What's new arround internet
| Src | Date (GMT) | Titre | Description | Tags | Stories | Notes |
| 2023-12-14 09:44:32 | Atténuation des menaces d'initié: 5 meilleures pratiques pour réduire le risque Insider Threat Mitigation: 5 Best Practices to Reduce Risk (lien direct) |
(This is an updated version of a blog that was originally published on 1/28/21.) Most security teams focus on detecting and preventing external threats. But not all threats come from the outside. The shift to hybrid work, accelerated cloud adoption and high rates of employee turnover have created a perfect storm for data loss and insider threats over the past several years. Today, insider threats rank amongst the top concerns for security leaders-30% of chief information security officers report that insider threats are their biggest cybersecurity threat over the next 12 months. It\'s easy to understand why. Insider threats have increased 44% since 2020 due to current market dynamics-and security teams are struggling to keep pace. According to the Verizon 2023 Data Breach Investigations Report, 74% of all breaches involve the human element. In short, data doesn\'t lose itself. People lose it. When the cybersecurity risk to your company\'s vital systems and data comes from the inside, finding ways to mitigate it can be daunting. Unlike with tools that combat external threats, security controls for data loss and insider threats can impact users\' daily jobs. However, with the right approach and insider threat management tools, that doesn\'t have to be the case. In this blog post, we\'ll share best practices for insider threat mitigation to help your business reduce risk and overcome common challenges you might face along the way. What is an insider threat? But first, let\'s define what we mean by an insider threat. In the cybersecurity world, the term “insider” describes anyone with authorized access to a company\'s network, systems or data. In other words, it is someone in a position of trust. Current employees, business partners and third-party contractors can all be defined as insiders. As part of their day-to-day jobs, insiders have access to valuable data and systems like: Computers and networks Intellectual property (IP) Personal data Company strategy Financial information Customer and partner lists All insiders pose a risk given their position of trust-but not all insiders are threats. An insider threat occurs when someone with authorized access to critical data or systems misuses that access-either on purpose or by making a mistake. The fallout from an insider threat can be dire for a business, including IP loss, legal liability, financial consequences and reputational damage. The challenge for security firms is to determine which insiders are threats, and what type of threats they are, so they know how to respond. There are three insider threat types: Careless. This type of risky insider is best described as a user with good intentions who makes bad decisions that can lead to data loss. The 2022 Cost of Insider Threats Global Report from Ponemon Institute notes that careless users account for more than half (56%) of all insider-led incidents. Malicious. Some employees-or third parties, like contractors or business partners-are motivated by personal gain. Or they might be intent on harming the business. In either case, these risky users might want to exfiltrate trade secrets or take IP when they leave the company. Industrial espionage and sabotage are examples of malicious insider activity. Ponemon research shows malicious insiders account for 26% of insiders. Compromised. Sometimes, external threat actors steal user login information or other credentials. They then use those credentials to access applications and systems. Ponemon reports that compromised users account for 18% of insiders. Insider threat mitigation best practices Companies can minimize brand and financial damage by detecting and stopping insider threats. How each security team approaches insider threats will vary depending on the industry, maturity and business culture. However, every organization can use the five best practices we\'ve outlined below to improve their insider threat prevention. 1. Identify your risky users Most insiders fall into the “care | Data Breach Tool Threat Industrial Cloud Technical | ★★ | ||
| 2023-12-14 00:08:10 | Problèmes de chemin d'installation et de portabilité personnalisés Custom Install Path & portability issues (lien direct) |
Si vous lisez mon blog depuis un certain temps, vous saurez que j'aime défier mon jeu de chasse aux menaces avec beaucoup d'err & # 8230;.banalités.Et pas les banalités que je peux ignorer, mais beaucoup d'entre elles & # 8230; Continuer la lecture & # 8594;
If you’ve been reading my blog for a while now you will know that I love to challenge my threat hunting game with a lot of err…. banalities. And not the banalities I can ignore, but a lot of these … Continue reading → |
Threat Technical | ★★★★ | ||
| 2023-12-13 19:14:05 | Pandora Hvnc silencieuse, mais puissante, l'outil de cybercriminalité populaire qui vole sous le radar Silent, Yet Powerful Pandora hVNC, The Popular Cybercrime Tool That Flies Under the Radar (lien direct) |
> Pandora HVNC est un cheval de Troie (rat) d'accès à distance qui est annoncé sur les forums de cybercriminalité depuis 2021. Étonnamment, il a reçu peu d'attention de la communauté de la cybersécurité.Malgré cela, il reste un outil largement utilisé et est favorisé par de nombreux acteurs de menace.Pandora HVNC permet aux attaquants d'obtenir un contrôle secrète sur un ordinateur victime.Ce [& # 8230;]
Le post Silencieux, mais mais encorePuissant Pandora Hvnc, le populaire outil de cybercriminalité qui vole sous le radar est apparu pour la première fois sur slashnext .
>Pandora hVNC is a remote access trojan (RAT) that has been advertised on cybercrime forums since 2021. Surprisingly, it has received little attention from the cybersecurity community. Despite this, it remains a widely used tool and is favoured by many threat actors. Pandora hVNC enables attackers to gain covert control over a victim’s computer. This […] The post Silent, Yet Powerful Pandora hVNC, The Popular Cybercrime Tool That Flies Under the Radar first appeared on SlashNext. |
Tool Threat Technical | ★★★★ | ||
| 2023-12-13 17:00:00 | Floss pour gophers et crabes: extraire les chaînes de go et les exécutables de rouille FLOSS for Gophers and Crabs: Extracting Strings from Go and Rust Executables (lien direct) |
|
Tool Technical | ★★★★ | ||
| 2023-12-12 12:43:11 | Les États-Unis s'adressent à la sécurisation de la chaîne d'approvisionnement des logiciels pour la gestion des logiciels open source, SBOM US addresses securing software supply chain for managing open-source software, SBOM (lien direct) |
U.S.Les agences de sécurité ont publié un rapport technique de cybersécurité (CTR) qui développe un mémo de juin 2023 du ...
U.S. security agencies published a cybersecurity technical report (CTR) that expands on a June 2023 memo from the... |
Technical | ★★★ | ||
| 2023-12-09 12:46:00 | Les chercheurs déverrouillent les dernières techniques anti-analyse de Guloader. Researchers Unveal GuLoader Malware\\'s Latest Anti-Analysis Techniques (lien direct) |
Les chasseurs de menaces ont démasqué les dernières astuces adoptées par une souche malveillante appelée & nbsp; Guloder & nbsp; dans le but de rendre l'analyse plus difficile.
"Alors que la fonctionnalité principale de Guloader \\ n'a pas changé radicalement au cours des dernières années, ces mises à jour constantes dans leurs techniques d'obscurcissement font de l'analyse de Guloder un processus long et à forte intensité de ressources", Elastic Security Labs
Threat hunters have unmasked the latest tricks adopted by a malware strain called GuLoader in an effort to make analysis more challenging. "While GuLoader\'s core functionality hasn\'t changed drastically over the past few years, these constant updates in their obfuscation techniques make analyzing GuLoader a time-consuming and resource-intensive process," Elastic Security Labs |
Malware Threat Technical | ★★★★ | ||
| 2023-12-08 16:38:00 | Ransomware-as-a-Service: la menace croissante que vous ne pouvez pas ignorer Ransomware-as-a-Service: The Growing Threat You Can\\'t Ignore (lien direct) |
Les attaques de ransomwares et NBSP; sont devenues une menace importante et omniprésente dans le domaine en constante évolution de la cybersécurité.Parmi les différentes itérations des ransomwares, une tendance qui a pris de l'importance est le ransomware en tant que service (RAAS).Ce développement alarmant a transformé le paysage de la cybercriminalité, permettant aux personnes ayant une expertise technique limitée de mener des attaques dévastatrices.
