What's new arround internet
| Src | Date (GMT) | Titre | Description | Tags | Stories | Notes |
| 2023-10-17 19:16:13 | Alerte zéro-jour: les systèmes 10K Cisco IOS XE sont désormais compromis Zero-Day Alert: 10K Cisco IOS XE Systems Now Compromised (lien direct) |
Un jour après Cisco a divulgué CVE-2023-20198 CVE-2023-20198, il reste non corrigé, et un fournisseur dit qu'un scan shodan affiche au moins 10 000 appareils Cisco avec un implant pour l'exécution de code arbitraire sur eux.Le vendeur a quant à lui mis à jour l'avis avec plus d'étapes d'atténuation.
Just a day after Cisco disclosed CVE-2023-20198, it remains unpatched, and one vendor says a Shodan scan shows at least 10,000 Cisco devices with an implant for arbitrary code execution on them. The vendor meanwhile has updated the advisory with more mitigation steps. |
Threat | ★★★ | ||
| 2023-10-17 17:52:39 | Mandia: la Chine remplace la Russie comme cyber-menace supérieure Mandia: China replaces Russia as top cyber threat (lien direct) |
Selon Kevin Mandia.
>Beijing\'s growing sophistication in cyberspace is making China an increasingly potent adversary, according to Kevin Mandia. |
Threat | ★★ | ||
| 2023-10-17 16:47:08 | Capacités essentielles de CTI pour les opérations de SOC efficaces Essential CTI Capabilities for Effective SOC Operations (lien direct) |
> Dans le paysage des menaces en évolution dynamique de l'ère numérique, les organisations doivent contrecarrer le cyber sophistiqué ...
>In the dynamically evolving threat landscape of the digital age, organizations must thwart sophisticated cyber... |
Threat | ★★ | ||
| 2023-10-17 15:47:00 | Explorer le domaine de l'IA génératrice malveillante: un nouveau défi de sécurité numérique Exploring the Realm of Malicious Generative AI: A New Digital Security Challenge (lien direct) |
Récemment, le paysage de la cybersécurité a été confronté à une nouvelle réalité intimidante & # 8211;La montée en puissance de l'IA générative malveillante, comme la fraude et le ver.Ces créations voyous, cachées dans les coins sombres d'Internet, constituent une menace distinctive pour le monde de la sécurité numérique.Dans cet article, nous examinerons la nature de la fraude générative de l'IA, analyserons la messagerie entourant ces créations,
Recently, the cybersecurity landscape has been confronted with a daunting new reality – the rise of malicious Generative AI, like FraudGPT and WormGPT. These rogue creations, lurking in the dark corners of the internet, pose a distinctive threat to the world of digital security. In this article, we will look at the nature of Generative AI fraud, analyze the messaging surrounding these creations, |
Threat | ★★ | ||
| 2023-10-17 15:30:00 | Fausses mises à jour du navigateur utilisées dans la distribution de logiciels malveillants Fake Browser Updates Used in Malware Distribution (lien direct) |
Proofpoint a identifié au moins quatre grappes de menaces distinctes
Proofpoint have identified at least four distinct threat clusters |
Malware Threat | ★★ | ||
| 2023-10-17 13:18:04 | Backbox présente le gestionnaire de vulnérabilité du réseau BackBox Introduces Network Vulnerability Manager (lien direct) |
Backbox présente le gestionnaire de vulnérabilité du réseau, devenant la première plate-forme à offrir une intégration approfondie de l'automatisation du réseau avec la gestion de la vulnérabilité pour les équipes de réseau
La plate-forme d'automatisation du réseau de backbox ferme la boucle entre les stocks dynamiques, la gestion de la vulnérabilité, l'intelligence des menaces pour les pare-feu et autres périphériques de réseau et de sécurité, et les mises à niveau automatisées du système d'exploitation.
-
revues de produits
BackBox Introduces Network Vulnerability Manager, becoming the First Platform to Offer Deep Integration of Network Automation with Vulnerability Management for Network Teams The BackBox Network Automation Platform closes the loop between dynamic inventory, vulnerability management, threat intelligence for firewalls and other network and security devices, and automated OS upgrades. - Product Reviews |
Vulnerability Threat | ★★ | ||
| 2023-10-17 13:00:41 | Menace la chasse pour trouver les bonnes choses Threat Hunting to Find the Good Stuff (lien direct) |
> Peter Havens de Cortex Product Marketing s'assoit avec Leeroy Perera, ingénieur de sécurité du personnel pour discuter de la pratique de la chasse aux menaces et de la façon dont nous l'appliquons dans notre Soc.
>Peter Havens from Cortex product marketing sits down with Leeroy Perera, staff security engineer to discuss the practice of threat hunting and how we apply it in our SOC. |
Threat | ★★ | ||
| 2023-10-17 12:00:00 | Le rôle essentiel de l'intelligence cyber-menace dans le paysage des ics / oc de la menace d'aujourd'hui The Critical Role of Cyber Threat Intelligence in Today\\'s ICS/OT Threat Landscape (lien direct) |
> La menace de prédation impose une pression aux organismes pour développer des instincts qui aident à identifier les menaces, utiliser des stratégies efficaces pour prévenir ...
Le post le rôle essentiel de l'intelligence de la cyber-menace dans le paysage ics / ot de la menace de aujourd'hui est apparu pour la première fois sur dragos .
>The threat of predation imposes pressure on organisms to develop instincts that help identify threats, employ effective strategies to prevent... The post The Critical Role of Cyber Threat Intelligence in Today\'s ICS/OT Threat Landscape first appeared on Dragos. |
Threat | ★★★ | ||
| 2023-10-17 11:16:00 | CERT-UA Rapports: 11 fournisseurs de télécommunications ukrainiens frappés par des cyberattaques CERT-UA Reports: 11 Ukrainian Telecom Providers Hit by Cyberattacks (lien direct) |
L'équipe d'intervention d'urgence informatique d'Ukraine (CERT-UA) a révélé que les acteurs de la menace "interféraient" avec au moins 11 fournisseurs de services de télécommunication dans le pays entre mai et septembre 2023.
L'agence suit l'activité sous le nom de l'UAC-0165, indiquant que les intrusions ont conduit à des interruptions de service pour les clients.
Le point de départ des attaques est une phase de reconnaissance en
The Computer Emergency Response Team of Ukraine (CERT-UA) has revealed that threat actors "interfered" with at least 11 telecommunication service providers in the country between May and September 2023. The agency is tracking the activity under the name UAC-0165, stating the intrusions led to service interruptions for customers. The starting point of the attacks is a reconnaissance phase in |
Threat | ★★★ | ||
| 2023-10-17 11:11:43 | Vulnérabilité de sécurité du système de vote électronique de Suisse \\ Security Vulnerability of Switzerland\\'s E-Voting System (lien direct) |
Le vote en ligne n'est pas en sécurité, point final.Cela n'empêche pas les organisations et les gouvernements de l'utiliser.(Et pour les élections à faible enjeux, il est probablement bien.Ed Appel explique pourquoi et c'est et c'est et c'est pourquoi et c'est# 8217; est une mauvaise idée:
L'année dernière, j'ai publié Une série en 5 parties sur le système de vote électronique de Suisse \\ .Comme tout système de vote sur Internet, il a des vulnérabilités de sécurité inhérentes: s'il y a des initiés malveillants, ils peuvent corrompre le nombre de votes;Et si des milliers d'ordinateurs d'électeurs sont piratés par des logiciels malveillants, les logiciels malveillants peuvent modifier les votes lorsqu'ils sont transmis.La Suisse & # 8220; résout & # 8221;Le problème des initiés malveillants dans leur bureau d'impression en déclarant officiellement qu'ils ne considéraient pas ce modèle de menace dans leur évaluation de la cybersécurité ...
