What's new arround internet
| Src | Date (GMT) | Titre | Description | Tags | Stories | Notes |
| 2024-05-08 07:00:00 | Fabric – Un framework open source pour travailler main dans la main avec l\'IA (lien direct) | Découvrez comment utiliser l'IA pour booster votre créativité et productivité. Des outils et exemples concrets pour intégrer l'IA dans vos workflows. | Tool | ★★★★ | ||
| 2024-05-08 06:00:27 | Comment les attaquants utilisent-ils des e-mails usurpés pour détourner vos communications commerciales?4 scénarios de risque How Do Attackers Use Spoofed Email to Hijack Your Business Communications? 4 Risk Scenarios (lien direct) |
When you hear the term “spoofed” email, does business email compromise (BEC) come to mind? It does for many people-especially security leaders. BEC is a form of email fraud, and it has been a top concern for chief information security officers for years. BEC scams are a costly problem. The latest Internet Crime Report from the FBI\'s Internet Crime Complaint Center (IC3) notes that adjusted losses from BEC were $2.9 billion last year. Since 2013, accumulated financial losses due to BEC have reached nearly $53 billion. Spoofing is impersonation, and it is the essence of email fraud. It is also one of the most common techniques used in other types of attacks like phishing and ransomware. Your business, like many, probably focuses on stopping spoofed emails before they can reach employees\' inboxes. However, there is more to worry about. Spoofed email has the potential to damage your brand reputation and jeopardize your business ecosystem, too. In this post, we will explore various impersonation risk scenarios. But first, let\'s look at some common tactics. Impersonation tactics Here are some common methods bad actors use to impersonate others so they can further their attacks. Display name spoofing. The display name appears in the “From:” field of an email. It is the easiest email identifier to manipulate. Attackers forge email headers so that client software displays the fraudulent sender, which most users take at face value. Domain spoofing. Bad actors will use an exact match of an organization\'s domain to launch this type of fraud attack. Attackers who engage in domain spoofing will attempt to imitate the sending server or sending domain. Lookalike domains. Third parties can register lookalike domains and send email that appears to have come from a trusted source. Compromised supplier accounts. In some advanced attacks, attackers will compromise an account from a supplier that works with the business that they want to target. They will use the compromised supplier account to hijack the email communication between their target and its supplier. Eventually, attackers are in a position to launch an attack or solicit fraudulent payment or sensitive data. Attack scenarios Now, let\'s dive into how attackers can use spoofed emails to exploit the trusted relationships you have with your customers, business partners, suppliers and employees. Scenario 1: Impersonate you to target your employees You are probably most familiar with the first scenario, where attackers pretend to be someone within your company, like your CEO or manager. The scam often starts with a simple lure that seems to be a benign message like: How is your day? Are you at your desk? Can you help me with something urgent? Once attackers get a victim to engage, the conversation evolves. The bad actor may request the victim to purchase gift cards for them, proceed with a fraudulent payment, or share confidential data. Not only can attackers impersonate executives, but they can also pretend to be general employees asking human resources to redirect their payrolls. In short, it doesn\'t matter what a victim\'s role is. Anyone can be impersonated to target anyone within an organization. An example of a simple lure where the attacker used display name spoofing to impersonate Ken, the CEO. Another example of a BEC lure where an attacker used a lookalike domain of Watertronics (vs. waltertronics, in the example) to spoof their CEO. Scenario 2: Exploit your suppliers or business partners to target your employees The most common theme in this scenario is supplier invoicing fraud. Bad actors will exploit a company\'s suppliers using tactics such as malicious lookalike domains of suppliers or compromised supplier accounts to either send a fake invoice or request the victim to redirect the payment to a bank account that the attackers control. (Sometimes, we see multiple | Ransomware Malware Tool Threat Cloud | |||
| 2024-05-08 00:59:58 | Cas de distribution de logiciels malveillants liant le site Web de jeu illégal ciblant le serveur Web coréen Case of Malware Distribution Linking to Illegal Gambling Website Targeting Korean Web Server (lien direct) |
Ahnlab Security Intelligence Center (ASEC) a découvert des preuves d'une souche malveillante distribuée aux serveurs Web au sudLa Corée, conduisant les utilisateurs à un site de jeu illégal.Après avoir initialement infiltré un serveur Web Windows Information (IIS) des services d'information sur Internet (IIS) mal gérés en Corée, l'acteur de menace a installé la porte arrière de METERPRETRER, un outil de transfert de port et un outil de logiciel malveillant du module IIS.Ils ont ensuite utilisé ProCDump pour exfiltrater les informations d'identification du compte du serveur.Les modules IIS prennent en charge les fonctionnalités d'extension des serveurs Web tels que ...
AhnLab SEcurity intelligence Center (ASEC) has discovered evidence of a malware strain being distributed to web servers in South Korea, leading users to an illegal gambling site. After initially infiltrating a poorly managed Windows Internet Information Services (IIS) web server in Korea, the threat actor installed the Meterpreter backdoor, a port forwarding tool, and an IIS module malware tool. They then used ProcDump to exfiltrate account credentials from the server. IIS modules support expansion features of web servers such as... |
Malware Tool Threat | ★★ | ||
| 2024-05-07 14:51:31 | Amélioration de la sécurité sociale: introduction Enhancing SOC security: Introducing Pure Signal™ Scout Insight (lien direct) |
Outil d'intelligence des menaces conviviale pour l'analyse IP et le domaine si vous êtes un analyste SOC ou un chef d'équipe et que vous êtes utilisé pour alerter la fatigue ...
