What's new arround internet
| Src | Date (GMT) | Titre | Description | Tags | Stories | Notes |
| 2022-06-07 16:38:51 | Texas AG enters Musk/Twitter fight by ordering Twitter to provide spam data (lien direct) | Paxton demands the spam data that Musk hasn't been able to get from Twitter. | Spam | |||
| 2022-06-07 01:14:19 | Researchers Warn of Spam Campaign Targeting Victims with SVCReady Malware (lien direct) | A new wave of phishing campaigns has been observed spreading a previously documented malware called SVCReady. "The malware is notable for the unusual way it is delivered to target PCs - using shellcode hidden in the properties of Microsoft Office documents," Patrick Schläpfer, a threat analyst at HP, said in a technical write-up. SVCReady is said to be in its early stage of development, with the | Spam Malware Threat | |||
| 2022-06-06 16:11:22 | Musk seeks a way out, claims Twitter violated deal by not providing spam data (lien direct) | Musk waived due diligence but claims he can kill deal if he doesn't get user data. | Spam | |||
| 2022-05-27 12:04:11 | The $44 Billion Smishing Problem and How to Not Be a Victim (lien direct) |
 Consumer Affairs reported on how big of a problem SMS phishing scams have become, and how it's about to get a lot worse. According to a recent FBI report, more than 320,000 Americans were targeted by these schemes in 2021, resulting in $44 billion in losses. Consumers on average get an average of 19.5 spam texts per month, over double the rate it was three years ago.
Consumer Affairs reported on how big of a problem SMS phishing scams have become, and how it's about to get a lot worse. According to a recent FBI report, more than 320,000 Americans were targeted by these schemes in 2021, resulting in $44 billion in losses. Consumers on average get an average of 19.5 spam texts per month, over double the rate it was three years ago. |
Spam | |||
| 2022-05-17 17:15:07 | Musk says Twitter must show data behind spam estimate or he\'ll kill the deal (lien direct) | Musk replied to Twitter CEO's spam explanation with criticism and a poop emoji. | Spam | |||
| 2022-05-17 12:24:22 | Musk: Doubt About Spam Accounts Could Scuttle Twitter Deal (lien direct) | 
|
Spam | |||
| 2022-05-17 12:11:00 | Twitter réplique à Elon Musk au sujet des spams, et explique comment il lutte contre les faux comptes (lien direct) | Le PDG du réseau social joue la carte de la transparence en expliquant comment ses équipes traquent les spams et faux comptes. Un processus complexe qui nécessite une adaptation constante.  |
Spam | |||
| 2022-05-13 15:28:09 | Musk says Twitter deal “on hold” over concern about number of spam accounts (lien direct) | Musk "still committed" to purchase amid talk he could back out or renegotiate. | Spam | |||
| 2022-05-11 15:49:52 | I/O 2022: Android 13 security and privacy (and more!) (lien direct) | Posted by Eugene Liderman and Sara N-Marandi, Android Security and Privacy TeamEvery year at I/O we share the latest on privacy and security features on Android. But we know some users like to go a level deeper in understanding how we're making the latest release safer, and more private, while continuing to offer a seamless experience. So let's dig into the tools we're building to better secure your data, enhance your privacy and increase trust in the apps and experiences on your devices. Low latency, frictionless securityRegardless of whether a smartphone is used for consumer or enterprise purposes, attestation is a key underpinning to ensure the integrity of the device and apps running on the device. Fundamentally, key attestation lets a developer bind a secret or designate data to a device. This is a strong assertion: "same user, same device" as long as the key is available, a cryptographic assertion of integrity can be made. With Android 13 we have migrated to a new model for the provisioning of attestation keys to Android devices which is known as Remote Key Provisioning (RKP). This new approach will strengthen device security by eliminating factory provisioning errors and providing key vulnerability recovery by moving to an architecture where Google takes more responsibility in the certificate management lifecycle for these attestation keys. You can learn more about RKP here. 