Online voting is insecure, period. This doesn’t stop organizations and governments from using it. (And for low-stakes elections, it’s probably fine.) Switzerland—not low stakes—uses online voting for national elections. Ed Appel explains why it’s a bad idea: Last year, I published a 5-part series about Switzerland\'s e-voting system. Like any internet voting system, it has inherent security vulnerabilities: if there are malicious insiders, they can corrupt the vote count; and if thousands of voters\' computers are hacked by malware, the malware can change votes as they are transmitted. Switzerland “solves” the problem of malicious insiders in their printing office by officially declaring that they won\'t consider that threat model in their cybersecurity assessment... |
Malware Vulnerability Threat | ★★ | ||
| 2023-10-17 09:42:17 | Etude Netskope Threat Labs : le plus haut pourcentage d\'activités cybercriminelles provient de Russie, tandis que la Chine affiche les motivations géopolitiques les plus fortes (lien direct) | Etude Netskope Threat Labs : le plus haut pourcentage d'activités cybercriminelles provient de Russie, tandis que la Chine affiche les motivations géopolitiques les plus fortes Cette étude révèle les techniques et les facteurs de motivation les plus couramment employés par les cybercriminels depuis le début de l'année 2023. - Investigations | Threat Studies | ★★★★ | ||
| 2023-10-17 09:08:51 | Kimsuky Threat Group utilise RDP pour contrôler les systèmes infectés Kimsuky Threat Group Uses RDP to Control Infected Systems (lien direct) |
Kimsuky, un groupe de menaces connu pour être soutenu par la Corée du Nord, est actif depuis 2013. Au début, ils ont attaqué les instituts de recherche liés à la Corée du Nord en Corée du Sud avant d'attaquer une agence d'énergie sud-coréenne en 2014. D'autres pays sont également devenus des cibles de leur attaque depuis 2017. [1] Le groupe lance généralement des attaques de phishing de lance contre la défense nationale, diplomatique diplomatique,, et les secteurs universitaires, les industries de la défense et des médias, ainsi que des organisations nationales.Leur objectif est d'exfiltrer les informations et la technologie internes ...
Kimsuky, a threat group known to be supported by North Korea, has been active since 2013. At first, they attacked North Korea-related research institutes in South Korea before attacking a South Korean energy agency in 2014. Other countries have also become targets of their attack since 2017. [1] The group usually launches spear phishing attacks on the national defense, diplomatic, and academic sectors, defense and media industries, as well as national organizations. Their goal is to exfiltrate internal information and technology... |
Threat | APT 43 | ★★★ | |
| 2023-10-17 05:00:21 | Êtes-vous sûr que votre navigateur est à jour?Le paysage actuel des fausses mises à jour du navigateur Are You Sure Your Browser is Up to Date? The Current Landscape of Fake Browser Updates (lien direct) |
Key Takeaways Proofpoint is tracking multiple different threat clusters that use similar themes related to fake browser updates. Fake browser updates abuse end user trust with compromised websites and a lure customized to the user\'s browser to legitimize the update and fool users into clicking. Threat actors do not send emails to share the compromised websites. The threat is only in the browser and can be initiated by a click from a legitimate and expected email, social media site, search engine query, or even just navigating to the compromised site. The different campaigns use similar lures, but different payloads. It is important to identify which campaign and malware cluster the threat belongs to help guide defender response. Overview Proofpoint is currently tracking at least four distinct threat clusters that use fake browser updates to distribute malware. Fake browser updates refer to compromised websites that display what appears to be a notification from the browser developer such as Chrome, Firefox, or Edge, informing them that their browser software needs to be updated. When a user clicks on the link, they do not download a legitimate browser update but rather harmful malware. Based on our research, TA569 has used fake browser updates for over five years to deliver SocGholish malware, but recently other threat actors have been copying the lure theme. Each threat actor uses their own methods to deliver the lure and payload, but the theme takes advantage of the same social engineering tactics. The use of fake browser updates is unique because it abuses the trust end users place in both their browser and the known sites that they visit. Threat actors that control the fake browser updates use JavaScript or HTML injected code that directs traffic to a domain they control, which can potentially overwrite the webpage with a browser update lure specific to the web browser that the potential victim uses. A malicious payload will then automatically download, or the user will receive a prompt to download a “browser update,” which will deliver the payload. Fake browser update lure and effectiveness The fake browser update lures are effective because threat actors are using an end-user\'s security training against them. In security awareness training, users are told to only accept updates or click on links from known and trusted sites, or individuals, and to verify sites are legitimate. The fake browser updates abuse this training because they compromise trusted sites and use JavaScript requests to quietly make checks in the background and overwrite the existing, website with a browser update lure. To an end user, it still appears to be the same website they were intending to visit and is now asking them to update their browser. Proofpoint has not identified threat actors directly sending emails containing malicious links, but, due to the nature of the threat, compromised URLs are observed in email traffic in a variety of ways. They are seen in normal email traffic by regular end users who are unaware of the compromised websites, in monitoring emails such as Google alerts, or in mass automated email campaigns like those distributing newsletters. This creates a situation where these emails are considered to be malicious during the time the site is compromised. Organizations should not treat the fake browser update threats as only an email problem, as end users could visit the site from another source, such as a search engine, social media site, or simply navigate to the site directly and receive the lure and potentially download the malicious payload. Each campaign uniquely filters traffic to hide from researchers and delay discovery, but all the methods are effective at filtering. While this may reduce the potential spread of malicious payloads, it enables actors to maintain their access to the compromised sites for longer periods of time. This can complicate the response, because with the multiple campaigns and changing payloads, responders must take time to | Malware Tool Threat Studies | ★★★★ | ||
| 2023-10-16 21:02:00 | MALICIEUX \\ 'AirTrike Alert \\' App cible les Israéliens Malicious \\'Airstrike Alert\\' App Targets Israelis (lien direct) |
Une version usurpée de l'application RedAlert populaire recueille des données d'utilisateurs sensibles sur les citoyens israéliens, y compris les contacts, les journaux d'appels, les détails du compte SMS, etc.
A spoofed version of the popular RedAlert app collects sensitive user data on Israeli citizens, including contacts, call logs, SMS account details, and more. |
Threat | ★★ | ||
| 2023-10-16 20:44:52 | Le bug de Cisco Zero-Day critique et non corrigé est sous exploitation active Critical, Unpatched Cisco Zero-Day Bug Is Under Active Exploit (lien direct) |
Aucun patch ou solution de contournement n'est actuellement disponible pour la défaut de gravité maximale, ce qui permet aux attaquants d'obtenir un privilège d'administrateur complet sur les appareils affectés à distance et sans authentification.
No patch or workaround is currently available for the maximum severity flaw, which allows attackers to gain complete administrator privilege on affected devices remotely and without authentication. |
Threat | ★★ | ||
| 2023-10-16 19:25:00 | Des pirates pro-russes exploitant la récente vulnérabilité de Winrar dans la nouvelle campagne Pro-Russian Hackers Exploiting Recent WinRAR Vulnerability in New Campaign (lien direct) |
Les groupes de piratage pro-russes ont exploité une vulnérabilité de sécurité récemment divulguée dans le service public d'archivage Winrar dans le cadre d'une campagne de phishing conçue pour récolter des références à partir de systèmes compromis.
"L'attaque implique l'utilisation de fichiers d'archives malveillants qui exploitent la vulnérabilité récemment découverte affectant les versions de logiciels de compression Winrar avant 6.23 et tracées en tant que
Pro-Russian hacking groups have exploited a recently disclosed security vulnerability in the WinRAR archiving utility as part of a phishing campaign designed to harvest credentials from compromised systems. "The attack involves the use of malicious archive files that exploit the recently discovered vulnerability affecting the WinRAR compression software versions prior to 6.23 and traced as |
Vulnerability Threat | ★★ | ||
| 2023-10-16 18:21:03 | \\ 'Romcom \\' Cyber Campagne cible les femmes dirigeants politiques \\'RomCom\\' Cyber Campaign Targets Women Political Leaders (lien direct) |
Un groupe de menaces connu sous le nom de "Void Rabisu" a utilisé un site Web de Sommet des dirigeants politiques usurpés pour cibler les participants à la conférence réelle avec des logiciels malveillants d'espionnage.
