One Article Review
| Source | |
|---|---|
| Identifiant | 8395081 |
| Date de publication | 2023-10-13 03:47:17 (vue: 2023-10-13 11:06:06) |
| Titre | Une analyse d'une webcontent de safari iOS dans la fenêtre dans l'exploit de processus GPU An analysis of an in-the-wild iOS Safari WebContent to GPU Process exploit |
| Texte | By Ian Beer
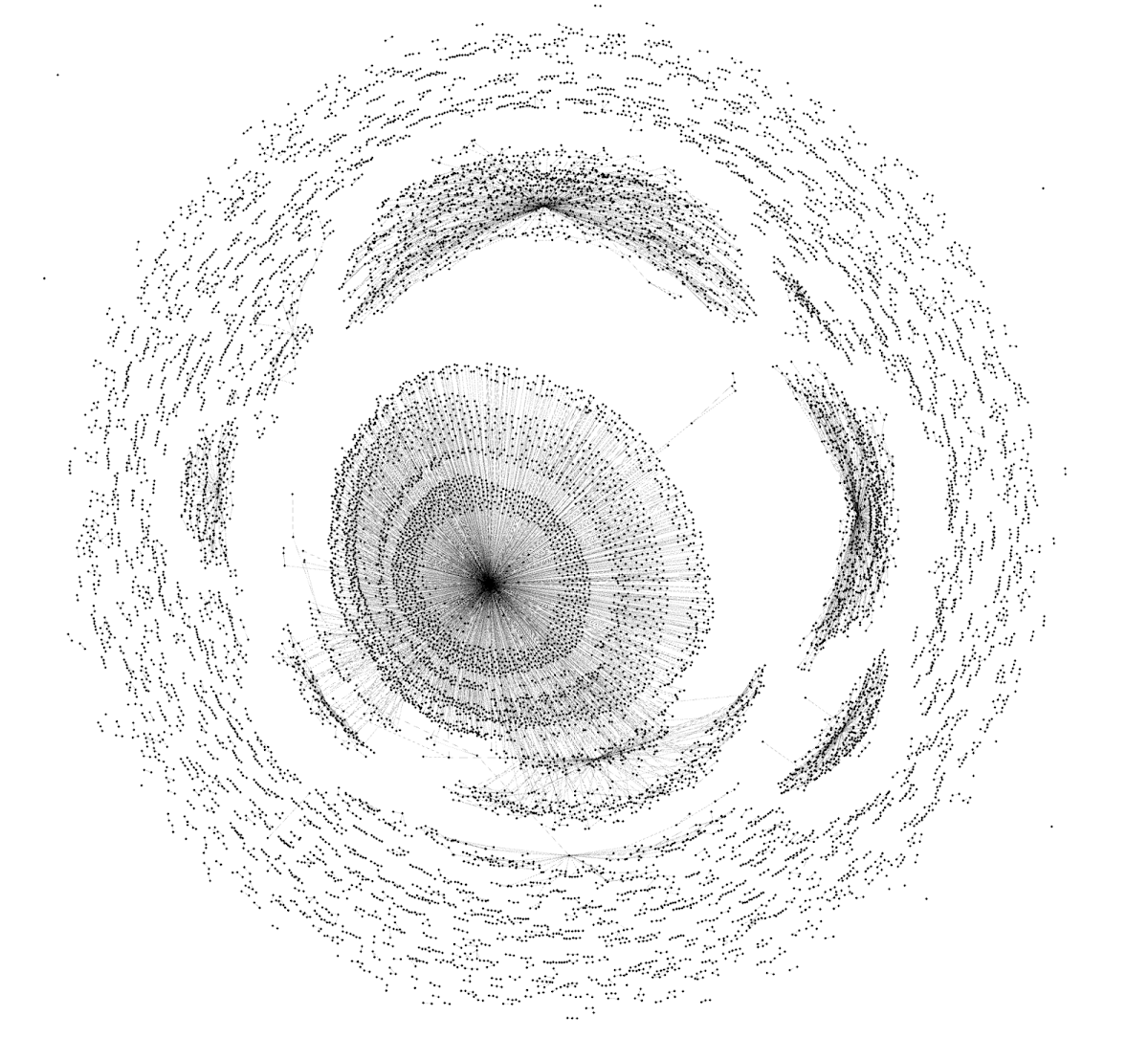 A graph representation of the sandbox escape NSExpression payload
In April this year Google\'s Threat Analysis Group, in collaboration with Amnesty International, discovered an in-the-wild iPhone zero-day exploit chain being used in targeted attacks delivered via malicious link. The chain was reported to Apple under a 7-day disclosure deadline and Apple released iOS 16.4.1 on April 7, 2023 fixing CVE-2023-28206 and CVE-2023-28205.