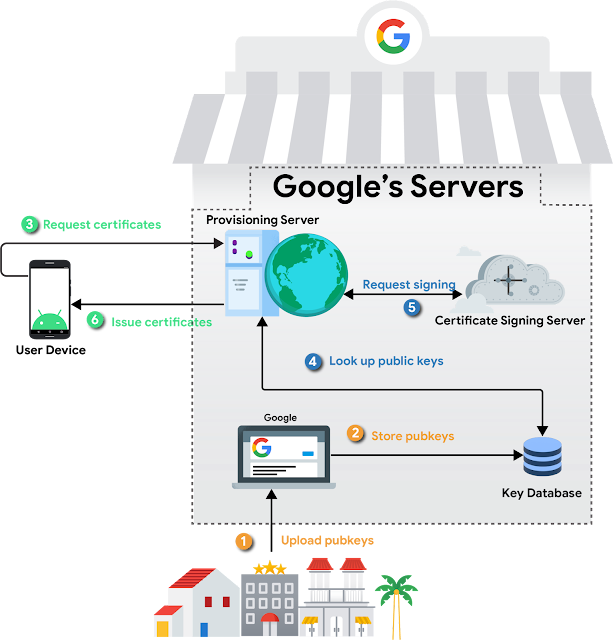 We're also making even more modules updatable directly through Google Play System Updates so we can automatically upgrade more system components and fix bugs, seamlessly, without you having to worry about it. We now have more than 30 components in Android that can be automatically updated through Google Play, including new modules in Android 13 for Bluetooth and ultra-wideband (UWB). Last year we talked about how the majority of vulnerabilities in major operating systems are caused by undefined behavior in programming languages like C/C++. Rust is an alternative language that provides the efficiency and flexibility required in advanced systems programming (OS, networking) but Rust comes with the added boost of memory safety. We are happy to report that Rust is being adopted in security critical parts of Android, such as our key management components and networking stacks. Hardening the platform doesn't just stop with continual improvements with memory safety and expansion of anti-exploitation techniques. It also includes hardening our API surfaces to provide a more secure experience to our end users. In Android 13 we implemented numerous enhancements to help mitigate potential vulnerabilities that app developers may inadvertently introduce. This includes making runtime receivers safer by allowing developers to specify whether a particular broadcast receiver in their app s We're also making even more modules updatable directly through Google Play System Updates so we can automatically upgrade more system components and fix bugs, seamlessly, without you having to worry about it. We now have more than 30 components in Android that can be automatically updated through Google Play, including new modules in Android 13 for Bluetooth and ultra-wideband (UWB). Last year we talked about how the majority of vulnerabilities in major operating systems are caused by undefined behavior in programming languages like C/C++. Rust is an alternative language that provides the efficiency and flexibility required in advanced systems programming (OS, networking) but Rust comes with the added boost of memory safety. We are happy to report that Rust is being adopted in security critical parts of Android, such as our key management components and networking stacks. Hardening the platform doesn't just stop with continual improvements with memory safety and expansion of anti-exploitation techniques. It also includes hardening our API surfaces to provide a more secure experience to our end users. In Android 13 we implemented numerous enhancements to help mitigate potential vulnerabilities that app developers may inadvertently introduce. This includes making runtime receivers safer by allowing developers to specify whether a particular broadcast receiver in their app s |
Spam Vulnerability | |||
| 2022-05-11 12:13:51 | Novel Phishing Trick Uses Weird Links to Bypass Spam Filters (lien direct) | A novel form of phishing takes advantage of a disparity between how browsers and email inboxes read web domains. | Spam | ★★★ | ||
| 2022-05-06 18:15:08 | CVE-2021-27758 (lien direct) | There is a security vulnerability in login form related to Cross-site Request Forgery which prevents user to login after attacker spam to login and system blocked victim's account. | Spam Vulnerability | ★★★★★ | ||
| 2022-05-04 15:01:01 | Phishers taking advantage of Gmail\'s SMTP relay service to impersonate brands (lien direct) | Since April 2022 phishing emails have been sent to Gmail users from legitimate addresses, making it hard to tell spam from legitimate sources. | Spam | |||
| 2022-04-29 09:49:00 | Vulnerable plugins plague the CMS website security landscape (lien direct) | Backdoors, card skimming, and spam are also common factors in website compromise. | Spam | |||
| 2022-04-19 15:00:00 | Anomali Cyber Watch: RaidForums Seized, Sandworm Attacks Ukrainian Power Stations, North Korea Steals Chemical Secrets, and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: APT, China, Cyberespionage, North Korea, Spearphishing, Russia, Ukraine, and Vulnerabilities. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Lazarus Targets Chemical Sector
(published: April 14, 2022)
In January 2022, Symantec researchers discovered a new wave of Operation Dream Job. This operation, attributed to the North Korea-sponsored group Lazarus, utilizes fake job offers via professional social media and email communications. With the new wave of attacks, Operation Dream Job switched from targeting the defense, government, and engineering sectors to targeting South Korean organizations operating within the chemical sector. A targeted user executes an HTM file sent via a link. The HTM file is copied to a DLL file to be injected into the legitimate system management software. It downloads and executes the final backdoor: a trojanized version of the Tukaani project LZMA Utils library (XZ Utils) with a malicious export added (AppMgmt). After the initial access, the attackers gain persistence via scheduled tasks, move laterally, and collect credentials and sensitive information.
