What's new arround internet
| Src | Date (GMT) | Titre | Description | Tags | Stories | Notes |
| 2024-04-18 13:40:42 | Empêcher les fuites de données généatives de l'IA avec Chrome Enterprise DLP Prevent Generative AI Data Leaks with Chrome Enterprise DLP (lien direct) |
Publié Kaleigh Rosenblat, Chrome Enterprise Senior Staff Engineer, Security Lead L'IA générative est devenue un outil puissant et populaire pour automatiser la création de contenu et des tâches simples.De la création de contenu personnalisée à la génération de code source, il peut augmenter à la fois notre productivité et notre potentiel créatif. Les entreprises souhaitent tirer parti de la puissance des LLM, comme les Gémeaux, mais beaucoup peuvent avoir des problèmes de sécurité et souhaiter plus de contrôle sur la façon dont les employés s'assurent de ces nouveaux outils.Par exemple, les entreprises peuvent vouloir s'assurer que diverses formes de données sensibles, telles que des informations personnellement identifiables (PII), des dossiers financiers et de la propriété intellectuelle interne, ne doit pas être partagé publiquement sur les plateformes d'IA génératrices.Les dirigeants de la sécurité sont confrontés au défi de trouver le bon équilibre - permettant aux employés de tirer parti de l'IA pour augmenter l'efficacité, tout en protégeant les données des entreprises. Dans cet article de blog, nous explorerons des politiques de reportage et d'application que les équipes de sécurité des entreprises peuvent mettre en œuvre dans Chrome Enterprise Premium Pour la prévention des pertes de données (DLP). 1. & nbsp; Voir les événements de connexion * pour comprendre l'utilisation des services d'IA génératifs au sein de l'organisation.Avec Chrome Enterprise \'s Reporting Connector , la sécurité et les équipes informatiques peuvent voir quand unL'utilisateur se connecte avec succès dans un domaine spécifique, y compris les sites Web d'IA génératifs.Les équipes d'opérations de sécurité peuvent tirer parti de cette télémétrie pour détecter les anomalies et les menaces en diffusant les données dans chronique ou autre tiers siems sans frais supplémentaires. 2. & nbsp; Activer le filtrage URL pour avertir les utilisateurs des politiques de données sensibles et les laisser décider s'ils souhaitent ou non accéder à l'URL, ou pour empêcher les utilisateurs de passer à certains groupes de sites. Par exemple, avec le filtrage d'URL de l'entreprise Chrome, les administrateurs informatiques peuvent créer des règlesqui avertissent les développeurs de ne pas soumettre le code source à des applications ou outils AI génératifs spécifiques, ou de les bloquer. 3. & nbsp; avertir, bloquer ou surveiller les actions de données sensibles dans les sites Web d'IA génératifs avec des règles dynamiques basées sur le contenu pour des actions telles que la pâte, les téléchargements / téléchargements de fichiers et l'impression. & nbsp; Chrome Enterprise DLP DLPRègles Donnez aux administrateurs des administrateurs des activités granulaires sur les activités du navigateur, telles que la saisie des informations financières dans les sites Web de Gen AI.Les administrateurs peuvent personnaliser les règles du DLP pour restre | Tool Legislation | ★★★ | ||
| 2024-04-18 09:53:59 | The Windows Registry Adventure # 1: Résultats d'introduction et de recherche The Windows Registry Adventure #1: Introduction and research results (lien direct) |
Posted by Mateusz Jurczyk, Google Project Zero In the 20-month period between May 2022 and December 2023, I thoroughly audited the Windows Registry in search of local privilege escalation bugs. It all started unexpectedly: I was in the process of developing a coverage-based Windows kernel fuzzer based on the Bochs x86 emulator (one of my favorite tools for security research: see Bochspwn, Bochspwn Reloaded, and my earlier font fuzzing infrastructure), and needed some binary formats to test it on. My first pick were PE files: they are very popular in the Windows environment, which makes it easy to create an initial corpus of input samples, and a basic fuzzing harness is equally easy to develop with just a single GetFileVersionInfoSizeW API call. The test was successful: even though I had previously fuzzed PE files in 2019, the new element of code coverage guidance allowed me to discover a completely new bug: issue #2281. For my next target, I chose the Windows registry. That\'s because arbitrary registry hives can be loaded from disk without any special privileges via the RegLoadAppKey API (since Windows Vista). The hives use a binary format and are fully parsed in the kernel, making them a noteworthy local attack surface. Furthermore, I was also somewhat familiar with basic harnessing of the registry, having fuzzed it in 2016 together with James Forshaw. Once again, the code coverage support proved useful, leading to the discovery of issue #2299. But when I started to perform a root cause analysis of the bug, I realized that: The hive binary format is not very well suited for trivial bitflipping-style fuzzing, because it is structurally simple, and random mutations are much more likely to render (parts of) the hive unusable than to trigger any interesting memory safety violations.On the other hand, the registry has many properties that make it an attractive attack | Tool Vulnerability Threat Studies | ★★★★ | ||
| 2024-04-18 09:46:51 | The Windows Registry Adventure # 2: Une brève histoire de la fonctionnalité The Windows Registry Adventure #2: A brief history of the feature (lien direct) |
Posted by Mateusz Jurczyk, Google Project Zero Before diving into the low-level security aspects of the registry, it is important to understand its role in the operating system and a bit of history behind it. In essence, the registry is a hierarchical database made of named "keys" and "values", used by Windows and applications to store a variety of settings and configuration data. It is represented by a tree structure, in which keys may have one or more sub-keys, and every subkey is associated with exactly one parent key. Furthermore, every key may also contain one or more values, which have a type (integer, string, binary blob etc.) and are used to store actual data in the registry. Every key can be uniquely identified by its name and the names of all of its ascendants separated by the special backslash character (\'\\'), and starting with the name of one of the top-level keys (HKEY_LOCAL_MACHINE, HKEY_USERS, etc.). For example, a full registry path may look like this: HKEY_CURRENT_USER\Software\Microsoft\Windows. At a high level, this closely resembles the structure of a file system, where the top-level key is equivalent to the root of a mounted disk partition (e.g. C:\), keys are equivalent to directories, and values are equivalent to files. One important distinction, however, is that keys are the only type of securable objects in the registry, and values play a much lesser role in the database than files do in the file system. Furthermore, specific subtrees of the registry are stored on disk in binary files called registry hives, and the hive mount points don\'t necessarily correspond one-to-one to the top-level keys (e.g. the C:\Windows\system32\config\SOFTWARE hive is mounted under HKEY_LOCAL_MACHINE\Software, a one-level nested key). Fundamentally, there are only a few basic operations that can be performed in the registry. These operations are summarized in the table below: Hives Load hive Unload hive Flush hive to disk Keys Open key Create key Delete key | Tool Prediction Technical | ★★★★ | ||
| 2024-04-18 06:00:36 | FAQ à partir de l'état du rapport Phish 2024, partie 2: comportements et attitudes des utilisateurs envers la sécurité FAQs from the 2024 State of the Phish Report, Part 2: User Behaviors and Attitudes Toward Security (lien direct) |
Welcome to the second installment of our two-part blog series where we answer the most frequently asked questions about the 2024 State of the Phish Report. In our previous article, we answered questions related to the threat landscape findings. Here, we answer questions related to user behaviors and attitudes, as well as how to grow your security awareness program. One of the most interesting findings that came out of the 2024 State of the Phish report was the fact that 71% of users admitted to engaging in a risky action and 96% of those users understood the risk. This suggests that people are not acting out of ignorance. Despite knowing that their actions could compromise themselves or their organization, people chose to proceed anyway. This information is crucial for the growth of any security awareness program. It enables organizations to tailor their efforts. By observing and analyzing how users interact with security policies, organizations can identify knowledge gaps and areas of resistance. When you engage users in this manner, you not only educate them but also transform them into active participants in protecting your organization. 96% of users who took a risky action knew that it was risky. (Source: 2024 State of the Phish from Proofpoint.) Our findings inspired hundreds of questions from audiences across the world. What follows are some of the questions that repeatedly came up. Frequently asked questions What are some ways to get users to care about security and get engaged? Two-way communication is key. Take a moment to explain to your employees why you\'re running a behavior change program, what the expectations are and what projected outcomes you foresee. Make it personal. Let people know that cybersecurity isn\'t just a work skill but a portable skill they can take home to help themselves and their families be safer in life. Keep your employees up to speed on what\'s happening in the current threat landscape. For example: What types of threats does your business see? Which departments are under attack? How does the security team handle these incidents? What can people do to defend against emerging threats that target them? Research for the 2024 State of the Phish report found that 87% of end users are more motivated to prioritize security when they see increased engagement from leadership or the security team. In short: You need to open up the lines of communication, listen to your employees and incorporate their feedback, and establish a security champion network to help facilitate communication more effectively. Any ideas on why the click rate for phishing simulations went up for many industries this year? There may be a few possible reasons. For starters, there has been an increase in the number of phishing tests sent. Our customers sent out a total of 183 million simulated phishing tests over a 12-month period, up from 135 million in the previous 12-month period. This 36% increase suggests that our customers may have either tested their users more frequently or tested more users in general. Also, some users might be new to these tests, resulting in a higher click rate. Regardless, if you are conducting a phishing campaign throughout the year, the click rates of phishing tests are expected to go up and down because you want to challenge your employees with new attack tactics they have not seen. Otherwise, the perception would be, “Oh, this is the face of a phish,” if you keep phishing your users with the same test. At Proofpoint, we use machine learning-driven leveled phishing to provide a more reliable way to accurately assess user vulnerability. This unique feature allows security teams to examine the predictability of a phishing template and obtain more consistent outcomes while improving users\' resilience against human-activated threats. People need to understand how attackers exploit human vulnerability. Phishing tests should reflect reality and be informed by real-world threats. They are designed to help people spot and re | Tool Vulnerability Threat | ★★ | ||
| 2024-04-18 02:00:00 | L'outil open source recherche des signaux dans les journaux cloud Noisy AWS Open Source Tool Looks for Signals in Noisy AWS Cloud Logs (lien direct) |
Permiso Security a annoncé le cartographe de console Cloud pendant Black Hat Asia pour aider les défenseurs à regarder à l'intérieur des journaux des événements de services Web Amazon pour les signes de cyberattaques.
Permiso Security announced Cloud Console Cartographer during Black Hat Asia to help defenders look inside Amazon Web Services events logs for signs of cyberattacks. |
Tool Cloud | ★★ | ||
| 2024-04-17 23:47:49 | Couvoir la fraude vocale à l'ère de l'IA Countering Voice Fraud in the Age of AI (lien direct) |
L'usurpation d'identification de l'appelant et la voix de la voix aiment sont des escroqueries de téléphone.Heureusement, nous avons des outils pour aider les organisations et les gens à protéger contre la combinaison sournoise.