Ransomware attacks have become a significant and pervasive threat in the ever-evolving realm of cybersecurity. Among the various iterations of ransomware, one trend that has gained prominence is Ransomware-as-a-Service (RaaS). This alarming development has transformed the cybercrime landscape, enabling individuals with limited technical expertise to carry out devastating attacks. |
Ransomware Threat Prediction Technical | ★★ | ||
| 2023-12-07 11:00:00 | Casinos de Las Vegas ciblés par des attaques de ransomwares Las Vegas casinos targeted by ransomware attacks (lien direct) |
The content of this post is solely the responsibility of the author. AT&T does not adopt or endorse any of the views, positions, or information provided by the author in this article. Introduction: Ever since the invention of internet browsers for personal computers came about in the 1990s, cybercrime has been on the rise. Almost 30 years after the invention of the Worldwide Web, cybercriminals have a variety of different methodologies and toolkits that they use on a daily basis to leverage vulnerabilities and commit crime. One of the most popular types of attacks that is used by threat actors is a ransomware attack. Most recently, several Las Vegas Casinos fell victim to a series of ransomware attacks. Las Vegas hacks: In mid-September 2023, two of the biggest Las Vegas casino and hotel chains found themselves to be victims of ransomware attacks. The two organizations that were targeted were Caesars Entertainment and MGM Resorts International. MGM Resorts International: The attack against MGM was first reported on September 11, 2023, when MGM personnel put out a public statement stating that a “cyber security incident” had affected some of its systems. On the days following this statement many guests reported numerous problems with the casino and the hotel operations of the company. On the casino side, many guests reported problems with slot machines and payout receipts. The slot machines in some of the MGM casinos were completely inoperable and, in the casinos, where they were operational, the machines were not able to print out the cash-out vouchers. On the hotel side, many of the organization\'s websites were inaccessible for a while after the attack. Guests across multiple MGM hotels reported issues with their mobile room keys not functioning, and new arrivals reported wait times of up to six hours to check in. A hacking group known as Scattered Spider has taken credit for the ransomware attack against MGM Resorts International. Scattered Spider first appeared in the cyber threat landscape in May 2022 and is thought to be individuals ages 19-22 and based out of the UK and USA. The attackers carried this attack out in three phases. The first phase was reconnaissance, in which they stalked the company’s LinkedIn Page and the employees that work there. The second phase of the attack was a vishing attack against MGM’s IT help desk. A vishing attack is when someone uses phone calls or voice communication to trick the victim into sharing personal information, credit card numbers, or credentials. Using the information they gathered on LinkedIn; the attackers were able to impersonate an MGM employee and tricked the help desk into giving them credentials into MGM systems. The attack\'s third phase was launching ransomware developed by another hacker group, ALPHAV. Scattered Spider rendered multiple systems throughout the organization useless unless the ransom is paid. Currently it is not known if MGM paid the ransom, but all casinos are once again fully operational. Caesars Entertainment: Days after MGM reported it had been hacked, Caesars Entertainment group disclosed to the SEC that they were also victims of a cyberattack around the same time as MGM. In a statement to the SEC, Caesar’s reported that confidential information about members of its customer loyalty program was stolen. Caesar’s representatives stated that the hackers were able to break into computer systems through a social engineering attack on an IT support contractor. Not much information is available about the execution of this attack. The use of a social engineering attack has led many people to believe that Scattered Spider was also behind this attack. The hackers demanded that Caesar’s pay a ransom of $30 million. It is reported that the organization paid $15million to the hackers and the company has “taken steps to ensure the stolen information is deleted by the hacker but canno | Ransomware Vulnerability Threat Mobile Technical | ★★★ | ||
| 2023-12-05 11:00:00 | Aperçu des systèmes de détection de fraude modernes Insights into modern fraud detection systems (lien direct) |
The content of this post is solely the responsibility of the author. AT&T does not adopt or endorse any of the views, positions, or information provided by the author in this article. Information security requirements and standards are in a constant state of evolution. Recent issues, such as COVID-19 and the growing global reliance on mobile devices and remote work solutions, have played important roles in this ongoing transformation. At the same time, the increasing sophistication of cyber attackers has added new layers of complexity to the cybersecurity landscape. In this article, I will explore the importance of implementing fraud detection systems as a crucial measure to mitigate the impact of both traditional and emerging fraudulent schemes. Challenges faced by financial institutions The landscape of user behavior has undergone significant shifts, primarily driven by external factors such as the COVID-19 pandemic. This factor led to an increase in online transactions, coupled with reduced income streams for many individuals, resulting in decreased spending in specific user categories. Additionally, local conflicts, like the war in Ukraine and Israel, influence spending patterns in particular regions. The implementation of restrictive measures and the resulting increase in stress levels have provided cyber crooks with more opportunities to exploit social engineering techniques through acts of intimidation. One prevalent scam involves fraudsters posing as bank security officials to deceive unsuspecting individuals. Another concerning trend is the rise of legitimate channels that drive people to scam schemes via mainstream advertising platforms like Google and Facebook. Furthermore, the economic hardships some people face have led them to seek alternative income sources, driving them to engage in various forms of online criminal activities. Some individuals become involved in schemes where they act as money mules or work in illegal call centers. It is challenging for financial institutions to guarantee absolute safety. Malicious individuals can present counterfeit identification to authorize transactions that were initially denied by the anti-fraud system. While financial institutions strive to know as much as possible about their clients and run transactions carefully, they are constrained by data retention limitations (typically several months) and the need to respond within seconds, as stipulated by Service Level Agreements. So, again, achieving complete certainty about every transaction remains a huge problem. Detecting suspicious activities becomes even more challenging when malicious employees request details about a specific client or transaction, as this falls within their routine work tasks. Some fraud detection systems use computer webcams or video surveillance cameras to monitor employee behavior. Modern surveillance systems have become more intelligent, leveraging artificial intelligence and historical data to perform comprehensive risk assessments and take action when unusual employee behavior is detected. However, these cameras may not always be effective in identifying deceitful behavior when employees remain almost motionless. Understanding fraud detection systems Fraud detection systems are designed to detect and prevent various forms of fraudulent activities, ranging from account hijacking and | Tool Threat Mobile Prediction Technical | ★★★ | ||
| 2023-12-02 00:06:39 | Preuve de vie… Proof of life… (lien direct) |
& # 8216; Blade Runner & # 8217;& # 8211;Le film Cult Classic & # 8211;nous enseigne que les (non) traits / comportements humains peuvent être détectés avec un soi-disant test de Voight-Kampff.Cet article consiste à discuter (de ne pas encore concevoir) un test similaire à nos fins de chasse aux menaces & # 8230;La clé & # 8230; Continuer la lecture & # 8594;
‘Blade Runner’ – the cult classic movie – teaches us that the (non-)human traits/behaviors can be detected with a so-called Voight-Kampff test. This post is about discussing (not designing yet) a similar test for our threat hunting purposes… The key … Continue reading → |
Threat Technical | ★★★ | ||
| 2023-11-29 13:01:45 | DET.Eng.Hebdomadaire # 49 - il n'y a pas de niveau de vache Det. Eng. Weekly #49 - There Is No Cow Level (lien direct) |
Imaginez un botnet de vaches. Imaginez
Imagine a botnet of cows.. IMAGINE |
Technical | ★★★ | ||
| 2023-11-27 22:00:00 | The Role of the CISO in Digital Transformation (lien direct) | Un CISO réussi devrait jouer un rôle de premier plan dans les initiatives de transformation numérique et de migration du cloud dans leur organisation.Le CISO est chargé de s'assurer que les contrôles de sécurité technique sont conçus et mis en œuvre de manière appropriée, et les modifications sont correctement gérées, en pensant à la sécurité dès le début.
A successful CISO should play a leading role in digital transformation and cloud migration initiatives in their organization. The CISO is responsible for making sure technical security controls are designed and implemented appropriately, and changes are properly managed, with security in mind from the very start. |
Cloud Technical | ★★ | ||
| 2023-11-27 16:31:36 | Sous la surface: comment les pirates tournent Netsupport contre les utilisateurs Beneath the Surface: How Hackers Turn NetSupport Against Users (lien direct) |
>  Les variantes de logiciels malveillants de NetSupport ont été une menace persistante, démontrant l'adaptabilité et les techniques d'infection en évolution.Dans cette analyse technique, nous plongeons ...
Les variantes de logiciels malveillants de NetSupport ont été une menace persistante, démontrant l'adaptabilité et les techniques d'infection en évolution.Dans cette analyse technique, nous plongeons ...
>  NetSupport malware variants have been a persistent threat, demonstrating adaptability and evolving infection techniques. In this technical analysis, we delve...