Analyst Comment: Organizations should train their users to recognize social engineering attacks including those posing as “dream job” proposals. Organizations facing cyberespionage threats should implement a defense-in-depth approach: layering of security mechanisms, redundancy, fail-safe defense processes.
MITRE ATT&CK: [MITRE ATT&CK] Scheduled Task - T1053 | [MITRE ATT&CK] User Execution - T1204 | [MITRE ATT&CK] Windows Management Instrumentation - T1047 | [MITRE ATT&CK] Process Injection - T1055 | [MITRE ATT&CK] Valid Accounts - T1078 | [MITRE ATT&CK] Signed Binary Proxy Execution - T1218 | [MITRE ATT&CK] Credentials from Password Stores - T1555
Tags: Lazarus, Operation Dream Job, North Korea, source-country:KP, South Korea, target-country:KR, APT, HTM, CPL, Chemical sector, Espionage, Supply chain, IT sector
Old Gremlins, New Methods
(published: April 14, 2022)
Group-IB researchers have released their analysis of threat actor OldGremlin’s new March 2022 campaign. OldGremlin favored phishing as an initial infection vector, crafting intricate phishing emails that target Russian industries. The threat actors utilized the current war between Russia and Ukraine to add a sense of legitimacy to their emails, with claims that users needed to click a link to register for a new credit card, as current ones would be rendered useless by incoming sanctions. The link leads users to a malicious Microsoft Office document stored within Dropbox. When macros are enabled, the threat actor’s new, custom backdoor, TinyFluff, a new version of their old TinyNode
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Lazarus Targets Chemical Sector
(published: April 14, 2022)
In January 2022, Symantec researchers discovered a new wave of Operation Dream Job. This operation, attributed to the North Korea-sponsored group Lazarus, utilizes fake job offers via professional social media and email communications. With the new wave of attacks, Operation Dream Job switched from targeting the defense, government, and engineering sectors to targeting South Korean organizations operating within the chemical sector. A targeted user executes an HTM file sent via a link. The HTM file is copied to a DLL file to be injected into the legitimate system management software. It downloads and executes the final backdoor: a trojanized version of the Tukaani project LZMA Utils library (XZ Utils) with a malicious export added (AppMgmt). After the initial access, the attackers gain persistence via scheduled tasks, move laterally, and collect credentials and sensitive information.
Analyst Comment: Organizations should train their users to recognize social engineering attacks including those posing as “dream job” proposals. Organizations facing cyberespionage threats should implement a defense-in-depth approach: layering of security mechanisms, redundancy, fail-safe defense processes.
