chain exploits with ransomware to kickstart distribution, an even higher bar for extortions, and the same overall ecosystem at work. In other words, no surprises.
In some ways, the ransomware attack involving Kaseya is a perfectly logical extension of everything we've seen since the end of last year with the disclosure of the SolarWinds attacks: the merger of supply chain exploits with ransomware to kickstart distribution, an even higher bar for extortions, and the same overall ecosystem at work. In other words, no surprises. |
Ransomware | |||
| 2021-07-06 15:45:16 | Cybereason vs. REvil Ransomware: The Kaseya Chronicles (lien direct) |
 As a spate of ransomware attacks continue to dominate the headlines in recent months, the infamous REvil ransomware gang has upped the ante significantly with a wide ranging operation that is suspected to have impacted thousands of small-to-midsize businesses through the compromise of a leading IT services provider.
As a spate of ransomware attacks continue to dominate the headlines in recent months, the infamous REvil ransomware gang has upped the ante significantly with a wide ranging operation that is suspected to have impacted thousands of small-to-midsize businesses through the compromise of a leading IT services provider. |
Ransomware Guideline | |||
| 2021-07-06 14:17:09 | Malicious Life Podcast: Jeff Moss on the History of DEF CON (lien direct) |
 Jeff Moss, founder of the DEF CON Hacker conference (as well as Black Hat), discusses the origins of DEF CON, its "interesting relationship” with law enforcement and intelligence agencies, and some of the notable shenanigans the conference attendees pulled off over the years - check it out…
Jeff Moss, founder of the DEF CON Hacker conference (as well as Black Hat), discusses the origins of DEF CON, its "interesting relationship” with law enforcement and intelligence agencies, and some of the notable shenanigans the conference attendees pulled off over the years - check it out… |
||||
| 2021-07-01 09:28:08 | CISO Stories Podcast: Why Relationships Matter if You Want to Elevate Security (lien direct) |
 Communication in any organization can be a challenge, especially when working with different levels of government and various funding mechanisms.
Communication in any organization can be a challenge, especially when working with different levels of government and various funding mechanisms. |
||||
| 2021-06-30 13:33:56 | What SMBs Need to Know about Ransomware Attacks (lien direct) |
 Ransomware attacks are on the rise. A recently released report by Cybereason, titled Ransomware: The True Cost to Business, detailed how malicious actors are fine-tuning their ransomware campaign tactics, and how both the frequency and severity of successful ransomware attacks have tremendous impact on victim organizations and their ability to conduct business.
Ransomware attacks are on the rise. A recently released report by Cybereason, titled Ransomware: The True Cost to Business, detailed how malicious actors are fine-tuning their ransomware campaign tactics, and how both the frequency and severity of successful ransomware attacks have tremendous impact on victim organizations and their ability to conduct business. |
Ransomware | |||
| 2021-06-28 14:08:06 | Malicious Life Podcast: The Life and Exploits of Albert Gonzales Part 1 (lien direct) |
 It was as a teenager that Albert Gonzalez, one of the greatest cybercriminals in history, developed the obsession that would go on to ruin his life. Gonzalez and some of his friends would go on to pull off some of the most remarkable crimes in the history of computers - but they just didn't know when to stop. If they did, they might have gotten away with it, and they might not have ruined their lives.
It was as a teenager that Albert Gonzalez, one of the greatest cybercriminals in history, developed the obsession that would go on to ruin his life. Gonzalez and some of his friends would go on to pull off some of the most remarkable crimes in the history of computers - but they just didn't know when to stop. If they did, they might have gotten away with it, and they might not have ruined their lives. |
||||
| 2021-06-25 22:54:59 | Ransomware Attacks: Will G7 and Biden-Putin Summits Prove Fruitful? (lien direct) |
 I've been very busy lately. Between the back-to-back ransomware attacks and the release of our ransomware report highlighting the impact on business from ransomware attacks, I have been asked to share my thoughts and insights on a variety of broadcast and print media outlets.
I've been very busy lately. Between the back-to-back ransomware attacks and the release of our ransomware report highlighting the impact on business from ransomware attacks, I have been asked to share my thoughts and insights on a variety of broadcast and print media outlets. |
Ransomware | |||
| 2021-06-23 12:56:41 | CISO Stories Podcast: Fixing the Talent Shortage - CyberSecurity Talent Initiative (lien direct) |
 As threats to the nation's security grow, there remains a substantial shortage of skilled cybersecurity professionals. The federal government and private sector can work together to fill their open positions and attract the next generation of motivated mission-driven cybersecurity leaders.
As threats to the nation's security grow, there remains a substantial shortage of skilled cybersecurity professionals. The federal government and private sector can work together to fill their open positions and attract the next generation of motivated mission-driven cybersecurity leaders. |
Guideline | |||
| 2021-06-22 13:07:04 | Malicious Life Podcast: History of the THOTCON Hacking Conference (lien direct) |
 THOTCON is not your ordinary, run-of-the-mill security conference, and it's obvious from the moment you browse their website. How did a local, small-scale event in Chicago grow to become a major cybersecurity conference? What is its connection to The Matrix movie?
THOTCON is not your ordinary, run-of-the-mill security conference, and it's obvious from the moment you browse their website. How did a local, small-scale event in Chicago grow to become a major cybersecurity conference? What is its connection to The Matrix movie? |
||||
| 2021-06-21 13:34:19 | XDR: The Key to Higher Education\'s Fight Against Ransomware (lien direct) |
 A single student recently became the conduit for a ransomware attack at a biomolecular institute. According to ZDNet, the attack occurred when a student at the unnamed European organization attempted to find a free version of a data visualization software solution.
