What's new arround internet
| Src | Date (GMT) | Titre | Description | Tags | Stories | Notes |
| 2021-02-23 14:00:00 | Case Study: SCM Insurance Services Finds True Partnership Cybereason (lien direct) |
 SCM Insurance Services has been supporting the insurance and risk management community for more than 30 years with over 200 locations and over 3,000 employees across North America providing claims adjusting, third-party administration (TPA), risk management, investigative, surveillance, risk mitigation, medical services, forensic services (accounting/engineering), and risk intelligence.
SCM Insurance Services has been supporting the insurance and risk management community for more than 30 years with over 200 locations and over 3,000 employees across North America providing claims adjusting, third-party administration (TPA), risk management, investigative, surveillance, risk mitigation, medical services, forensic services (accounting/engineering), and risk intelligence. |
||||
| 2021-02-22 13:45:00 | Ransomware Attacks Remain Persistent and Pervasive (lien direct) |
 Ransomware has been the scourge of businesses for some time now, and it doesn't seem that there is an end in sight where the impact to business is concerned.
Ransomware has been the scourge of businesses for some time now, and it doesn't seem that there is an end in sight where the impact to business is concerned. |
||||
| 2021-02-19 13:40:58 | Kia Motors America: Ransomware Not Behind Extended Systems Outage (lien direct) |
 Kia Motors America stated that a ransomware attack was not the apparent cause of an extended systems outage affecting the automobile dealer's IT systems. It all started with an error message…
Kia Motors America stated that a ransomware attack was not the apparent cause of an extended systems outage affecting the automobile dealer's IT systems. It all started with an error message… |
Ransomware | |||
| 2021-02-18 14:00:00 | Cybereason Expands Middle East and North Africa Presence with Dubai\'s Oxygen (lien direct) |
 Cybereason is pleased to announce a partnership with Oxygen DMCC, the Dubai-based leader in AI-powered cybersecurity and mobility solutions, enabling enterprises across the Middle East and North Africa (MENA) to detect and end cyber attacks on endpoints anywhere on their networks.
Cybereason is pleased to announce a partnership with Oxygen DMCC, the Dubai-based leader in AI-powered cybersecurity and mobility solutions, enabling enterprises across the Middle East and North Africa (MENA) to detect and end cyber attacks on endpoints anywhere on their networks. |
Guideline | |||
| 2021-02-17 20:19:15 | Malicious Life Podcast: Should Law Enforcement Use Facial Recognition? Pt. 2 (lien direct) |
 It seems likely that legislation alone won't be able to regulate the widespread use of facial recognition. However, placing AI in the hands of law enforcement or the government does have its dangers due to the limitations of the technology itself and the biases of the officers who use it.
It seems likely that legislation alone won't be able to regulate the widespread use of facial recognition. However, placing AI in the hands of law enforcement or the government does have its dangers due to the limitations of the technology itself and the biases of the officers who use it. |
||||
| 2021-02-17 18:35:26 | Global Law Firm Attributes Data Breach to Compromise at File Sharing Provider (lien direct) |
 An international law firm attributed a data breach to a compromise at a cloud solutions company that provides file-sharing services. According to the Wall Street Journal, a threat actor claimed to have stolen data from global law firm Jones Day and published that information on the dark web.
An international law firm attributed a data breach to a compromise at a cloud solutions company that provides file-sharing services. According to the Wall Street Journal, a threat actor claimed to have stolen data from global law firm Jones Day and published that information on the dark web. |
Data Breach Threat | |||
| 2021-02-17 14:00:00 | CISO Stories Podcast: Sled Security - Pandemics, Policies, and Penny-Pinching (lien direct) |
 The Cybersecurity Coalition's Ari Schwartz brings us up to date on some of the organization's initiatives and then dives into some of the challenges SLED defenders are facing in trying to do more with less…
The Cybersecurity Coalition's Ari Schwartz brings us up to date on some of the organization's initiatives and then dives into some of the challenges SLED defenders are facing in trying to do more with less… |
||||
| 2021-02-16 13:00:00 | Cybereason vs. NetWalker Ransomware (lien direct) |
 The NetWalker ransomware has been one of the most notorious ransomware families over the course of the past year, targeting organizations in the US and Europe including several healthcare organizations, despite several known threat actors publicly claiming to abstain from targeting such organizations due to COVID-19.