Caller ID spoofing and AI voice deepfakes are supercharging phone scams. Fortunately, we have tools to help organizations and people protect against the devious combination. |
Tool | ★★ | ||
| 2024-04-17 19:17:10 | \\ 'brut \\' outils de ransomware proliférant sur le Web sombre pour pas cher, les chercheurs trouvent \\'Crude\\' ransomware tools proliferating on the dark web for cheap, researchers find (lien direct) |
L'usurpation d'identification de l'appelant et la voix de la voix aiment sont des escroqueries de téléphone.Heureusement, nous avons des outils pour aider les organisations et les gens à protéger contre la combinaison sournoise.
Caller ID spoofing and AI voice deepfakes are supercharging phone scams. Fortunately, we have tools to help organizations and people protect against the devious combination. |
Ransomware Tool | ★★ | ||
| 2024-04-17 18:00:31 | Réduire le désabonnement d'incitation avec une composition de modèle explosive Reducing Prompting Churn with Exploding Template Composition (lien direct) |
Engineering Insights is an ongoing blog series that gives a behind-the-scenes look into the technical challenges, lessons and advances that help our customers protect people and defend data every day. Each post is a firsthand account by one of our engineers about the process that led up to a Proofpoint innovation. In the nascent world of large language models (LLMs), prompt engineering has emerged as a critical discipline. However, as LLM applications expand, it is becoming a more complex challenge to manage and maintain a library of related prompts. At Proofpoint, we developed Exploding Prompts to manage the complexity through exploding template composition. We first created the prompts to generate soft labels for our data across a multitude of models and labeling concerns. But Exploding Prompts has also enabled use cases for LLMs that were previously locked away because managing the prompt lifecycle is so complex. Recently, we\'ve seen exciting progress in the field of automated prompt generation and black-box prompt optimization through DSPy. Black-box optimization requires hand-labeled data to generate prompts automatically-a luxury that\'s not always an option. You can use Exploding Prompts to generate labels for unlabeled data, as well as for any prompt-tuning application without a clear (or tractable) objective for optimization. In the future, Exploding Prompts could be used with DSPy to achieve a human-in-the-loop feedback cycle. We are also thrilled to announce that Exploding Prompts is now an open-source release. We encourage you to explore the code and consider how you might help make it even better. The challenge: managing complexity in prompt engineering Prompt engineering is not just about crafting queries that guide intelligent systems to generate the desired outputs; it\'s about doing it at scale. As developers push the boundaries of what is possible with LLMs, the need to manage a vast array of prompts efficiently becomes more pressing. Traditional methods often need manual adjustments and updates across numerous templates, which is a process that\'s both time-consuming and error-prone. To understand this problem, just consider the following scenario. You need to label a large quantity of data. You have multiple labels that can apply to each piece of data. And each label requires its own prompt template. You timebox your work and find a prompt template that achieves desirable results for your first label. Happily, most of the template is reusable. So, for the next label, you copy-paste the template and change the portion of the prompt that is specific to the label itself. You continue doing this until you figure out the section of the template that has persisted through each version of your labels can be improved. Now you now face the task of iterating through potentially dozens of templates to make a minor update to each of the files. Once you finish, your artificial intelligence (AI) provider releases a new model that outperforms your current model. But there\'s a catch. The new model requires another small update to each of your templates. To your chagrin, the task of managing the lifecycle of your templates soon takes up most of your time. The solution: exploding prompts from automated dependency graphs Prompt templating is a popular way to manage complexity. Exploding Prompts builds on prompt templating by introducing an “explode” operation. This allows a few single-purpose templates to explode into a multitude of prompts. This is accomplished by building dependency graphs automatically from the directory structure and the content of prompt template files. At its core, Exploding Prompts embodies the “write it once” philosophy. It ensures that every change made in a template correlates with a single update in one file. This enhances efficiency and consistency, as updates automatically propagate across all relevant generated prompts. This separation ensures that updates can be made with speed and efficiency so you can focus on innovation rather th | Malware Tool Threat Studies Cloud Technical | ★★★ | ||
| 2024-04-17 16:37:00 | Genai: un nouveau mal de tête pour les équipes de sécurité SaaS GenAI: A New Headache for SaaS Security Teams (lien direct) |
L'introduction du Chatgpt d'Open Ai \\ a été un moment déterminant pour l'industrie du logiciel, touchant une course Genai avec sa version de novembre 2022.Les fournisseurs SaaS se précipitent désormais pour mettre à niveau les outils avec des capacités de productivité améliorées qui sont motivées par une IA générative.
Parmi une large gamme d'utilisations, les outils Genai permettent aux développeurs de créer plus facilement des logiciels, d'aider les équipes de vente dans la rédaction de courrier électronique banal,
The introduction of Open AI\'s ChatGPT was a defining moment for the software industry, touching off a GenAI race with its November 2022 release. SaaS vendors are now rushing to upgrade tools with enhanced productivity capabilities that are driven by generative AI. Among a wide range of uses, GenAI tools make it easier for developers to build software, assist sales teams in mundane email writing, |
Tool Cloud | ChatGPT | ★★ | |
| 2024-04-17 14:36:00 | Gouvernement américain et partenaire OpenSSF sur un nouvel outil de gestion SBOM US Government and OpenSSF Partner on New SBOM Management Tool (lien direct) |
OpenSSF, en collaboration avec le gouvernement américain, a développé Protobom, un outil open source conçu pour simplifier la gestion SBOM pour les organisations
OpenSSF, in collaboration with the US Government, has developed Protobom, a open source tool designed to simplify SBOM management for organizations |
Tool | ★★ | ||
| 2024-04-17 13:00:35 | IA pour la découverte des risques: 10 façons de le faire fonctionner pour vous AI for Risk Discovery: 10 Ways to Make it Work For You (lien direct) |
> Au-delà du buzz des chatbots ou des recommandations personnalisées, la profonde capacité de l'IA à anticiper et à neutraliser les risques prend de l'ampleur parmi les organisations.Alors que les vastes volumes de surtension de données et de réglementations resserrent leur emprise, les outils d'évaluation des risques traditionnels vacillent sous le poids.Dans une telle toile de fond, tirer parti des prouesses de la gestion des risques de l'IA de l'IA garantit la conformité à l'évolution des réglementations et une position proactive contre les menaces imprévues.Naviguer dans les complexités de la gestion des risques avec l'IA peut sembler intimidant, mais pour ceux qui désirent rester en tête dans la course numérique, l'intégration de l'IA dans leur stratégie de risque n'est pas une question de & # 8216; si & # 8217;mais & # 8216; quand & # 8217;.Voici [& # 8230;]
>Beyond the buzz of chatbots or personalized recommendations, AI’s profound ability to anticipate and neutralize risks is gaining momentum among organizations. As the vast volumes of data surge and regulations tighten their grip, traditional risk assessment tools falter under the weight. Against such a backdrop, leveraging AI’s risk management prowess ensures compliance with evolving regulations and a proactive stance against unforeseen threats. Navigating the complexities of risk management with AI might seem daunting, but for those keen to stay ahead in the digital race, integrating AI into their risk strategy is not a matter of ‘if’ but ‘when’. Here is […] |
Tool | ★★ | ||
| 2024-04-17 10:00:00 | Unearthing APT44: Russia\'s Notorious Cyber Sabotage Unit Sandworm (lien direct) | Written by: Gabby Roncone, Dan Black, John Wolfram, Tyler McLellan, Nick Simonian, Ryan Hall, Anton Prokopenkov, Luke Jenkins, Dan Perez, Lexie Aytes, Alden Wahlstrom
With Russia\'s full-scale invasion in its third year, Sandworm (aka FROZENBARENTS) remains a formidable threat to Ukraine. The group\'s operations in support of Moscow\'s war aims have proven tactically and operationally adaptable, and as of today, appear to be better integrated with the activities of Russia\'s conventional forces than in any other previous phase of the conflict. To date, no other Russian government-backed cyber group has played a more central role in shaping and supporting Russia\'s military campaign. Yet the threat posed by Sandworm is far from limited to Ukraine. Mandiant continues to see operations from the group that are global in scope in key political, military, and economic hotspots for Russia. Additionally, with a record number of people participating in national elections in 2024, Sandworm\'s history of attempting to interfere in democratic processes further elevates the severity of the threat the group may pose in the near-term. Given the active and diffuse nature of the threat posed by Sandworm globally, Mandiant has decided to graduate the group into a named Advanced Persistent Threat: APT44. As part of this process, we are releasing a report, “APT44: Unearthing Sandworm”, that provides additional insights into the group\'s new operations, retrospective insights, and context on how the group is adjusting to support Moscow\'s war aims. Key Findings Sponsored by Russian military intelligence, APT44 is a dynamic and operationally mature threat actor that is actively engaged in the full spectrum of espionage, attack, and influence operations. While most state-backed threat groups tend to specialize in a specific mission such as collecting intelligence, sabotaging networks, or conducting information operations, APT44 stands apart in how it has honed each of these capabilities and sought to integrate them into a unified playbook over time. Each of these respective components, and APT44\'s efforts to blend them for combined effect, are foundational to Russia\'s guiding “information confrontation” concept for cyber warfare. 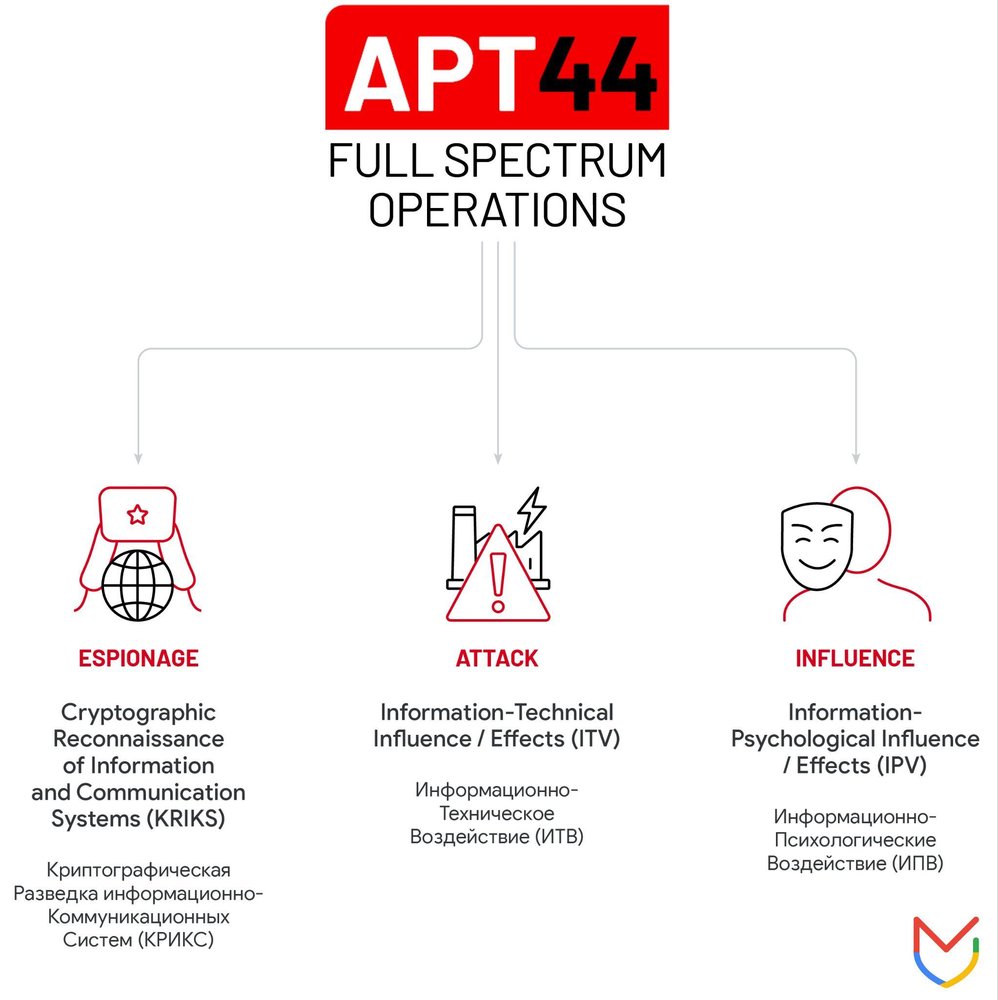 Figure 1: APT44\'s spectrum of operations