NetSupport malware variants have been a persistent threat, demonstrating adaptability and evolving infection techniques. In this technical analysis, we delve...
|
Malware Threat Technical | ★ | ||
| 2023-11-21 21:19:53 | Agent Tesla: le format d'archive ZPAQ inhabituel fournit des logiciels malveillants Agent Tesla: Unusual ZPAQ Archive Format Delivers Malware (lien direct) |
#### Description
Une nouvelle variante de l'agent Tesla a été découverte qui utilise l'extension de fichier archive ZPAQ et .wav pour infecter les systèmes et voler des informations à environ 40 navigateurs Web et divers clients de messagerie.ZPAQ est un format de compression de fichiers qui offre un meilleur rapport de compression et une fonction de journalisation par rapport à des formats largement utilisés comme ZIP et RAR.Cependant, le ZPAQ a un support logiciel limité, ce qui rend difficile le travail, en particulier pour les utilisateurs sans expertise technique.Le fichier exécutable .NET est gonflé avec zéro octets, ce qui permet aux acteurs de menace de contourner les mesures de sécurité traditionnelles et d'augmenter l'efficacité de leur attaque.
L'utilisation du format de compression ZPAQ soulève plus de questions que de réponses.Les hypothèses ici sont que les acteurs de la menace ciblent un groupe spécifique de personnes qui ont des connaissances techniques ou utilisent des outils d'archives moins connus, ou ils testent d'autres techniques pour diffuser plus rapidement les logiciels malveillants et contourner les logiciels de sécurité.
Le malware utilise Telegram en tant que C&C en raison de son utilisation juridique généralisée et du fait que son trafic est souvent autorisé à travers des pare-feu, ce qui en fait un support utile pour une communication secrète.Comme tout autre voleur, l'agent Tesla peut nuire non seulement aux particuliers mais aussi aux organisations.Il a gagné en popularité parmi les cybercriminels pour de nombreuses raisons, notamment la facilité d'utilisation, la polyvalence et l'abordabilité sur le Dark Web.
#### URL de référence (s)
1. https://www.gdatasoftware.com/blog/2023/11/37822-agent-Tesla-zpaq
#### Date de publication
20 novembre 2023
#### Auteurs)
Anna Lvova
#### Description A new variant of Agent Tesla has been discovered that uses the ZPAQ archive and .wav file extension to infect systems and steal information from approximately 40 web browsers and various email clients. ZPAQ is a file compression format that offers a better compression ratio and journaling function compared to widely used formats like ZIP and RAR. However, ZPAQ has limited software support, making it difficult to work with, especially for users without technical expertise. The .NET executable file is bloated with zero bytes, which allows threat actors to bypass traditional security measures and increase the effectiveness of their attack. The usage of the ZPAQ compression format raises more questions than answers. The assumptions here are that either threat actors target a specific group of people who have technical knowledge or use less widely known archive tools, or they are testing other techniques to spread malware faster and bypass security software. The malware uses Telegram as a C&C due to its widespread legal usage and the fact that its traffic is often allowed through firewalls, making it a useful medium for covert communication. Like any other stealer, Agent Tesla can harm not only private individuals but also organizations. It has gained popularity among cybercriminals for many reasons including ease of use, versatility, and affordability on the Dark Web. #### Reference URL(s) 1. https://www.gdatasoftware.com/blog/2023/11/37822-agent-tesla-zpaq #### Publication Date November 20, 2023 #### Author(s) Anna Lvova |
Malware Tool Threat Technical | ★★★ | ||
| 2023-11-21 20:45:00 | Le rôle du CISO dans la transformation numérique The Role of the CISO in Digital Transformation (lien direct) |
Un CISO réussi devrait jouer un rôle de premier plan dans les initiatives de transformation numérique et de migration du cloud dans leur organisation.Le CISO est chargé de s'assurer que les contrôles de sécurité technique sont conçus et mis en œuvre de manière appropriée, et les modifications sont correctement gérées, en pensant à la sécurité dès le début.
A successful CISO should play a leading role in digital transformation and cloud migration initiatives in their organization. The CISO is responsible for making sure technical security controls are designed and implemented appropriately, and changes are properly managed, with security in mind from the very start. |
Cloud Technical | ★★ | ||
| 2023-11-21 13:15:00 | Résultats de l'étude comparative sur les attaques de ransomware Linux et Windows, explorant les tendances notables et la montée des attaques sur les systèmes Linux Comparative Study Results on Linux and Windows Ransomware Attacks, Exploring Notable Trends and Surge in Attacks on Linux Systems (lien direct) |
> Fait saillie: & # 160;Évolution du paysage: Check Point Research (RCR) dévoile une étude complète explorant la surtension des attaques de ransomwares contre les systèmes Linux, faisant des comparaisons avec leurs homologues Windows.Tendance de simplification: L'analyse de la RCR en RCR révèle une tendance notable vers la simplification parmi les familles de ransomwares ciblant les linux.Les fonctionnalités de base réduites aux processus de cryptage de base, rendant ces menaces insaisissables et difficiles à détecter les informations de chiffrement: un examen comparatif des techniques de chiffrement entre Windows et Linux expose une préférence pour les algorithmes Chacha20 / RSA et AES / RSA dans les ransomwares de Linux.& # 160;Dans une étude récente menée par Check Point Research (RCR), un examen approfondi des attaques de ransomwares contre Linux et Windows [& # 8230;]
>Highlights: Evolving Landscape: Check Point Research (CPR) unveils a comprehensive study exploring the surge in ransomware attacks on Linux systems, drawing comparisons to their Windows counterparts. Simplification Trend: CPR’s analysis reveals a notable trend towards simplification among Linux-targeting ransomware families. Core functionalities reduced to basic encryption processes, making these threats elusive and challenging to detect Encryption Insights: A comparative examination of encryption techniques between Windows and Linux exposes a preference for ChaCha20/RSA and AES/RSA algorithms in Linux ransomware. In a recent study conducted by Check Point Research (CPR), an in-depth examination of ransomware attacks on Linux and Windows […] |
Ransomware Studies Prediction Technical | ★★★★ | ||
| 2023-11-21 08:35:02 | Prévenir les attaques de fatigue du MFA: sauvegarder votre organisation Preventing MFA Fatigue Attacks: Safeguarding Your Organization (lien direct) |
Gaining access to critical systems and stealing sensitive data are top objectives for most cybercriminals. Social engineering and phishing are powerful tools to help them achieve both. That\'s why multifactor authentication (MFA) has become such an important security measure for businesses and users. Without MFA as part of the user authentication process, it is much less challenging for an attacker with stolen credentials to authenticate a user\'s account. The primary goal of MFA is to reduce the risk of unauthorized access, especially in situations where passwords alone may not provide enough protection. Even if an attacker steals a user\'s password, with MFA they still need the second factor (and maybe others) to gain access to an account. Examples of MFA factors include biometrics, like fingerprints, and signals from user devices, like GPS location. MFA isn\'t a perfect solution, though-it can be bypassed. Adversaries are relentless in their efforts to undermine any security defenses standing in the way of their success. (The evolution of phish kits for stealing MFA tokens is evidence of that.) But sometimes, attackers will choose to take an in-your-face approach that is not very creative or technical. MFA fatigue attacks fall into that category. What are MFA fatigue attacks-and how do they work? MFA fatigue attacks, also known as MFA bombing or MFA spamming, are a form of social engineering. They are designed to wear down a user\'s patience so that they will accept an MFA request out of frustration or annoyance-and thus enable an attacker to access their account or device. Many people encounter MFA requests daily, or even multiple times per day, as they sign-in to various apps, sites, systems and platforms. Receiving MFA requests via email, phone or other devices as part of that process is a routine occurrence. So, it is logical for a user to assume that if they receive a push notification from an account that they know requires MFA, it is a legitimate request. And if they are very busy at the time that they receive several push notifications in quick succession to authenticate an account, they may be even more inclined to accept a request without scrutinizing it. Here\'s an overview of how an MFA attack works: A malicious actor obtains the username and password of their target. They can achieve this in various ways, from password-cracking tactics like brute-force attacks to targeted phishing attacks to purchasing stolen credentials on the dark web. The attacker then starts to send MFA notifications to the user continuously, usually via automation, until that individual feels overwhelmed and approves the login attempt just to make the requests stop. (Usually, the push notifications from MFA solutions require the user to simply click a “yes” button to authenticate from the registered device or email account.) Once the attacker has unauthorized access to the account, they can steal sensitive data, install malware and do other mischief, including impersonating the user they have compromised-taking their actions as far as they can or want to go. 3 examples of successful MFA fatigue attacks To help your users understand the risk of these attacks, you may want to include some real-world examples in your security awareness program on this topic. Here are three notable incidents, which are all associated with the same threat actor: Uber. In September 2022, Uber reported that an attacker affiliated with the threat actor group Lapsus$ had compromised a contractor\'s account. The attacker may have purchased corporate account credentials on the dark web, Uber said in a security update. The contractor received several MFA notifications as the attacker tried to access the account-and eventually accepted one. After the attacker logged in to the account, they proceeded to access other accounts, achieving privilege escalation. One action the attacker took was to reconfigure Uber\'s OpenDNS to display a graphic image on some of the company\'s internal sites. Cisco. Cisco suffer | Ransomware Data Breach Malware Tool Threat Technical | Uber | ★★★ | |
| 2023-11-20 22:01:00 | Les logiciels malveillants utilisent la trigonométrie pour suivre les traits de souris Malware Uses Trigonometry to Track Mouse Strokes (lien direct) |
La dernière version de l'infosaler Lummac2 comprend une nouvelle astuce anti-sandbox pour éviter de faire exploser lorsqu'aucun mouvement de souris humain n'est détecté.