The NetWalker ransomware has been one of the most notorious ransomware families over the course of the past year, targeting organizations in the US and Europe including several healthcare organizations, despite several known threat actors publicly claiming to abstain from targeting such organizations due to COVID-19. |
Ransomware Threat | |||
| 2021-02-15 14:00:00 | The Cybereason Difference: Why PenTesters Don\'t Want to be Our Valentine (lien direct) |
 This is the inaugural blog for our new series, The Cybereason Difference. Each post will explore a unique way that Cybereason empowers defenders. For this post, we decided to take a look at some of the reasons why we often get notes from our customers to the effect of, “I'm having fun watching our pentesters get frustrated over and over again as they attempt to bypass Cybereason - literally throwing the kitchen sink at it to no avail!”
This is the inaugural blog for our new series, The Cybereason Difference. Each post will explore a unique way that Cybereason empowers defenders. For this post, we decided to take a look at some of the reasons why we often get notes from our customers to the effect of, “I'm having fun watching our pentesters get frustrated over and over again as they attempt to bypass Cybereason - literally throwing the kitchen sink at it to no avail!” |
||||
| 2021-02-12 19:59:42 | CISO Stories Podcast: Telling Scary Stories to the Board? Stop. Here\'s Why… (lien direct) |
 CISOs today have varied tenures at organizations depending upon their ability to master learning the business of the organization. Enjoy this podcast with special guest Mischel Kwon to learn how to translate information security technical issues into a business-focused language and determine the right amount of technical language to share with executives…
CISOs today have varied tenures at organizations depending upon their ability to master learning the business of the organization. Enjoy this podcast with special guest Mischel Kwon to learn how to translate information security technical issues into a business-focused language and determine the right amount of technical language to share with executives… |
||||
| 2021-02-12 14:43:04 | Malicious Life Podcast: Should Law Enforcement Use Facial Recognition? Pt. 1 (lien direct) |
 There are plenty of reasons why law enforcement should use AI for facial recognition - after all, humans are notoriously bad eye witnesses. However, placing AI in the hands of law enforcement does have its dangers due to the limitations of the technology itself and the biases of the officers who use it.
There are plenty of reasons why law enforcement should use AI for facial recognition - after all, humans are notoriously bad eye witnesses. However, placing AI in the hands of law enforcement does have its dangers due to the limitations of the technology itself and the biases of the officers who use it. |
||||
| 2021-02-10 14:00:00 | The Cybereason Malop: Achieving Operation-Centric Security (lien direct) |
 Targeted attacks are increasingly taking aim at multiple users and devices simultaneously as well as leveraging a wider range of tactics, techniques and procedures.
Targeted attacks are increasingly taking aim at multiple users and devices simultaneously as well as leveraging a wider range of tactics, techniques and procedures. |
||||
| 2021-02-09 16:21:37 | Attacker Tries to Poison Florida City\'s Water Supply (lien direct) |
 A cyberattacker attempted to poison a Florida municipality's water supply by breaking into the city's water treatment plant systems. On February 5, an operator at the water treatment plant for the City of Oldsmar in Pinellas County noticed someone controlling his mouse. The operator didn't think much of the activity at first, reported WTSP-TV.
A cyberattacker attempted to poison a Florida municipality's water supply by breaking into the city's water treatment plant systems. On February 5, an operator at the water treatment plant for the City of Oldsmar in Pinellas County noticed someone controlling his mouse. The operator didn't think much of the activity at first, reported WTSP-TV. |
||||
| 2021-02-08 18:47:37 | Extortionists Publish Data Stolen from Two Healthcare Service Providers (lien direct) |
 An attacker group published information stolen from two healthcare service providers in a reported attempt to extort them for money. On February 5, NBC News reported that a well-known ransomware group had published tens of thousands of files to a data leaks website on the dark web. Among those files were scanned diagnostic results, letters to health insurers and a folder containing background checks on employees.