MITRE ATT&CK: [MITRE ATT&CK] Scheduled Task - T1053 | [MITRE ATT&CK] User Execution - T1204 | [MITRE ATT&CK] Windows Management Instrumentation - T1047 | [MITRE ATT&CK] Process Injection - T1055 | [MITRE ATT&CK] Valid Accounts - T1078 | [MITRE ATT&CK] Signed Binary Proxy Execution - T1218 | [MITRE ATT&CK] Credentials from Password Stores - T1555
Tags: Lazarus, Operation Dream Job, North Korea, source-country:KP, South Korea, target-country:KR, APT, HTM, CPL, Chemical sector, Espionage, Supply chain, IT sector
Old Gremlins, New Methods
(published: April 14, 2022)
Group-IB researchers have released their analysis of threat actor OldGremlin’s new March 2022 campaign. OldGremlin favored phishing as an initial infection vector, crafting intricate phishing emails that target Russian industries. The threat actors utilized the current war between Russia and Ukraine to add a sense of legitimacy to their emails, with claims that users needed to click a link to register for a new credit card, as current ones would be rendered useless by incoming sanctions. The link leads users to a malicious Microsoft Office document stored within Dropbox. When macros are enabled, the threat actor’s new, custom backdoor, TinyFluff, a new version of their old TinyNode |
Ransomware Spam Malware Vulnerability Threat Guideline Medical | APT 38 APT 28 | ||
| 2022-04-14 11:00:00 | Threat Source newsletter (April 14, 2022) - It\'s Tax Day, and you know what that means (lien direct) | By Jon Munshaw. Welcome to this week's edition of the Threat Source newsletter. The deadline to file taxes in the United States is Monday. That means a few things: everyone should probably make sure their liquor cabinet is fully stocked, your spam filters are all turned on in your email... [[ This is only the beginning! Please visit the blog for the complete entry ]] | Spam Threat | |||
| 2022-04-11 15:15:08 | CVE-2022-0949 (lien direct) | The Block Bad Bots and Stop Bad Bots Crawlers and Spiders and Anti Spam Protection WordPress plugin before 6.930 does not properly sanitise and escape the fingerprint parameter before using it in a SQL statement via the stopbadbots_grava_fingerprint AJAX action, available to unauthenticated users, leading to a SQL injection | Spam Guideline | |||
| 2022-03-25 12:15:07 | CVE-2022-1064 (lien direct) | SQL injection through marking blog comments on bulk as spam in GitHub repository forkcms/forkcms prior to 5.11.1. | Spam | |||
| 2022-03-14 15:15:09 | CVE-2022-0254 (lien direct) | The WordPress Zero Spam WordPress plugin before 5.2.11 does not properly sanitise and escape the order and orderby parameters before using them in a SQL statement in the admin dashboard, leading to a SQL injection | Spam Guideline | |||
| 2022-03-13 14:26:20 | Filter Blocked 70,000 Emails to Indiana Lawmakers on Bill (lien direct) | A spam filter blocked as many as 70,000 emails sent to Indiana legislators about a contentious bill that aimed to place restrictions on teaching about racism and political topics. | Spam | |||
| 2022-03-09 20:48:00 | Chinese hackers attempted phishing on emails affiliated with US government (lien direct) | All phishing emails were successfully marked as spam and filtered by Gmail in February. | Spam | |||
| 2022-03-04 17:23:01 | Picking up the phone still might be the best way to do business (lien direct) | State of the Call report shows that voice calls remain preferred form of communication, despite spam risks | Spam | |||
| 2022-02-15 22:31:33 | SquirrelWaffle Adds a Twist of Fraud to Exchange Server Malspamming (lien direct) | Researchers have never before seen SquirrelWaffle attackers use typosquatting to keep sending spam once a targeted Exchange server has been patched for ProxyLogon/ProxyShell. | Spam | |||
| 2022-02-15 14:24:51 | CyberheistNews Vol 12 #07 [Heads Up] FBI Warns Against New Criminal QR Code Scams (lien direct) |
 [Heads Up] FBI Warns Against New Criminal QR Code Scams
Email not displaying? |
CyberheistNews Vol 12 #07 | Feb. 15th., 2022
[Heads Up] FBI Warns Against New Criminal QR Code Scams
QR codes have been around for many years. While they were adopted for certain niche uses, they never did quite reach their full potential. They are a bit like Rick Astley in that regard, really popular for one song, but well after the boat had sailed. Do not get me wrong, Rick Astley achieved a lot. In recent years, he has become immortalized as a meme and Rick roller, but he could have been so much more.
However, in recent years, with lockdown and the drive to keep things at arms length, QR codes have become an efficient way to facilitate contactless communications, or the transfer of offers without physically handing over a coupon. As this has grown in popularity, more people have become familiar with how to generate their own QR codes and how to use them as virtual business cards, discount codes, links to videos and all sorts of other things.