User-friendly threat intelligence tool for IP and domain analysis If you are a SOC Analyst or Team Manager and are used to alert fatigue... |
Tool Threat | ★★★ | ||
| 2024-05-07 13:42:04 | Le phishing du code QR est un problème - ce qui est pourquoi Proofpoint a introduit la simulation de phishing du code QR QR Code Phishing is a Problem-That\\'s Why Proofpoint Has Introduced QR Code Phishing Simulation (lien direct) |
QR codes are a part of our everyday lives. They appear in everything from restaurant menus to payment portals. We can use them to quickly access information or perform tasks with a simple scan from our smartphones. However, the ubiquity and convenience of QR codes have also made them an attractive tool for attackers. These seemingly innocuous squares have become a Trojan horse for phishing schemes. In December 2023, Proofpoint launched new in-line threat detection capabilities to stop QR code-based threats. We did this for several reasons. First, we recognized that these attacks are highly deceptive, and existing technologies could not analyze embedded URLs with accuracy. We also understood it was highly likely that users would fall victim to these attacks, as external survey data indicated over 80% of users believe that QR codes are safe. Additionally, our own research showed that QR code attacks had already hit the mainstream. Now, we see daily QR code attack spikes reaching into the tens of thousands. So, our customers must stay vigilant about this threat. To help in that effort, Proofpoint now offers QR code phishing simulations through Proofpoint Security Awareness. You can use them to help your users learn how to recognize and proactively report real QR code phishing attempts. In this post, we will cover the basics of our simulations, and how they serve as a key pillar of our human-centric security strategy. But first, let\'s examine how QR code phishing works. The sequence of events in a QR code attack In QR code phishing, an attacker will disguise malicious URLs within a QR code and embed the QR code into an email. The email is socially engineered to convince the victim to scan the code. After the code is scanned, the victim is redirected to a fraudulent website that is designed to steal sensitive data like login credentials, credit card numbers or personal data. Overview of a QR code attack sequence. What makes malicious QR codes so hard to detect is that attackers are intentionally combining evasion tactics with malicious QR codes to evade email gateways. For example, in a recent QR code attack, threat actors hid malicious QR codes within a PDF attachment. Further, the redirected URL used evasion tactics like adding a Cloudflare CAPTCHA to appear legitimate. Threat actors know that if successfully delivered to their victim it can lead to a successful compromise and they are motivated to continue investing in evasion. The solution: QR code phishing simulation The risk of user exposure to a QR code phishing attack is high, which is why it\'s so important to educate your users about this threat. Here is where our QR code phishing simulation can help. At its core, the simulation works by using email templates that are derived from real-world attacks. Administrators can use the prebuilt templates to launch simulation campaigns that test how employees might react to a QR code attack. These simulations give users firsthand experience in how to identify, avoid and report these threats. This exercise also helps administrators understand their users\' vulnerabilities so that they can develop tailored educational plans. A sample of a QR Code Phishing Simulation template from Proofpoint. To help hone a user\'s knowledge and skills, the prebuilt templates are automatically categorized based on their difficulty level using our Leveled Phishing capability. Proofpoint is the first and only security awareness provider to combine machine learning and NIST Phish Scale research to automatically categorize the level of difficulty of our phishing simulation templates. Leveled Phishing ensures that administrators can objectively challenge a user\'s understanding of the threat. As a user\'s knowledge improves with each simulation, the administrator can continue to challenge that user by launching more, and more difficult, simulations. If the user fails a s | Tool Vulnerability Threat | ★★ | ||
| 2024-05-07 12:53:29 | Utilisateurs d'Intel et ARM Mac: Coucoo Spyware peut nuire à votre PC Intel and ARM Mac Users: Cuckoo Spyware Can Harm Your PC (lien direct) |
Le Web regorge de logiciels espions présentant des applications légitimes et précieuses. kandji, une plate-forme de gestion et de sécurité Apple de périphériques, identifié un nouveau spyware-cum-infostealer qui cible les macs Intel et ARM. Ils ont nommé les logiciels espions & # 8220; coucou & # 8221;Parce qu'il infecte le système hôte et vole ses ressources, un peu comme l'oiseau. Qu'est-ce que le déguisement des logiciels espions de Cuckoo s? Coucou se déguise en binaire mach-o, un format exécutable conçu pour les systèmes Apple. Les chercheurs de Kandji ont commencé par un fichier nommé dumpmediaspotifymusicconverter , également appelé & # 8220; upd & # 8221;téléchargé sur virus total. Il suit et enregistre les données de iCloud Keychain, Apple Notes, Browsers Web et Crypto Wallet. Même des applications comme Discord, Filezilla, Steam et Telegram sont sa cible.Les chercheurs de Kandji notent que le logiciel espion mue le son du système pour capturer des captures d'écran. Il lance également l'application pour couvrir ses pistes et agir comme si rien ne s'était passé. En recherchant le Web, ils ont constaté qu'il était hébergé sur un site Web qui offrait des applications à convertir la musique des services de streaming à mp3. Les sites Web suspects proposent des versions gratuites et payantes d'applications pour déchirer la musique des services de streaming et pour iOS et Android Recovery.Voici quelques-uns d'entre eux: Dumpmedia [.] com TUNESOLO [.] com Fonedog [.] com TUNESFUN [.] com Tunefab [.] com Tous les groupes d'applications sur ces sites ont un ID de développeur de la technologie Yian Shenzhen Co., Ltd (VRBJ4VRP).Applications d'applications sur FonEdog ont une identification différente: Fonedog Technology Limited (Cuau2GTG98). Après avoir téléchargé une application Spotify vers MP3, ils ont ouvert le fichier image de disque et ont été surpris de trouver la même & # 8220; UPD & # 8221;fichier avec l'application réelle. Le binaire malveillant n'a pas fonctionné parce que Gatekeeper l'a bloqué.Après avoir accordé une autorisation manuelle, l'application a vérifié le lieu pour déterminer le pays de l'utilisateur. . Étonnamment, CUCUS WA LE REAGNER SI LE SYSTÈME appartient à l'un des pays suivants: Arménie Bélarus Kazakhstan Russie Ukraine CUCUS veut tout savoir this Spyware est conçu pour capturer autant d'informations que possible et l'envoyer au serveur de commande et de contrôle. CUCUS peut déterminer vos informations matérielles exactes, obtenir la liste des applications installées et capturer les processus en cours d'exécution. La recherche d'outils pour extraire l'audio ou la vidéo d'un service de streaming au MP3 ou à tout autre format souhaité est courant, et les attaquants voulaient capitaliser sur cet intérêt. Évitez de télécharger des applications à partir de sites indignes de confiance vers | Tool Mobile | ★★★ | ||
| 2024-05-06 21:03:51 | TunnelVision – la faille qui fait sauter le VPN et laisse fuiter vos données (lien direct) | TunnelVision, une technique exploitant le protocole DHCP, permet de contourner la protection des VPN et d'intercepter le trafic des utilisateurs à leur insu, remettant en cause la sécurité promise par ces outils. Découvrez son fonctionnement et comment vous en prémunir. | Tool Vulnerability | ★★★ | ||
| 2024-05-06 19:30:00 | Le défaut Critical Tinyproxy ouvre plus de 50 000 hôtes à l'exécution du code distant Critical Tinyproxy Flaw Opens Over 50,000 Hosts to Remote Code Execution (lien direct) |
Plus de 50% des 90 310 hôtes ont été trouvés exposant A & NBSP; Tinyproxy Service & NBSP; sur Internet qui \\ est vulnérable à un défaut de sécurité non corrigé dans l'outil de proxy HTTP / HTTPS.