The latest LummaC2 infostealer version includes a novel anti-sandbox trick to avoid detonating when no human mouse movements are detected. |
Malware Technical | ★★★ | ||
| 2023-11-20 17:57:48 | LUMMAC2 V4.0 MALWOWIRS VOLAGNE DES DONNÉES AVEC TRIGONOMÉTRIE pour détecter les utilisateurs humains LummaC2 v4.0 Malware Stealing Data with Trigonometry to Detect Human Users (lien direct) |
> Par deeba ahmed
Lummac2 est de retour en tant que Lummac2 v4.0.
Ceci est un article de HackRead.com Lire la publication originale: Lummac2 V4.0 MALWOWIRS VOLAGNE DES DONNÉES AVEC TRIGONOMÉTRIE Pour détecter les utilisateurs humains
>By Deeba Ahmed LummaC2 is back as LummaC2 v4.0. This is a post from HackRead.com Read the original post: LummaC2 v4.0 Malware Stealing Data with Trigonometry to Detect Human Users |
Malware Technical | ★★★★ | ||
| 2023-11-20 16:19:00 | Lummac2 Malware déploie une nouvelle technique anti-sandbox basée sur la trigonométrie LummaC2 Malware Deploys New Trigonometry-Based Anti-Sandbox Technique (lien direct) |
Le voleur malveillant connu sous le nom de Lummac2 (aka Lummma Stealer) propose désormais une nouvelle technique anti-sandbox qui exploite le principe mathématique de la trigonométrie pour échapper à la détection et exfiltrer des informations précieuses des hôtes infectés.
La méthode est conçue pour "retarder la détonation de l'échantillon jusqu'à ce que l'activité de la souris humaine soit détectée", a déclaré le chercheur en sécurité d'Outpost24 Alberto Mar & iacute; n dans une technique
The stealer malware known as LummaC2 (aka Lumma Stealer) now features a new anti-sandbox technique that leverages the mathematical principle of trigonometry to evade detection and exfiltrate valuable information from infected hosts. The method is designed to "delay detonation of the sample until human mouse activity is detected," Outpost24 security researcher Alberto Marín said in a technical |
Malware Technical | ★★ | ||
| 2023-11-20 15:42:54 | Vx-Underground Malware Collective encadré par Phobos Ransomware VX-Underground malware collective framed by Phobos ransomware (lien direct) |
Une nouvelle variante de ransomware Phobos encadre le populaire collectif de partage de logiciels malveillants VX-Underground, indiquant que le groupe est derrière les attaques à l'aide de l'encrypteur.[...]
A new Phobos ransomware variant frames the popular VX-Underground malware-sharing collective, indicating the group is behind attacks using the encryptor. [...] |
Ransomware Malware Technical | ★★★★ | ||
| 2023-11-20 08:47:33 | Campagne d'attaque de cryptojacking contre les serveurs Web Apache à l'aide de Cobalt Strike Cryptojacking Attack Campaign Against Apache Web Servers Using Cobalt Strike (lien direct) |
Ahnlab Security Emergency Response Center (ASEC) surveillait les attaques contre les serveurs Web vulnérables qui ont des vulnérabilités non corrigées ouêtre mal géré.Étant donné que les serveurs Web sont exposés à l'extérieur dans le but de fournir des services Web à tous les utilisateurs disponibles, ceux-ci deviennent des objectifs d'attaque majeurs pour les acteurs de la menace.Les principaux exemples de services Web qui prennent en charge les environnements Windows incluent les services d'information Internet (IIS), Apache, Apache Tomcat et Nginx.Bien que le service Web Apache soit généralement utilisé dans les environnements Linux, il y en a ...
AhnLab Security Emergency response Center (ASEC) is monitoring attacks against vulnerable web servers that have unpatched vulnerabilities or are being poorly managed. Because web servers are externally exposed for the purpose of providing web services to all available users, these become major attack targets for threat actors. Major examples of web services that support Windows environments include Internet Information Services (IIS), Apache, Apache Tomcat, and Nginx. While the Apache web service is usually used in Linux environments, there are some... |
Vulnerability Threat Technical | ★★★ | ||
| 2023-11-20 08:00:00 | Une référence de détection et de réponse conçue pour le nuage A Detection and Response Benchmark Designed for the Cloud (lien direct) |
La performance de votre Centre d'opération de sécurité \\ répond-elle à l'indice de référence 5/5/5 pour la détection des menaces cloud et la réponse aux incidents?
Does your security operation center\'s performance meet the 5/5/5 benchmark for cloud threat detection and incident response? |
Threat Cloud Technical | ★★★★ | ||
| 2023-11-20 07:55:44 | Distribution du fichier LNK malveillant déguisé en matière de matériel promotionnel d'entreprise Distribution of Malicious LNK File Disguised as Producing Corporate Promotional Materials (lien direct) |
Récemment, AhnLab Security Response Center (ASEC) a identifié un fichier LNK malveillant distribué à financier etPersonnel de Blockchain Corporation par e-mail et autres façons.Le fichier LNK malveillant est distribué via URL et AHNLAB Smart Defence (ASD) a confirmé les URL suivantes.Le fichier téléchargé est un fichier compressé nommé & # 8220; Blockchain Corporate Solution Handbook Production.zip & # 8221;.L'acteur de menace a alternativement téléchargé un fichier malveillant et un fichier légitime sur les URL, provoquant une confusion dans l'analyse.Quand le malveillant ...
Recently, AhnLab Security Emergency response Center (ASEC) has identified a malicious LNK file being distributed to financial and blockchain corporation personnel through email and other ways. The malicious LNK file is distributed via URLs and AhnLab Smart Defense (ASD) has confirmed the following URLs. The file being downloaded is a compressed file named “Blockchain Corporate Solution Handbook Production.zip”. The threat actor alternately uploaded a malicious file and a legitimate file at the URLs, causing confusion in analysis. When the malicious... |
Threat Technical | ★★ | ||
| 2023-11-20 06:31:18 | Circonstances d'une attaque exploitant un programme de gestion des actifs (Andariel Group) Circumstances of an Attack Exploiting an Asset Management Program (Andariel Group) (lien direct) |
L'équipe d'analyse ASEC a identifié les circonstances du groupe Andariel distribuant des logiciels malveillants via une attaque en utilisant une certaine gestion des actifsprogramme.Le groupe Andariel est connu pour être dans une relation coopérative avec ou une organisation filiale du groupe Lazare.Le groupe Andariel lance généralement des attaques de phishing de lance, d'arrosage ou de chaîne d'approvisionnement pour la pénétration initiale.Il existe également un cas où le groupe a exploité une solution de gestion centrale pendant le processus d'installation de logiciels malveillants.Récemment, le groupe Andariel ...