APT44 has aggressively pursued a multi-
Figure 1: APT44\'s spectrum of operations
APT44 has aggressively pursued a multi- |
Malware Tool Threat Mobile Cloud | NotPetya | ★★ | |
| 2024-04-17 10:00:00 | Introduction à l'analyse de la composition logicielle et comment sélectionner un outil SCA Introduction to Software Composition Analysis and How to Select an SCA Tool (lien direct) |
The content of this post is solely the responsibility of the author. AT&T does not adopt or endorse any of the views, positions, or information provided by the author in this article. Software code is constantly growing and becoming more complex, and there is a worrying trend: an increasing number of open-source components are vulnerable to attacks. A notable instance was the Apache Log4j library vulnerability, which posed serious security risks. And this is not an isolated incident. Using open-source software necessitates thorough Software Composition Analysis (SCA) to identify these security threats. Organizations must integrate SCA tools into their development workflows while also being mindful of their limitations. Why SCA Is Important Open-source components have become crucial to software development across various industries. They are fundamental to the construction of modern applications, with estimates suggesting that up to 96% of the total code bases contain open-source elements. Assembling applications from diverse open-source blocks presents a challenge, necessitating robust protection strategies to manage and mitigate risks effectively. Software Composition Analysis is the process of identifying and verifying the security of components within software, especially open-source ones. It enables development teams to efficiently track, analyze, and manage any open-source element integrated into their projects. SCA tools identify all related components, including libraries and their direct and indirect dependencies. They also detect software licenses, outdated dependencies, vulnerabilities, and potential exploits. Through scanning, SCA creates a comprehensive inventory of a project\'s software assets, offering a full view of the software composition for better security and compliance management. Although SCA tools have been available for quite some time, the recent open-source usage surge has cemented their importance in application security. Modern software development methodologies, such as DevSecOps, emphasize the need for SCA solutions for developers. The role of security officers is to guide and assist developers in maintaining security across the Software Development Life Cycle (SDLC), ensuring that SCA becomes an integral part of creating secure software. Objectives and Tasks of SCA Tools Software Composition Analysis broadly refers to security methodologies and tools designed to scan applications, typically during development, to identify vulnerabilities and software license issues. For effective management of open-source components and associated risks, SCA solutions help navigate several tasks: 1) Increasing Transparency A developer might incorporate various open-source packages into their code, which in turn may depend on additional open-source packages unknown to the developer. These indirect dependencies can extend several levels deep, complicating the understanding of exactly which open-source code the application uses. Reports indicate that 86% of vulnerabilities in node.js projects stem from transitive (indirect) dependencies, w | Tool Vulnerability Threat Patching Prediction Cloud Commercial | ★★ | ||
| 2024-04-16 18:56:00 | Les outils AWS, Google et Azure CLI pourraient fuir les informations d'identification dans les journaux de construction AWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs (lien direct) |
La nouvelle recherche sur la cybersécurité a révélé que les outils d'interface de ligne de commande (CLI) d'Amazon Web Services (AWS) et de Google Cloud peuvent exposer des informations d'identification sensibles dans les journaux de construction, posant des risques importants aux organisations.
La vulnérabilité a été nommée Coded & nbsp; Leakycli & nbsp; par la société de sécurité cloud Orca.
"Certaines commandes sur Azure CLI, AWS CLI et Google Cloud CLI peuvent exposer des informations sensibles
New cybersecurity research has found that command-line interface (CLI) tools from Amazon Web Services (AWS) and Google Cloud can expose sensitive credentials in build logs, posing significant risks to organizations. The vulnerability has been codenamed LeakyCLI by cloud security firm Orca. "Some commands on Azure CLI, AWS CLI, and Google Cloud CLI can expose sensitive information in |
Tool Vulnerability Cloud | ★★★★ | ||
| 2024-04-16 18:42:47 | La nouvelle vulnérabilité «Leakycli» fuit AWS et Google Cloud Indementiels New Vulnerability “LeakyCLI” Leaks AWS and Google Cloud Credentials (lien direct) |
par waqas Une vulnérabilité critique nommée Leakycli expose les informations d'identification de cloud sensibles à partir d'outils populaires utilisés avec AWS et Google Cloud.Cela présente un risque majeur pour les développeurs, montrant la nécessité de pratiques de sécurité solides.Apprenez à atténuer Leakycli et fortifier votre infrastructure cloud. Ceci est un article de HackRead.com Lire la publication originale: | Tool Vulnerability Cloud | ★★★ | ||
| 2024-04-16 06:00:54 | De l'ingénierie sociale aux abus DMARC: Ta427 \\'s Art of Information Gathering From Social Engineering to DMARC Abuse: TA427\\'s Art of Information Gathering (lien direct) |
Key takeaways TA427 regularly engages in benign conversation starter campaigns to establish contact with targets for long-term exchanges of information on topics of strategic importance to the North Korean regime. In addition to using specially crafted lure content, TA427 heavily leverages think tank and non-governmental organization-related personas to legitimize its emails and increase the chances that targets will engage with the threat actor. To craftily pose as its chosen personas, TA427 uses a few tactics including DMARC abuse in concert with free email addresses, typosquatting, and private email account spoofing. TA427 has also incorporated web beacons for initial reconnaissance of its targets, establishing basic information like that the email account is active. Overview Proofpoint researchers track numerous state-sponsored and state-aligned threat actors. TA427 (also known as Emerald Sleet, APT43, THALLIUM or Kimsuky), a Democratic People\'s Republic of Korea (DPRK or North Korea) aligned group working in support of the Reconnaissance General Bureau, is particularly prolific in email phishing campaigns targeting experts for insight into US and the Republic of Korea (ROK or South Korea) foreign policy. Since 2023, TA427 has directly solicited foreign policy experts for their opinions on nuclear disarmament, US-ROK policies, and sanction topics via benign conversation starting emails. In recent months, Proofpoint researchers have observed (Figure 1) a steady, and at times increasing, stream of this activity. While our researchers have consistently observed TA427 rely on social engineering tactics and regularly rotating its email infrastructure, in December 2023 the threat actor began to abuse lax Domain-based Message Authentication, Reporting and Conformance (DMARC) policies to spoof various personas and, in February 2024, began incorporating web beacons for target profiling. It is this initial engagement, and the tactics successfully leveraged by TA427, which this blog is focused on. Figure 1. Volume of TA427 phishing campaigns observed between January 2023 and March 2024. Social engineering TA427 is a savvy social engineering expert whose campaigns are likely in support of North Korea\'s strategic intelligence collection efforts on US and ROK foreign policy initiatives. Based on the targets identified and the information sought, it is believed that TA427\'s goal is to augment North Korean intelligence and inform its foreign policy negotiation tactics (example Figure 2). TA427 is known to engage its targets for extended periods of time through a series of benign conversations to build a rapport with targets that can occur over weeks to months. They do so by constantly rotating which aliases are used to engage with the targets on similar subject matter. Figure 2. Example of TA427 campaign focused on US policy during an election year. Using timely, relevant lure content (as seen in Figure 3) customized for each victim, and often spoofing individuals in the DPRK research space with whom the victim is familiar to encourage engagement, targets are often requested to share their thoughts on these topics via email or a formal research paper or article. Malware or credential harvesting are never directly sent to the targets without an exchange of multiple messages, and based on Proofpoint visibility, rarely utilized by the threat actor. It is possible that TA427 can fulfill its intelligence requirements by directly asking targets for their opinions or analysis rather than from an infection. Additionally, insight gained from the correspondence is likely used to improve targeting of the victim organization and establish rapport for later questions and engagement. Figure 3. Timeline of real-world events based on international press reporting, side-by-side with Proofpoint observed subject lures. Lure content often includes invitations to attend events about North Korean policies regarding international affairs, questions regarding topics such as how deterr | Malware Tool Threat Conference | APT 37 APT 43 | ★★ | |
| 2024-04-16 02:59:03 | SCM et NERC: ce que vous devez savoir SCM and NERC: What You Need to Know (lien direct) |
Les configurations de sécurité sont un facteur souvent ignoré mais essentiel dans la posture de sécurité de toute organisation: tout outil, programme ou solution peut être vulnérable aux cyberattaques ou à d'autres incidents de sécurité si les paramètres ne sont pas configurés correctement.Rester au-dessus de toutes ces configurations de sécurité peut être une responsabilité intimidante pour la sécurité ou les équipes informatiques sur lesquelles se concentrer, c'est là que la gestion de la configuration de la sécurité (SCM) entre en jeu. Bien que SCM puisse être un outil précieux pour les organisations de tous les secteurs, il estParticulièrement utile pour les organisations critiques nécessaires pour se conformer à certains ...