An attacker group published information stolen from two healthcare service providers in a reported attempt to extort them for money. On February 5, NBC News reported that a well-known ransomware group had published tens of thousands of files to a data leaks website on the dark web. Among those files were scanned diagnostic results, letters to health insurers and a folder containing background checks on employees. |
Ransomware | |||
| 2021-02-04 14:00:00 | The Security Value of Exploit Protection (lien direct) |
 An exploit attack occurs when a malicious actor takes advantage of a software vulnerability to penetrate and then damage or steal information from a computer system. One feature that Cybereason provides to protect users from exploit attacks is our Exploit Protection. The following is a quick rundown of some of the key terms for understanding exploit attacks.
An exploit attack occurs when a malicious actor takes advantage of a software vulnerability to penetrate and then damage or steal information from a computer system. One feature that Cybereason provides to protect users from exploit attacks is our Exploit Protection. The following is a quick rundown of some of the key terms for understanding exploit attacks. |
Vulnerability | |||
| 2021-02-04 13:05:00 | Cybereason XDR Dubbed Hottest New Cybersecurity Product by CRN (lien direct) |
 Cybereason is pleased to announce that Cybereason XDR was named one of the hottest new cybersecurity products of 2020 by CRN. With Cybereason XDR, defenders can pinpoint, understand and end any Malop™ (malicious operation) across the entire IT stack whether on-premises, mobile or in the cloud.
Cybereason is pleased to announce that Cybereason XDR was named one of the hottest new cybersecurity products of 2020 by CRN. With Cybereason XDR, defenders can pinpoint, understand and end any Malop™ (malicious operation) across the entire IT stack whether on-premises, mobile or in the cloud. |
||||
| 2021-02-03 16:08:52 | Malicious Life Podcast: Inside Clearview AI Facial Recognition (lien direct) |
 Clearview AI scrapes billions of images off social media and the open web, applies facial recognition algorithms on them, and sells that data to law enforcement agencies all over the world. But who are the people behind this secretive company, and what did a breach into its databases reveal?
Clearview AI scrapes billions of images off social media and the open web, applies facial recognition algorithms on them, and sells that data to law enforcement agencies all over the world. But who are the people behind this secretive company, and what did a breach into its databases reveal? |
||||
| 2021-02-03 14:42:59 | Nearly One-Third of Attack Targets Weren\'t Running SolarWinds (lien direct) |
 Approximately one-third of organizations affected by the SolarWinds supply chain attacks weren't actually running the IT management company's affected software.
Approximately one-third of organizations affected by the SolarWinds supply chain attacks weren't actually running the IT management company's affected software. |
||||
| 2021-02-02 21:07:01 | Krebs, Curry and Cyber Security (lien direct) |
 The daily drumbeat of data spills, breaches, and thefts can foster breach fatigue, apathy, and cynicism among even the hardiest security professionals. What sets in is a suspicion that all our efforts are for naught, and that we are perpetually a step behind the bad guys.
The daily drumbeat of data spills, breaches, and thefts can foster breach fatigue, apathy, and cynicism among even the hardiest security professionals. What sets in is a suspicion that all our efforts are for naught, and that we are perpetually a step behind the bad guys. |
||||
| 2021-02-01 14:00:00 | NHS Warns of New COVID-19 Vaccine-Related Phishing Campaigns (lien direct) |
 The United Kingdom's National Health Service (NHS) warned that scammers are in the process of sending out fake COVID-19 vaccine invitations. On January 25th, Urology Cancer Research & Education (UCARE) Oxford reached out to the NHS on Twitter and shared an image of one such fake invitation that it had received.
The United Kingdom's National Health Service (NHS) warned that scammers are in the process of sending out fake COVID-19 vaccine invitations. On January 25th, Urology Cancer Research & Education (UCARE) Oxford reached out to the NHS on Twitter and shared an image of one such fake invitation that it had received. |
||||
| 2021-01-28 17:55:04 | Emotet Botnet Infrastructure Disrupted in International Takedown (lien direct) |
 Law enforcement entities and judicial authorities located around the world succeeded in disrupting the Emotet botnet's infrastructure through a coordinated takedown effort.