QRime Codes
As with most things, once they begin to gain a bit of popularity, criminals move in to see how they can manipulate the situation to their advantage. Recently, we have seen fake QR codes stuck to parking meters enticing unwitting drivers to scan the code, and hand over their payment details believing they were paying for parking, whereas they were actually handing over their payment information to criminals.
The rise in QR code fraud resulted in the FBI releasing an advisory warning against fake QR codes that are being used to scam users. In many cases, a fake QR code will lead people to a website that looks like the intended legitimate site. So, the usual verification process of checking the URL and any other red flags apply.
CONTINUED with links and 4 example malicious QR codes on the KnowBe4 blog:
https://blog.knowbe4.com/qr-codes-in-the-time-of-cybercrime
[Heads Up] FBI Warns Against New Criminal QR Code Scams
Email not displaying? |
CyberheistNews Vol 12 #07 | Feb. 15th., 2022
[Heads Up] FBI Warns Against New Criminal QR Code Scams
QR codes have been around for many years. While they were adopted for certain niche uses, they never did quite reach their full potential. They are a bit like Rick Astley in that regard, really popular for one song, but well after the boat had sailed. Do not get me wrong, Rick Astley achieved a lot. In recent years, he has become immortalized as a meme and Rick roller, but he could have been so much more.
However, in recent years, with lockdown and the drive to keep things at arms length, QR codes have become an efficient way to facilitate contactless communications, or the transfer of offers without physically handing over a coupon. As this has grown in popularity, more people have become familiar with how to generate their own QR codes and how to use them as virtual business cards, discount codes, links to videos and all sorts of other things.
QRime Codes
As with most things, once they begin to gain a bit of popularity, criminals move in to see how they can manipulate the situation to their advantage. Recently, we have seen fake QR codes stuck to parking meters enticing unwitting drivers to scan the code, and hand over their payment details believing they were paying for parking, whereas they were actually handing over their payment information to criminals.
The rise in QR code fraud resulted in the FBI releasing an advisory warning against fake QR codes that are being used to scam users. In many cases, a fake QR code will lead people to a website that looks like the intended legitimate site. So, the usual verification process of checking the URL and any other red flags apply.
CONTINUED with links and 4 example malicious QR codes on the KnowBe4 blog:
https://blog.knowbe4.com/qr-codes-in-the-time-of-cybercrime
|
Ransomware Data Breach Spam Malware Threat Guideline | APT 15 APT 43 | ||
| 2022-02-14 11:52:32 | Half of all emails in 2021 were spam (lien direct) | Email spam rates averaged 46% over the year globally, according to a new report by Kaspersky. In its new Spam and Phishing in 2021 report, the Russian AV company revealed that spam rates peaked at 48% in June. The majority came from machines in Russia (25%), followed by Germany (14%), the US (10%) and China (9%). […] | Spam | |||
| 2022-02-11 10:08:00 | Half of Global Emails Were Spam in 2021 (lien direct) | COVID-19 still looms large in corporate inboxes | Spam | |||
| 2022-02-09 10:00:28 | Spam and phishing in 2021 (lien direct) | Statistics on spam and phishing with the key trends in 2021: investment scams, fake streaming websites, theft of corporate credentials and COVID-19. | Spam | |||
| 2022-01-28 03:10:59 | Hackers Using Device Registration Trick to Attack Enterprises with Lateral Phishing (lien direct) | Microsoft has disclosed details of a large-scale, multi-phase phishing campaign that uses stolen credentials to register devices on a victim's network to further propagate spam emails and widen the infection pool. The tech giant said the attacks manifested through accounts that were not secured using multi-factor authentication (MFA), thereby making it possible for the adversary to take | Spam | |||
| 2022-01-24 12:05:20 | Emotet spam uses unconventional IP address formats to evade detection (lien direct) | Experts warn Emotet malware campaign using “unconventional” IP address formats in an attempt to evade detection. Threat actors behind a recent Emotet malware campaign have been observed using using “unconventional” IP address formats to evade detection. Trend Micro researchers reported that threat actors are using hexadecimal and octal representations of the IP address. “We observed Emotet spam […] | Spam Malware Threat | |||
| 2022-01-10 14:54:48 | Email spam is breaking through again. Here\'s what you can do to minimize it (lien direct) | Pas de details / No more details | Spam | |||
| 2021-12-20 16:56:12 | Spam Calling Rates Spike Globally (lien direct) |
 Spam calls in the US spiked in October, according to Truecaller's annual Global Spam Report. The report observed that Truecaller customers in the US received 3,115,861 spam calls in October. The researchers note that a user in the US receives an average of 4.8 spam calls per month, totalling approximately 1.4 billion calls across the country every month.