A single student recently became the conduit for a ransomware attack at a biomolecular institute. According to ZDNet, the attack occurred when a student at the unnamed European organization attempted to find a free version of a data visualization software solution. |
Ransomware | |||
| 2021-06-17 12:40:51 | CISO Stories Podcast: So You Want to be a Cyber Spy? (lien direct) |
 Ira Winkler, CISO at Skyline Technology Solutions, recounts his amazing journey from wannabe astronaut to NSA intelligence analyst, social engineer, systems hacker and author, and some of the crazy things that happened along the way - check it out...
Ira Winkler, CISO at Skyline Technology Solutions, recounts his amazing journey from wannabe astronaut to NSA intelligence analyst, social engineer, systems hacker and author, and some of the crazy things that happened along the way - check it out... |
||||
| 2021-06-17 12:32:14 | Biden-Putin Summit and Why Threat Actors Just Won\'t Give it a Rest (lien direct) |
 On June 11, McDonald's said in a message to its U.S. employees that it had discovered unauthorized activity on an internal security system. The burger chain responded by bringing on some external consultants to investigate what had happened, reported the Wall Street Journal.
On June 11, McDonald's said in a message to its U.S. employees that it had discovered unauthorized activity on an internal security system. The burger chain responded by bringing on some external consultants to investigate what had happened, reported the Wall Street Journal. |
Threat | |||
| 2021-06-16 04:04:05 | Report: Ransomware Attacks and the True Cost to Business (lien direct) |
 Ransomware attacks have continued to make headlines, and for good reason: on average, there is a new ransomware attack every 11 seconds, and the losses to organizations from ransomware attacks is projected to reach $20 billion over the course of 2021 following a record increase in losses of more than 225% in 2020. So what is the true cost to businesses who have been impacted by a ransomware attack?
Ransomware attacks have continued to make headlines, and for good reason: on average, there is a new ransomware attack every 11 seconds, and the losses to organizations from ransomware attacks is projected to reach $20 billion over the course of 2021 following a record increase in losses of more than 225% in 2020. So what is the true cost to businesses who have been impacted by a ransomware attack? |
Ransomware | |||
| 2021-06-15 15:00:00 | Russia\'s Offer to Extradite Attackers - and a Grain of Salt (lien direct) |
 President Vladimir Putin said that Russia would be willing to hand over cyber criminals to the United States if Washington agreed to reciprocate. According to Reuters, Putin disclosed his country's willingness to work with the United States on prosecuting cyber criminals in an interview aired by state television over the weekend.
President Vladimir Putin said that Russia would be willing to hand over cyber criminals to the United States if Washington agreed to reciprocate. According to Reuters, Putin disclosed his country's willingness to work with the United States on prosecuting cyber criminals in an interview aired by state television over the weekend. |
||||
| 2021-06-15 13:46:35 | Deja Vu: What Do NotPetya and SolarWinds Have in Common? (lien direct) |
 As I was waking up in Boston on the morning of June 27, 2017, reports were being shared on social media that an electric power supplier in Ukraine was hit by a cyber attack. Within about an hour, a Danish power supplier was also knocked offline and Maersk shipping announced that it was affected as well. By the time I arrived at my desk, companies around the world were shut down by the same attack--which Symantec declared as Petya ransomware. It was going to be a busy and interesting day.
As I was waking up in Boston on the morning of June 27, 2017, reports were being shared on social media that an electric power supplier in Ukraine was hit by a cyber attack. Within about an hour, a Danish power supplier was also knocked offline and Maersk shipping announced that it was affected as well. By the time I arrived at my desk, companies around the world were shut down by the same attack--which Symantec declared as Petya ransomware. It was going to be a busy and interesting day. |
NotPetya NotPetya | |||
| 2021-06-15 12:56:41 | Malicious Life Podcast: China\'s Unrestricted Cyberwarfare Part 3 (lien direct) |
 For more than a decade, China orchestrated a sophisticated espionage campaign against Nortel Networks, using Huawei, Chinese civilians working in Canada, and even organized crime gangs to steal important technical and operational information. When Nortel finally fell, the Chinese were there to reap the rewards of their death.
For more than a decade, China orchestrated a sophisticated espionage campaign against Nortel Networks, using Huawei, Chinese civilians working in Canada, and even organized crime gangs to steal important technical and operational information. When Nortel finally fell, the Chinese were there to reap the rewards of their death. |
||||
| 2021-06-14 11:59:48 | Ransomware Attacks are Evolving: What You Need to Know (lien direct) |
 One look at all the ransomware attacks from the past few years, and it's clear that crypto-malware actors are attempting to maximize their financial gain. We've observed these threat groups using multiple techniques to profit even more off their victims than in years past. Here are a few tactics that stood out to us.
One look at all the ransomware attacks from the past few years, and it's clear that crypto-malware actors are attempting to maximize their financial gain. We've observed these threat groups using multiple techniques to profit even more off their victims than in years past. Here are a few tactics that stood out to us.
|
Threat Ransomware | |||
| 2021-06-09 13:23:33 | CISO Stories Podcast: No Insider Cybersecurity Risk? Guess Again! (lien direct) |
 We want to trust our employees and contractors working within our organizations. For the most part, people are doing their jobs with integrity every day. What happens when an employee decides to leave the organization and start their own business – but with your Intellectual property or customer lists?
We want to trust our employees and contractors working within our organizations. For the most part, people are doing their jobs with integrity every day. What happens when an employee decides to leave the organization and start their own business – but with your Intellectual property or customer lists? |
To see everything:
Our RSS (filtrered)