Law enforcement entities and judicial authorities located around the world succeeded in disrupting the Emotet botnet's infrastructure through a coordinated takedown effort. |
||||
| 2021-01-28 14:00:00 | Sam Curry on the \'Real Privacy Mandate\' (lien direct) |
 National Privacy Day is a time to look at the current state of privacy and to set the direction and tone for the future. On January 28, 2021, let's stop and think not just about the minimum requirements of privacy legislation but rather about the world we're building and handing to our children.
National Privacy Day is a time to look at the current state of privacy and to set the direction and tone for the future. On January 28, 2021, let's stop and think not just about the minimum requirements of privacy legislation but rather about the world we're building and handing to our children. |
||||
| 2021-01-28 13:05:00 | Cybereason Partners with Ensign to Provide Managed Detection and Response Services in APAC (lien direct) |
 Cybereason, the leader in future ready attack protection, is pleased to announce a partnership with Ensign InfoSecurity , one of the Asia Pacific's largest pure-play cybersecurity firms, to expand the suite of cybersecurity solutions and services that Ensign offers to protect its Asia Pacific customers from the evolving cyber threats.
Cybereason, the leader in future ready attack protection, is pleased to announce a partnership with Ensign InfoSecurity , one of the Asia Pacific's largest pure-play cybersecurity firms, to expand the suite of cybersecurity solutions and services that Ensign offers to protect its Asia Pacific customers from the evolving cyber threats. |
Guideline | ★★★★★ | ||
| 2021-01-27 14:30:00 | SolarWinds Attacks Highlight Advantage of Indicators of Behavior for Early Detection (lien direct) |
 I've talked about the SolarWinds Supply Chain Attacks recently more than you'd care to know over the past month or so (just ask anyone who knows me), with key points from a few of the discussions making their way into the public sphere here and here.
I've talked about the SolarWinds Supply Chain Attacks recently more than you'd care to know over the past month or so (just ask anyone who knows me), with key points from a few of the discussions making their way into the public sphere here and here. |
||||
| 2021-01-26 14:00:00 | (Déjà vu) Cybereason vs. RansomEXX Ransomware (lien direct) |
 Research by: Daniel Frank
Research by: Daniel Frank |
Ransomware | |||
| 2021-01-25 14:44:34 | Wipro\'s State of Cybersecurity Report Reveals Valuable Insights (lien direct) |
 It is true in general that technology is always changing, and the threat landscape is constantly evolving, but 2020 has amplified the cybersecurity challenge. Organizations of all sizes and across all industries already struggled to effectively manage risk and cyber resilience, but the global pandemic of COVID-19 has introduced a sudden and dramatic shift that tips the playing field in favor of attackers and exacerbates the task.
It is true in general that technology is always changing, and the threat landscape is constantly evolving, but 2020 has amplified the cybersecurity challenge. Organizations of all sizes and across all industries already struggled to effectively manage risk and cyber resilience, but the global pandemic of COVID-19 has introduced a sudden and dramatic shift that tips the playing field in favor of attackers and exacerbates the task. |
Threat | |||
| 2021-01-22 14:00:00 | Last Hurrah: Executive Order to Protect IaaS Platforms from Malicious Actors (lien direct) |
 President Donald Trump signed an executive order to prevent foreign malicious cyber actors from misusing United States Infrastructure as a Service (IaaS) products. In the executive order, dated January 19, President Trump explained that foreign malicious cyber actors were using IaaS products made in the United States to aid their efforts in stealing sensitive information as well as targeting U.S. critical infrastructure:
President Donald Trump signed an executive order to prevent foreign malicious cyber actors from misusing United States Infrastructure as a Service (IaaS) products. In the executive order, dated January 19, President Trump explained that foreign malicious cyber actors were using IaaS products made in the United States to aid their efforts in stealing sensitive information as well as targeting U.S. critical infrastructure: |
||||
| 2021-01-21 14:08:16 | SolarWinds Attacks Highlight Importance of Operation-Centric Approach (lien direct) |
 We're still learning the full extent of the SolarWinds supply chain attacks. On January 11, for instance, researchers published a technical breakdown of a malicious tool detected as SUNSPOT that was employed as part of the infection chain involving the IT management software provider's Orion platform.