Security configurations are an often ignored but essential factor in any organization\'s security posture: any tool, program, or solution can be vulnerable to cyberattacks or other security incidents if the settings are not configured correctly. Staying on top of all of these security configurations can be a daunting responsibility for security or IT teams to focus on, which is where security configuration management (SCM) comes in. While SCM can be a valuable tool for organizations across all sectors, it is particularly helpful for critical organizations required to comply with certain... |
Tool | ★★ | ||
| 2024-04-16 02:58:57 | Casquer un filet de cybersécurité pour sécuriser l'IA génératrice dans la fabrication Casting a Cybersecurity Net to Secure Generative AI in Manufacturing (lien direct) |
L'IA générative a explosé en popularité dans de nombreuses industries.Bien que cette technologie présente de nombreux avantages, elle soulève également des problèmes de cybersécurité uniques.La sécurisation de l'IA doit être une priorité absolue pour les organisations alors qu'elles se précipitent pour mettre en œuvre ces outils.L'utilisation d'une IA générative dans la fabrication pose des défis particuliers.Plus d'un tiers des fabricants prévoient d'investir dans cette technologie, ce qui en fait le quatrième changement de commerce stratégique le plus courant de l'industrie.Au fur et à mesure que cette tendance se poursuit, les fabricants - souvent les cibles de cybercriminalité privilégiées - doivent s'assurer que l'IA générative est suffisamment sécurisée avant que ses risques l'emportent ...
Generative AI has exploded in popularity across many industries. While this technology has many benefits, it also raises some unique cybersecurity concerns. Securing AI must be a top priority for organizations as they rush to implement these tools. The use of generative AI in manufacturing poses particular challenges. Over one-third of manufacturers plan to invest in this technology, making it the industry\'s fourth most common strategic business change. As that trend continues, manufacturers - often prime cybercrime targets - must ensure generative AI is secure enough before its risks outweigh... |
Tool Prediction | ★★ | ||
| 2024-04-15 20:31:45 | Zero-Day Exploitation of Unauthenticated Remote Code Execution Vulnerability in GlobalProtect (CVE-2024-3400) (lien direct) | ## Instantané
Le 10 avril 2024, la volexité a découvert l'exploitation zéro-jour d'une vulnérabilité dans la fonctionnalité GlobalProtect de Palo Alto Networks Pan-OS à l'un de ses clients de surveillance de la sécurité des réseaux (NSM).La vulnérabilité a été confirmée comme un problème d'injection de commande de système d'exploitation et attribué CVE-2024-3400.Le problème est une vulnérabilité d'exécution de code distante non authentifiée avec un score de base CVSS de 10,0.L'acteur de menace, que volexité suit sous l'alias UTA0218, a pu exploiter à distance l'appareil de pare-feu, créer un shell inversé et télécharger d'autres outils sur l'appareil.L'attaquant s'est concentré sur l'exportation des données de configuration des appareils, puis en le tirant en tirant comme point d'entrée pour se déplacer latéralement au sein des organisations victimes.Au cours de son enquête, Volexity a observé que l'UTA0218 avait tenté d'installer une porte dérobée Python personnalisée, que volexité appelle Upstyle, sur le pare-feu.La porte dérobée Upstyle permet à l'attaquant d'exécuter des commandes supplémentaires sur l'appareil via des demandes de réseau spécialement conçues.UTA0218 a été observé en exploitant des appareils de pare-feu pour déployer avec succès des charges utiles malveillantes.Après avoir réussi à exploiter les appareils, UTA0218 a téléchargé des outils supplémentaires à partir de serveurs distants qu'ils contrôlaient afin de faciliter l'accès aux réseaux internes des victimes.Ils se sont rapidement déplacés latéralement à travers les réseaux victimes de victimes, extrait les informations d'identification sensibles et autres fichiers qui permettraient d'accéder pendant et potentiellement après l'intrusion.Le métier et la vitesse employés par l'attaquant suggèrent un acteur de menace hautement capable avec un livre de jeu clair sur quoi accéder pour poursuivre leurs objectifs.Il est probable que l'exploitation du dispositif de pare-feu, suivie d'une activité de planche pratique, a été limitée et ciblée.Cependant, les preuves d'une activité de reconnaissance potentielle impliquant une exploitation plus répandue visant à identifier les systèmes vulnérables semblent avoir eu lieu au moment de la rédaction.
## Les références
[https://security.paloaltonetworks.com/CVE-2024-3400#new_tab.
[https://www.volexity.com/blog/2024/04/12/zero-ay-exploitation-of-unauthenticated-remote-code-execution-vulnerabilité-in-GlobalProtect-CVE-2024-3400 /] (https://www.volexity.com/blog/2024/04/12/zero-kay-exploitation-of-unauthenticated-remote-code-execution-vulnerabilité-in-globalprotect-CVE-2024-3400 /)
## Snapshot On April 10, 2024, Volexity discovered zero-day exploitation of a vulnerability in the GlobalProtect feature of Palo Alto Networks PAN-OS at one of its network security monitoring (NSM) customers. The vulnerability was confirmed as an OS command injection issue and assigned CVE-2024-3400. The issue is an unauthenticated remote code execution vulnerability with a CVSS base score of 10.0. The threat actor, which Volexity tracks under the alias UTA0218, was able to remotely exploit the firewall device, create a reverse shell, and download further tools onto the device. The attacker focused on exporting configuration data from the devices, and then leveraging it as an entry point to move laterally within the victim organizations. During its investigation, Volexity observed that UTA0218 attempted to install a custom Python backdoor, which Volexity calls UPSTYLE, on the firewall. The UPSTYLE backdoor allows the attacker to execute additional commands on the device via specially crafted network requests. UTA0218 was observed exploiting firewall devices to successfully deploy malicious payloads. After successfully exploiting devices, UTA0218 downloaded additional tooling from remote servers they controlled in order to facilitate access to victims\' internal networks. They quickly moved laterally thr |
Tool Vulnerability Threat | ★★ | ||
| 2024-04-15 19:49:12 | Planification collaborative: améliorer la coordination de l'équipe avec des outils open source Collaborative Scheduling: Enhancing Team Coordination With Open-Source Tools (lien direct) |
> Par uzair amir
Dans l'environnement de travail en évolution rapide d'aujourd'hui, la planification collaborative se distingue comme un pilier fondamental pour efficace & # 8230;
Ceci est un article de HackRead.com Lire la publication originale: Planification collaborative: améliorer la coordination de l'équipe avec des outils open-source
>By Uzair Amir In the rapidly evolving work environment of today, collaborative scheduling stands out as a foundational pillar for effective… This is a post from HackRead.com Read the original post: Collaborative Scheduling: Enhancing Team Coordination With Open-Source Tools |
Tool | ★★ | ||
| 2024-04-15 16:31:28 | Les nouvelles attaques de Steganoamor utilisent la stéganographie pour cibler 320 organisations dans le monde entier New SteganoAmor attacks use steganography to target 320 orgs globally (lien direct) |
Une nouvelle campagne menée par le groupe de piratage TA558 cache du code malveillant à l'intérieur d'images en utilisant la stéganographie pour fournir divers outils de logiciels malveillants sur des systèmes ciblés.[...]
A new campaign conducted by the TA558 hacking group is concealing malicious code inside images using steganography to deliver various malware tools onto targeted systems. [...] |
Malware Tool | ★★ | ||
| 2024-04-15 15:15:00 | Faits saillants hebdomadaires, 15 avril 2024 Weekly OSINT Highlights, 15 April 2024 (lien direct) |
## Snapshot Last week\'s OSINT reporting reveals a landscape of diverse cyber threats characterized by sophisticated attack tactics and adaptable threat actors. One key trend was the increasing use of artificial intelligence (AI) by cybercriminals, including AI-powered malvertising on social media platforms and suspected LLM-generated content in a malware campaign targeting German organizations. Additionally, several OSINT articles reported on the trend of exploiting popular platforms like YouTube and GitHub to distribute malware. Threat actors demonstrate a keen understanding of user behavior, leveraging enticing content and fake webpages to lure victims into downloading malicious payloads, highlighting the importance of proactive defense strategies to mitigate evolving threats effectively. ## Description 1. **[German Organizations Targeted with Rhadamanthys Malware](https://security.microsoft.com/intel-explorer/articles/119bde85):** Proofpoint identifies TA547 launching an email campaign targeting German organizations with Rhadamanthys malware, representing a shift in techniques for the threat actor. The campaign involves impersonating a German retail company in emails containing password-protected ZIP files containing LNK files triggering PowerShell scripts to load Rhadamanthys into memory, bypassing disk writing. The incorporation of suspected LLM-generated content into the attack chain provides insight into how threat actors are leveraging LLM-generated content in malware campaigns. 2. **[Russian-Language Cybercrime Operation Leveraging Fake Web3 Gaming Projects](https://security.microsoft.com/intel-explorer/articles/0cdc08b5):** The Insikt Group uncovers a large-scale Russian-language cybercrime operation distributing infostealer malware through fake Web3 gaming projects targeting both macOS and Windows users. Threat actors entice users with the potential for cryptocurrency earnings, distributing malware like Atomic macOS Stealer (AMOS), Stealc, Rhadamanthys, or RisePro upon visiting imitation Web3 gaming projects\' webpages. 3. **[AI-Powered Malvertising Campaigns on Social Media](https://security.microsoft.com/intel-explorer/articles/1e1b0868):** Bitdefender discusses the use of artificial intelligence (AI) by cybercriminals in malvertising campaigns on social media platforms, impersonating popular AI software to distribute stealers like Rilide, Vidar, IceRAT, and Nova Stealer. These campaigns target European users through fake AI software webpages on Facebook, organized by taking over existing accounts and boosting page popularity through engaging content. 4. **[Exploitation of YouTube Channels for Infostealer Distribution](https://security.microsoft.com/intel-explorer/articles/e9f5e219):** AhnLab identifies a trend where threat actors exploit YouTube channels to distribute Infostealers like Vidar and LummaC2, disguising them as cracked versions of legitimate software. Attackers hijack popular channels with hundreds of thousands of subscribers, distributing malicious links through video descriptions and comments, highlighting concerns about the potential reach and impact of distributed malware. 5. **[VenomRAT Distribution via Phishing Email with Malicious SVG Files](https://security.microsoft.com/intel-explorer/articles/98d69c76):** FortiGuard Labs reveals a threat actor distributing VenomRAT and other plugins through phishing emails containing malicious Scalable Vector Graphics (SVG) files. The email attachment downloads a ZIP file containing an obfuscated Batch file, subsequently loading VenomRAT using ScrubCrypt to maintain a connection with a command and control (C2) server and install plugins on victims\' environments. 6. **[Malware Distribution through GitHub Repositories Manipulation](https://security.microsoft.com/intel-explorer/articles/4d0ffb2c):** Checkmarx reports a cybercriminal attack campaign manipulating GitHub\'s search functionality to distribute malware through repositories. Attackers create repositories with popular names and topics, hiding malicious code withi | Ransomware Spam Malware Tool Threat Prediction | ★★ | ||
| 2024-04-15 10:13:05 | Les IA comme ChatGPT aident-elles réellement les étudiants en informatique ? (lien direct) | Deux études explorent l'impact des générateurs de code IA sur l'apprentissage des étudiants novices en programmation, révélant à la fois les avantages et les pièges de ces outils puissants qui transforment l'enseignement de l'informatique. | Tool | ChatGPT | ★★★ | |