The ASEC analysis team identified the circumstances of the Andariel group distributing malware via an attack using a certain asset management program. The Andariel group is known to be in a cooperative relationship with or a subsidiary organization of the Lazarus group. The Andariel group usually launches spear phishing, watering hole, or supply chain attacks for initial penetration. There is also a case where the group exploited a central management solution during the malware installation process. Recently, the Andariel group... |
Malware Technical | APT 38 APT 38 | ★★★ | |
| 2023-11-16 19:21:00 | Les experts découvrent Darkcasino: Nouvelle menace émergente exploite Winrar Flaw Experts Uncover DarkCasino: New Emerging APT Threat Exploiting WinRAR Flaw (lien direct) |
Un groupe de piratage qui a exploité une faille de sécurité récemment divulguée dans le logiciel Winrar en tant que jour zéro a maintenant été classé comme une menace persistante avancée entièrement nouvelle (APT).
La société de cybersécurité NSFOCUS a décrit Darkcasino comme un acteur "à motivation économique" qui a été révélé pour la première fois en 2021.
"Darkcasino est un acteur de menace approprié avec une forte capacité technique et d'apprentissage, qui est bonne
A hacking group that leveraged a recently disclosed security flaw in the WinRAR software as a zero-day has now been categorized as an entirely new advanced persistent threat (APT). Cybersecurity company NSFOCUS has described DarkCasino as an "economically motivated" actor that first came to light in 2021. "DarkCasino is an APT threat actor with strong technical and learning ability, who is good |
Threat Technical | ★★ | ||
| 2023-11-16 16:19:54 | Chasse des éléphants |À l'intérieur d'un groupe de hack-for-hire indien Elephant Hunting | Inside an Indian Hack-For-Hire Group (lien direct) |
Exploration des subtilités techniques d'Appin, un groupe hack-for-embauche, révélant l'attribution confirmée et l'activité de menace mondiale, ancienne et nouvelle.
Exploring the technical intricacies of Appin, a hack-for-hire group, revealing confirmed attribution and global threat activity, both old and new. |
Threat Technical | ★★ | ||
| 2023-11-16 14:15:19 | Informations exploitables: simplifier l'explication des menaces via le résumé de la condamnation Actionable Insights: Simplifying Threat Explainability via the Condemnation Summary (lien direct) |
In this blog series we cover how to improve your company\'s security posture with actionable insights. Actionable insights are a critical tool to help you improve your security posture and stop initial compromise in the attack chain. You can use them to identify and respond to potential risks, enhance your incident response capabilities, and make more informed security decisions. In previous actionable insights blog posts, we covered these topics: People risk Origin risk Business email compromise (BEC) risk Ensuring proper risk context Risk efficacy Telephone-oriented attack delivery (TOAD) risk Threat intelligence Your risk profile In this post, we are excited to announce the new TAP Condemnation Summary-which is available to all Proofpoint Targeted Attack Protection (TAP) customers who use the Proofpoint Aegis threat protection platform. We\'ll explain why it is an invaluable resource and we\'ll explore some of its key reports. Threat explainability: Introducing the Condemnation Summary In the ever-evolving cybersecurity landscape, clear communication and rapid understanding of email threats are essential. Proofpoint introduced the Condemnation Summary to enhance threat visibility and explain-in plain, everyday language-why a particular threat is condemned. The summary makes it easier for both technical and nontechnical users to comprehend email threats. You can find the TAP Condemnation Summary in the Evidence section of the threat details page for any individual threat within your Aegis platform. Let\'s explore how this new feature can help your business. Insights: What you can learn from the Condemnation Summary The Condemnation Summary helps demystify email threats and streamline the decision-making process for threat remediation. Here\'s what you can expect from this innovative feature. User and VIP insights The Condemnation Summary includes a highlights card that spotlights impacted users and VIPs. With drilldown options and actionable items, you can quickly determine who is affected. You can use these insights to understand the steps you need to take to mitigate the threat. Details about affected users shown in the Condemnation Summary. Threat state overview This section of the summary breaks down the state of the threat or campaign, complete with timestamps. A chronological view provides you with a clear understanding of how the threat evolved, so you can assess its severity and impact. The threat state overview section in the Condemnation Summary. User-friendly descriptions The Condemnation Summary offers high-level observations from our behavioral and machine learning detection layers. Threats are described in everyday language. So nontechnical users can better grasp the nature of a threat and its potential consequences. High-level observations in plain language in the Condemnation Summary. Source attribution It\'s helpful to understand where a threat originated. Condemnation Sources gives you insight into which sources contributed to the detection and condemnation of the threat. The Condemnation Sources section in the Condemnation Summary. Targeted controls: Taking action The Condemnation Summary isn\'t just a feature for visibility or explainability. It\'s a tool for action. Here\'s how to make the most of this new feature: Mitigate threats faster. With user and VIP insights, you can respond promptly to threats that are impacting specific individuals. Take immediate actions to protect these users and mitigate risks. Improve your communication about threats. The user-friendly descriptions in the Condemnation Summary make it easier to communicate threat details to nontechnical stakeholders. This, in turn, helps to foster better collaboration around security across your business. See how threats evolve. When you have a timeline of a threat\'s progression, you can assess how a threat evolved and whether it is part of a broader campaign. Track where threats come from. It is cruci | Tool Threat Technical | ★★★ | ||
| 2023-11-15 22:52:24 | Lolbins pour les connaisseurs… partie 3 Lolbins for connoisseurs… Part 3 (lien direct) |
J'adore explorer des chemins logiciels inexplorés.Et pas nécessairement au niveau de l'assemblage & # 8211;et cela parce que souvent & # 8230;Ce n'est même pas nécessaire.Ils me conduisent souvent à des endroits vraiment étranges f.ex.Découvrir un logiciel qui lit une adresse mémoire & # 8230; | Technical | ★★★ | ||
| 2023-11-15 03:12:53 | Les institutions financières à New York sont confrontées à des règles plus strictes de cybersécurité Financial Institutions in New York Face Stricter Cybersecurity Rules (lien direct) |
Les conseils d'administration doivent maintenir un niveau approprié d'expertise en cyber, des incidents doivent être signalés dans les 72 heures suivant la détermination et tous les paiements de rançon effectués doivent être signalés dans une journée.Ce ne sont que quelques-uns des modifications apportées par le Département des services financiers de l'État de New York à ses exigences de cybersécurité pour les services financiers (23 NYCRR 500), à compter du 1er novembre 2023. Ce resserrement des règnes tiendra les entreprises à un examen supérieur de la sécurité et à faireLes parties prenantes techniques et non techniques comme plus responsables.Bien que cela puisse sembler bénin, le mouvement est plus ...
Boards of directors need to maintain an appropriate level of cyber expertise, incidents must be reported within 72 hours after determination, and all ransom payments made must be reported within a day. Those are just some of the changes made by The New York State Department of Financial Services to its Cybersecurity Requirements for Financial Services (23 NYCRR 500) , effective November 1, 2023. This tightening of the reigns will hold businesses to higher security scrutiny and make technical and non-technical stakeholders alike more accountable. While this may seem benign, the move is more... |
Technical | ★★ | ||
| 2023-11-14 14:00:23 | Livre blanc technique de Socradar: \\ 'un 100m + USD négociateur \\'s Guide pour survivre les ransomwares \\' SOCRadar Technical Whitepaper: \\'A 100M+ USD Negotiator\\'s Guide to Surviving Ransomware\\' (lien direct) |
À une époque où les menaces numériques évoluent constamment, les attaques de ransomwares sont apparues comme un formidable ...