A threat group known as "Void Rabisu" used a spoofed Women Political Leaders Summit website to target attendees to the actual conference with espionage malware. |
Threat Conference | ★★ | ||
| 2023-10-16 17:42:53 | Déverrouiller la puissance de Zero avec NetSkope et Okta Unlocking The Power of Zero with Netskope and Okta (lien direct) |
> Nous devons changer & # 160;La façon dont nous, en tant que praticiens de la sécurité, brise les obstacles à la sensibilisation à la menace collective à travers les points de contact de l'identité au sein de la cybersécurité.Il est devenu impératif que nous gagnions la capacité d'évaluer en continu le risque des utilisateurs avec des actions de réponse automatique - un passage à une défense d'identité unifiée et contente. & # 160;Lorsque nous pensons aux tendances actuelles, que cela fonctionne à partir de [& # 8230;]
>We need to shift how we as security practitioners break the barriers for collective threat awareness across identity touchpoints within cybersecurity. It\'s become imperative that we gain the ability to continuously assess user risk with automatic response actions-a shift towards a unified, contextually-driven identity defense. When we think about current trends, whether that\'s working from […] |
Threat | ★★ | ||
| 2023-10-16 17:29:48 | Discord toujours un foyer d'activité malveillante - maintenant les aptes rejoignent le plaisir Discord still a hotbed of malware activity - Now APTs join the fun (lien direct) |
Discord continue d'être un terrain reproducteur pour une activité malveillante par les pirates et maintenant des groupes APT, avec elle couramment utilisée pour distribuer des logiciels malveillants, exfilter les données et ciblé par les acteurs de la menace pour voler des jetons d'authentification.[...]
Discord continues to be a breeding ground for malicious activity by hackers and now APT groups, with it commonly used to distribute malware, exfiltrate data, and targeted by threat actors to steal authentication tokens. [...] |
Malware Threat | ★★★ | ||
| 2023-10-16 15:30:00 | Ransomware cible les serveurs WS_FTP non corrigés Ransomware Targets Unpatched WS_FTP Servers (lien direct) |
Les acteurs de la menace ont tenté d'escalader les privilèges en utilisant l'outil open source Godpotato
The threat actors attempted to escalate privileges using the open-source GodPotato tool |
Ransomware Tool Threat | ★★ | ||
| 2023-10-16 14:04:05 | 16 octobre & # 8211;Rapport de renseignement sur les menaces 16th October – Threat Intelligence Report (lien direct) |
> Pour les dernières découvertes de cyber-recherche pour la semaine du 9 octobre, veuillez télécharger notre bulletin Threat_Intelligence.Les meilleurs attaques et violations Gang de ransomware de verrouillage ont revendiqué la responsabilité d'une prétendue attaque contre le revendeur de produits et services informatiques de plusieurs milliards de dollars CDW.Le gang a demandé une rançon de 80 millions de dollars et a menacé de publier des données volées, censées [& # 8230;]
>For the latest discoveries in cyber research for the week of 9th October, please download our Threat_Intelligence Bulletin. TOP ATTACKS AND BREACHES LockBit ransomware gang has claimed responsibility for an alleged attack on the multibillion-dollar IT products and services reseller CDW. The gang has demanded $80M ransom and threatened to release stolen data, said to […] |
Ransomware Threat | ★★ | ||
| 2023-10-16 13:00:58 | Présentation de Playblocks Horizon Point Point: la plate-forme d'automatisation et de collaboration ultime Introducing Check Point Horizon Playblocks: The Ultimate Security Automation and Collaboration Platform (lien direct) |
> En 2023, les CISO prièrent la priorité à la mise en œuvre de l'automatisation dans leurs mesures de cybersécurité, selon le Forbes Technology Council.L'automatisation peut réduire considérablement la charge de travail des centres d'opérations de sécurité (SOC) et améliorer la sécurité globale.Cependant, pour lutter efficacement contre les cyber-menaces, la collaboration entre les produits, les personnes et les processus est crucial.Les équipes qui collaborent surpassent celles où chaque membre travaille seul.La collaboration à la recherche et à d'autres initiatives mène à de meilleures découvertes et à des percées plus rapides.Ce principe peut également être appliqué au paysage de menace d'une organisation.Le risque de silos de sécurité même avec des outils de sécurité sophistiqués déployés, la collaboration peut déverrouiller la prochaine [& # 8230;]
>In 2023, CISOs will prioritize the implementation of automation in their cybersecurity measures, according to the Forbes Technology Council. Automation can significantly reduce the workload of Security Operations Centers (SOCs) and enhance overall security. However, to effectively combat cyber threats, collaboration among products, people, and processes is crucial. Teams that collaborate out-perform those where each member works on their own. Collaborating on research and other initiatives leads to better findings and faster breakthroughs. This principle can also be applied to an organization\'s threat landscape. The Risk of Security Silos Even with sophisticated security tools deployed, collaboration can unlock the next […] |
Tool Threat | ★★ | ||
| 2023-10-16 12:36:55 | SecurityScorecard grève des renseignements sur les menaces SecurityScorecard STRIKE Threat Intelligence (lien direct) |
Après le déclenchement de la guerre entre Israël et le Hamas le 7 octobre 2023, une grande variété d'acteurs de menaces ont commencé à revendiquer la responsabilité des cyberattaques contre les entités liées aux deux côtés du conflit.
-
mise à jour malveillant
Following the outbreak of war between Israel and Hamas on October 7, 2023, a wide variety of threat actors began claiming responsibility for cyberattacks against entities linked to both sides of the conflict. - Malware Update |
Threat | ★★ | ||
| 2023-10-16 11:30:00 | Le secteur des soins de santé a mis en garde contre le nouveau groupe de ransomwares Noescape Healthcare Sector Warned About New Ransomware Group NoEscape (lien direct) |
Le gouvernement américain a souligné les opérations du groupe Noescape, qui serait un changement de marque de l'acteur de menace russe Avaddon
The US government highlighted the operations of the NoEscape group, which is believed to be a rebrand of Russian threat actor Avaddon |
Ransomware Threat Medical | ★★ | ||
| 2023-10-16 10:29:00 | La chaîne intelligente de Binance \\ est exploitée dans la nouvelle campagne \\ 'EtherHiding \\' malware Binance\\'s Smart Chain Exploited in New \\'EtherHiding\\' Malware Campaign (lien direct) |
Des acteurs de menace ont été observés au service de code malveillant en utilisant des contrats de chaîne intelligente de Binance \\ de Binance (BSC) dans ce qui a été décrit comme le «niveau suivant de l'hébergement pare-balles».
La campagne, détectée il y a deux mois, a été nommée EtherHiding par Guardio Labs.