Le problème, suivi comme & nbsp; CVE-2023-49606, procure un score CVSS de 9,8 sur un maximum de 10, par Cisco Talos, qui l'a décrit comme un bug de l'utilisation après les versions impactant les versions 1.10.0 et 1.11.1,qui est le
More than 50% of the 90,310 hosts have been found exposing a Tinyproxy service on the internet that\'s vulnerable to a critical unpatched security flaw in the HTTP/HTTPS proxy tool. The issue, tracked as CVE-2023-49606, carries a CVSS score of 9.8 out of a maximum of 10, per Cisco Talos, which described it as a use-after-free bug impacting versions 1.10.0 and 1.11.1, which is the |
Tool | ★★★ | ||
| 2024-05-06 16:26:54 | Faits saillants hebdomadaires, 6 mai 2024 Weekly OSINT Highlights, 6 May 2024 (lien direct) |
## Snapshot Last week\'s OSINT reporting reveals a spectrum of sophisticated cyber threats orchestrated by diverse threat actors targeting organizations globally. The articles highlight various attack vectors, including DNS manipulation techniques (Muddling Meerkat), social engineering tactics with Python-based RATs (DEV#POPPER), and ransomware campaigns exploiting legitimate files (Sophos ransomware). Threat actors range from nation-state affiliated groups like Muddling Meerkat to financially motivated actors leveraging ransomware like Dagon Locker. Several reports highlight the persistent nature of cyber threats as threat actors continue to exploit well-known vulnerabilities like [CVE-2015-2051](https://sip.security.microsoft.com/intel-explorer/cves/CVE-2015-2051/description) and evolve established tools such as the[ZLoader banking trojan](https://sip.security.microsoft.com/intel-profiles/cbcac2a1de4e52fa5fc4263829d11ba6f2851d6822569a3d3ba9669e72aff789)to launch successful attacks. These findings emphasize the ongoing need for organizations to prioritize patch management and remain vigilant against evolving tactics employed by threat actors leveraging both known and refined techniques to infiltrate systems and compromise networks. ## Description 1. [**Cyberattacks Targeting Poorly Managed MS-SQL Servers**](https://sip.security.microsoft.com/intel-explorer/articles/f5f3ecc6): Threat actors exploit vulnerabilities in improperly managed MS-SQL servers to install Mallox ransomware. The attack involves deploying Remcos RAT for system control and leveraging a custom remote screen control malware, highlighting the risk posed by insecure database management practices. 2. [**Sophos Ransomware Campaign Exploiting Legitimate Files**](https://security.microsoft.com/intel-explorer/articles/e27d7355): Sophisticated ransomware campaign exploits legitimate Sophos executables and DLLs by altering their content and inserting malicious payloads like Cobalt Strike and Brute Ratel. Attackers use JavaScript loaders via email for initial access, disguising malicious activity within seemingly legitimate files to evade detection. 3. [**Social Engineering Attack Targeting Developers**](https://security.microsoft.com/intel-explorer/articles/7ef7309c): North Korean threat actors use fake job interviews to deliver Python-based RATs to developers, exploiting their trust in the job application process. The attackers mimic real companies and interview processes to deceive developers into downloading and executing malicious software. 4. [**Detailed Account of Intrusion using IcedID and Cobalt Strike**](https://security.microsoft.com/intel-explorer/articles/55e96eb8): A comprehensive incident report details a sophisticated intrusion involving IcedID malware and Cobalt Strike beacons. The threat actors employed multiple evasion techniques, lateral movement tools, and exfiltration methods, culminating in the deployment of Dagon Locker ransomware. 5. [**Evolution of ZLoader Trojan with New Evasion Tactics**](https://sip.security.microsoft.com/intel-explorer/articles/0d7c21ec): ZLoader, a modular banking trojan derived from ZeuS source code, reappears with enhanced obfuscation methods and anti-analysis features. This malware\'s evolution demonstrates a strategic effort to evade detection and limit binary execution to infected systems. 6. [**Emergence of Goldoon Botnet Targeting D-Link Devices**](https://sip.security.microsoft.com/intel-explorer/articles/de08653e): The Goldoon botnet exploits CVE-2015-2051 vulnerability to compromise D-Link devices and launch denial-of-service attacks. The malware, once executed, establishes a persistent connection with a C2 server and contains 27 different attack methods, posing a significant threat to affected organizations. 7. [**Muddling Meerkat: DNS Manipulation by Nation-State Actors**](https://security.microsoft.com/intel-explorer/articles/b6049233): The threat actor group, suspected to be affiliated with China, employs DNS manipulation techniques to hijack internet traffic for strat | Ransomware Malware Tool Vulnerability Threat | ★★ | ||
| 2024-05-06 13:15:00 | #RSAC: 70% des entreprises hiérarchisent l'innovation sur la sécurité dans les projets génératifs d'IA #RSAC: 70% of Businesses Prioritize Innovation Over Security in Generative AI Projects (lien direct) |
Un rapport IBM a révélé que la plupart des organisations s'exposent à des risques de sécurité lors de la mise en œuvre d'outils générateurs d'IA
An IBM report found that most organizations are exposing themselves to security risks when implementing generative AI tools |
Tool | ★★★ | ||
| 2024-05-06 11:11:16 | Proton Pass lance Pass Monitor (lien direct) | Proton Pass lance Pass Monitor, une nouvelle suite de sécurité comprenant la surveillance du Dark Web, Password Health et bien plus encore • Fonctionnalité essentielle de Pass Monitor, la surveillance du Dark Web dans Proton Pass alertera désormais les utilisateurs si leurs identifiants de messagerie ont été exposés sur le dark web, où les e-mails et les identifiants volés sont achetés et vendus. • Les alertes incluront des détails sur les adresses e-mail et les alias qui auraient été compromis à partir d'un site tiers, la source et la date de la brèche, ainsi que des recommandations sur la manière dont les utilisateurs peuvent se protéger. • Pass Monitor inclut également Password Health. Disponible pour tous les utilisateurs, cette fonctionnalité permet d'identifier les mots de passe faibles ou réutilisés ainsi que ceux pour lesquels la double authentification n'a pas été activée. • Proton Pass devient le premier gestionnaire de mots de passe associant le chiffrement de bout en bout, la surveillance du Dark Web, l'identification de la santé des mots de passe et la sécurité avancée des comptes. • Cette nouvelle fonctionnalité offre aux utilisateurs encore plus de contrôle sur la sécurité de leur compte et met à disposition les outils dont ils ont besoin pour se protéger. - Produits | Tool | ★★★ | ||
| 2024-05-06 07:54:03 | Genai alimente la dernière vague des menaces de messagerie modernes GenAI Is Powering the Latest Surge in Modern Email Threats (lien direct) |