Spam calls in the US spiked in October, according to Truecaller's annual Global Spam Report. The report observed that Truecaller customers in the US received 3,115,861 spam calls in October. The researchers note that a user in the US receives an average of 4.8 spam calls per month, totalling approximately 1.4 billion calls across the country every month. |
Spam | |||
| 2021-12-17 11:47:21 | Phorpiex botnet is back, in 2021 it $500K worth of crypto assets (lien direct) | Experts reported the resurgence of the Phorpiex botnet, in one year it allowed to steal crypto assets worth of half a million dollars. Experts at Check Point Research have monitored the resurgence of the Phorpiex botnet, an old threat that was involved in sextortion spam campaigns, crypto-jacking, cryptocurrency clipping (substituting the original wallet address saved in […] | Spam Threat | |||
| 2021-12-13 11:15:09 | CVE-2021-24863 (lien direct) | The WP Block and Stop Bad Bots Crawlers and Spiders and Anti Spam Protection Plugin StopBadBots WordPress plugin before 6.67 does not sanitise and escape the User Agent before using it in a SQL statement to save it, leading to a SQL injection | Spam Guideline | |||
| 2021-12-08 16:00:01 | Fight back against spam calls with this subscription to the RoboKiller app (lien direct) | RoboKiller will nip those annoying, automated calls in the bud. Now it's available for a discount on a five-year subscription. | Spam | |||
| 2021-12-08 15:47:28 | Credential-Harvesting Phishing Campaign Urges Review of Spam (lien direct) |
 Researchers at MailGuard have observed a phishing campaign that's using phony “spam notification” emails that purport to come from Microsoft Office 365. The emails tell recipients that an important-looking email has been sent to their spam folder, and they'll need to click a link to view the supposed message.
Researchers at MailGuard have observed a phishing campaign that's using phony “spam notification” emails that purport to come from Microsoft Office 365. The emails tell recipients that an important-looking email has been sent to their spam folder, and they'll need to click a link to view the supposed message. |
Spam | |||
| 2021-12-05 11:07:37 | Convincing Microsoft phishing uses fake Office 365 spam alerts (lien direct) | A persuasive and ongoing series of phishing attacks are using fake Office 365 notifications asking the recipients to review blocked spam messages, with the end goal of stealing their Microsoft credentials. [...] | Spam | |||
| 2021-12-03 07:46:29 | Talos Takes Ep. #79: Emotet\'s back with the worst type of holiday present (lien direct) | By Jon Munshaw. The latest episode of Talos Takes is available now. Download this episode and subscribe to Talos Takes using the buttons below, or visit the Talos Takes page. Emotet is back, and it brought the worst possible holiday present (just in time for peak spam season, too!). We... [[ This is only the beginning! Please visit the blog for the complete entry ]] | Spam | |||
| 2021-12-02 15:28:25 | Twitter removes 3,400 accounts used in govt propaganda campaigns (lien direct) | Twitter today announced the permanent removal of more than 3,400 accounts linked to governments of six countries running manipulation or spam campaigns. [...] | Spam | |||
| 2021-11-23 20:30:00 | Anomali Cyber Watch: APT, Emotet, Iran, RedCurl and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: APT, Data breach, Data leak, Malspam, Phishing, and Vulnerabilities. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Emotet malware is back and rebuilding its botnet via TrickBot
(published: November 15, 2021)
After Europol enforcement executed a takeover of the Emotet infrastructure in April 2021 and German law enforcement used this infrastructure to load a module triggering an uninstall of existing Emotet installs, new Emotet installs have been detected via initial infections with TrickBot. These campaigns and infrastructure appear to be rapidly proliferating. Once infected with Emotet, in addition to leveraging the infected device to send malspam, additional malware can be downloaded and installed on the victim device for various purposes, including ransomware. Researchers currently have not seen any spamming activity or any known malicious documents dropping Emotet malware besides from TrickBot. It is possible that Emotet is using Trickbot to rebuild its infrastructure and steal email chains it will use in future spam attacks.