Over the last few years Apple has been hardening the Safari WebContent (or "renderer") process sandbox attack surface on iOS, recently removing the ability for the WebContent process to access GPU-related hardware directly. Access to graphics-related drivers is now brokered via a GPU process which runs in a separate sandbox.
Analysis of this in-the-wild exploit chain reveals the first known case of attackers exploiting the Safari IPC layer to "hop" from WebContent to the GPU process, adding an extra link to the exploit chain (CVE-2023-32409).
On the surface this is a positive sign: clear evidence that the renderer sandbox was hardened sufficiently that (in this isolated case at least) the attackers needed to bundle an additional, separate exploit. Project Zero has long advocated for attack-surface reduction as an effective tool for improving security and this would seem like a clear win for that approach.
On the other hand, upon deeper inspection, things aren\'t quite so rosy. Retroactively sandboxing code which was never designed with compartmentalization in mind is rarely simple to do effectively. In this case the exploit targeted a very basic buffer overflow vulnerability in unused IPC support code for a disabled feature - effectively new attack surface which exists only because of the introduced sandbox. A simple fuzzer targeting the IPC layer would likely have found this vulnerability in seconds.
A graph representation of the sandbox escape NSExpression payload
In April this year Google\'s Threat Analysis Group, in collaboration with Amnesty International, discovered an in-the-wild iPhone zero-day exploit chain being used in targeted attacks delivered via malicious link. The chain was reported to Apple under a 7-day disclosure deadline and Apple released iOS 16.4.1 on April 7, 2023 fixing CVE-2023-28206 and CVE-2023-28205.
Over the last few years Apple has been hardening the Safari WebContent (or "renderer") process sandbox attack surface on iOS, recently removing the ability for the WebContent process to access GPU-related hardware directly. Access to graphics-related drivers is now brokered via a GPU process which runs in a separate sandbox.
Analysis of this in-the-wild exploit chain reveals the first known case of attackers exploiting the Safari IPC layer to "hop" from WebContent to the GPU process, adding an extra link to the exploit chain (CVE-2023-32409).
On the surface this is a positive sign: clear evidence that the renderer sandbox was hardened sufficiently that (in this isolated case at least) the attackers needed to bundle an additional, separate exploit. Project Zero has long advocated for attack-surface reduction as an effective tool for improving security and this would seem like a clear win for that approach.
On the other hand, upon deeper inspection, things aren\'t quite so rosy. Retroactively sandboxing code which was never designed with compartmentalization in mind is rarely simple to do effectively. In this case the exploit targeted a very basic buffer overflow vulnerability in unused IPC support code for a disabled feature - effectively new attack surface which exists only because of the introduced sandbox. A simple fuzzer targeting the IPC layer would likely have found this vulnerability in seconds.