Generative artificial intelligence (GenAI) tools like ChatGPT have extensive business value. They can write content, clean up context, mimic writing styles and tone, and more. But what if bad actors abuse these capabilities to create highly convincing, targeted and automated phishing messages at scale? No need to wonder as it\'s already happening. Not long after the launch of ChatGPT, business email compromise (BEC) attacks, which are language-based, increased across the globe. According to the 2024 State of the Phish report from Proofpoint, BEC emails are now more personalized and convincing in multiple countries. In Japan, there was a 35% increase year-over-year for BEC attacks. Meanwhile, in Korea they jumped 31% and in the UAE 29%. It turns out that GenAI boosts productivity for cybercriminals, too. Bad actors are always on the lookout for low-effort, high-return modes of attack. And GenAI checks those boxes. Its speed and scalability enhance social engineering, making it faster and easier for attackers to mine large datasets of actionable data. As malicious email threats increase in sophistication and frequency, Proofpoint is innovating to stop these attacks before they reach users\' inboxes. In this blog, we\'ll take a closer look at GenAI email threats and how Proofpoint semantic analysis can help you stop them. Why GenAI email threats are so dangerous Verizon\'s 2023 Data Breach Investigations Report notes that three-quarters of data breaches (74%) involve the human element. If you were to analyze the root causes behind online scams, ransomware attacks, credential theft, MFA bypass, and other malicious activities, that number would probably be a lot higher. Cybercriminals also cost organizations over $50 billion in total losses between October 2013 and December 2022 using BEC scams. That represents only a tiny fraction of the social engineering fraud that\'s happening. Email is the number one threat vector, and these findings underscore why. Attackers find great success in using email to target people. As they expand their use of GenAI to power the next generation of email threats, they will no doubt become even better at it. We\'re all used to seeing suspicious messages that have obvious red flags like spelling errors, grammatical mistakes and generic salutations. But with GenAI, the game has changed. Bad actors can ask GenAI to write grammatically perfect messages that mimic someone\'s writing style-and do it in multiple languages. That\'s why businesses around the globe now see credible malicious email threats coming at their users on a massive scale. How can these threats be stopped? It all comes down to understanding a message\'s intent. Stop threats before they\'re delivered with semantic analysis Proofpoint has the industry\'s first predelivery threat detection engine that uses semantic analysis to understand message intent. Semantic analysis is a process that is used to understand the meaning of words, phrases and sentences within a given context. It aims to extract the underlying meaning and intent from text data. Proofpoint semantic analysis is powered by a large language model (LLM) engine to stop advanced email threats before they\'re delivered to users\' inboxes in both Microsoft 365 and Google Workspace. It doesn\'t matter what words are used or what language the email is written in. And the weaponized payload that\'s included in the email (e.g., URL, QR code, attached file or something else) doesn\'t matter, either. With Proofpoint semantic analysis, our threat detection engines can understand what a message means and what attackers are trying to achieve. An overview of how Proofpoint uses semantic analysis. How it works Proofpoint Threat Protection now includes semantic analysis as an extra layer of threat detection. Emails must pass through an ML-based threat detection engine, which analyzes them at a deeper level. And it does | Ransomware Data Breach Tool Vulnerability Threat | ChatGPT | ★★★ | |
| 2024-05-05 00:00:00 | BSIDESSF 2024 Écritures: pas d'outils (un défi de bash perplexe) BSidesSF 2024 Writeups: No Tools (A puzzling Bash challenge) (lien direct) |
pas d'outils est un défi terminal assez simple, quelque chose pour les nouveaux joueursmâcher. Je soupçonne qu'il existe plusieurs façons différentes de le résoudre, mais l'idée de base est de lire un fichier en utilisant uniquement des fonctions intégrées de sh . Je l'ai personnellement résolu avec le lire intégré: $ lire file= "nv"> $ drapeau Ctf { where-are-mon-tools } Une autre solution que mon co-organisateur a développée a utilisé Exec : $ exec | Tool | ★★ | ||
| 2024-05-05 00:00:00 | BSIDESSF 2024 Écritures: ne peut pas donner (exploitation CGI) BSidesSF 2024 Writeups: Can\\'t Give In (CGI exploitation) (lien direct) |
The premise of the three challenges cant-give-in, cant-give-in-secure, and cant-give-in-securer are to learn how to exploit and debug compiled code that\'s loaded as a CGI module. You might think that\'s unlikely, but a surprising number of enterprise applications (usually hardware stuff - firewalls, network “security” appliances, stuff like that) is powered by CGI scripts. You never know! This challenge was inspired by one of my co-workers at GreyNoise asking how to debug a CGI script. I thought it\'d be cool to make a multi-challenge series in case others didn\'t know! This write-up is intended to be fairly detailed, to help new players understand their first stack overflow! Part 1: cant-give-in The vulnerability First, let\'s look at the vuln! All three challenges have pretty similar vulnerabilities, but here\'s what the first looks like: char *strlength = getenv("CONTENT_LENGTH"); if(!strlength) { printf("ERROR: Please send data!"); exit(0); } int length = atoi(strlength); read(fileno(stdin), data, length); if(!strcmp(data, "password=MyCoolPassword")) { printf("SUCCESS: authenticated successfully!"); } else { printf("ERROR: Login failed!"); } The way CGI works - a fact that I\'d forgotten since learning Perl like 20 years ago - is that the headers are processed by Apache and sent to the script as environmental variables, and the body (ie, POST data) is sent on stdin. In that script, we read the Content-Length from a variable, then read that many bytes of the POST body into a static buffer. That\'s a fairly standard buffer overflow, with the twist that it\'s in a CGI application! We can demonstrate the issue pretty easily by running the CGI directly (I\'m using dd to produce 200 characters without cluttering up the screen): | Tool Vulnerability Threat | ★★★ | ||
| 2024-05-03 20:14:15 | Les acteurs menacés attaquent les serveurs MS-SQL pour déployer des ransomwares Threat Actors Attacking MS-SQL Servers to Deploy Ransomware (lien direct) |
## Instantané
Les professionnels de la cybersécurité de GBhackers ont découvert une série de cyberattaques ciblant les serveurs Microsoft SQL (MS-SQL) mal gérés pour installer les ransomwares de Mallox sur les systèmes.
** En savoir plus sur la couverture de Microsoft \\ pour [MalloxRansomware ici.] (Https://sip.security.microsoft.com/intel-profiles/7fbe39c998c8a495a1652ac6f8bd34852c00f97dc61278cafc56dca1d443131e) **
##Description
Le modus operandi du groupe des acteurs de la menace implique d'exploiter les vulnérabilités dans des serveurs MS-SQL mal gérés.En utilisant des attaques de force brute et du dictionnaire, les attaquants obtiennent un accès non autorisé, ciblant principalement le compte SA (administrateur système système).
Une fois à l'intérieur, ils déploient l'outil d'accès à distance REMCOS (RAT) pour prendre le contrôle du système infecté.Remcos Rat, initialement utilisé pour la violation et le contrôle du système, a été réutilisé par des attaquants pour des activités malveillantes, avec des capacités telles que le keylogging, la capture de capture d'écran et le contrôle sur les webcams et les microphones.De plus, un logiciel malveillant à télécommande sur mesure est déployé, permettant aux attaquants d'accéder au système infecté à l'aide de l'ID AnyDesk obtenu à partir du serveur de commande et de contrôle.
Le ransomware de Mallox, connu pour cibler les serveurs MS-SQL, a ensuite été installé pour crypter le système.Mallox Ransomware, utilise des algorithmes de cryptage AES-256 et SHA-256, ajoutant une extension ".rmallox" aux fichiers cryptés.
Les modèles d'attaque observés dans cette campagne ressemblent à une ressemblance frappante avec les incidents précédents impliquant le Coinmin Tor2mine et le ransomware Bluesky, suggérant le travail du même groupe de menaces.
## Recommandations
La documentation technique Microsoft SQL Server et les étapes pour sécuriser les serveurs SQL peuvent être trouvées ici:
[Documentation de sécurité pour SQL Server & Azure SQL Base de données - SQL Server |Microsoft Learn] (https://learn.microsoft.com/en-us/sql/relationd-databases/security/security-center-for-sql-server-database-engine-and-azure-sql-database?view=SQL-Server-Ver16)
## Les références
["Les acteurs de la menace attaquant les serveurs MS-SQL pour déployer les ransomwares"] (https://gbhackers.com/ms-sql-deploy-ransomware/) GBHACKERS (consulté en 2024-05-03).