In an era where digital threats constantly evolve, ransomware attacks have emerged as a formidable... |
Ransomware Technical | ★★ | ||
| 2023-11-14 00:00:00 | Les évaluations de la cybersécurité et la fortification des défenses numériques avec CRQ évaluant les cyber-risques sont essentielles pour développer des plans d'action basés sur les données pour stimuler les défenses numériques.Découvrez quelle évaluation vous soutient le mieux pour atteindre les objectifs de cybersécurité.En savoir plus Cybersecurity Assessments and Fortifying Digital Defenses With CRQ Assessing cyber risk is critical for developing data-driven action plans to boost digital defenses. Discover which assessment best supports you in reaching cybersecurity goals. Read More (lien direct) |
The Vital Role of Cyber Assessments and Fortifying Digital Defenses âAs cyber attacks become more sophisticated and complex and regulatory bodies impose stricter cybersecurity requirements, organizations worldwide are facing mounting pressure to adopt security solutions. Understandably, many executives have reacted by implementing a multitude of security tools that supposedly complement one another and better protect organization systems.  âHowever, this strategy often falls short, preventing stakeholders from comprehensively understanding their unique cyber environments. Instead of developing an intimate knowledge of the business units most vulnerable to threats, organizations risk exposing their assets due to their adopt-as-many-tools-as-possible approach. âAfter all, providing effective protection against what remains relatively unknown is impossible.âThis widespread ignorance about the cyber environment is precisely why cyber assessments are so crucial. These evaluations offer a structured approach to identifying, analyzing, and mitigating digital vulnerabilities and provide organizations with a detailed blueprint of their most susceptible business units.âNot All Assessments Are Created Equal âWhile all cyber assessments help businesses become more aware of their cyber risk levels, itâs essential to note that not all reveal the same insights. There are various types of assessments, each tailored to meet specific goals. Some analyze overall cybersecurity posture, while others dive deeper into specific areas, such as compliance and incident response planning. âEach of the available assessments offers organizations valuable data, security leaders can leverage to make informed decisions. Before choosing which IT environment evaluation to invest in, itâs important to discuss with key stakeholders and executives what youâd like to achieve with the new information youâll discover. âDefining a Goal: Risk, Governance, or Compliance âA great place to start when determining organizational goals for the assessment is cybersecurity risk, governance, and compliance (GRC). Cyber GRC is a commonly used industry framework and set of practices that businesses of all sizes harness to manage and secure their information systems, data, and assets. Each of these components serves a specific purpose.  âRisk âA cyber risk assessment aims to identify the factors that make a company vulnerable, generate conclusions regarding the vectors most likely to be the origin of an attack (due to those vulnerabilities), and offer insights about the level of damage a cyber event would cause. âCompanies can proactively address the relevant business units by revealing threat likelihood levels. This information also helps cyber teams determine which areas they want to devote the most resources to. It\'s important to note that both qualitative and quantitative risk assessments exist. âGovernance âThe role of cyber governance is to establish a framework of policies, procedures, and decision-making processes to ensure that cybersecurity efforts are embedded within the broader company culture and align with business goals. It likewise evaluates how well cyber strategies match overall objectives, offering cyber teams an opportunity to better coordinate with other executives and teams. âAn assessment focused on governance also determines if cybersecurity responsibilities are appropriately distributed throughout the organization, such as whether employees are required to use multi-factor authentication (MFA). Other included evaluation points are training programs, incident reporting mechanisms, and event response planning, all of which directly impact an organizationâs risk level. âCompliance âOne would conduct a compliance assessment to ensure an organization | Data Breach Tool Vulnerability Threat Technical | ★★★ | ||
| 2023-11-13 06:18:08 | Permettre des mises à jour de signature de spam en temps réel sans ralentir les performances Enabling Real-Time Spam Signature Updates without Slowing Down Performance (lien direct) |
Engineering Insights est une série de blogs en cours qui donne à des coulisses sur les défis techniques, les leçons et les avancées qui aident nos clients à protéger les personnes et à défendre les données chaque jour.Chaque message est un compte de première main de l'un de nos ingénieurs sur le processus qui a conduit à une innovation de preuves. ProofPoint Conformité intelligente classe le contenu texte qui provient du contenu des médias sociaux partout aux demandes fournies par le client.Une partie de notre système détecte le contenu du spam, généralement à partir de sources basées sur les médias sociaux. Un défi commun pour les systèmes de détection de spam est que les adversaires modifient leur contenu pour échapper à la détection.Nous avons un algorithme qui résout ce problème. Parfois, les faux positifs doivent également être corrigés.Nous gérons cela en maintenant une liste d'exclusion et une liste positive de signatures de spam.Dans cet article de blog, nous expliquons comment nous mettons à jour les signatures de spam en temps réel sans avoir un impact négatif sur les performances. Une nécessité d'évoluer sans compromettre les performances Au fur et à mesure que la clientèle de Proofpoint Patrol a augmenté, nous avons dû la mettre à l'échelle afin de continuer à fournir des services rapides et fiables.À l'origine, le service de catégorisation de texte était intégré à notre service de classificateur de base et n'a pas pu être mis à l'échelle indépendamment.Nous avons décidé de le séparer en son propre service afin que nous puissions le développer et l'étendre indépendamment de notre service de classificateur. Notre première libération de ce nouveau système nous a permis d'évoluer plus efficacement et a entraîné une forte diminution de la latence.Une partie de l'amélioration des performances est venue du chargement de l'ensemble de signature de spam dans la mémoire au démarrage du service. Cependant, cela a conduit à une limitation où nous ne pouvions pas facilement mettre à jour nos ensembles de signature positive ou d'exclusion sans reconstruire et redéployer notre application.Cela signifiait que notre système de spam n'apprendrait pas de nouvelles signatures de spam au fil du temps, ce qui entraînerait également une augmentation des faux négatifs. Une solution de stockage de données en mémoire: redis Peu de temps après avoir rejoint Proofpoint, j'ai été chargé d'améliorer le système de détection des spams pour apprendre au fil du temps, tout en conservant les avantages sociaux.Nous avions besoin d'une solution avec une latence à faible lecture, et idéalement une latence d'écriture faible, car notre rapport lecture / écriture était assis vers 80/20. Une solution potentielle était Redis, une solution de stockage de données en mémoire open source.Amazon propose une implémentation de Redis-MemoryDB-qui peut fournir une persistance de données au-delà de ce qu'une solution de cache typique peut offrir. Présentation d'une solution de stockage de signature en mémoire. À la fin des performances, Amazon possède une latence de lecture microseconde et une latence d'écriture à un chiffre.Tout en étudiant des solutions potentielles, nous avons remarqué des latences similaires avec notre charge de travail. Nous avons généralement plus de requêtes de lecture que l'écriture;Cependant, nous avons des pics occasionnels dans les requêtes d'écriture. Un graphique montrant les commandes de lecture au fil du temps. Un graphique montrant des commandes d'écriture au fil du temps. Le fait que MemoryDB persiste nos signatures de spam et notre liste d'exclusion permettrait à notre système de stocker de nouvelles signatures de spam lors de l'exécution.Cela permettrait également à notre système de s'améliorer avec le temps.Nous serions également en mesure de répondre rapidement aux rapports faux positifs en mettant à jour la liste en temps réel. Nos résultats Après avoir terminé notre | Spam Cloud Technical | ★★★ | ||
| 2023-11-09 16:20:00 | MUDDYC2GO: Nouveau cadre C2 Iranian Hackers Utilisation contre Israël MuddyC2Go: New C2 Framework Iranian Hackers Using Against Israel (lien direct) |
Des acteurs iraniens de l'État-nation ont été observés en utilisant un cadre de commandement et de contrôle (C2) sans papiers précédemment appelé Muddyc2go dans le cadre d'attaques ciblant Israël.
"Le composant Web du Framework \\ est rédigé dans le langage de programmation Go", a déclaré Simon Kenin, chercheur en sécurité de Deep Instinct, dans un rapport technique publié mercredi.
L'outil a été attribué à Muddywater, un iranien
Iranian nation-state actors have been observed using a previously undocumented command-and-control (C2) framework called MuddyC2Go as part of attacks targeting Israel. "The framework\'s web component is written in the Go programming language," Deep Instinct security researcher Simon Kenin said in a technical report published Wednesday. The tool has been attributed to MuddyWater, an Iranian |
Tool Technical | ★★★ | ||
| 2023-11-08 16:30:00 | Guide: comment VCISOS, MSPS et MSSP peuvent protéger leurs clients des risques Gen AI Guide: How vCISOs, MSPs and MSSPs Can Keep their Customers Safe from Gen AI Risks (lien direct) |
Téléchargez le guide gratuit, "C'est un monde d'IA génératif: comment VCISO, MSPS et MSSPS peuvent protéger leurs clients des risques Gen Gen AI."