Analyst Comment: Phishing continues to be a preferred method for initial infection by many actors and malware families. End users should be cautious with email attachments and links, and organizations should have robust endpoint protections that are regularly updated.
***For Anomali ThreatStream Customers***
To assist in helping the community, especially with the online shopping season upon us, Anomali Threat Research has made available two, threat actor-focused dashboards: Mummy Spider and Wizard Spider, for Anomali ThreatStream customers. The Dashboards are preconfigured to provide immediate access and visibility into all known Mummy Spider and Wizard Spider indicators of compromise (IOCs) made available through commercial and open-source threat feeds that users manage on ThreatStream.
MITRE ATT&CK: [MITRE ATT&CK] Phishing - T1566 | [MITRE ATT&CK] Shared Modules - T1129 | [MITRE ATT&CK] Data Encrypted - T1022 | [MITRE ATT&CK] Ingress Tool Transfer - T1105 | [MITRE ATT&CK] Automated Collection - T1119
Tags: Emotet, Trickbot, phishing, ransomware
Wind Turbine Giant Offline After Cyber Incident
(published: November 22, 2021)
The internal IT systems for Vestas Wind Systems, the world's largest manufacturer of wind turbines, have been hit by an attack. This attack does not appear to have affected their manufacturing or supply chain, and recovery of affected systems is underway, although a number of systems remain off as a precaution. The company has announced that some data has been compromised. The investigation of this incident is ongoing, but may have been a ransomware attack. The incidents of ransomware across the globe increased by near
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Emotet malware is back and rebuilding its botnet via TrickBot
(published: November 15, 2021)
After Europol enforcement executed a takeover of the Emotet infrastructure in April 2021 and German law enforcement used this infrastructure to load a module triggering an uninstall of existing Emotet installs, new Emotet installs have been detected via initial infections with TrickBot. These campaigns and infrastructure appear to be rapidly proliferating. Once infected with Emotet, in addition to leveraging the infected device to send malspam, additional malware can be downloaded and installed on the victim device for various purposes, including ransomware. Researchers currently have not seen any spamming activity or any known malicious documents dropping Emotet malware besides from TrickBot. It is possible that Emotet is using Trickbot to rebuild its infrastructure and steal email chains it will use in future spam attacks.
Analyst Comment: Phishing continues to be a preferred method for initial infection by many actors and malware families. End users should be cautious with email attachments and links, and organizations should have robust endpoint protections that are regularly updated.
***For Anomali ThreatStream Customers***
To assist in helping the community, especially with the online shopping season upon us, Anomali Threat Research has made available two, threat actor-focused dashboards: Mummy Spider and Wizard Spider, for Anomali ThreatStream customers. The Dashboards are preconfigured to provide immediate access and visibility into all known Mummy Spider and Wizard Spider indicators of compromise (IOCs) made available through commercial and open-source threat feeds that users manage on ThreatStream.
MITRE ATT&CK: [MITRE ATT&CK] Phishing - T1566 | [MITRE ATT&CK] Shared Modules - T1129 | [MITRE ATT&CK] Data Encrypted - T1022 | [MITRE ATT&CK] Ingress Tool Transfer - T1105 | [MITRE ATT&CK] Automated Collection - T1119
Tags: Emotet, Trickbot, phishing, ransomware
Wind Turbine Giant Offline After Cyber Incident
(published: November 22, 2021)
The internal IT systems for Vestas Wind Systems, the world's largest manufacturer of wind turbines, have been hit by an attack. This attack does not appear to have affected their manufacturing or supply chain, and recovery of affected systems is underway, although a number of systems remain off as a precaution. The company has announced that some data has been compromised. The investigation of this incident is ongoing, but may have been a ransomware attack. The incidents of ransomware across the globe increased by near |
Ransomware Spam Malware Tool Vulnerability Threat Patching | |||