## Snapshot Cybersecurity professionals at GBHackers have discovered a series of cyberattacks targeting poorly managed Microsoft SQL (MS-SQL) servers to install Mallox Ransomware on systems. **Read more about Microsoft\'s coverage for [Mallox Ransomware here.](https://sip.security.microsoft.com/intel-profiles/7fbe39c998c8a495a1652ac6f8bd34852c00f97dc61278cafc56dca1d443131e)** ## Description The threat actor group\'s modus operandi involves exploiting vulnerabilities in improperly managed MS-SQL servers. By employing brute force and dictionary attacks, the attackers gain unauthorized access, primarily targeting the SA (System Administrator) account. Once inside, they deploy the Remcos Remote Access Tool (RAT) to take control of the infected system. Remcos RAT, initially used for system breach and control, has been repurposed by attackers for malicious activities, featuring capabilities such as keylogging, screenshot capture, and control over webcams and microphones. Additionally, a custom-made remote screen control malware is deployed, allowing attackers to gain access to the infected system using the AnyDesk ID obtained from the command and control server. Mallox ransomware, known for targeting MS-SQL servers, was then installed to encrypt the system. Mallox ransomware, utilizes AES-256 and SHA-256 encryption algorithms, appending a ".rmallox" extension to encrypted files. The attack patterns observed in this campaign bear a striking resemblance to |
Ransomware Malware Tool Vulnerability Threat Technical | ★★★ | ||
| 2024-05-03 12:00:54 | Edward Snowden lance un dernier avertissement sur la confidentialité du Bitcoin (lien direct) | Edward Snowden alerte sur les risques pour la confidentialité de Bitcoin. Les autorités américaines intensifient leur offensive contre les outils de protection de la vie privée. Des entreprises comme Wasabi Wallet et Trezor ont dû restreindre leurs services aux États-Unis. | Tool | |||
| 2024-05-03 00:36:38 | McAfee domine le test de performance PC-COMPARATIVES AV McAfee Dominates AV-Comparatives PC Performance Test (lien direct) |
>  À notre époque numérique, un ordinateur n'est pas seulement un outil;C'est une passerelle vers un monde de possibilités, de divertissement, ...
À notre époque numérique, un ordinateur n'est pas seulement un outil;C'est une passerelle vers un monde de possibilités, de divertissement, ...
>  In our digital age, a computer is not just a tool; it’s a gateway to a world of possibilities, entertainment,...
In our digital age, a computer is not just a tool; it’s a gateway to a world of possibilities, entertainment,...
|
Tool | ★★ | ||
| 2024-05-02 10:00:00 | L'API Microsoft Graph apparaît comme un outil d'attaquant supérieur pour tracer le vol de données Microsoft Graph API Emerges as a Top Attacker Tool to Plot Data Theft (lien direct) |
Armemer les propres services de Microsoft \\ pour la commande et le contrôle est simple et rentable, et cela aide les attaquants à mieux éviter la détection.
Weaponizing Microsoft\'s own services for command-and-control is simple and costless, and it helps attackers better avoid detection. |
Tool | ★★ | ||
| 2024-05-02 05:00:00 | \\ 'Dunequixote \\' montre que les méthodes de cyberattaque furtives évoluent.Les défenseurs peuvent-ils suivre? \\'DuneQuixote\\' Shows Stealth Cyberattack Methods Are Evolving. Can Defenders Keep Up? (lien direct) |
Une récente campagne ciblant les organisations gouvernementales du Moyen-Orient joue des outils de détection standard comme un violon.Les cyberattaques deviennent plus créatifs, les défenseurs doivent commencer à suivre le rythme.
A recent campaign targeting Middle Eastern government organizations plays standard detection tools like a fiddle. With cyberattackers getting more creative, defenders must start keeping pace. |
Tool | ★★★ | ||
| 2024-05-02 03:20:36 | Cybersécurité: la bataille des esprits Cybersecurity: The Battle of Wits (lien direct) |
Avec la cybersécurité, les champs de bataille numériques s'étendent sur la vaste étendue d'Internet.D'un côté, nous avons des adversaires de plus en plus sophistiqués et rusés.De l'autre, des praticiens de cybersécurité qualifiés qui sont désespérés de protéger à tout prix leurs entreprises.Une vérité fondamentale sonne claire: c'est une bataille d'esprit continue et implacable.Tout comme les mercenaires modernes, les mauvais acteurs sont armés d'un arsenal d'outils et de menaces sophistiqués, à la recherche continue de tout bink dans l'armure de sécurité à exploiter.Leurs objectifs vont du gain financier et de la fraude ...
With cybersecurity, the digital battlegrounds stretch across the vast expanse of the internet. On the one side, we have increasingly sophisticated and cunning adversaries. On the other, skilled cybersecurity practitioners who are desperate to protect their companies\' assets at all costs. One fundamental truth rings clear: it\'s an ongoing and relentless battle of wits. Much like modern-day mercenaries, bad actors are armed with an arsenal of sophisticated tools and threats , continually looking for any chinks in the security armor to exploit. Their objectives range from financial gain and fraud... |
Tool Threat | ★★ | ||
| 2024-05-01 20:56:45 | La campagne de logiciels malveillants tente la maltraitance des binaires de sophos Malware Campaign Attempts Abuse of Sophos Binaries (lien direct) |
## Instantané Sophos discute d'une campagne de ransomwares qui exploite des exécutables et des DLL légitimes de Sophos en modifiant leur contenu d'origine, en écrasant le code de point d'entrée et en insérant la charge utile déchiffrée comme ressource. ## Description Cette usurpation d'identité des fichiers légitimes vise à infiltrer les systèmes.L'enquête a révélé plusieurs charges utiles, telles que Cobalt Strike, Brute Ratel, Qakbot et Latrodectus, indiquant l'implication de plus d'un groupe criminel. L'accès initial aux systèmes des victimes \\ 'impliquait l'utilisation de chargeurs JavaScript envoyés par e-mail.Le comportement malveillant vise à confondre les analystes en se déguisant en fichiers légitimes, en évitant potentiellement la détection.Les attaquants ont ciblé plusieurs exécutables Sophos And dlls, y compris sophosleanup.exe, sophosfstelemetry.exe, sophosfx.exe, sophosintelixpackager.exe, sophosntpuninstall.eXE, Healthapi.dll et Sophosuninstall.exe.Ces fichiers se sont révélés malveillants et ont été associés à diverses charges utiles et connexions C2. ## Recommandations Microsoft recommande les atténuations suivantes pour réduire l'impact des menaces de ransomware. - Allumez [Protection en livraison du cloud] (https://learn.microsoft.com/microsoft-365/security/defender-endpoint/configure-lock-at-first-sight-microsoft-defender-asvirus?ocid=magicti_ta_learndoc)Dans Microsoft Defender Antivirus ou l'équivalent pour que votre produit antivirus couvre des outils et techniques d'attaquant en évolution rapide.Les protections d'apprentissage automatique basées sur le cloud bloquent une énorme majorité de variantes nouvelles et inconnues. - Allumez [Protection Tamper] (https://learn.microsoft.com/microsoft-365/security/defender-endpoint/prevent-changes-to-security-settings-with-tamper-protection?ocid=Magicti_TA_LearnDoc).Empêcher les attaquants d'empêcher les services de sécurité. - Exécutez [Détection et réponse de point de terminaison (EDR) en mode bloc] (https://learn.microsoft.com/microsoft-365/security/defender-endpoint/edr-in-lock-mode?ocid=Magicti_TA_Learndoc), de sorte que celaLe défenseur du point final peut bloquer les artefacts malveillants, même lorsque votre antivirus non microsoft ne détecte pas la menace ou lorsque Microsoft Defender Antivirus fonctionne en mode passif.EDR en mode bloc fonctionne dans les coulisses pour corriger les artefacts malveillants détectés après la durée. - Activer [Investigation and Remediation] (https://learn.microsoft.com/microsoft-365/security/defender-endpoint/automated-investigations?ocid=Magicti_TA_Learndoc) en mode automatisé complet pour permettre au défenseur de prendre une action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate sur l'action immédiate surAlertes pour résoudre les violations, réduisant considérablement le volume d'alerte. - Les clients de Microsoft Defender peuvent activer [Règles de réduction de la surface d'attaque] (https://learn.microsoft.com/microsoft-365/security/defender-endpoint/attack-surface-reduction?ocid=Magicti_TA_LearnDoc) pour prévenir les techniques d'attaque communes utilisées utilisées | Ransomware Malware Tool Threat | ★★ | ||
| 2024-05-01 19:46:49 | Attaque "Stream Dirty": découvrir et atténuer un modèle de vulnérabilité commun dans les applications Android “Dirty stream” attack: Discovering and mitigating a common vulnerability pattern in Android apps (lien direct) |