| 2024-04-15 10:00:00 | Le cycle de vie d'un fichier numérique The Lifecycle of a Digital File (lien direct) |
The content of this post is solely the responsibility of the author. AT&T does not adopt or endorse any of the views, positions, or information provided by the author in this article. In the digital world, every document, image, video, or program we create leaves a trail. Understanding the lifecycle of a file, from its creation to deletion, is crucial for various purposes, including data security, data recovery, and digital forensics. This article delves into the journey a file takes within a storage device, explaining its creation, storage, access, and potential deletion phases. File Lifecycle 1. Creation: Birth of a Digital Entity A file\'s life begins with its creation. This can happen in various ways: Software Applications: When you create a new document in a word processor, edit an image in a photo editing software, or record a video, the application allocates space on the storage device and writes the data associated with the file. Downloads: Downloading a file from the internet involves copying data from the remote server to your storage device. Data Transfers: Copying a file from one location to another on the same device or transferring it to a different device creates a new instance of the file. System Processes: Operating systems and applications sometimes create temporary files during various processes. These files may be automatically deleted upon task completion. During creation, the operating system assigns a unique identifier (often a filename) to the file and stores it in a directory (folder) along with additional information about the file, known as metadata. This metadata typically includes: File size: The total amount of storage space occupied by the file. Creation date and time: The timestamp of when the file was first created. Modification date and time: The timestamp of the last time the file content was modified. File access permissions: Restrictions on who can read, write, or execute the file. File type: Information about the type of file (e.g., .docx, .jpg, .exe). 2. Storage: Finding a Home Storage devices like hard disk drives (HDDs), solid-state drives (SSDs), and flash drives hold the data associated with files. However, the data isn\'t stored as a continuous stream of information. Instead, it\'s broken down into smaller chunks called sectors. When a file is created, the operating system allocates a specific number of sectors on the storage device to hold the file content. This allocation process can happen in various ways depending on the file system used. Here are some key points to remember about file storage: Fragmentation: Over time, as files are created, deleted, and resized, the available sectors become fragmented across the storage device. This fragmentation can impact file access speed. File Allocation Table (FAT) or Similar Structures: Some file systems rely on a separate table (FAT) or index that keeps track of which sectors belong to specific files. Deleted Files: When a file is deleted, the operating system typically only removes the reference to the file from the directory structure. The actual data may still reside on the storage device until overwritten by new data. 3. Access: Reading and Writing We interact with files by accessing them for various purposes, such as reading a document, editing an image, or running a program. This involves the following steps: File System Request: When an application attempts to access a file, it sends a request to the operating system. Directory Lookup: The opera | Tool | ★★★ | ||
| 2024-04-15 08:13:08 | MongoDB étend sa collaboration avec Google Cloud (lien direct) | MongoDB étend sa collaboration avec Google Cloud pour aider ses clients à déployer et à mettre à l'échelle de nouvelles catégories d'applications La disponibilité de MongoDB Atlas Search Nodes sur Google Cloud permet aux entreprises d'isoler et de mettre à l'échelle les charges de travail d'IA générative de manière plus simple et plus rentable. L'extension Vertex AI de Google Cloud pour MongoDB Atlas et la nouvelle intégration entre Spark et BigQuery permettent aux clients de créer des applications d'IA générative de manière encore plus transparente en utilisant leurs propres données. MongoDB rejoint le réseau Industry Value Network (IVN) de Google Cloud et présente une nouvelle intégration de MongoDB Atlas à la solution Manufacturing Data Engine de Google Cloud pour aider les entreprises à créer des solutions adaptées à leur secteur. Le déploiement des outils de gestion de base de données MongoDB Enterprise Advanced (EA) dans le portefeuille de solutions Google Distributed Cloud (GDC) aide les entreprises à exécuter des applications conformes aux exigences de sécurité et de confidentialité des données les plus strictes. - Produits | Tool Cloud | ★★★ | ||
| 2024-04-12 21:24:21 | VPN par Google One Service pour arrêter plus tard cette année VPN By Google One Service To Shut Down Later This Year (lien direct) |
Google a annoncé qu'il fermait son service complémentaire gratuit, VPN de Google One, dans les prochains mois après son lancement il y a moins de quatre ans.
Pour les personnes inconscientes, en octobre 2020, Google a déployé un service de réseau privé virtuel gratuit (VPN) appelé "VPN par Google One" dans certains pays à tous les clients avec des plans d'abonnement de 2 To ou plus sur Google One, son abonnementService de stockage cloud.
De plus, le service VPN gratuit a été annoncé comme une couche supplémentaire de protection en ligne pour votre téléphone Android & # 8221;Et cela permet de la tranquillité d'esprit que vos données sont sûres. & # 8221;
Cependant, 9to5Google rapporte que la société envoie désormais un e-mail à Google One utilisateurs pour les informer de sa fermeture.
«En mettant l'accent sur la fourniture des fonctionnalités et des avantages les plus demandés, nous cessons la livraison gratuite pour sélectionner des commandes imprimées de Google Photos (au Canada, au Royaume-Uni, aux États-Unis et à l'UE) à partir du 15 mai etVPN par Google One plus tard cette année », lit l'e-mail envoyé aux utilisateurs.
Bien que l'e-mail ne mentionne pas la raison spécifique de la fermeture ou la date de clôture exacte du service VPN Google One, un porte-parole de l'entreprise a déclaré à 9to5Google que la société abandonnait la fonctionnalité VPN en raison de l'équipe & # 8220;Les gens trouvés n'étaient tout simplement pas utilisés. & # 8221;
Le porte-parole a également ajouté que la dépréciation permettra à l'équipe de «recentrer» et de «prendre en charge des fonctionnalités plus demandées avec Google One».
Cependant, les propriétaires des smartphones de Pixel 7 de Google et au-dessus pourront toujours utiliser la fonction VPN intégrée gratuite par Google One après qu'il n'est pas disponible via l'application Paramètres sur les périphériques Pixel.
De plus, la fonction VPN disponible avec Google Fi Wireless Service sera également disponible.
Outre ce qui précède, Google a également annoncé la disponibilité de Magic Editor, un outil de retouche photo basé sur l'IA dans Google Photos, à tous les utilisateurs de Pixel, qui était initialement limité aux utilisateurs de Pixel 8 et Pixel 8 Pro.
Google has announced that it is shutting down its free add-on service, VPN by Google One, in the coming months after it was launched less than four years ago. For those unaware, in October 2020, Google rolled out a free virtual private network (VPN) service called “VPN by Google One” in select countries to all customers with 2TB or higher subscription plans on Google One, its subscription-based cloud storage service. Further, the free VPN service was advertised as an “extra layer of online protection for your Android phone” and that allows for “peace of mind that your data is safe.” However, 9to5Google reports that the company is now emailing Google One users to notify them of its shutdown. “With a focus on providing the most in-demand features and benefits, we\'re discontinuing free shipping for select print orders from Google Photos (in Canada, the UK, US, and EU) starting on May 15 and VPN by Google One later this year,” reads the email sent to the users. Although the email doesn\'t mention the specific reason for the shutdown or the exact closing date for the Google One VPN service, a company spokesperson told 9to5Google that the company is discontinuing the VPN feature because the team “found people simply weren\'t using it.” The spokesperson also adde |
Tool Mobile Cloud | ★★ | ||
| 2024-04-12 20:39:19 | Nouvel outil protège les organisations de nxdomain attaques New Tool Shields Organizations From NXDOMAIN Attacks (lien direct) |
Akamai rejoint une liste croissante de fournisseurs de sécurité visant à renforcer les défenses des entreprises.
Akamai joins a growing list of security vendors aiming to strengthen companies\' DNS defenses. |
Tool | ★★ | ||
| 2024-04-12 18:11:30 | TA547 cible les organisations allemandes avec Rhadamanthys Stealer TA547 Targets German Organizations with Rhadamanthys Stealer (lien direct) |
#### Géolocations ciblées
- Allemagne
## Instantané
Proofpoint a identifié TA547 lancement d'une campagne de courriel ciblant les organisations allemandes avec Rhadamanthys malware, marquant la première utilisation connue de Rhadamanthys par cet acteur de menace.La campagne consistait à usurper l'identité d'une entreprise de vente au détail allemande dans des e-mails contenant des fichiers ZIP protégés par mot de passe prétendument liés aux factures, ciblant plusieurs industries en Allemagne.
## Description
Les fichiers zip contenaient des fichiers LNK qui, lorsqu'ils sont exécutés, ont déclenché un script PowerShell pour exécuter un script distant chargeant des Rhadamanthys en mémoire, en contournant l'écriture de disque.Le script PowerShell affichait des caractéristiques suggérant un contenu généré par la machine, potentiellement à partir de modèles de langues grands (LLM).
La récente campagne en Allemagne représente un changement dans les techniques de TA547, y compris l'utilisation de LNK comprimés et du voleur Rhadamanthys non observé auparavant.L'incorporation de contenu suspecté de LLM dans la chaîne d'attaque donne un aperçu de la façon dont les acteurs de la menace tirent parti du contenu généré par LLM dans les campagnes de logiciels malveillants, bien qu'il n'ait pas modifié la fonctionnalité ou l'efficacité du malware ou la façon dont les outils de sécurité ont défendu contre lui.