Le roman Twist marque la dernière itération d'une campagne en cours qui exploite des sites WordPress compromis pour servir sans méfiance
Threat actors have been observed serving malicious code by utilizing Binance\'s Smart Chain (BSC) contracts in what has been described as the "next level of bulletproof hosting." The campaign, detected two months ago, has been codenamed EtherHiding by Guardio Labs. The novel twist marks the latest iteration in an ongoing campaign that leverages compromised WordPress sites to serve unsuspecting |
Malware Threat | ★★ | ||
| 2023-10-16 10:00:00 | Renforcement de la cybersécurité: multiplication de force et efficacité de sécurité Strengthening Cybersecurity: Force multiplication and security efficiency (lien direct) |
In the ever-evolving landscape of cybersecurity, the battle between defenders and attackers has historically been marked by an asymmetrical relationship. Within the cybersecurity realm, asymmetry has characterized the relationship between those safeguarding digital assets and those seeking to exploit vulnerabilities. Even within this context, where attackers are typically at a resource disadvantage, data breaches have continued to rise year after year as cyber threats adapt and evolve and utilize asymmetric tactics to their advantage. These include technologies and tactics such as artificial intelligence (AI), and advanced social engineering tools. To effectively combat these threats, companies must rethink their security strategies, concentrating their scarce resources more efficiently and effectively through the concept of force multiplication. Asymmetrical threats, in the world of cybersecurity, can be summed up as the inherent disparity between adversaries and the tactics employed by the weaker party to neutralize the strengths of the stronger one. The utilization of AI and similar tools further erodes the perceived advantages that organizations believe they gain through increased spending on sophisticated security measures. Recent data from InfoSecurity Magazine, referencing the 2023 Checkpoint study, reveals a disconcerting trend: global cyberattacks increased by 7% between Q1 2022 and Q1 2023. While not significant at first blush, a deeper analysis reveals a more disturbing trend specifically that of the use of AI. AI\'s malicious deployment is exemplified in the following quote from their research: "...we have witnessed several sophisticated campaigns from cyber-criminals who are finding ways to weaponize legitimate tools for malicious gains." Furthermore, the report highlights: "Recent examples include using ChatGPT for code generation that can help less-skilled threat actors effortlessly launch cyberattacks." As threat actors continue to employ asymmetrical strategies to render organizations\' substantial and ever-increasing security investments less effective, organizations must adapt to address this evolving threat landscape. Arguably, one of the most effective methods to confront threat adaptation and asymmetric tactics is through the concept of force multiplication, which enhances relative effectiveness with fewer resources consumed thereby increasing the efficiency of the security dollar. Efficiency, in the context of cybersecurity, refers to achieving the greatest cumulative effect of cybersecurity efforts with the lowest possible expenditure of resources, including time, effort, and costs. While the concept of efficiency may seem straightforward, applying complex technological and human resources effectively and in an efficient manner in complex domains like security demands more than mere calculations. This subject has been studied, modeled, and debated within the military community for centuries. Military and combat efficiency, a domain with a long history of analysis, | Tool Vulnerability Threat Studies Prediction | ChatGPT | ★★★ | |
| 2023-10-16 09:55:21 | Les logiciels espions capturés comme applications d'alerte de fusée israéliennes Spyware Caught Masquerading as Israeli Rocket Alert Applications (lien direct) |
> Un acteur de menace cible les Israéliens avec des logiciels espions se faisant passer pour une application Android pour recevoir des alertes de fusée.
>A threat actor targets Israelis with spyware masquerading as an Android application for receiving rocket alerts. |
Threat | ★★ | ||
| 2023-10-16 09:31:32 | Clearfake: un nouveau venu dans les «fausses mises à jour» menace le paysage ClearFake: a newcomer to the “fake updates” threats landscape (lien direct) |
Clearfake est un nouveau framework JavaScript malveillant déployé sur des sites Web compromis pour fournir d'autres logiciels malveillants à l'aide de la technique de téléchargement.Ce blog vise à présenter une analyse technique du flux d'installation de Clearfake, les logiciels malveillants livrés par Clearfake, l'infrastructure C2 et les opportunités de suivi.
la publication Suivante clearfake: un newcomersaux & # 8220; fausses mises à jour & # 8221;Menaces Paysage est un article de blog Sekoia.io .
ClearFake is a new malicious JavaScript framework deployed on compromised websites to deliver further malware using the drive-by download technique. This blogpost aims at presenting a technical analysis of the ClearFake installation flow, the malware delivered by ClearFake, the C2 infrastructure and tracking opportunities. La publication suivante ClearFake: a newcomer to the “fake updates” threats landscape est un article de Sekoia.io Blog. |
Malware Threat | ★★★ | ||
| 2023-10-16 09:23:26 | Piraté, Shadow affirme l\'intégrité de ses " PC cloud " (lien direct) | Des tiers ont pu accéder à des données client de Shadow après une attaque de social engineering contre un employé. Quel en est le bilan ? | Threat Cloud | ★★★ | ||
| 2023-10-16 07:29:59 | Navigation du cyber-risque: ce qu'il faut rechercher dans la couverture de la cyber-assurance Navigating Cyber Risk: What to Look for in Cyber Insurance Coverage (lien direct) |
Modern threats like phishing, ransomware and data breaches cast a dark cloud over businesses across sectors. For most bad actors, the goal of an attack is financial. As Proofpoint noted in the 2023 State of the Phish report, 30% of businesses that endured a successful attack experienced a direct monetary loss, such as a fraudulent invoice, wire transfer or payroll redirection. That is an increase of 76% year over year. A cyber insurance policy can protect you from the financial losses caused by cybersecurity incidents and data breaches. And when businesses pair cyber insurance with the prowess of Proofpoint solutions, they can build a formidable defense strategy. In this blog, we\'ll go over some best practices for choosing and managing you cyber insurance policy so you can protect yourself from risk. Actions that cyber criminals monetize Our research for the latest State of the Phish report shows that the three most common consequences of a cyber attack are: Data breach (44%) Ransomware infection (43%) Account compromise (36%) Notably, cyber criminals can monetize all these actions. Most common results of successful phishing attacks. (Source: 2023 State of the Phish report from Proofpoint.) Just one cybersecurity incident can cost tens of thousands of dollars. So, it\'s easy to understand why insurers see these incidents as too costly to cover in their general liability policies. But with cyber insurance, your business has a tool to help manage risk. Why cyber insurance can be a vital financial safety net While firewalls and endpoint protections remain vital, the truth is that a level of residual risk always exists. No matter how fortified your security is, breaches can happen due to ingenious adversaries, human error or just unfortunate circumstances. This is where cyber insurance comes to the rescue. It is the safety net that catches your business when your defenses fall short. It can help you cover costs like ransomware payments, legal fees, and costs associated with crisis management and revenue loss. In the graphic below, we can see how often cyber insurance covered losses from ransomware attacks among those surveyed for our 2023 State of the Phish report. Nearly three-quarters (73%) of businesses with cyber insurance policies said their insurers paid at least some of their ransomware-related losses. (Source: 2023 State of the Phish report from Proofpoint.) Cyber insurance best practices Now that we\'ve covered why cyber insurance can be a vital financial safety net, let\'s look at some essential best practices for cyber insurance. These measures can help your business become more effective at managing cybersecurity risks. Find an expert and ask for support and guidance. Specialized brokers are your allies in the intricate world of cyber insurance. Insurers vary in risk appetite, claim acceptance rates and expertise. Brokers have an in-depth grasp of this landscape, and they will assess your options meticulously. They will help ensure that the policy you choose is the right fit for your industry, size, risk profile and more. Be prepared for a rigorous assessment. Today, insurers want more insight into your company\'s security protocols and controls before they issue a cyber insurance policy. So preparedness is key. Be ready to provide evidence, like external audits, penetration test results and compliance certifications to insurers. If you implement access controls that insurers deem vital, such as multifactor authentication (MFA) and privileged access management (PAM), it may help to reduce your premiums. Closely examine coverage scope. Coverage specifics vary globally. But you will find that most cyber insurance policies cover a portion of losses from ransomware attacks and expenses linked to crisis responses. You need to have a thorough understanding of the breach scenarios your policy does or does not cover. Take note of any exclusions. Also, be sure to scrutinize services like breach investigation support, legal | Ransomware Tool Threat Guideline Cloud | ★★★ | ||
| 2023-10-16 03:01:08 | Comprendre l'empreinte de la cybersécurité: techniques et stratégies Understanding Cybersecurity Footprinting: Techniques and Strategies (lien direct) |
L'empreinte, également connue sous le nom d'empreintes digitales, est une méthodologie utilisée par les testeurs de pénétration, les professionnels de la cybersécurité et même les acteurs de menace pour recueillir des informations sur une organisation cible afin d'identifier les vulnérabilités potentielles.L'empreinte est la première étape des tests de pénétration.Il implique la numérisation des ports ouverts, la cartographie des topologies du réseau et la collecte d'informations sur les hôtes, leurs systèmes d'exploitation, leurs adresses IP et leurs comptes d'utilisateurs.Ces données recueillies aident à générer un plan technique complet de l'organisation cible.En utilisant l'empreinte, les chercheurs en cybersécurité peuvent ...