| 2021-11-22 05:01:13 | Back from the dead: Emotet re-emerges, begins rebuilding to wrap up 2021 (lien direct) | Executive summary Emotet has been one of the most widely distributed threats over the past several years. It has typically been observed being distributed via malicious spam email campaigns, and often leads to additional malware infections as it provides threat actors with an initial foothold in an... [[ This is only the beginning! Please visit the blog for the complete entry ]] | Spam Malware Threat Guideline | |||
| 2021-11-22 03:47:12 | Hackers Exploiting ProxyLogon and ProxyShell Flaws in Spam Campaigns (lien direct) | Threat actors are exploiting ProxyLogon and ProxyShell exploits in unpatched Microsoft Exchange Servers as part of an ongoing spam campaign that leverages stolen email chains to bypass security software and deploy malware on vulnerable systems. The findings come from Trend Micro following an investigation into a number of intrusions in the Middle East that culminated in the distribution of a | Spam Malware | |||
| 2021-11-16 18:07:17 | Here are the new Emotet spam campaigns hitting mailboxes worldwide (lien direct) | The Emotet malware kicked into action yesterday after a ten-month hiatus with multiple spam campaigns delivering malicious documents to mailboxes worldwide. [...] | Spam Malware | |||
| 2021-11-16 14:28:03 | RansomOps: Detecting Complex Ransomware Operations (lien direct) |
 In a recent blog post we discussed how today's more complex RansomOps attacks are more akin to stealthy APT-like operations than the old “spray and pray” mass email spam campaign of old, and how there are multiple players from the larger Ransomware Economy at work, each with their own specializations.
In a recent blog post we discussed how today's more complex RansomOps attacks are more akin to stealthy APT-like operations than the old “spray and pray” mass email spam campaign of old, and how there are multiple players from the larger Ransomware Economy at work, each with their own specializations. |
Ransomware Spam | |||
| 2021-11-15 15:04:23 | (Déjà vu) Emotet malware is back and rebuilding its botnet via TrickBot (lien direct) | The Emotet malware was considered the most widely spread malware in the past, using spam campaigns and malicious attachments to distribute the malware. [...] | Spam Malware | |||
| 2021-11-15 15:04:23 | The Emotet malware is back and rebuilding its botnet via TrickBot (lien direct) | The Emotet malware was considered the most widely spread malware in the past, using spam campaigns and malicious attachments to distribute the malware. [...] | Spam Malware | |||
| 2021-11-15 09:22:00 | FBI Fixes Misconfigured Server After Hoax Email Alert (lien direct) | Spam sent from FBI address warned of imminent cyber-threat | Spam | |||
| 2021-11-15 01:07:00 | Il a humilié le FBI en utilisant son domaine pour envoyer du spam (lien direct) | Un hacker a profité de la mauvaise configuration d'un site web de l'agence fédérale pour envoyer de faux messages. Un hoax pas bien méchant, mais quand même sacrément vexant.  |
Spam | ★★★ | ||
| 2021-11-13 22:46:53 | Hoax Email Blast Abused Poor Coding in FBI Website (lien direct) | The Federal Bureau of Investigation (FBI) confirmed today that its fbi.gov domain name and Internet address were used to blast out thousands of fake emails about a cybercrime investigation. According to an interview with the person who claimed responsibility for the hoax, the spam messages were sent by abusing insecure code in an FBI online portal designed to share information with state and local law enforcement authorities. | Spam | |||
| 2021-11-13 22:35:26 | Hundreds of thousands of fake warnings of cyberattacks sent from a hacked FBI email server (lien direct) | Threat actors hacked email servers of the FBI to distribute spam email impersonating FBI warnings of fake cyberattacks. The email servers of the FBI were hacked to distribute spam email impersonating the Department of Homeland Security (DHS) warnings of fake sophisticated chain attacks from an advanced threat actor. The message tells the recipients that their […] | Spam Threat | |||
| 2021-11-13 13:36:16 | FBI system hacked to email \'urgent\' warning about fake cyberattacks (lien direct) | The Federal Bureau of Investigation (FBI) email servers were hacked to distribute spam email impersonating FBI warnings that the recipients' network was breached and data was stolen. [...] | Spam | |||
| 2021-11-11 16:34:07 | Windows 10 App Installer abused in BazarLoader malware attacks (lien direct) | The TrickBot gang operators are now abusing the Windows 10 App Installer to deploy their BazarLoader malware on the systems of targets who fall victim to a highly targeted spam campaign. [...] | Spam Malware |
To see everything:
Our RSS (filtrered)