Chatgpt se vante désormais de 1,5 à 2 milliards de visites par mois.D'innombrables ventes, marketing, RH, exécutif informatique, soutien technique, opérations, finances et autres fonctions alimentent les invites de données et les requêtes dans les moteurs d'IA génératifs.Ils utilisent ces outils pour écrire
Download the free guide, "It\'s a Generative AI World: How vCISOs, MSPs and MSSPs Can Keep their Customers Safe from Gen AI Risks." ChatGPT now boasts anywhere from 1.5 to 2 billion visits per month. Countless sales, marketing, HR, IT executive, technical support, operations, finance and other functions are feeding data prompts and queries into generative AI engines. They use these tools to write |
Tool Technical | ChatGPT | ★★ | |
| 2023-11-08 07:33:45 | AVERTISSEMENT contre Phobos Ransomware distribué via RDP vulnérable Warning Against Phobos Ransomware Distributed via Vulnerable RDP (lien direct) |
Ahnlab Security Emergency Response Center (ASEC) a récemment découvert la distribution active des ransomwares de phobos.Phobos est une variante connue pour partager des similitudes techniques et opérationnelles avec les ransomwares Dharma et Crysis.Ces souches de ransomware ciblent généralement les services de protocole de bureau à distance externe en externe (RDP) avec des titres vulnérables en tant que vecteurs d'attaque.Compte tenu de la présence fréquente de la distribution des ransomwares qui exploite ces RDP vulnérables comme points d'accès initiaux, il est conseillé aux administrateurs d'être prudents.[1] [2] [3] 1. Présentation du ransomware phobos Phobos Ransomware ...
AhnLab Security Emergency response Center (ASEC) has recently discovered the active distribution of the Phobos ransomware. Phobos is a variant known for sharing technical and operational similarities with the Dharma and CrySis ransomware. These ransomware strains typically target externally exposed Remote Desktop Protocol (RDP) services with vulnerable securities as attack vectors. Given the frequent occurrence of ransomware distribution that leverages these vulnerable RDPs as initial access points, administrators are advised to be cautious. [1] [2] [3] 1. Phobos Ransomware Overview Phobos ransomware... |
Ransomware Technical | ★★★ | ||
| 2023-11-06 21:23:00 | Nouvel Google Cloud Rat utilise des événements de calendrier pour C2 Novel Google Cloud RAT Uses Calendar Events for C2 (lien direct) |
Les cybercriminels abusent des fonctions légitimes au sein des services cloud, et les fournisseurs ne peuvent pas les arrêter totalement, en particulier en ce qui concerne des approches innovantes comme celle-ci.
Cybercriminals are abusing legitimate functions within cloud services, and providers can\'t totally stop them, especially when it comes to innovative approaches like this. |
Cloud Technical | ★★★★★ | ||
| 2023-11-06 03:00:54 | Ce que nous avons appris du rapport "le Cyber-Resilient CEO" What We Learned From "The Cyber-Resilient CEO" Report (lien direct) |
Dans le paysage numérique d'aujourd'hui, la cybersécurité n'est pas seulement une préoccupation technique;C'est un impératif stratégique.Alors que nous nous plongeons dans les idées d'un récent rapport d'Accenture intitulé «Le PDG du cyber-résilient», nous découvrirons le rôle essentiel des PDG dans la sauvegarde de leurs organisations contre les cyber-menaces.Découvrez comment un groupe sélectionné de dirigeants navigue sur le terrain complexe des cyber-vulnérabilités, faisant de la cybersécurité une pierre angulaire de la résilience commerciale.Les PDG des complexités de cyber-menace reconnaissent que le monde des affaires est en proie à des cyber-vulnérabilités.Ce rapport révèle ce perturbateur ...
In today\'s digital landscape, cybersecurity is not just a technical concern; it\'s a strategic imperative. As we delve into the insights from a recent report from Accenture titled " The Cyber-Resilient CEO ," we\'ll uncover CEOs\' critical role in safeguarding their organizations against cyber threats. Discover how a select group of leaders navigates the complex terrain of cyber vulnerabilities, making cybersecurity a cornerstone of business resilience. The Cyber-Threat Complexities CEOs recognize that the business world is rife with cyber vulnerabilities. This report reveals that disruptive... |
Vulnerability Guideline Technical | ★★★ | ||
| 2023-11-05 17:45:05 | Alors, avez-vous entendu parler de Havoc, le nouvel outil du cyber arsenal? So, have you heard about Havoc, the new tool in the cyber arsenal? (lien direct) |
Permettez-moi de vous donner la baisse de ce que le brassage dans le métro numérique avec ce nouveau logiciel appelé Havoc.Maintenant, vous pourriez être [Plus ...]
Let me give you the lowdown on what’s brewing in the digital underground with this fresh piece of software called Havoc. Now, you might be [more...] |
Tool Tool Technical | ★★★★ | ||
| 2023-11-02 12:00:24 | Plus de moyens pour les utilisateurs d'identifier les applications testées sur la sécurité indépendante sur Google Play More ways for users to identify independently security tested apps on Google Play (lien direct) |
Posted by Nataliya Stanetsky, Android Security and Privacy Team
Keeping Google Play safe for users and developers remains a top priority for Google. As users increasingly prioritize their digital privacy and security, we continue to invest in our Data Safety section and transparency labeling efforts to help users make more informed choices about the apps they use.
Research shows that transparent security labeling plays a crucial role in consumer risk perception, building trust, and influencing product purchasing decisions. We believe the same principles apply for labeling and badging in the Google Play store. The transparency of an app\'s data security and privacy play a key role in a user\'s decision to download, trust, and use an app.
Highlighting Independently Security Tested VPN Apps
Last year, App Defense Alliance (ADA) introduced MASA (Mobile App Security Assessment), which allows developers to have their apps independently validated against a global security standard. This signals to users that an independent third-party has validated that the developers designed their apps to meet these industry mobile security and privacy minimum best practices and the developers are going the extra mile to identify and mitigate vulnerabilities. This, in turn, makes it harder for attackers to reach users\' devices and improves app quality across the ecosystem. Upon completion of the successful validation, Google Play gives developers the option to declare an “Independent security review” badge in its Data Safety section, as shown in the image below. While certification to baseline security standards does not imply that a product is free of vulnerabilities, the badge associated with these validated apps helps users see at-a-glance that a developer has prioritized security and privacy practices and committed to user safety.
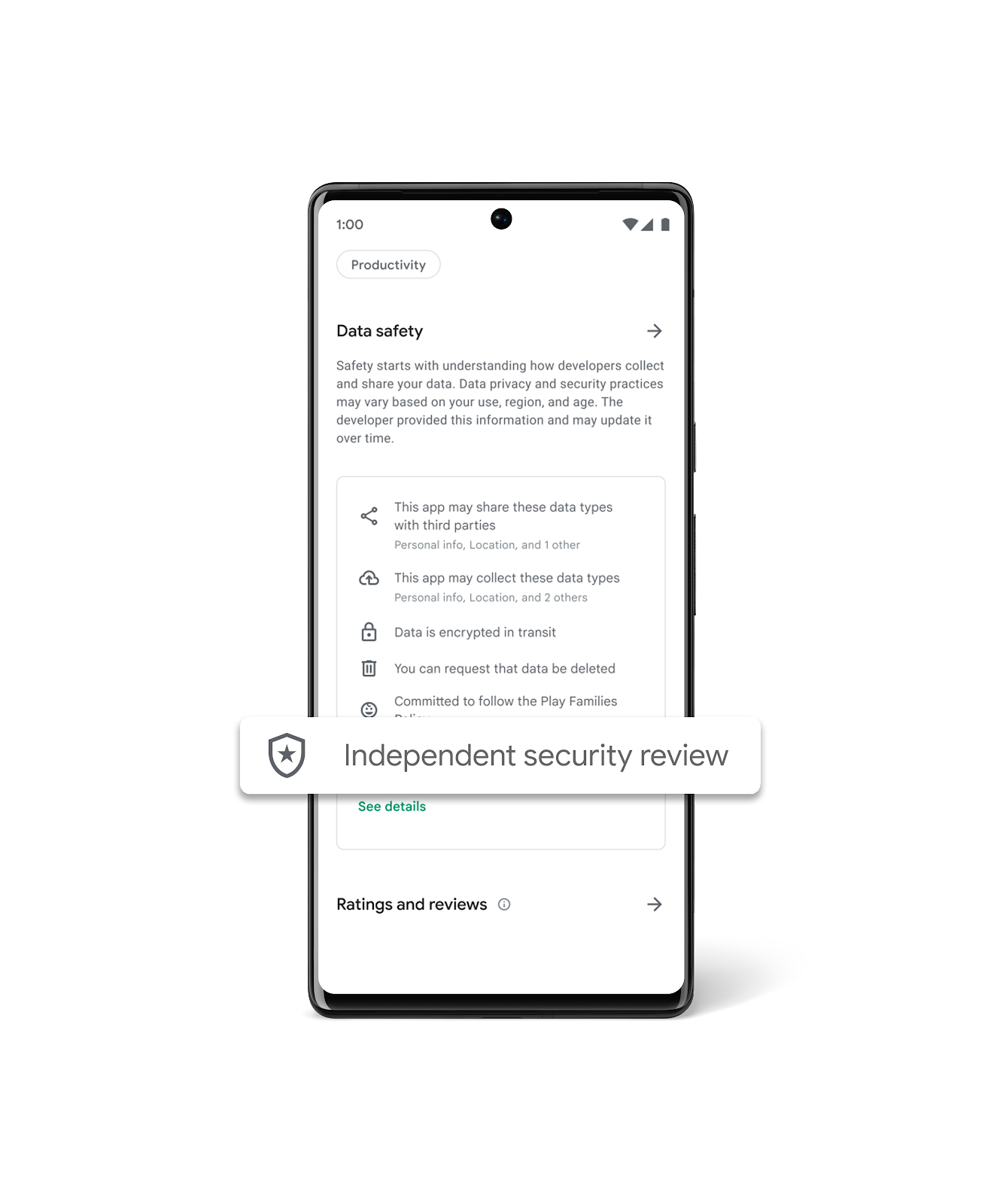 To help give users a simplified view of which apps have undergone an independent security validation, we\'re introducing a new Google Play store banner for specific app types, starting with VPN apps. We\'ve launched this banner beginning with VPN apps due to the sensitive and significant amount of user data these apps handle. When a user searches for VPN apps, they will now see a banner at the top of Google Play that educates them about the “Independent security review” badge in the Data Safety Section. Users also have the ability to “Learn More”, which redirects them to the App Validation Directory, a centralized place to view all VPN apps that have been independently security reviewed. Users can also discover additional technical assessment details in the App Validation Directory, helping them to make more informed decisions about what VPN apps to download, use, and trust with their data.