Footprinting, also known as fingerprinting, is a methodology used by penetration testers, cybersecurity professionals, and even threat actors to gather information about a target organization to identify potential vulnerabilities. Footprinting is the first step in penetration testing. It involves scanning open ports, mapping network topologies, and collecting information about hosts, their operating systems, IP addresses, and user accounts. This gathered data helps to generate a comprehensive technical blueprint of the target organization. Using footprinting, cybersecurity researchers can... |
Threat | ★★★ | ||
| 2023-10-16 00:00:00 | Attention: Lumma Stealer distribué via Discord CDN Beware: Lumma Stealer Distributed via Discord CDN (lien direct) |
Ce blog explique comment les acteurs de menace abusent du réseau de livraison de contenu (CDN) de Discord \\ pour héberger et diffuser Lumma Stealer, et parle de capacités supplémentaires aux informations volant des logiciels malveillants.
This blog discusses how threat actors abuse Discord\'s content delivery network (CDN) to host and spread Lumma Stealer, and talks about added capabilities to the information stealing malware. |
Threat | ★★★ | ||
| 2023-10-13 20:01:00 | Nouvelle campagne de cyberattaque de Peapod ciblant les femmes dirigeantes politiques New PEAPOD Cyberattack Campaign Targeting Women Political Leaders (lien direct) |
Le personnel militaire de l'Union européenne et les dirigeants politiques travaillant sur les initiatives d'égalité des sexes sont devenus la cible d'une nouvelle campagne qui offre une version mise à jour de RomCom Rat appelé Peapod.
La société de cybersécurité Trend Micro a attribué les attaques à un acteur de menace qu'il suit sous le nom de vide Rabisu, également connu sous le nom de Storm-0978, Tropical Scorpius et UNC2596, et qui est également
European Union military personnel and political leaders working on gender equality initiatives have emerged as the target of a new campaign that delivers an updated version of RomCom RAT called PEAPOD. Cybersecurity firm Trend Micro attributed the attacks to a threat actor it tracks under the name Void Rabisu, which is also known as Storm-0978, Tropical Scorpius, and UNC2596, and is also |
Threat Prediction | ★★ | ||
| 2023-10-13 19:10:50 | Les périls des moteurs de recherche: une récente alerte d'escroquerie technologique The Perils of Search Engines: A Recent Tech Scam Alert (lien direct) |
Les moteurs de recherche comme Google sont devenus nos principaux navigateurs dans le vaste monde du ...
Search engines like Google have become our primary navigators in the vast world of the... |
Threat | ★★★ | ||
| 2023-10-13 17:23:00 | Les chercheurs dévoilent le nouvel ensemble d'outils de Todckat \\ Researchers Unveil ToddyCat\\'s New Set of Tools for Data Exfiltration (lien direct) |
L'acteur avancé de menace persistante (APT) connue sous le nom de Toddycat a été lié à un nouvel ensemble d'outils malveillants conçus pour l'exfiltration de données, offrant un aperçu plus profond de la tactique et des capacités de l'équipe de piratage.
Les résultats proviennent de Kaspersky, qui a d'abord mis en lumière l'adversaire l'année dernière, le liant aux attaques contre des entités de haut niveau en Europe et en Asie pour près de trois
The advanced persistent threat (APT) actor known as ToddyCat has been linked to a new set of malicious tools that are designed for data exfiltration, offering a deeper insight into the hacking crew\'s tactics and capabilities. The findings come from Kaspersky, which first shed light on the adversary last year, linking it to attacks against high-profile entities in Europe and Asia for nearly three |
Tool Threat | ★★ | ||
| 2023-10-13 13:15:11 | CVE-2023-29464 (lien direct) | FactoryTalk Linx, dans le Rockwell Automation PanelView Plus, permet à un acteur de menace non authentifié de lire les données de la mémoire via des paquets malveillants fabriqués.L'envoi d'une taille supérieure à la taille du tampon entraîne une fuite de données de la mémoire, ce qui entraîne une divulgation d'informations.Si la taille est suffisamment grande, elle fait que les communications sur le protocole industriel commune ne répondent pas à tout type de paquet, entraînant un déni de service à FactoryTalk Linx sur le protocole industriel commun.
FactoryTalk Linx, in the Rockwell Automation PanelView Plus, allows an unauthenticated threat actor to read data from memory via crafted malicious packets. Sending a size larger than the buffer size results in leakage of data from memory resulting in an information disclosure. If the size is large enough, it causes communications over the common industrial protocol to become unresponsive to any type of packet, resulting in a denial-of-service to FactoryTalk Linx over the common industrial protocol. |
Threat Industrial | |||
| 2023-10-13 11:15:00 | Mises à jour des produits de renseignement Mandiant Threat pour octobre 2023 Mandiant Threat Intelligence Product Updates for October 2023 (lien direct) |
mandiantIntelligence de menace a ajouté un certain nombre de fonctionnalités et capacités nouvelles et mises à jour, qui sont désormais disponibles dans l'aperçu public ou la disponibilité générale.Ces nouvelles capacités vous aident à gagner du temps et à mieux comprendre les menaces vous ciblant.
Aperçu public
Surveillance des informations d'identification compromises: Surveillez vos informations d'identification compromises qui peuvent avoir fui sur la toile profonde et sombre.Les capacités de surveillance des informations d'identification compromises dans Surveillance des menaces numériques peut vous alerter automatiquement si des comptes liés à votre organisation - les deux employés interneset les clients - ont
Mandiant Threat Intelligence has added a number of new and updated features and capabilities, which are now available in public preview or general availability. These new capabilities help you save time and gain more insight into the threats targeting you. Public Preview Compromised credentials monitoring: Monitor your compromised credentials that may have leaked on the deep and dark web. The compromised credentials monitoring capabilities in Digital Threat Monitoring can automatically alert you if any accounts linked to your organization - both internal employees and customers - have |
Threat | ★★★ | ||
| 2023-10-13 08:21:01 | Rapport d'analyse sur le Volgmer et Scout Malwares de Lazarus Analysis Report on Lazarus Threat Group\\'s Volgmer and Scout Malwares (lien direct) |
aperçu1.Analyse de la porte dérobée de Volgmer….1.1.Version précoce de Volgmer …… .. 1.1.1.Analyse des compte-gouttes Volgmer …… .. 1.1.2.Analyse de la porte dérobée de Volgmer….1.2.Version ultérieure de Volgmer …… .. 1.2.1.Analyse de Volgmer Backdoor2.Analyse du téléchargeur Scout….2.1.DIGNES (Volgmer, Scout)….2.2.Analyse du téléchargeur Scout …… .. 2.2.1.Scout Downloader v1 …… .. 2.2.2.Scout Downloader V23.Conclusion Table des matières Le groupe de menaces de Lazarus parrainé par l'État a des dossiers d'activité qui remontent à 2009. Au début, leurs activités étaient principalement axées sur ...