|
| Envoyé | Oui |
| Condensat | #0: #0x10 #0x18 #0x20 #0x28 #0x34 #0x38 #0x60 #0x80 #1: #2: #30 #3: #4: #5: #6: #7: #8: #9:webkit::remoterenderingbackend::createimagebuffer #define #index #mach #sym# #sym#invocation #sym#invocationimp #sym; $class $class key $classes $classname $null $objects $objects array $objects: $top $top dictionary $top: $version $version: $x0 template &buffer &cglibraryloadimageiodyld &msg &objc &result &sentinel &underscoredname …which &reply &v18 iogpumetalresource* unsigned *image 0001 0111 0x4000ll 0x515151510000n 0x616161610000n 0x818181810000n 1000 1001 1010 1011 1100 1110 1111 58995 = ^ a a2 a3 actually alignment: alloc alternateimage ascii at:&hasbaseurl atindex: b bitmap bridge c ca::cg::drawimage::drawimage cbz cmp decoder destrect dontcopybackingstore export fillcolor forkey:baseurlkey function gpuconnectiontowebprocess if imageidentifier imagesize indicating info initforreadingfromdata: int isobjectclassallowed issuballocdisabled: it jbhk ldp ldr length: let loc mach method mov nativeimageresourceidentifier new nodes nsfunctionexpression into offset options options: passing pinnedgpulocation: primitive: q0 q1 q2 remote remoterenderingbackend::createimagebuffer ipc resourceinargs: ret retarbitrary retroactively return shouldinterpolate::yes size:sizeof srcrect stur syntax then they to uid unionset:nsattributedstring v v11 var view which x0 x8 * arrays *a6 *allowedclasses *ctm *free *image *img *matching *result *self *sym; *this ++wtf::objectidentifierbase::generateidentifierinternal +0x18 in +0x60 in +0x78 in +0x98 is +0x98 of +8 in //webkit::gpuprocess::gpuprocess 0 000 0000 0010 0011 0100 0101 0110 0ll 0ll; 0x00000000 0x0000000000000000 0x0000000000003f10 0x0000000000004000 0x000000013574c0f0 0x00000001420041d0 0x0a1a0a1a0a2a0a2a 0x0a1a0a1a0a2a0a2b 0x0a1a0a1a0a2a0a2c 0x0a1a0a1a0a2a0a2d 0x1 0x10 0x10 byte 0x10000 they 0x13574c000: 0x13574c010: 0x13574c020: 0x1413; 0x18 0x18 bytes 0x186a0 0x19afa9760 0x1da613438 0x1dd2d05b8 0x1dd2d45f0 0x1dd2da340 0x1dd2da348 0x1dd448e70 0x1dd453458 0x1ddc50ed1 0x2 0x200000000n; 0x2222222222222222 0x271: 0x28 0x2a2: 0x2c7: 0x2d4: 0x2df: 0x2f3: 0x3 0x30 byte 0x30; 0x3333333333333333 0x34 0x34343434n 0x34invocationinstance 0x39: 0x3a30dd9dll; 0x3a30dd9e 0x3a: 0x4000 0x4000 0x4000 which 0x4000ll 0x402: 0x412: 0x414141410000n 0x4444444444444444 0x469: 0x46d: 0x46e: 0x474: 0x77a9d075 0x78 0x78 bytes 0x7f6f3229ll; 0x80 0x80000000; 0x88 0x88 below 0x88 bytes 0x88442ab6 0x8888888888888888 0x89442aab 0x89442ab8 0x89442fa2 0x9442ab8 0x9999999999999999 0x9b5: 0x9b7: 0x9b8:setstreamdestinationid 0x9b9: 0x9ba: 0xa85: 0xaaaaaaaaaaaaaaaa 0xba2: 0xba5: 0xba6: 0xbad: 0xc1c1c1c1c1c1c1c1 0xc78 0xd1d1d1d1d1d1d1d1 0xd2d2d2d2d2d2d2d2 0xdba0dba; 0xdba1dba 0xdba1dba send 0xdba1dba; 0xdddddddddddddddd 0xe 0xffff bytes 0xffffffff0ll 0xfffffffffffffff0ll; 0xffffll; 1 before 100 1000 100000 1001 10n 1101 1111 11::operator 11n 128ll 12n 136 1392 13n 14319 14320 14321 14322 14323 14n 15015 15n 160 16336 16; 16k 16kb 16n 17; 17n 188b55cd4 188b55cd8 188b55cdc 188b55ce0 188b55ce8 188b55cec 188b55cf0 188b55cf4 188b55cf8 188b55cfc 188b55d00 188b55d04 188b55d08 188b55d0c 18; 18n 19; 19n 1d61ed988 200 200; 2023 2023 fixing 20; 2147483648; 218 21; 2 |
| Tags | Tool Vulnerability Threat |
| Stories | |
| Notes | ★★ |
| Move | 

|
L'article ne semble pas avoir été repris aprés sa publication.
L'article ne semble pas avoir été repris sur un précédent.