We're still learning the full extent of the SolarWinds supply chain attacks. On January 11, for instance, researchers published a technical breakdown of a malicious tool detected as SUNSPOT that was employed as part of the infection chain involving the IT management software provider's Orion platform. |
Tool | Solardwinds Solardwinds | ||
| 2021-01-13 14:00:00 | Cybereason and SYNNEX Corporation Partner to End Cyber Attacks (lien direct) |
 Cybereason and SYNNEX Corporation are pleased to announce a strategic agreement that enables SMBs and Enterprises to detect and end cyber attacks on endpoints anywhere on their networks.
Cybereason and SYNNEX Corporation are pleased to announce a strategic agreement that enables SMBs and Enterprises to detect and end cyber attacks on endpoints anywhere on their networks. |
||||
| 2021-01-12 14:03:32 | (Déjà vu) Cybereason vs. Conti Ransomware (lien direct) |
 Research by: Lior Rochberger
Research by: Lior Rochberger |
Ransomware | |||
| 2021-01-11 21:35:00 | Cybereason and Intel Introduce Hardware-Enabled Ransomware Protections for Businesses (lien direct) |
 Ransomware can literally put organizations and lives at risk, as witnessed in 2020 with the continuous onslaught of attacks against the healthcare industry, research organizations working on COVID-19 vaccines, telecommunication centers, financial institutions, the public sector and companies across every industry vertical.
Ransomware can literally put organizations and lives at risk, as witnessed in 2020 with the continuous onslaught of attacks against the healthcare industry, research organizations working on COVID-19 vaccines, telecommunication centers, financial institutions, the public sector and companies across every industry vertical. |
Ransomware | |||
| 2021-01-05 19:42:44 | Contextualizing Microsoft\'s Source Code Exposure in the SolarWinds Attacks (lien direct) |
 In the middle of December, IT management software provider SolarWinds revealed in a security advisory that it had fallen victim to a sophisticated supply chain attack. The offensive involved the placement of a backdoor known as SUNBURST into versions 2019.4 HF 5, 2020.2 with no hotfix installed and 2020.2 HF 1 of the company's Orion Platform software. If executed, SUNBURST allowed an attacker to compromise the server running the Orion build.
In the middle of December, IT management software provider SolarWinds revealed in a security advisory that it had fallen victim to a sophisticated supply chain attack. The offensive involved the placement of a backdoor known as SUNBURST into versions 2019.4 HF 5, 2020.2 with no hotfix installed and 2020.2 HF 1 of the company's Orion Platform software. If executed, SUNBURST allowed an attacker to compromise the server running the Orion build. |
Solardwinds Solardwinds | |||
| 2021-01-04 13:30:00 | Ever Evolving: Israel Barak on Running Remote SOC Ops (lien direct) |
 We spent some time with Israel Barak, Chief Information Security Officer at Cybereason, who discussed some of the challenges of running a world-wide SOC remotely during the pandemic - check it out...
We spent some time with Israel Barak, Chief Information Security Officer at Cybereason, who discussed some of the challenges of running a world-wide SOC remotely during the pandemic - check it out... |
||||
| 2020-12-24 13:00:00 | Amazon Gift Card Offer Serves Up Dridex Banking Trojan (lien direct) |
 Research by: Daniel Frank
Research by: Daniel Frank |
★★★★ | |||
| 2020-12-23 14:00:00 | Cybereason vs. Clop Ransomware (lien direct) |
 Research by: Daniel Frank
Research by: Daniel Frank |
Ransomware | |||
| 2020-12-22 21:14:06 | Cybereason vs. SolarWinds Supply Chain Attack (lien direct) |
 On December 13, 2020, IT infrastructure management provider SolarWinds issued a Security Advisory regarding their SolarWinds Orion Platform after experiencing a “highly sophisticated” supply chain attack. The activity is reported to have begun as early as Spring 2020, as reported by researchers from security firm FireEye.