## Recommandations
[Consultez la rédaction de Microsoft \\ sur les voleurs d'informations ici.] (Https://sip.security.microsoft.com/intel-profiles/2296d491ea381b532b24f2575f9418d4b6723c17b8a1f507d20c2140a75d16d6)
[Consultez OSINT supplémentaire sur Rhadamanthys ici.] (Https://sip.security.microsoft.com/intel-explorer/articles/0131b256)
## Les références
[https://www.poolinpoint.com/us/blog/thereat-insight/security-brief-ta547-targets-geman-organizations-rhadamanthys-tealermenace-insight / sécurité-Brief-Ta547-Targets-German-Organisations-Rhadamanthys-Stealer)
#### Targeted Geolocations - Germany ## Snapshot Proofpoint has identified TA547 launching an email campaign targeting German organizations with Rhadamanthys malware, marking the first known use of Rhadamanthys by this threat actor. The campaign involved impersonating a German retail company in emails containing password-protected ZIP files purportedly related to invoices, targeting multiple industries in Germany. ## Description The ZIP files contained LNK files which, when executed, triggered a PowerShell script to run a remote script loading Rhadamanthys into memory, bypassing disk writing. The PowerShell script displayed characteristics suggestive of machine-generated content, potentially from large language models (LLMs). The recent campaign in Germany represents a shift in techniques for TA547, including the use of compressed LNKs and the previously unobserved Rhadamanthys stealer. The incorporation of suspected LLM-generated content into the attack chain provides insight into how threat actors are leveraging LLM-generated content in malware campaigns, although it did not change the functionality or efficacy of the malware or the way security tools defended against it. ## Recommendations [Check out Microsoft\'s write-up on information stealers here.](https://sip.security.microsoft.com/intel-profiles/2296d491ea381b532b24f2575f9418d4b6723c17b8a1f507d20c2140a75d16d6) [Check out additional OSINT on Rhadamanthys here.](https://sip.security.microsoft.com/intel-explorer/articles/0131b256) ## References [https://www.proofpoint.com/us/blog/threat-insight/security-brief-ta547-targets-german-organizations-rhadamanthys-stealer](https://www.proofpoint.com/us/blog/threat-insight/security-brief-ta547-targets-german-organizations-rhadamanthys-stealer) |
Malware Tool Threat | ★★ | ||
| 2024-04-12 17:02:59 | Exploitation zéro-jour de la vulnérabilité d'exécution du code distant non authentifié dans GlobalProtect (CVE-2024-3400) Zero-Day Exploitation of Unauthenticated Remote Code Execution Vulnerability in GlobalProtect (CVE-2024-3400) (lien direct) |
> La volexité tient à remercier les réseaux Palo Alto pour leur partenariat, leur coopération et leur réponse rapide à ce problème critique.Leurs recherches peuvent être trouvées ici.Le 10 avril 2024, la volexité a identifié l'exploitation zéro-jour d'une vulnérabilité trouvée dans la fonctionnalité GlobalProtect de Palo Alto Networks Pan-OS à l'un de ses clients de surveillance de la sécurité des réseaux (NSM).La volexité a reçu des alertes concernant le trafic de réseau suspect émanant du pare-feu du client.Une enquête ultérieure a déterminé que le dispositif avait été compromis.Le lendemain, le 11 avril 2024, la volexité a observé plus loin, une exploitation identique à un autre de ses clients NSM par le même acteur de menace.L'acteur de menace, que volexité suit sous l'alias UTA0218, a pu exploiter à distance l'appareil de pare-feu, créer un shell inversé et télécharger d'autres outils sur l'appareil.L'attaquant s'est concentré sur l'exportation des données de configuration des périphériques, puis en le tirant en tirant comme point d'entrée pour se déplacer latéralement dans [& # 8230;]
>Volexity would like to thank Palo Alto Networks for their partnership, cooperation, and rapid response to this critical issue. Their research can be found here. On April 10, 2024, Volexity identified zero-day exploitation of a vulnerability found within the GlobalProtect feature of Palo Alto Networks PAN-OS at one of its network security monitoring (NSM) customers. Volexity received alerts regarding suspect network traffic emanating from the customer\'s firewall. A subsequent investigation determined the device had been compromised. The following day, April 11, 2024, Volexity observed further, identical exploitation at another one of its NSM customers by the same threat actor. The threat actor, which Volexity tracks under the alias UTA0218, was able to remotely exploit the firewall device, create a reverse shell, and download further tools onto the device. The attacker focused on exporting configuration data from the devices, and then leveraging it as an entry point to move laterally within […] |
Tool Vulnerability Threat | ★★★ | ||
| 2024-04-12 15:19:00 | Les pirates iraniens de Muddywater adoptent un nouvel outil C2 \\ 'darkbeatc2 \\' dans la dernière campagne Iranian MuddyWater Hackers Adopt New C2 Tool \\'DarkBeatC2\\' in Latest Campaign (lien direct) |
L'acteur de menace iranien connue sous le nom de Muddywater a été attribué à une nouvelle infrastructure de commandement et de contrôle (C2) appelé & nbsp; darkbeatc2, devenant le dernier outil de ce type dans son arsenal après & nbsp; middyc2go.
"Tout en passant occasionnellement à un nouvel outil d'administration à distance ou en modifiant leur cadre C2, les méthodes de Muddywater \\ restent constantes"
The Iranian threat actor known as MuddyWater has been attributed to a new command-and-control (C2) infrastructure called DarkBeatC2, becoming the latest such tool in its arsenal after SimpleHarm, MuddyC3, PhonyC2, and MuddyC2Go. "While occasionally switching to a new remote administration tool or changing their C2 framework, MuddyWater\'s methods remain constant," Deep |
Tool Threat | ★★ | ||
| 2024-04-12 14:00:00 | Sécurité des infrastructures critiques: observations des lignes de front Critical Infrastructure Security: Observations From the Front Lines (lien direct) |
Les attaques contre des infrastructures critiques accélèrent - mais les organisations ont désormais les connaissances et les outils nécessaires pour se défendre contre eux.
Attacks on critical infrastructure are ramping up - but organizations now have the knowledge and tools needed to defend against them. |
Tool | ★★ | ||
| 2024-04-12 10:39:00 | Écumoire de carte de crédit sournois déguisée en tracker Facebook inoffensif Sneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker (lien direct) |
Les chercheurs en cybersécurité ont découvert un skimmer de la carte de crédit qui est caché dans un faux script de tracker Meta Pixel et NBSP; dans une tentative d'éliminer la détection.
SUCURI a déclaré que les logiciels malveillants sont injectés dans des sites Web via des outils qui permettent un code personnalisé, tels que des plugins WordPress comme & nbsp; Simple personnalisé CSS et JS et nbsp; ou la section "Scripts divers" du panneau d'administration Magento.
"
Cybersecurity researchers have discovered a credit card skimmer that\'s concealed within a fake Meta Pixel tracker script in an attempt to evade detection. Sucuri said that the malware is injected into websites through tools that allow for custom code, such as WordPress plugins like Simple Custom CSS and JS or the "Miscellaneous Scripts" section of the Magento admin panel. " |
Malware Tool | ★★★ | ||
| 2024-04-12 08:01:00 | Le groupe de menaces Fin7 cible l'industrie automobile américaine Threat Group FIN7 Targets the U.S. Automotive Industry (lien direct) |
Les analystes de BlackBerry ont identifié une campagne de phisces de lance du groupe de menaces FIN7 qui ciblait un grand constructeur automobile basé aux États-Unis.FIN7 a utilisé le leurre d'un outil de numérisation IP gratuit pour exécuter des logiciels malveillants et prendre pied initial.
BlackBerry analysts have identified a spear-phishing campaign by threat group FIN7 that targeted a large automotive manufacturer based in the United States. FIN7 used the lure of a free IP scanning tool to run malware and gain an initial foothold. |
Malware Tool Threat | ★★ | ||
| 2024-04-12 06:00:03 | Arrêt de cybersécurité du mois: vaincre les attaques de création d'applications malveillantes Cybersecurity Stop of the Month: Defeating Malicious Application Creation Attacks (lien direct) |
This blog post is part of a monthly series, Cybersecurity Stop of the Month, which explores the ever-evolving tactics of today\'s cybercriminals. It focuses on the critical first three steps in the attack chain in the context of email threats. The goal of this series is to help you understand how to fortify your defenses to protect people and defend data against emerging threats in today\'s dynamic threat landscape. The critical first three steps of the attack chain-reconnaissance, initial compromise and persistence. So far in this series, we have examined these types of attacks: Supplier compromise EvilProxy SocGholish eSignature phishing QR code phishing Telephone-oriented attack delivery (TOAD) Payroll diversion MFA manipulation Supply chain compromise Multilayered malicious QR code attack In this post, we examine an emerging threat-the use of malicious cloud applications created within compromised cloud tenants following account takeover. We refer to it as MACT, for short. Background Cloud account takeover (ATO) attacks are a well-known risk. Research by Proofpoint found that last year more than 96% of businesses were actively targeted by these attacks and about 60% had at least one incident. Financial damages reached an all-time high. These findings are unsettling. But there is more for businesses to worry about. Cybercriminals and state-sponsored entities are rapidly adopting advanced post-ATO techniques. And they have embraced the use of malicious and abused OAuth apps. In January 2024, Microsoft revealed that a nation-state attacker had compromised its cloud environments and stolen valuable data. This attack was attributed to TA421 (aka Midnight Blizzard and APT29), which are threat groups that have been attributed to Russia\'s Foreign Intelligence Service (SVR). Attackers exploited existing OAuth apps and created new ones within hijacked cloud tenants. After the incident, CISA issued a new advisory for businesses that rely on cloud infrastructures. Proofpoint threat researchers observed attackers pivoting to the use of OAuth apps from compromised-and often verified-cloud tenants. Threat actors take advantage of the trust that\'s associated with verified or recognized identities to spread cloud malware threats as well as establish persistent access to sensitive resources. The scenario Proofpoint monitors a malicious campaign named MACT Campaign 1445. It combines a known tactic used by cloud ATO attackers with new tactics, techniques and procedures. So far, it has affected dozens of businesses and users. In this campaign, attackers use hijacked user accounts to create malicious internal apps. In tandem, they also conduct reconnaissance, exfiltrate data and launch additional attacks. Attackers use a unique anomalous URL for the malicious OAuth apps\' reply URL-a local loopback with port 7823. This port is used for TCP traffic. It is also associated with a known Windows Remote Access Trojan (RAT). Recently, Proofpoint researchers found four accounts at a large company in the hospitality industry compromised by attackers. In a matter of days, attackers used these accounts to create four distinct malicious OAuth apps. The threat: How did the attack happen? Here is a closer look at how the attack unfolded. Initial access vectors. Attackers used a reverse proxy toolkit to target cloud user accounts. They sent individualized phishing lures to these users, which enabled them to steal their credentials as well as multifactor authentication (MFA) tokens. A shared PDF file with an embedded phishing URL that attackers used to steal users\' credentials. Unauthorized access (cloud account takeover). Once attackers had stolen users\' credentials, they established unauthorized access to the four targeted accounts. They logged in to several native Microsoft 365 sign-in apps, including “Azure Portal” and “Office Home.” Cloud malware (post-access OAuth app creat | Spam Malware Tool Threat Cloud | APT 29 | ★★★ | |
| 2024-04-11 23:38:46 | Outils OSINT les mieux payés et gratuits pour 2024 Best Paid and Free OSINT Tools for 2024 (lien direct) |
> Par waqas
Dans cet article, nous explorerons 12 outils OSINT payants et gratuits qui sont accessibles au public et peuvent être très utiles lorsqu'ils sont utilisés correctement et à des fins appropriées.