Overview1. Analysis of Volgmer Backdoor…. 1.1. Early Version of Volgmer…….. 1.1.1. Analysis of Volgmer Dropper…….. 1.1.2. Analysis of Volgmer Backdoor…. 1.2. Later Version of Volgmer…….. 1.2.1. Analysis of Volgmer Backdoor2. Analysis of Scout Downloader…. 2.1. Droppers (Volgmer, Scout)…. 2.2. Analysis of Scout Downloader…….. 2.2.1. Scout Downloader v1…….. 2.2.2. Scout Downloader v23. Conclusion Table of Contents The seemingly state-sponsored Lazarus threat group has records of activity that date back to 2009. In the early days, their activities were mostly focused on... |
Threat | APT 38 | ★★ | |
| 2023-10-13 03:47:17 | Une analyse d'une webcontent de safari iOS dans la fenêtre dans l'exploit de processus GPU An analysis of an in-the-wild iOS Safari WebContent to GPU Process exploit (lien direct) |
By Ian Beer
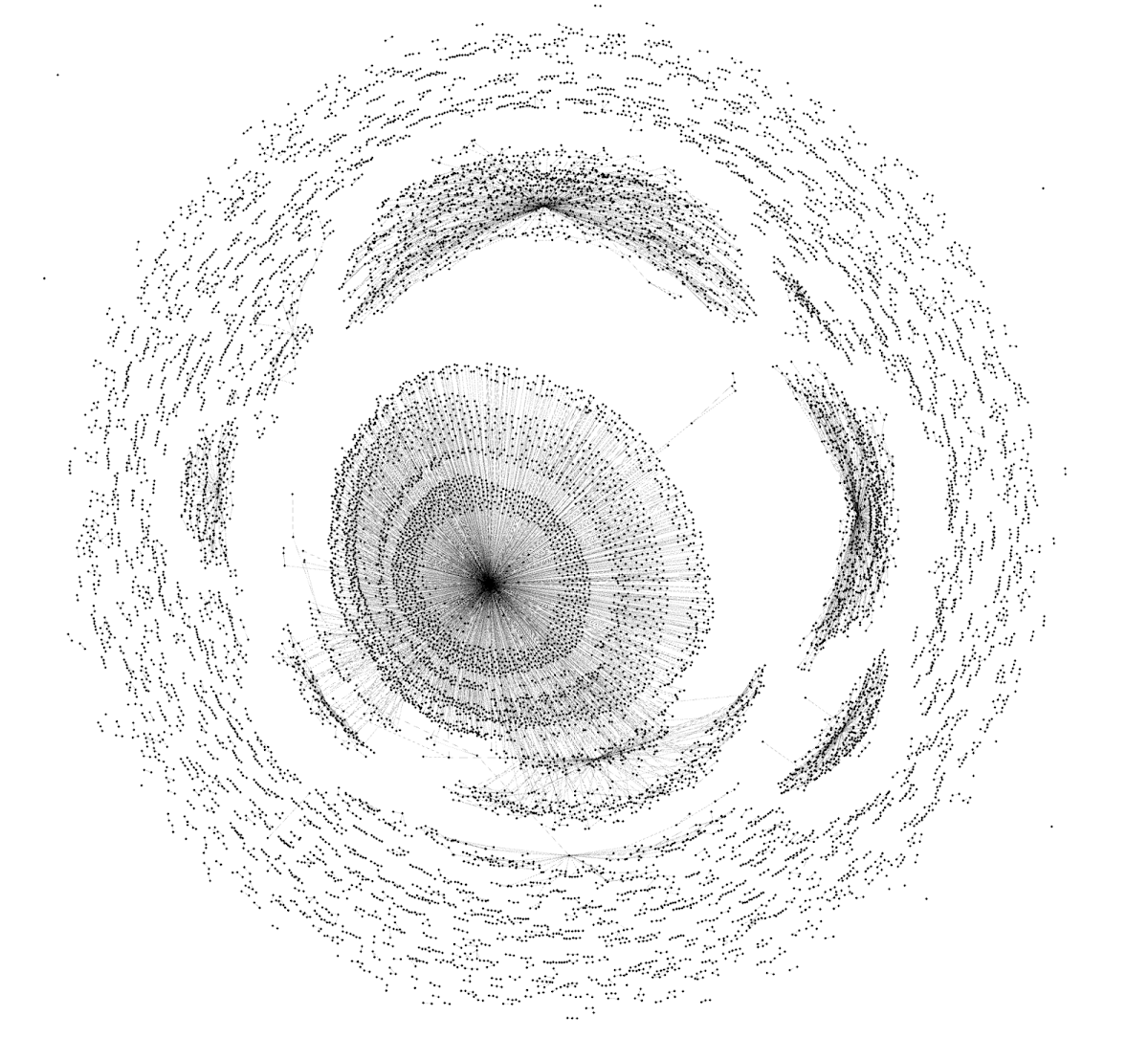 A graph representation of the sandbox escape NSExpression payload
In April this year Google\'s Threat Analysis Group, in collaboration with Amnesty International, discovered an in-the-wild iPhone zero-day exploit chain being used in targeted attacks delivered via malicious link. The chain was reported to Apple under a 7-day disclosure deadline and Apple released iOS 16.4.1 on April 7, 2023 fixing CVE-2023-28206 and CVE-2023-28205.
Over the last few years Apple has been hardening the Safari WebContent (or "renderer") process sandbox attack surface on iOS, recently removing the ability for the WebContent process to access GPU-related hardware directly. Access to graphics-related drivers is now brokered via a GPU process which runs in a separate sandbox.
Analysis of this in-the-wild exploit chain reveals the first known case of attackers exploiting the Safari IPC layer to "hop" from WebContent to the GPU process, adding an extra link to the exploit chain (CVE-2023-32409).
On the surface this is a positive sign: clear evidence that the renderer sandbox was hardened sufficiently that (in this isolated case at least) the attackers needed to bundle an additional, separate exploit. Project Zero has long advocated for attack-surface reduction as an effective tool for improving security and this would seem like a clear win for that approach.
On the other hand, upon deeper inspection, things aren\'t quite so rosy. Retroactively sandboxing code which was never designed with compartmentalization in mind is rarely simple to do effectively. In this case the exploit targeted a very basic buffer overflow vulnerability in unused IPC support code for a disabled feature - effectively new attack surface which exists only because of the introduced sandbox. A simple fuzzer targeting the IPC layer would likely have found this vulnerability in seconds.
A graph representation of the sandbox escape NSExpression payload
In April this year Google\'s Threat Analysis Group, in collaboration with Amnesty International, discovered an in-the-wild iPhone zero-day exploit chain being used in targeted attacks delivered via malicious link. The chain was reported to Apple under a 7-day disclosure deadline and Apple released iOS 16.4.1 on April 7, 2023 fixing CVE-2023-28206 and CVE-2023-28205.
Over the last few years Apple has been hardening the Safari WebContent (or "renderer") process sandbox attack surface on iOS, recently removing the ability for the WebContent process to access GPU-related hardware directly. Access to graphics-related drivers is now brokered via a GPU process which runs in a separate sandbox.
Analysis of this in-the-wild exploit chain reveals the first known case of attackers exploiting the Safari IPC layer to "hop" from WebContent to the GPU process, adding an extra link to the exploit chain (CVE-2023-32409).
On the surface this is a positive sign: clear evidence that the renderer sandbox was hardened sufficiently that (in this isolated case at least) the attackers needed to bundle an additional, separate exploit. Project Zero has long advocated for attack-surface reduction as an effective tool for improving security and this would seem like a clear win for that approach.
On the other hand, upon deeper inspection, things aren\'t quite so rosy. Retroactively sandboxing code which was never designed with compartmentalization in mind is rarely simple to do effectively. In this case the exploit targeted a very basic buffer overflow vulnerability in unused IPC support code for a disabled feature - effectively new attack surface which exists only because of the introduced sandbox. A simple fuzzer targeting the IPC layer would likely have found this vulnerability in seconds.
|
Tool Vulnerability Threat | ★★ | ||
| 2023-10-13 00:00:00 | Le vide Rabisu cible les dirigeants politiques féminines avec une nouvelle variante ROMCOM maximale Void Rabisu Targets Female Political Leaders with New Slimmed-Down ROMCOM Variant (lien direct) |
Près d'un an après que le vide Rabisu a déplacé son ciblage des attaques de ransomwares opportunistes en mettant l'accent sur le cyberespionnage, l'acteur de menace développe toujours son malware principal, la porte dérobée ROMCOM.
Almost a year after Void Rabisu shifted its targeting from opportunistic ransomware attacks with an emphasis on cyberespionage, the threat actor is still developing its main malware, the ROMCOM backdoor. |
Ransomware Threat | ★★ | ||
| 2023-10-12 23:15:11 | CVE-2023-36843 (lien direct) | Une manipulation inappropriée de la vulnérabilité des éléments spéciaux incohérents dans le module Junos Services Framework (JSF) des réseaux Juniper Networks Junos OS permet unL'attaquant basé sur le réseau non authentifié provoque un crash dans le moteur de transfert de paquets (PFE) et entraînant ainsi un déni de service (DOS).