On December 13, 2020, IT infrastructure management provider SolarWinds issued a Security Advisory regarding their SolarWinds Orion Platform after experiencing a “highly sophisticated” supply chain attack. The activity is reported to have begun as early as Spring 2020, as reported by researchers from security firm FireEye. |
Solardwinds | |||
| 2020-12-22 14:00:00 | 2021 Security Crystal Ball: Trends and Predictions for the Year Ahead (lien direct) |
 2020 kicked off with a bang, literally, as General Soleimani was killed less than a week into the year. This had immediate repercussions with simple website defacements by minor actors ideologically aligned with Iran and concerns of cyber escalations.
2020 kicked off with a bang, literally, as General Soleimani was killed less than a week into the year. This had immediate repercussions with simple website defacements by minor actors ideologically aligned with Iran and concerns of cyber escalations. |
||||
| 2020-12-21 04:08:43 | Cybereason and Oracle Team Up for Security at Scale from the Endpoint to the Cloud (lien direct) |
 The sudden transition to remote work brought on by the pandemic resulted in many companies ensuring employees had the necessary tools to work remotely. However, that left little focus on the rising security risks that come with home networks and endpoints.
The sudden transition to remote work brought on by the pandemic resulted in many companies ensuring employees had the necessary tools to work remotely. However, that left little focus on the rising security risks that come with home networks and endpoints. |
||||
| 2020-12-18 18:16:30 | Impact of XDR on the Modern SOC: New ESG Report (lien direct) |
 As we hurtle towards the end of 2020, the only constant we can come to expect is change itself. We're pressed on two sides: our corporate IT environments continue to change, and attackers are more persistent and explosive than ever. While it is possible to secure a modern, distributed, multi-cloud environment, it feels out of reach for most security teams. Between data lake management, detection and rules tuning, and repetitive response actions, it's challenging to architect, build, and maintain -- and of course prove that it's making the business safer.
As we hurtle towards the end of 2020, the only constant we can come to expect is change itself. We're pressed on two sides: our corporate IT environments continue to change, and attackers are more persistent and explosive than ever. While it is possible to secure a modern, distributed, multi-cloud environment, it feels out of reach for most security teams. Between data lake management, detection and rules tuning, and repetitive response actions, it's challenging to architect, build, and maintain -- and of course prove that it's making the business safer. |