Ceci est un article de HackRead.com Lire la publication originale: Outils OSINT les mieux payés et gratuits pour 2024
>By Waqas In this article, we will explore 12 paid and free OSINT tools that are publicly available and can be very useful when utilized properly and for appropriate purposes. This is a post from HackRead.com Read the original post: Best Paid and Free OSINT Tools for 2024 |
Tool | ★★★★ | ||
| 2024-04-11 16:00:00 | Apple stimule les alertes spyware pour les attaques mercenaires Apple Boosts Spyware Alerts For Mercenary Attacks (lien direct) |
La révision souligne que des sociétés comme NSO Group, connues pour des outils de surveillance comme Pegasus
The revision points out companies like NSO Group, known for surveillance tools like Pegasus |
Tool | ★★ | ||
| 2024-04-11 15:17:48 | La violation des données SISENSE déclenche une alerte CISA et des appels urgents pour les réinitialités des informations d'identification Sisense Data Breach Triggers CISA Alert and Urgent Calls for Credential Resets (lien direct) |
> Le gouvernement américain émet une alerte rouge pour ce qui semble être une violation massive de la chaîne d'approvisionnement à Sissen, une entreprise qui vend des outils d'analyse de grosses données.
>The US government issues a red-alert for what appears to be a massive supply chain breach at Sisense, a company that sells big-data analytics tools. |
Data Breach Tool | ★★ | ||
| 2024-04-11 12:14:00 | Apple étend le système d'alerte spyware pour avertir les utilisateurs des attaques de mercenaires Apple Expands Spyware Alert System to Warn Users of Mercenary Attacks (lien direct) |
Apple mercredi & nbsp; révisé & nbsp; sa documentation relative à son système de notification de menace spyware mercenaire pour mentionner qu'il alerte les utilisateurs lorsqu'ils peuvent avoir été ciblés individuellement par de telles attaques.
Il a également spécifiquement appelé des sociétés comme NSO Group pour développer des outils de surveillance commerciale tels que Pegasus qui sont utilisés par les acteurs de l'État pour réaliser "ciblé individuellement
Apple on Wednesday revised its documentation pertaining to its mercenary spyware threat notification system to mention that it alerts users when they may have been individually targeted by such attacks. It also specifically called out companies like NSO Group for developing commercial surveillance tools such as Pegasus that are used by state actors to pull off "individually targeted |
Tool Threat Commercial | ★★★★ | ||
| 2024-04-11 06:23:43 | FAQS de l'état de l'État 2024 du rapport Phish, partie 1: Le paysage des menaces FAQs from the 2024 State of the Phish Report, Part 1: The Threat Landscape (lien direct) |
In this two-part blog series, we will address many of the frequently asked questions submitted by attendees. In our first installment, we address questions related to the threat landscape. Understanding the threat landscape is paramount in crafting a human-centric security strategy. That\'s the goal behind our 10th annual State of the Phish report. When you know what threats are out there and how people are interacting with them, you can create a modern cybersecurity strategy that puts the complexity of human behavior and interaction at the forefront. Our report was launched a month ago. Since then, we\'ve followed up with a few webinars to discuss key findings from the report, including: Threat landscape findings: Over 1 million phishing threats involved EvilProxy, which bypasses multifactor authentication (MFA). Yet, 89% of security pros still believe that MFA provides complete protection against account takeover. BEC threat actors benefit from generative AI. Proofpoint detected and stopped over 66 million targeted business email compromise (BEC) attacks per month on average in 2023. User behavior and attitude findings: 71% of surveyed users took at least one risky action, and 96% of them knew that those actions were associated with risk. 58% of those risky actions were related to social engineering tactics. 85% of security pros believed that most employees know they are responsible for security. Yet nearly 60% of employees either weren\'t sure or disagreed. These findings inspired hundreds of questions from audiences across the world. What follows are some of the questions that repeatedly came up. Frequently asked questions What are the definitions of BEC and TOAD? Business email compromise (BEC) essentially means fraud perpetrated through email. It can take many forms, such as advance fee fraud, payroll redirection, fraudulent invoicing or even extortion. BEC typically involves a deception, such as the spoofing of a trusted third party\'s domain or the impersonation of an executive (or literally anyone the recipient trusts). BEC is hard to detect because it is generally pure social engineering. In other words, there is often no credential harvesting portal or malicious payload involved. Threat actors most often use benign conversation to engage the victim. Once the victim is hooked, attackers then convince that person to act in favor of them, such as wiring money to a specified account. Similarly, telephone-oriented attack delivery (TOAD) attacks also use benign conversations. But, in this case, a threat actor\'s goal is to motivate the victim to make a phone call. From there, they will walk their target through a set of steps, which usually involve tricking the victim into giving up their credentials or installing a piece of malware on their computer. TOAD attacks have been associated with high-profile malware families known to lead to ransomware, as well as with a wide variety of remote access tools like AnyDesk that provide the threat actors direct access to victims\' machines. The end goal might still be fraud; for example, there have been cases where payment was solicited for “IT services” or software (Norton LifeLock). But the key differentiator for TOAD, compared with BEC, is the pivot out of the email space to a phone call., is the pivot out of the email space to the phone. What is the difference between TOAD and vishing? TOAD often starts with an email and requires victims to call the fraudulent number within that email. Vishing, on the other hand, generally refers to fraudulent solicitation of personally identifiable information (PII) and may or may not involve email (it could result from a direct call). Some TOAD attempts may fall into this category, but most perpetrators focus on getting software installed on a victim\'s machine. How do you see artificial intelligence (AI) affecting phishing? What are security best practices to help defend against these novel phishing attacks? AI allows threat actors to tighten up grammatical and s | Ransomware Malware Tool Threat Cloud Technical | ★★★ | ||
| 2024-04-10 14:45:00 | Cagey Phishing Campaign fournit plusieurs rats pour voler des données Windows Cagey Phishing Campaign Delivers Multiple RATs to Steal Windows Data (lien direct) |
Diverses fonctionnalités anti-détection, y compris l'utilisation de l'outil d'évasion antivirus brouillé, alimentent une attaque qui vise à prendre le contrôle des machines Microsoft Windows.
Various anti-detection features, including the use of the ScrubCrypt antivirus-evasion tool, fuel an attack that aims to take over Microsoft Windows machines. |
Tool | ★★★ | ||
| 2024-04-10 13:43:47 | Un guide détaillé sur RustScan A Detailed Guide on RustScan (lien direct) |
Dans le domaine de la cybersécurité, les outils de numérisation du réseau jouent un rôle vital dans la reconnaissance et l'évaluation de la vulnérabilité.Parmi la gamme d'options disponibles, RustScan a
In the realm of cybersecurity, network scanning tools play a vital role in reconnaissance and vulnerability assessment. Among the array of options available, Rustscan has |
Tool Vulnerability | ★★★ | ||
| 2024-04-10 10:32:57 | Silos brillants avec un cyber maill, l'épine dorsale des cyberopes renforcés AI Shattering Silos With Cyber Mesh, the Backbone of AI-Reinforced CyberOps (lien direct) |
Le cyber maillage ne concerne pas seulement l'intégration, il s'agit de favoriser un écosystème intelligent où les outils de sécurité fonctionnent ensemble comme une machine bien huilée, alimentée par les idées glanées de l'IA et de l'apprentissage automatique.