En recevant un trafic SSL malformé, le PFE se bloque.Un redémarrage manuel sera nécessaire pour récupérer l'appareil.
Ce problème n'affecte que les appareils avec les réseaux Juniper Networks Advanced Menace Prevention (ATP) Cloud compatible avec des informations cryptées sur le trafic (configurées via & acirc; & euro; & tilde; Security-Metadata-Streaming Policy & acirc; & euro; & Trade;).
Ce problème affecte Juniper Networks Junos OS:
* Toutes les versions avant 20.4R3-S8, 20.4R3-S9;
* 21.1 version 21.1r1 et versions ultérieures;
* 21.2 Versions avant 21.2R3-S6;
* 21.3 Versions avant 21.3R3-S5;
* 21.4 versions avant 21.4R3-S5;
* 22.1 versions avant 22.1r3-s4;
* 22.2 Versions avant 22.2R3-S2;
* 22.3 versions avant 22.3r2-s2, 22.3r3;
* 22.4 Versions avant 22.4R2-S1, 22.4R3;
An Improper Handling of Inconsistent Special Elements vulnerability in the Junos Services Framework (jsf) module of Juniper Networks Junos OS allows an unauthenticated network based attacker to cause a crash in the Packet Forwarding Engine (pfe) and thereby resulting in a Denial of Service (DoS). Upon receiving malformed SSL traffic, the PFE crashes. A manual restart will be needed to recover the device. This issue only affects devices with Juniper Networks Advanced Threat Prevention (ATP) Cloud enabled with Encrypted Traffic Insights (configured via ‘security-metadata-streaming policy’). This issue affects Juniper Networks Junos OS: * All versions prior to 20.4R3-S8, 20.4R3-S9; * 21.1 version 21.1R1 and later versions; * 21.2 versions prior to 21.2R3-S6; * 21.3 versions prior to 21.3R3-S5; * 21.4 versions prior to 21.4R3-S5; * 22.1 versions prior to 22.1R3-S4; * 22.2 versions prior to 22.2R3-S2; * 22.3 versions prior to 22.3R2-S2, 22.3R3; * 22.4 versions prior to 22.4R2-S1, 22.4R3; |
Vulnerability Threat Cloud | |||
| 2023-10-12 19:23:20 | Connaissez-vous bien votre surface d'attaque?Cinq conseils pour réduire le risque d'exposition How Well Do You Know Your Attack Surface? Five Tips to Reduce the Risk of Exposure (lien direct) |
Dans un paysage numérique de plus en plus connecté, la sécurité de vos données et des actifs de votre organisation est plus critique que jamais.Selon le rapport de chasse aux menaces Crowdsstrike 2023, plus de 20% de toutes les intrusions interactives sont associées à l'exploitation des applications accessibles au public.À mesure que la surface d'attaque d'une organisation se développe et que les cyber-états prolifèrent, c'est [& # 8230;]
In an increasingly connected digital landscape, the security of your organization’s data and publicly facing assets is more critical than ever. According to the CrowdStrike 2023 Threat Hunting Report, more than 20% of all interactive intrusions are associated with the exploitation of public-facing applications. As an organization\'s attack surface expands and cyberthreats proliferate, it is […] |
Threat | ★★ | ||
| 2023-10-12 16:57:00 | (Déjà vu) Shellbot utilise des IPS hex ShellBot Uses Hex IPs to Evade Detection in Attacks on Linux SSH Servers (lien direct) |
Les acteurs de la menace derrière Shellbot tirent parti des adresses IP transformés en sa notation hexadécimale pour infiltrer les serveurs Linux SSH mal gérés et déployer les logiciels malveillants DDOS.
"Le flux global reste le même, mais l'URL de téléchargement utilisé par l'acteur de menace pour installer Shellbot est passé d'une adresse IP ordinaire à une valeur hexadécimale", le centre d'intervention d'urgence de sécurité Ahnlab (ASEC)
The threat actors behind ShellBot are leveraging IP addresses transformed into its hexadecimal notation to infiltrate poorly managed Linux SSH servers and deploy the DDoS malware. "The overall flow remains the same, but the download URL used by the threat actor to install ShellBot has changed from a regular IP address to a hexadecimal value," the AhnLab Security Emergency response Center (ASEC) |
Threat | ★★★ | ||
| 2023-10-12 15:59:00 | Microsoft Defender contrecarte à grande échelle Akira Ransomware Attack Microsoft Defender Thwarts Large-Scale Akira Ransomware Attack (lien direct) |
Microsoft a déclaré mercredi qu'une fonctionnalité de confinement des utilisateurs dans Microsoft Defender pour Endpoint a aidé à contrecarrer une "tentative de cryptage à grande échelle" effectuée par des acteurs de ransomware Akira ciblant une organisation industrielle inconnue début juin 2023.
L'équipe de renseignement sur les menaces du géant de la technologie suit l'opérateur en tant que Storm-1567.
Les dispositifs à levier d'attaque qui n'étaient pas à bord à Microsoft
Microsoft on Wednesday said that a user containment feature in Microsoft Defender for Endpoint helped thwart a "large-scale remote encryption attempt" made by Akira ransomware actors targeting an unknown industrial organization in early June 2023. The tech giant\'s threat intelligence team is tracking the operator as Storm-1567. The attack leveraged devices that were not onboarded to Microsoft |
Ransomware Threat Industrial | ★★★ | ||
| 2023-10-12 13:07:52 | Étude mondiale Sage : les PME ont du mal à suivre le rythme des cyber menaces (lien direct) | >La moitié des PME interrogées a subi un incident de sécurité au cours de l’année écoulée. Sage présente aujourd'hui son étude mondiale pour comprendre comment les PME perçoivent la cybersécurité et quels sont les principaux obstacles auxquels elles sont confrontées dans ce domaine. Tribune – D'après le rapport, les PME en France montrent une certaine […] The post Étude mondiale Sage : les PME ont du mal à suivre le rythme des cyber menaces first appeared on UnderNews. | Threat | ★★ | ||
| 2023-10-12 13:00:00 | Comment j'ai commencé: Attack Surface Management How I got started: Attack surface management (lien direct) |
> Alors que le paysage des menaces se multiplie en sophistication et complexité, de nouveaux rôles dans la cybersécurité se présentent plus fréquemment que jamais.Par exemple, attaquez la gestion de la surface.Ces professionnels de la cybersécurité sont responsables de l'identification, de la cartographie et de la sécurisation de tous les actifs numériques externes auxquels l'organisation possède ou est connectée.Cela inclut les serveurs, les domaines, les actifs cloud et tout [& # 8230;]
>As the threat landscape multiplies in sophistication and complexity, new roles in cybersecurity are presenting themselves more frequently than ever before. For example, attack surface management. These cybersecurity professionals are responsible for identifying, mapping and securing all external digital assets an organization owns or is connected to. This includes servers, domains, cloud assets and any […] |
Threat Cloud | ★★★ | ||
| 2023-10-12 11:33:00 | L'Agence finlandaise de renseignement avertit la Russie traitant la Finlande comme un pays hostile \\ '\\' Finnish intelligence agency warns Russia treating Finland as a \\'hostile country\\' (lien direct) |
 «Les relations entre la Finlande et la Russie se sont considérablement détériorées», a averti jeudi le service finlandais de sécurité et de renseignement (SUPO), à la suite d'un acte présumé de sabotage ciblant l'infrastructure maritime du pays.Dans un aperçu de la sécurité nationale , Supo a déclaré: «Bien que la menace de la menace deLes opérations de renseignement et d'influence contre les infrastructures critiques ont augmenté, un effet paralysant
«Les relations entre la Finlande et la Russie se sont considérablement détériorées», a averti jeudi le service finlandais de sécurité et de renseignement (SUPO), à la suite d'un acte présumé de sabotage ciblant l'infrastructure maritime du pays.Dans un aperçu de la sécurité nationale , Supo a déclaré: «Bien que la menace de la menace deLes opérations de renseignement et d'influence contre les infrastructures critiques ont augmenté, un effet paralysant
 “Relations between Finland and Russia have significantly deteriorated,” warned the Finnish Security and Intelligence Service (Supo) on Thursday, in the wake of a suspected act of sabotage targeting the country\'s maritime infrastructure. In a national security overview, Supo said: “While the threat of intelligence and influencing operations against critical infrastructure has increased, a crippling effect
“Relations between Finland and Russia have significantly deteriorated,” warned the Finnish Security and Intelligence Service (Supo) on Thursday, in the wake of a suspected act of sabotage targeting the country\'s maritime infrastructure. In a national security overview, Supo said: “While the threat of intelligence and influencing operations against critical infrastructure has increased, a crippling effect |
Threat | ★★ | ||
| 2023-10-12 10:00:00 | L'évolution des attaques de phishing The evolution of phishing attacks (lien direct) |