||||
| 2020-12-15 18:11:05 | Molerats APT: New Malware and Techniques in Middle East Espionage Campaign (lien direct) |
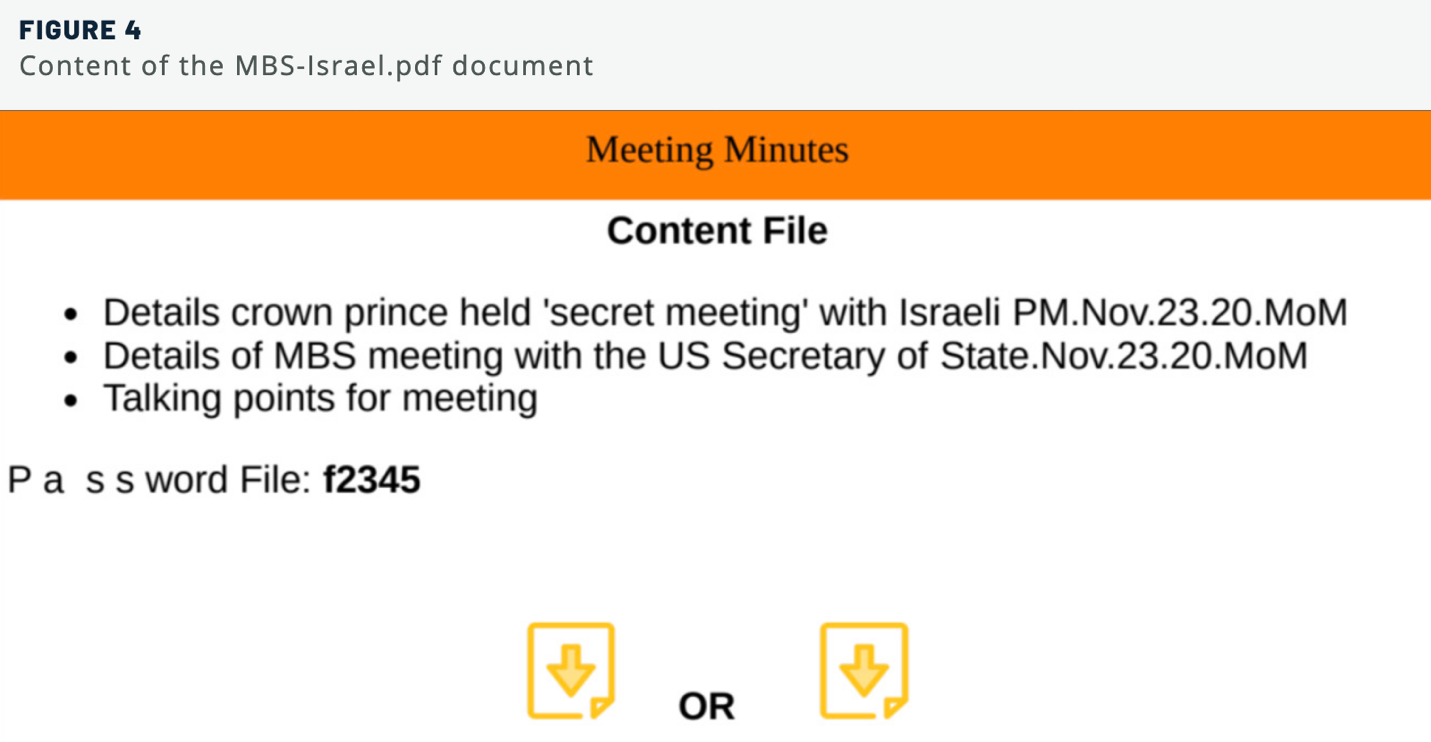 Security researchers observed a politically motivated APT called “Molerats” using three new malware variants to conduct espionage in the Middle East.
Security researchers observed a politically motivated APT called “Molerats” using three new malware variants to conduct espionage in the Middle East. |
Malware | |||
| 2020-12-14 21:47:12 | The SolarWinds Supply Chain Attack and the Limits of Cyber Hygiene (lien direct) |
 By now, you've probably heard: On December 13, Reuters reported that malicious actors had gone after both the U.S. Department of Treasury and the U.S. Department of Commerce. The National Security Council met at the White House on December 12 to talk things over. A day later, U.S. officials indicated that they had asked CISA and the FBI to look into what had happened.
By now, you've probably heard: On December 13, Reuters reported that malicious actors had gone after both the U.S. Department of Treasury and the U.S. Department of Commerce. The National Security Council met at the White House on December 12 to talk things over. A day later, U.S. officials indicated that they had asked CISA and the FBI to look into what had happened. |
||||
| 2020-12-14 14:30:00 | Ever Evolving: Jake Williams on Running an Infosec Consultancy Remotely (lien direct) |
 We spent some time with Jake Williams - founder and President at Rendition Infosec and SANS Instructor - discusses some of the challenges in remotely running a successful infosec consultancy - check it out...
We spent some time with Jake Williams - founder and President at Rendition Infosec and SANS Instructor - discusses some of the challenges in remotely running a successful infosec consultancy - check it out... |
||||
| 2020-12-10 16:00:31 | Cybereason vs. Ryuk Ransomware (lien direct) |
 Ryuk ransomware has been infecting victims since around 2018, and is believed to be based on the source code of Hermes ransomware, which was sold on an internet hacking forum back in 2017. Since its inception, Ryuk has been used to target large organizations to great effect, having accumulated as much as $61.26 million (as of Feb 2020) in ransom payments according to federal investigations.