Cyber Mesh is not just about integration, it\'s about fostering an intelligent ecosystem where security tools work together like a well-oiled machine, powered by the insights gleaned from AI and machine learning. |
Tool | ★★★ | ||
| 2024-04-10 10:12:47 | Mémoire de sécurité: TA547 cible les organisations allemandes avec Rhadamanthys Stealer Security Brief: TA547 Targets German Organizations with Rhadamanthys Stealer (lien direct) |
Ce qui s'est passé Proofpoint a identifié TA547 ciblant les organisations allemandes avec une campagne de courriel livrant des logiciels malveillants de Rhadamanthys.C'est la première fois que les chercheurs observent TA547 utiliser des Rhadamanthys, un voleur d'informations utilisé par plusieurs acteurs de menaces cybercriminaux.De plus, l'acteur a semblé utiliser un script PowerShell que les chercheurs soupçonnent a été généré par un modèle grand langage (LLM) tel que Chatgpt, Gemini, Copilot, etc. Les e-mails envoyés par l'acteur de menace ont usurpé l'identité de la société de vente au détail allemande Metro prétendant se rapporter aux factures. De: Metro! Sujet: Rechnung No: 31518562 Attachement: in3 0gc- (94762) _6563.zip Exemple TA547 Courriel imitant l'identité de la société de vente au détail allemande Metro. Les e-mails ont ciblé des dizaines d'organisations dans diverses industries en Allemagne.Les messages contenaient un fichier zip protégé par mot de passe (mot de passe: mar26) contenant un fichier LNK.Lorsque le fichier LNK a été exécuté, il a déclenché PowerShell pour exécuter un script PowerShell distant.Ce script PowerShell a décodé le fichier exécutable Rhadamanthys codé de base64 stocké dans une variable et l'a chargé en tant qu'assemblage en mémoire, puis a exécuté le point d'entrée de l'assemblage.Il a par la suite chargé le contenu décodé sous forme d'un assemblage en mémoire et a exécuté son point d'entrée.Cela a essentiellement exécuté le code malveillant en mémoire sans l'écrire sur le disque. Notamment, lorsqu'il est désabuscée, le deuxième script PowerShell qui a été utilisé pour charger les rhadamanthys contenait des caractéristiques intéressantes non couramment observées dans le code utilisé par les acteurs de la menace (ou les programmeurs légitimes).Plus précisément, le script PowerShell comprenait un signe de livre suivi par des commentaires grammaticalement corrects et hyper spécifiques au-dessus de chaque composant du script.Il s'agit d'une sortie typique du contenu de codage généré par LLM et suggère que TA547 a utilisé un certain type d'outil compatible LLM pour écrire (ou réécrire) le PowerShell, ou copié le script à partir d'une autre source qui l'avait utilisé. Exemple de PowerShell soupçonné d'être écrit par un LLM et utilisé dans une chaîne d'attaque TA547. Bien qu'il soit difficile de confirmer si le contenu malveillant est créé via LLMS & # 8211;Des scripts de logiciels malveillants aux leurres d'ingénierie sociale & # 8211;Il existe des caractéristiques d'un tel contenu qui pointent vers des informations générées par la machine plutôt que générées par l'homme.Quoi qu'il en soit, qu'il soit généré par l'homme ou de la machine, la défense contre de telles menaces reste la même. Attribution TA547 est une menace cybercriminale à motivation financière considérée comme un courtier d'accès initial (IAB) qui cible diverses régions géographiques.Depuis 2023, TA547 fournit généralement un rat Netsupport mais a parfois livré d'autres charges utiles, notamment Stealc et Lumma Stealer (voleurs d'informations avec des fonctionnalités similaires à Rhadamanthys).Ils semblaient favoriser les pièces javascript zippées comme charges utiles de livraison initiales en 2023, mais l'acteur est passé aux LNK compressées début mars 2024. En plus des campagnes en Allemagne, d'autres ciblage géographique récent comprennent des organisations en Espagne, en Suisse, en Autriche et aux États-Unis. Pourquoi est-ce important Cette campagne représente un exemple de certains déplacements techniques de TA547, y compris l'utilisation de LNK comprimés et du voleur Rhadamanthys non observé auparavant.Il donne également un aperçu de la façon dont les acteurs de la menace tirent parti de contenu probable généré par LLM dans les campagnes de logiciels malveillants. Les LLM peuvent aider les acteurs de menace à comprendre les chaînes d'attaque plus sophistiquées utilisées | Malware Tool Threat | ChatGPT | ★★ | |
| 2024-04-10 10:00:00 | Les risques de sécurité du chat Microsoft Bing AI pour le moment The Security Risks of Microsoft Bing AI Chat at this Time (lien direct) |
The content of this post is solely the responsibility of the author. AT&T does not adopt or endorse any of the views, positions, or information provided by the author in this article. AI has long since been an intriguing topic for every tech-savvy person, and the concept of AI chatbots is not entirely new. In 2023, AI chatbots will be all the world can talk about, especially after the release of ChatGPT by OpenAI. Still, there was a past when AI chatbots, specifically Bing’s AI chatbot, Sydney, managed to wreak havoc over the internet and had to be forcefully shut down. Now, in 2023, with the world relatively more technologically advanced, AI chatbots have appeared with more gist and fervor. Almost every tech giant is on its way to producing large Language Model chatbots like chatGPT, with Google successfully releasing its Bard and Microsoft and returning to Sydney. However, despite the technological advancements, it seems that there remains a significant part of the risks that these tech giants, specifically Microsoft, have managed to ignore while releasing their chatbots. What is Microsoft Bing AI Chat Used for? Microsoft has released the Bing AI chat in collaboration with OpenAI after the release of ChatGPT. This AI chatbot is a relatively advanced version of ChatGPT 3, known as ChatGPT 4, promising more creativity and accuracy. Therefore, unlike ChatGPT 3, the Bing AI chatbot has several uses, including the ability to generate new content such as images, code, and texts. Apart from that, the chatbot also serves as a conversational web search engine and answers questions about current events, history, random facts, and almost every other topic in a concise and conversational manner. Moreover, it also allows image inputs, such that users can upload images in the chatbot and ask questions related to them. Since the chatbot has several impressive features, its use quickly spread in various industries, specifically within the creative industry. It is a handy tool for generating ideas, research, content, and graphics. However, one major problem with its adoption is the various cybersecurity issues and risks that the chatbot poses. The problem with these cybersecurity issues is that it is not possible to mitigate them through traditional security tools like VPN, antivirus, etc., which is a significant reason why chatbots are still not as popular as they should be. Is Microsoft Bing AI Chat Safe? Like ChatGPT, Microsoft Bing Chat is fairly new, and although many users claim that it is far better in terms of responses and research, its security is something to remain skeptical over. The modern version of the Microsoft AI chatbot is formed in partnership with OpenAI and is a better version of ChatGPT. However, despite that, the chatbot has several privacy and security issues, such as: The chatbot may spy on Microsoft employees through their webcams. Microsoft is bringing ads to Bing, which marketers often use to track users and gather personal information for targeted advertisements. The chatbot stores users\' information, and certain employees can access it, which breaches users\' privacy. - Microsoft’s staff can read chatbot conversations; therefore, sharing sensitive information is vulnerable. The chatbot can be used to aid in several cybersecurity attacks, such as aiding in spear phishing attacks and creating ransomware codes. Bing AI chat has a feature that lets the chatbot “see” what web pages are open on the users\' other tabs. The chatbot has been known to be vulnerable to prompt injection attacks that leave users vulnerable to data theft and scams. Vulnerabilities in the chatbot have led to data le | Ransomware Tool Vulnerability | ChatGPT | ★★ | |
| 2024-04-09 23:30:40 | Les nouveaux outils JAMF donnent aux contrôles de sécurité et de conformité de l'entreprise New Jamf Tools Give Enterprise IT Security and Compliance Controls (lien direct) |
La société de gestion de périphériques a introduit un score de durcissement de flotte et une escalade de privilège (le bon type) à sa plate-forme de sécurité finale pour les appareils Apple.
The device management company introduced a Fleet Hardening Score and Privilege Escalation (the good kind) to its endpoint security platform for Apple devices. |
Tool | ★★ | ||
| 2024-04-09 19:00:26 | La maison se précipitait vers l'expression sur les outils de surveillance expirés House hurtles toward showdown over expiring surveillance tools (lien direct) |
> La question est l'article 702 de la Foreign Intelligence Surveillance Act, qui autorise l'espionnage que certains considèrent comme vitale pour la sécurité et que d'autres considèrent comme une menace de confidentialité incontrôlable.
>At issue is Section 702 of the Foreign Intelligence Surveillance Act, which authorizes snooping that some consider vital to security and others view as an out-of-control privacy threat. |
Tool Threat | ★★ | ||
| 2024-04-09 18:12:39 | Les outils et plugins essentiels pour le développement WordPress The Essential Tools and Plugins for WordPress Development (lien direct) |
> Par owais sultan
WordPress, un système de gestion de contenu largement utilisé, doit une grande partie de sa flexibilité aux plugins.Ces petits & # 8230;
Ceci est un article de HackRead.com Lire le post original: l'essentielOutils et plugins pour le développement WordPress
>By Owais Sultan WordPress, a widely used content management system, owes a great deal of its flexibility to plugins. These small… This is a post from HackRead.com Read the original post: The Essential Tools and Plugins for WordPress Development |
Tool | ★★ | ||
| 2024-04-09 12:54:00 | Les attaquants utilisant des outils d'obscurcissement pour fournir des logiciels malveillants en plusieurs étapes via le phishing de la facture Attackers Using Obfuscation Tools to Deliver Multi-Stage Malware via Invoice Phishing (lien direct) |
Les chercheurs en cybersécurité ont découvert une attaque à plusieurs étages complexe qui tire parti des leurres de phishing sur le thème de la facture pour fournir un large éventail de logiciels malveillants tels que & nbsp; Venom Rat, Remcos Rat, Xworm, Nanocore Rat et un voleur qui cible les portefeuilles crypto.
Les e-mails sont livrés avec des pièces jointes de fichiers Vector Graphics (SVG) évolutives qui, une fois cliqué, activent la séquence d'infection, Fortinet
Cybersecurity researchers have discovered an intricate multi-stage attack that leverages invoice-themed phishing decoys to deliver a wide range of malware such as Venom RAT, Remcos RAT, XWorm, NanoCore RAT, and a stealer that targets crypto wallets. The email messages come with Scalable Vector Graphics (SVG) file attachments that, when clicked, activate the infection sequence, Fortinet |
Malware Tool | ★★ | ||
| 2024-04-09 10:00:00 | La menace cachée à la vue: analyse des attaques sous-textuelles dans les communications numériques The Hidden Threat in Plain Sight: Analyzing Subtextual Attacks in Digital Communications (lien direct) |
The content of this post is solely the responsibility of the author. AT&T does not adopt or endorse any of the views, positions, or information provided by the author in this article. In our always-online world, we\'re facing a new kind of cyber threat that\'s just as sneaky as it is harmful: subtextual attacks. These aren\'t your run-of-the-mill security breaches; they\'re cunningly crafted messages that may look harmless—but they actually carry a dangerous payload within them. Join me as we take a closer look at this under-the-radar, but still dangerous, threat. We\'ll explore how these deceptive messages can sneak past our defenses, trick people into taking unwanted actions, and steal sensitive information without ever tripping an alarm. The Rise of Subtextual Attacks Unlike traditional cyber attacks, which are often direct and identifiable, subtextual attacks rely on subtlety and deception. Attackers craft messages that on the surface appear harmless or unrelated to any malicious activity. However, embedded within these communications are instructions, links, or information that can compromise security, manipulate behavior, or extract sensitive data. And not only is big data paramount in advertising and other avenues, but it’s also like keeping everything in your wallet—it’s convenient, helpful even, but signals to attackers that you’re indeed willing to put all your eggs in one basket when it comes to communications. These attacks exploit the nuances of language and context and require a sophisticated understanding of human communication and digital interaction patterns. For instance, a seemingly benign email might include a specific choice of words or phrases that, when interpreted correctly, reveal a hidden command or a disguised link to a malicious site. Psychological Manipulation Through Subtext Subtextual attacks also leverage psychological manipulation, influencing individuals to act in ways that compromise security or divulge confidential information. By understanding the psychological triggers and behavioral patterns of targets, attackers craft messages that subtly guide the recipient\'s actions. For instance, an attacker might use social engineering techniques combined with subtextual cues to convince a user to bypass normal security protocols. An email that seems to come from a trusted colleague or superior, containing subtle suggestions or cues, can be more effective in eliciting certain actions than a direct request or command. Attackers can also exploit the principle of urgency or scarcity, embedding subtle cues in communications that prompt the recipient to act quickly, bypassing their usual critical thinking or security procedures. The Evolution of Digital Forensics To combat the growing rise of subtextual attacks, the field of digital forensics has evolved significantly over the past decade. Initially focused on recovering and analyzing electronic information to investigate crime, digital forensics now incorporates advanced linguistic analysis, data pattern recognition, and machine learning to detect hidden threats. Modern digital forensic tools can analyze vast qua | Ransomware Tool Vulnerability Threat Medical | ★★ | ||
| 2024-04-09 07:00:00 | Indicator of Canary – Traquez les fichiers piégés comme un pro (lien direct) | Indicator of Canary est une collection de preuves de concept (PoC) pour détecter les "canaris", des fichiers piégés avec des indicateurs de compromission et des URLs de callback malveillantes. Les scripts permettent d'extraire ces canaris de différents formats de fichiers, d'identifier leur origine et d'automatiser les vérifications dans les outils. Cela aide à repérer les incidents de sécurité potentiels et à prendre des décisions en conséquence. | Tool | ★★ |
To see everything:
Our RSS (filtrered)