## Snapshot Microsoft discovered a path traversal-affiliated vulnerability pattern in multiple popular Android applications that could enable a malicious application to overwrite files in the vulnerable application\'s home directory. The implications of this vulnerability pattern include arbitrary code execution and token theft, depending on an application\'s implementation. Arbitrary code execution can provide a threat actor with full control over an application\'s behavior. Meanwhile, token theft can provide a threat actor with access to the user\'s accounts and sensitive data. We identified several vulnerable applications in the Google Play Store that represented over four billion installations. We anticipate that the vulnerability pattern could be found in other applications. We\'re sharing this research so developers and publishers can check their apps for similar issues, fix as appropriate, and prevent introducing such vulnerabilities into new apps or releases. As threats across all platforms continue to evolve, industry collaboration among security researchers, security vendors, and the broader security community is essential in improving security for all. Microsoft remains committed to working with the security community to share vulnerability discoveries and threat intelligence to protect users across platforms. After discovering this issue, we identified several vulnerable applications. As part of our responsible disclosure policy, we notified application developers through Coordinated Vulnerability Disclosure (CVD) via Microsoft Security Vulnerability Research (MSVR) and worked with them to address the issue. We would like to thank the Xiaomi, Inc. and WPS Office security teams for investigating and fixing the issue. As of February 2024, fixes have been deployed for the aforementioned apps, and users are advised to keep their device and installed applications up to date. Recognizing that more applications could be affected, we acted to increase developer awareness of the issue by collaborating with Google to publish an article on the Android Developers website, providing guidance in a high-visibility location to help developers avoid introducing this vulnerability pattern into their applications. We also wish to thank Google\'s Android Application Security Research team for their partnership in resolving this issue. In this post, we continue to raise developer and user awareness by giving a general overview of the vulnerability pattern, and then focusing on Android share targets, as they are the most prone to these types of attacks. We go through an actual code execution case study where we demonstrate impact that extends beyond the mobile device\'s scope and could even affect a local network. Finally, we provide guidance to users and application developers and illustrate the importance of collaboration to improve security for all. ## Activity Overview ### Data and file sharing on Android The Android operating system enforces isolation by assigning each application its own dedicated data and memory space. To facilitate data and file sharing, Android provides a component called a content provider, which acts as an interface for managing and exposing data to the rest of the installed applications in a secure manner. When used correctly, a content provider provides a reliable solution. However, improper implementation can introduce vulnerabilities that could enable bypassing of read/write restrictions within an application\'s home directory. The Android software development kit (SDK) includes the [FileProvider](https://developer.android.com/reference/androidx/core/content/FileProvider) class, a subclass of ContentProvider that enables file sharing between installed applications. An application that needs to share its files with other applications can declare a FileProvider in its app manifest and declare the specific paths to share. Every file provider has a property called authority, which identifies it system-wide, and can b | Tool Vulnerability Threat Studies Mobile Technical | ★★★ | ||
| 2024-05-01 19:01:06 | Muddywater Campaign abuse d'agents Atera MuddyWater Campaign Abusing Atera Agents (lien direct) |
#### Targeted Geolocations - Israel - India - Algeria - Italy - Egypt - Türkiye #### Targeted Industries - Transportation Systems - Aviation - Information Technology - Healthcare & Public Health - Government Agencies & Services - General Public Services - Federal ## Snapshot Researchers at HarfangLab have been monitoring a campaign by Iran-based threat group MuddyWater, tracked by Microsoft as [Mango Sandstorm](https://sip.security.microsoft.com/intel-profiles/36949e052b63fa06ee586aef3d1fec8dd2e1b567e231d88c28c16299f9b25340), characterized by the use of Remote Monitoring and Management (RMM) tools. Microsoft tracks this actor as Mango Sandstorm, [read more about them here](https://sip.security.microsoft.com/intel-profiles/36949e052b63fa06ee586aef3d1fec8dd2e1b567e231d88c28c16299f9b25340). ## Description According to HarfangLab, MuddyWater has been utilizing legitimate RMM software in its attacks since at least 2021, but has been monitoring this campaign using Atera Agent since October 2023. Leveraging Atera\'s free trial offers, the agents seen in this campaign have been registered using both compromised enterprise and personal email accounts. The infection chain in this campaign begins with the deployment of spearphishing emails. These emails are highly tailored to the victim organization and contain malicious attachments or links. Upon interaction, MuddyWater leverages free file sharing sites to host the RMM software, in this case Atera Agent, giving the group remote access and control over compromised systems. The group likely does not rely on the Subsequently, the group is able to execute commands, conduct reconnaissance, and move laterally across the network facilitating the deployment of additional malware payloads enabling the group to maintain persistence and exfiltrate sensitive data. ## Microsoft Analysis Microsoft Threat Intelligence has identified that this campaign is likely attributed to the actor Microsoft tracks as Mango Sandstorm, an Iranian nation-state actor with ties to Iran\'s Ministry of Intelligence and Security (MOIS). In past operations, Mango Sandstorm has primarily, but not exclusively, sought to collect information assessed to have strategic value, typically from organizations in the aviation, education, defense, energy, government, and telecommunications sectors in the Middle East and North Africa. Mango Sandstorm tends to favor spearphishing attacks. In this and prior campaigns, the group has been observed using commercial RMM tools to achieve persistence in a target environment. Mango Sandstorm has been identified attempting to deliver Atera, SimpleHelp, RPort, N-able Advanced Monitoring Agent, Splashtop, Syncro, and AnyConnect. ## Detections As tools used in these types of campaigns might have legitimate uses, they are not typically detected as malicious, and proactive hunting is recommended. ## Recommendations Microsoft recommends the following mitigations to reduce the impact of activity associated with Mango Sandstorm\'s operations. - Use the Attack Simulator in Microsoft Defender for Office 365 to organize realistic, yet safe, simulated phishing and password attack campaigns in your organization by training end users against clicking URLs in unsolicited messages and disclosing their credentials. Training should include checking for poor spelling and grammar in phishing emails or the application\'s consent screen as well as spoofed app names, logos and domain URLs appearing to originate from legitimate applications or companies. Note: Attack Simulator testing currently only supports phishing emails containing links. - Encourage users to use Microsoft Edge and other web browsers that support SmartScreen, which identifies and blocks malicious websites, including phishing sites, scam sites, and sites that contain exploits and host malware. - Harden internet-facing assets and identify and se | Malware Tool Threat Medical Commercial | ★★★ | ||
| 2024-05-01 17:11:23 | Nord Security présente Nordstellar Nord Security introduces NordStellar (lien direct) |
Les créateurs de NordVPN lance Nordstellar, une nouvelle plateforme de gestion de l'exposition aux menaces pour les entreprises
● Nordstellar permet aux entreprises de réduire les temps de détection des fuites de données et de minimiser les risques pour une organisation
● Pendant plusieurs années, la plate-forme a été utilisée et testée comme un outil interne, désormais mis à la disposition du public
● C'est la troisième solution B2B par Nord Security, y compris un gestionnaire de mots de passe pour les entreprises - Nordpass, et une solution de sécurité d'accès au réseau - Nordlayer
● Cette année, la société a également lancé Saily - un service ESIM
-
revues de produits
The creators of NordVPN launches NordStellar, a new threat exposure management platform for businesses ● NordStellar allows companies to cut down on data leak detection times and minimize risk to an organization ● For several years, the platform was used and tested as an internal tool, now made available to the public ● It\'s the third B2B solution by Nord Security, including a password manager for businesses - NordPass, and a network access security solution - NordLayer ● This year, the company also launched Saily - an eSIM service - Product Reviews |
Tool Threat | ★★ | ||
| 2024-05-01 16:33:00 | Tout le monde est un expert: comment autonomiser vos employés pour le succès de la cybersécurité Everyone\\'s an Expert: How to Empower Your Employees for Cybersecurity Success (lien direct) |
Il y a un désir humain naturel d'éviter les scénarios menaçants. & Nbsp; L'ironie, bien sûr, est si vous espérez atteindre un semblant de sécurité, & nbsp; vous êtes arrivé à & nbsp; rester prêt à affronter ces & nbsp; très nbsp;mêmes menaces.