A practical guide to phishing and best practices to avoid falling victim. Introduction Over the past several years, remote and hybrid work has quickly gained popularity amongst those seeking a to reduce the amount of time on the road or an improved work/life balance. To accomplish this, users are often working from multiple devices, some of which may be company issued, but others may be privately owned. Cyberattackers have leveraged this trend to bypass traditional security controls using social engineering, with phishing attacks being a favored tactic. In fact, the FBI Internet Crime Report issued in 2022 reported phishing as the top reported internet crime for the past 5 years. Its ability to persuade individuals to divulge sensitive information to seemingly familiar contacts and companies over email and/or SMS text messages has resulted in significant data breaches, both personal and financial, across all industries. Mobile phishing, in particular, is quickly becoming a preferred attack vector among hackers seeking to use them as a jump point to gain access to proprietary data within a company’s network. This article provides an overview of the origins of phishing, its impact on businesses, the types of mobile phishing attacks hackers employ, and ways in which companies can best defend themselves against such attacks. The origins of phishing The belief among many in the cybersecurity industry is that phishing attacks first emerged in the mid-90s when dial-up was the only means of gaining access to the internet. Hackers posing as ISP administrators used fake screen names to establish credibility with the user, enabling them to “phish” for personal log-in data. Once successful, they were able to exploit the victim’s account by sending out phishing emails to other users in their contact list, with the goal of scoring free internet access or other financial gain. Awareness of phishing was still limited until May 2000 when Love Bug entered the picture. Love Bug, a highly effective and contagious virus designed to take advantage of the user’s psyche was unleashed in the Philippines, impacting an estimated 45 million Window PCs globally. Love Bug was sent via email with the subject line reading “ILOVEYOU”. The body of the message simply read “Kindly check the attached LOVELETTER coming from me”. Users who couldn’t resist opening the message unleashed a worm virus infecting and overwriting user’s files with copies of the virus. When the user opened the file, they would reinfect the system. Lovebug elevated phishing to a new level as it demonstrated the ability to target a user’s email mailing list for the purpose of spamming acquaintances thereby incentivizing the reader to open his/her email. This enabled the lovebug worm to infect computer systems and steal other user’s passwords providing the hacker the opportunity to log-in to other user accounts providing unlimited internet access. Since Love Bug, the basic concept and primary goal of phishing tactics has remained consistent, but the tactics and vectors have evolved. The window of opportunity has increased significantly for hackers with the increased use of social media (e.g., Linkedin, Twitter, Facebook). This provides more personal data to the hackers enabling them to exploit their targets with more sophisticated phishing tactics while avoiding detection. Phishing’s impact in the marketplace today Phishing attacks present a significant threat for organizations as their ability to capture proprietary business and financial data are both costly and time consuming for IT organizations to detect and remediate. Based on a | Ransomware Malware Tool Threat Prediction | ★★★ | ||
| 2023-10-12 09:27:20 | J'ai été frappé par les ransomwares-temps quoi?Étapes pour gérer les conséquences I\\'ve Been Hit by Ransomware-Now What? Steps for Dealing with the Aftermath (lien direct) |
The following is an excerpt from the Ransomware Survival Guide, our free handbook on preventing, managing and recovering from ransomware threats at every stage of the attack chain. This blog post provides general tips-it is not a substitute for professional cybersecurity and incident response services. The best ransomware strategy is to avoid it in the first place. But increasingly advanced attacks against the software supply chain and end users have shown that even the best-prepared companies can be caught out. Ransomware may not even be the first malware payload to infect your system, because many ransomware gangs now prefer to buy access to targets already infected with Trojans or loader malware. During an attack, you have short-term problems to resolve, like getting computers, phones and networks back online and dealing with ransom demands. But a panicked response won\'t help-and may make things worse. Here are some general steps you can take to contain the threat and start on the road to recovery. Questions to answer during a ransomware attack Before you react to an attack, it\'s important to take a step back and ask questions that will inform your response. Your answers should help network administrators scope the problem, devise an action plan and possibly curtail the spread. Who in your environment is compromised? How widespread are the infections? Is a threat actor actively scouting your environment, exfiltrating data or ready to drop ransomware on other devices? What network permissions do compromised accounts or devices have? Ransomware may have been installed only after attackers had already moved laterally within the network or stolen credentials and other data. What type of attack is it? Is this attack a secondary infection? Did it come from downloaders, remote access Trojans (RATs) or other malware installed on the infected machine or others on the network? Keep in mind that ransomware spreads quickly and is often a byproduct of other threats. If you see one infection, there are probably others that you don\'t see. Proactively look for other issues within your environment. Now as you take action, there are three general step to follow: Step 1: Isolate infected systems The second employees see the ransomware demand or notice something\'s odd-such as suddenly losing access to their own files-they should disconnect from the network and take the infected machine to the IT department. To prepare for this scenario, we recommend that you keep valuable data and systems separated so that a security issue on one system doesn\'t affect other systems. For example, your sensitive research or business data should not reside on the same server and network segment as your email environment. We advise against having employees reboot their system. Only the IT security team should attempt a reboot, and even that will work only in the event that it is “scareware,” or fake ransomware. "Scareware" is malware that appears to be ransomware but isn\'t. It may lock the user\'s screen with a ransom demand and payment instructions, but the data is not actually encrypted. In those scenarios, standard anti-malware tools can help. Knowing the difference isn\'t always easy. Determine the scope of the problem using threat intelligence and external incident responders or forensic analysts when necessary. While all ransomware is bad, some attacks are worse than others. Your response-including whether to pay the ransom-hinges on several factors. Step 2: Call law enforcement Ransomware-like other forms of theft and extortion-is a crime. Nobody has the right to seize devices, networks or data-let alone demand a ransom in exchange for it. Notifying the proper authorities is a necessary first step. Contact local or federal law enforcement right away. Special departments exist specifically to aid cyber crime victims, so do not be afraid to pick up your phone and call them. They are there to help you and may have access to decryption keys or information on payment recovery after | Ransomware Malware Tool Threat | ★★★ | ||
| 2023-10-12 08:13:11 | Shadow PC met en garde contre la violation de données alors que le pirate essaie de vendre des joueurs \\ ' Shadow PC warns of data breach as hacker tries to sell gamers\\' info (lien direct) |
Shadow PC, un fournisseur de services haut de gamme de cloud computing, avertit les clients d'une violation de données qui a exposé des informations privées aux clients \\ ', car un acteur de menace prétend vendre les données volées pour plus de 500 000 clients.[...]
Shadow PC, a provider of high-end cloud computing services, is warning customers of a data breach that exposed customers\' private information, as a threat actor claims to be selling the stolen data for over 500,000 customers. [...] |
Data Breach Threat Cloud | ★★ |
To see everything:
Our RSS (filtrered)