Ryuk ransomware has been infecting victims since around 2018, and is believed to be based on the source code of Hermes ransomware, which was sold on an internet hacking forum back in 2017. Since its inception, Ryuk has been used to target large organizations to great effect, having accumulated as much as $61.26 million (as of Feb 2020) in ransom payments according to federal investigations. |
Ransomware | |||
| 2020-12-09 02:00:00 | New Malware Arsenal Abusing Cloud Platforms in Middle East Espionage Campaign (lien direct) |
 The Cybereason Nocturnus Team has identified an active espionage campaign employing three previously unidentified malware variants that use Facebook, Dropbox, Google Docs and Simplenote for command & control and the exfiltration of data from targets across the Middle East. The full report can be downloaded here (ungated).
The Cybereason Nocturnus Team has identified an active espionage campaign employing three previously unidentified malware variants that use Facebook, Dropbox, Google Docs and Simplenote for command & control and the exfiltration of data from targets across the Middle East. The full report can be downloaded here (ungated). |
Malware | |||
| 2020-12-07 20:46:46 | Ever Evolving: Katie Nickels on Incident Response in a Remote World (lien direct) |
 We spent some time with Katie Nickels - current Director of Intelligence at Red Canary and formerly MITRE ATT&CK Threat Intelligence Lead - to discuss applied threat intelligence, prioritizing threats for impact, and working incident response in remote environments - check it out...
We spent some time with Katie Nickels - current Director of Intelligence at Red Canary and formerly MITRE ATT&CK Threat Intelligence Lead - to discuss applied threat intelligence, prioritizing threats for impact, and working incident response in remote environments - check it out... |
Threat Guideline | APT 15 | ||
| 2020-12-04 18:23:59 | Is XDR the Next Silver Bullet? (lien direct) |
 Join us for an hour-long panel on the intricacies of XDR and how it will affect the security industry. Learn what XDR is, specific use cases, and how security practitioners can easily integrate this new technology into their security stack.
Join us for an hour-long panel on the intricacies of XDR and how it will affect the security industry. Learn what XDR is, specific use cases, and how security practitioners can easily integrate this new technology into their security stack. |
||||
| 2020-12-04 10:00:00 | Meet the League of Defenders (lien direct) |
 When I chose a career in B2B marketing I'm not sure I ever imagined I'd be a part of a team that spent weeks architecting intricate owl wings and razor-sharp talons, but here we are. While 2020 has been filled with many challenging surprises, this was a great one for me. And because we are driven by the mission of defending together, today we released a video of what it took to bring our new league of animated owls to life. But first, some history of the owl + Cybereason.
When I chose a career in B2B marketing I'm not sure I ever imagined I'd be a part of a team that spent weeks architecting intricate owl wings and razor-sharp talons, but here we are. While 2020 has been filled with many challenging surprises, this was a great one for me. And because we are driven by the mission of defending together, today we released a video of what it took to bring our new league of animated owls to life. But first, some history of the owl + Cybereason. |
||||
| 2020-12-02 14:30:00 | Ensuring Digital Safety and Security This Holiday Season (lien direct) |
 In mid-2020, the Cybereason Research Team detected an active campaign that targeted Brazilian customers of MercadoLivre, one of the largest e-commerce platforms in Latin America.
In mid-2020, the Cybereason Research Team detected an active campaign that targeted Brazilian customers of MercadoLivre, one of the largest e-commerce platforms in Latin America. |
||||
| 2020-11-30 14:30:00 | Ever Evolving: Rachel Tobac Talks Social Engineering (lien direct) |
 We spent some time with Rachel Tobac discussing techniques, awareness and training for organizations seeking to limit the risk from one of the most difficult security threats to counter - social engineering attacks - check it out...
We spent some time with Rachel Tobac discussing techniques, awareness and training for organizations seeking to limit the risk from one of the most difficult security threats to counter - social engineering attacks - check it out... |
||||
| 2020-11-26 01:51:59 | Cybereason vs. Egregor Ransomware (lien direct) |
 Research by: Lior Rochberger
Research by: Lior Rochberger |
Ransomware |
To see everything:
Our RSS (filtrered)