En tant que décideur pour votre organisation, vous le savez bien.Mais peu importe le nombre d'experts ou d'outils de cybersécurité de confiance, votre organisation a une garde debout,
There\'s a natural human desire to avoid threatening scenarios. The irony, of course, is if you hope to attain any semblance of security, you\'ve got to remain prepared to confront those very same threats. As a decision-maker for your organization, you know this well. But no matter how many experts or trusted cybersecurity tools your organization has a standing guard, |
Tool | ★★ | ||
| 2024-05-01 10:00:00 | Histoires du SOC & # 8211;Combattre les escroqueries «alertes de sécurité» Stories from the SOC – Combating “Security Alert” Scams (lien direct) |
Executive Summary
The “Security Alert” scam is a prevalent tech-support fraud that threatens both Windows and Apple users. It exploits the trust of users by masquerading as an official support site, using fake pop-up warnings to lure users into dialing scam phone numbers by conveying a sense of urgency. The ultimate goal is gaining remote access to the user’s system and pilfering personal data to extort money.
Combating a “Security Alert” scam is difficult on many fronts because most of the time attackers leverage newly registered domains, which means there is a lack of malicious OSINT (open-source intelligence), and they are able to bypass traditional detection methods. To gain remote access, attackers need the end user to call into a fraudulent support team to install a Remote Desktop Protocol (RDP) tool. An endpoint detection and response (EDR) tool might not catch the initial intrusion as such tools are also used for legitimate business reasons. The most successful way to combat phishing/scams is by end-user education and communication with the IT department.
In a recent incident, a fake “Microsoft Security Alert” domain targeted one of our Managed Endpoint Security with SentinelOne customers, causing alarm for the end users and IT staff, but fortunately, the end user did not fall into the trap of calling the fraudulent number.
The customer immediately contacted their assigned Threat Hunter for support and guidance, and the Threat Hunter was able to quickly utilize the security measures in place, locate multiple domains, and report them to the Alien Labs threat intelligence team.
AT&T Cybersecurity was one of the first cybersecurity companies to alert on the domains and share the information via the Open Threat Exchange (OTX) threat intelligence sharing community, helping other organizations protect against it.
Investigation
Initial Alarm Review
Indicators of Compromise (IOCs)
The initial security layers failed to raise alarms for several reasons. First, the firewalls did not block the domain because it was newly registered and therefore not yet on any known block lists. Second, the platform did not create any alarms because the domain’s SSL certificates were properly configured. Finally, the EDR tool did not alert because no downloads were initiated from the website. The first indication of an issue came from an end user who feared a hack and reported it to the internal IT team.
Utilizing the information provided by the end user, the Threat Hunter was able to locate the user\'s asset. Sniffing the URL data revealed a deceptive “Microsoft Security Alert” domain and a counterfeit McAfee website. These were detected largely because of improvements recommended during the customer\'s monthly meetings with the Threat Hunter, including a recommendation to activate the SentinelOne Deep Visibility browser extension, which is the tool that was instrumental in capturing URL information with greater accuracy after all the redirects.
 Figure I – Fake Microsoft Support page
Figure I – Fake Microsoft Support page
 Figure 2 – Fake McAfee page
Artifact (Indicator of Compromise) IOC Fake McAfee Page bavareafastrak[.]org Website Hosting Scam Pages Galaxytracke[.]com Zip file hash Tizer.zip - 43fb8fb69d5cbb8d8651af075059a8d96735a0d5
Figure 3 – Indicators of compromise
Expanded Investigation
Events Search
With the understanding that the e
Figure 2 – Fake McAfee page
Artifact (Indicator of Compromise) IOC Fake McAfee Page bavareafastrak[.]org Website Hosting Scam Pages Galaxytracke[.]com Zip file hash Tizer.zip - 43fb8fb69d5cbb8d8651af075059a8d96735a0d5
Figure 3 – Indicators of compromise
Expanded Investigation
Events Search
With the understanding that the e |
Hack Tool Threat | ★★ | ||
| 2024-05-01 05:12:14 | Quelle est la meilleure façon d'arrêter la perte de données Genai?Adopter une approche centrée sur l'homme What\\'s the Best Way to Stop GenAI Data Loss? Take a Human-Centric Approach (lien direct) |
Chief information security officers (CISOs) face a daunting challenge as they work to integrate generative AI (GenAI) tools into business workflows. Robust data protection measures are important to protect sensitive data from being leaked through GenAI tools. But CISOs can\'t just block access to GenAI tools entirely. They must find ways to give users access because these tools increase productivity and drive innovation. Unfortunately, legacy data loss prevention (DLP) tools can\'t help with achieving the delicate balance between security and usability. Today\'s release of Proofpoint DLP Transform changes all that. It provides a modern alternative to legacy DLP tools in a single, economically attractive package. Its innovative features help CISOs strike the right balance between protecting data and usability. It\'s the latest addition to our award-winning DLP solution, which was recognized as a 2024 Gartner® Peer Insights™ Customers\' Choice for Data Loss Prevention. Proofpoint was the only vendor that placed in the upper right “Customers\' Choice” Quadrant. In this blog, we\'ll dig into some of our latest research about GenAI and data loss risks. And we\'ll explain how Proofpoint DLP Transform provides you with a human-centric approach to reduce those risks. GenAI increases data loss risks Users can make great leaps in productivity with ChatGPT and other GenAI tools. However, GenAI also introduces a new channel for data loss. Employees often enter confidential data into these tools as they use them to expedite their tasks. Security pros are worried, too. Recent Proofpoint research shows that: Generative AI is the fastest-growing area of concern for CISOs 59% of board members believe that GenAI is a security risk for their business “Browsing GenAI sites” is one of the top five alert scenarios configured by companies that use Proofpoint Information Protection Valuable business data like mergers and acquisitions (M&A) documents, supplier contracts, and price lists are listed as the top data to protect A big problem faced by CISOs is that legacy DLP tools can\'t capture user behavior and respond to natural language processing-based user interfaces. This leaves security gaps. That\'s why they often use blunt tools like web filtering to block employees from using GenAI apps altogether. You can\'t enforce acceptable use policies for GenAI if you don\'t understand your content and how employees