To help give users a simplified view of which apps have undergone an independent security validation, we\'re introducing a new Google Play store banner for specific app types, starting with VPN apps. We\'ve launched this banner beginning with VPN apps due to the sensitive and significant amount of user data these apps handle. When a user searches for VPN apps, they will now see a banner at the top of Google Play that educates them about the “Independent security review” badge in the Data Safety Section. Users also have the ability to “Learn More”, which redirects them to the App Validation Directory, a centralized place to view all VPN apps that have been independently security reviewed. Users can also discover additional technical assessment details in the App Validation Directory, helping them to make more informed decisions about what VPN apps to download, use, and trust with their data.
|
Tool Vulnerability Mobile Technical | ★★ | ||
| 2023-11-02 11:30:00 | Bugy octets # 216 & # 8211;Injections SQL, Android XSS et rédaction de rapports de qualité Bug Bytes #216 – SQL injections, Android XSS and Writing Quality Reports (lien direct) |
> Bug Bytes est une newsletter hebdomadaire organisée par les membres de la communauté Bug Bounty.La deuxième série est organisée par InsiderPhd.Chaque semaine, elle nous tient à jour avec une liste complète des articles, des outils, des tutoriels et des ressources.Ce numéro couvre la semaine du 23 octobre au 29 octobre Intigriti News de mon cahier
>Bug Bytes is a weekly newsletter curated by members of the bug bounty community. The second series is curated by InsiderPhD. Every week, she keeps us up to date with a comprehensive list of write-ups, tools, tutorials and resources. This issue covers the week from October 23rd to October 29th Intigriti News From my notebook |
Tool Mobile Technical | ★★★ | ||
| 2023-11-01 16:25:55 | Pouses de bibliothèque publique de Toronto causées par une attaque de ransomware Black Basta Toronto Public Library outages caused by Black Basta ransomware attack (lien direct) |
La bibliothèque publique de Toronto connaît des pannes techniques en cours en raison d'une attaque noire de ransomware de Basta.[...]
The Toronto Public Library is experiencing ongoing technical outages due to a Black Basta ransomware attack. [...] |
Ransomware Technical | ★★ | ||
| 2023-10-29 23:17:07 | Enquêtes Telegram et Osint Telegram and OSINT Investigations (lien direct) |
Telegram en tant que l'une de vos sources OSINT alors que la répression de la désinformation s'intensifie sur les plateformes de médias sociaux traditionnelles, Telegram est devenu un nouveau sanctuaire [plus ...]
Telegram as one of your OSINT sources As the crackdown on misinformation intensifies on traditional social media platforms, Telegram has emerged as a new sanctuary [more...] |
Technical | ★★★★ | ||
| 2023-10-28 21:15:23 | Au-delà du bon ol \\ '.Bashrc Entrée… Partie 3 Beyond the good ol\\' .bashrc entry… Part 3 (lien direct) |
Mise à jour après l'avoir publié, @netspooky m'a fait un ping avec quelques informations supplémentaires.Apparemment, cette technique est connue depuis au moins 2019 et a été démo par @ zer0pwn en premier.Ce billet de blog de MCG le décrit.Old Post Cette entrée est A & # 8230; Continuer la lecture & # 8594;
Update After I posted it, @netspooky pinged me with some additional info. Apparently, this technique is known since at least 2019 and was demoed by @zer0pwn first. This blog post from MCG describes it. Old Post This entry is a … Continue reading → |
Technical | ★★★ | ||
| 2023-10-26 13:08:32 | Anatomie d'une violation d'initiés provenant de l'ordinateur portable d'un entrepreneur \\ Anatomy of an insider breach originating from a contractor\\'s laptop (lien direct) |
Keith Siepel, responsable informatique chez Hydrotech, Inc., examine une cyber-menace avancée découverte par DarkTrace sur un réseau de client \\.
Keith Siepel, IT Manager at Hydrotech, Inc., examines an advanced cyber-threat discovered by Darktrace on a customer\'s network. |
Technical | ★★★ | ||
| 2023-10-26 13:08:32 | Anatomie d'un cheval de Troie zéro-jour capturé par notre appliance Darktrace Anatomy of a zero-day trojan caught by our Darktrace appliance (lien direct) |
Keith Siepel, responsable informatique chez Hydrotech, Inc., examine une cyber-menace avancée découverte par DarkTrace sur un réseau de client \\.
Keith Siepel, IT Manager at Hydrotech, Inc., examines an advanced cyber-threat discovered by Darktrace on a customer\'s network. |
Technical | ★★★ | ||
| 2023-10-03 00:39:56 | Master Intelligence Virustotal: un guide complet de la feuille de triche VTI Mastering VirusTotal Intelligence: A Comprehensive Guide to VTI Cheat Sheet (lien direct) |
À quelle fréquence vous êtes-vous retrouvé perdu dans le dédale des fonctionnalités et des options que Virustotal Intelligence (VTI) offre?Si
How often have you found yourself lost in the maze of features and options that VirusTotal Intelligence (VTI) offers? If |
Technical | ★★★★ | ||
| 2023-10-02 20:16:45 | Rester en avance sur les ransomwares: un guide complet pour la sécurité des e-mails et la détection gérée Staying Ahead of Ransomware: A Comprehensive Guide to Email Security and Managed Detection (lien direct) |
Introduction aux attaques de ransomware de protection des ransomwares MD
Introduction to MDR Ransomware protection Ransomware attacks are on the rise, costing businesses millions and putting immense pressure on internal |
Ransomware Technical | ★★★ | ||
| 2023-10-02 19:27:46 | Déballage du pouvoir d'Osint dans les enquêtes sur la criminalité financière Unpacking the Power of OSINT in Financial Crime Investigations (lien direct) |
OSINT est-il le lien manquant dans vos enquêtes sur la criminalité financière?À une époque où les crimes financiers deviennent de plus en plus sophistiqués,
Is OSINT the Missing Link in Your Financial Crime Investigations? In an era where financial crimes are becoming increasingly sophisticated, |
Technical | ★★★★ | ||
| 2023-10-02 19:01:31 | 18 requêtes Shodan pour webcam osint (2023) 18 Shodan Queries for Webcam OSINT (2023) (lien direct) |
Vous êtes-vous déjà demandé comment découvrir le monde caché des webcams à l'aide de Shodan?Vous & # 8217; n'est pas seul.Avec la montée
Have you ever wondered how to uncover the hidden world of webcams using Shodan? You’re not alone. With the rise |
Technical | ★★★ |
To see everything:
Our RSS (filtrered)