are interacting with it. If you want your employees to use these tools without putting your data security at risk, you need to take a human-centric approach to data loss. A human-centric approach stops data loss With a human-centric approach, you can detect data loss risk across endpoints and cloud apps like Microsoft 365, Google Workspace and Salesforce with speed. Insights into user intent allow you to move fast and take the right steps to respond to data risk. Proofpoint DLP Transform takes a human-centric approach to solving the security gaps with GenAI. It understands employee behavior as well as the data that they are handling. It surgically allows and disallows employees to use GenAI tools such as OpenAI ChatGPT and Google Gemini based on employee behavior and content inputs, even if the data has been manipulated or has gone through multiple channels (email, web, endpoint or cloud) before reaching it. Proofpoint DLP Transform accurately identifies sensitive content using classical content and LLM-powered data classifiers and provides deep visibility into user behavior. This added context enables analysts to reach high-fidelity verdicts about data risk across all key channels including email, cloud, and managed and unmanaged endpoints. With a unified console and powerful analytics, Proofpoint DLP Transform can accelerate incident resolution natively or as part of the security operations (SOC) ecosystem. It is built on a cloud-native architecture and features modern privacy controls. Its lightweight and highly stable user-mode agent is unique in | Tool Medical Cloud | ChatGPT | ★★★ | |
| 2024-04-30 19:13:26 | Résoudre le dilemme du service d'assistance avec p-dem Solving the Help Desk Dilemma with P-DEM (lien direct) |
> Une dure réalité pour les entreprises et les agents de l'entreprise d'Enterprise d'aujourd'hui qui dirigent les bureaux d'aide d'entreprise aujourd'hui sont dans une situation très difficile.Ils sont chargés de résoudre un volume considérablement accru de billets, mais n'ont pas la visibilité et les outils nécessaires pour le faire. & # 160;Dépassé et souvent incapable de faire leur travail efficacement, les professionnels de l'assistance [& # 8230;]
>A harsh reality for today\'s enterprise help desks Leaders and agents running enterprise help desks today are in a very tough spot. They are tasked with resolving a dramatically increased volume of tickets, yet lack the visibility and tools needed to do so. Overwhelmed and often unable to do their jobs effectively, help desk professionals […] |
Tool | ★★ | ||
| 2024-04-30 12:14:48 | Détection du vol de données du navigateur à l'aide des journaux d'événements Windows Detecting browser data theft using Windows Event Logs (lien direct) |
Publié par Will Harris, Chrome Security Team Le modèle de processus sandboxé de Chrome \\ de se défend bien contre le contenu Web malveillant, mais il existe des limites à la façon dont l'application peut se protéger des logiciels malveillants déjà sur l'ordinateur.Les cookies et autres informations d'identification restent un objectif de grande valeur pour les attaquants, et nous essayons de lutter contre cette menace continue de plusieurs manières, notamment en travaillant sur des normes Web comme dbsc Cela aidera à perturber l'industrie du vol de cookies car l'exfiltration de ces cookies n'aura plus de valeur. Lorsqu'il n'est pas possible d'éviter le vol d'identification et de cookies par malware, la prochaine meilleure chose est de rendre l'attaque plus observable par antivirus, d'agents de détection de terminaux ou d'administrateurs d'entreprise avec des outils d'analyse de journaux de base. Ce blog décrit un ensemble de signaux à utiliser par les administrateurs système ou les agents de détection de point de terminaison qui devraient signaler de manière fiable tout accès aux données protégées du navigateur d'une autre application sur le système.En augmentant la probabilité d'une attaque détectée, cela modifie le calcul pour les attaquants qui pourraient avoir un fort désir de rester furtif et pourraient les amener à repenser ces types d'attaques contre nos utilisateurs. arrière-plan Les navigateurs basés sur le chrome sur Windows utilisent le DPAPI (API de protection des données) pour sécuriser les secrets locaux tels que les cookies, le mot de passe, etc.La protection DPAPI est basée sur une clé dérivée des informations d'identification de connexion de l'utilisateur et est conçue pour se protéger contre l'accès non autorisé aux secrets des autres utilisateurs du système ou lorsque le système est éteint.Étant donné que le secret DPAPI est lié à l'utilisateur connecté, il ne peut pas protéger contre les attaques de logiciels malveillants locaux - l'exécution de logiciels malveillants en tant qu'utilisateur ou à un niveau de privilège plus élevé peut simplement appeler les mêmes API que le navigateur pour obtenir le secret DPAPI. Depuis 2013, Chromium applique l'indicateur CryptProtect_Audit aux appels DPAPI pour demander qu'un journal d'audit soit généré lorsque le décryptage se produit, ainsi que le marquage des données en tant que détenue par le navigateur.Parce que tout le stockage de données crypté de Chromium \\ est soutenu par une clé sécurisée DPAPI, toute application qui souhaite décrypter ces données, y compris les logiciels malveillants, devrait toujours générer de manière fiable un journal d'événements clairement observable, qui peut être utilisé pour détecter ces typesd'attaques. Il y a trois étapes principales impliquées dans le profit de ce journal: Activer la connexion sur l'ordinateur exécutant Google Chrome, ou tout autre navigateur basé sur le chrome. Exporter les journaux des événements vers votre système backend. Créer une logique de détection pour détecter le vol. Ce blog montrera également comment la journalisation fonctionne dans la pratique en la testant contre un voleur de mot de passe Python. Étape 1: Activer la connexion sur le système Les événements DPAPI sont connectés à deux endroits du système.Premièrement, il y a le 4693 Événement qui peut être connecté au journal de sécurité.Cet événement peut être activé en activant "Audit l'activité DPAPI" et les étapes pour ce faire sont d | Malware Tool Threat | ★★ | ||
| 2024-04-30 10:00:00 | Acquisition de données volatiles à partir de systèmes linux en direct: partie I Volatile Data Acquisition from Live Linux Systems: Part I (lien direct) |
The content of this post is solely the responsibility of the author. AT&T does not adopt or endorse any of the views, positions, or information provided by the author in this article.
In the domain of digital forensics, volatile data assumes a paramount role, characterized by its ephemeral nature. Analogous to fleeting whispers in a bustling city, volatile data in Linux systems resides transiently within the Random Access Memory (RAM), encapsulating critical system configurations, active network connections, running processes, and traces of user activities. Once a Linux machine powers down, this ephemeral reservoir of information dissipates swiftly, rendering it irretrievable.
Recognizing the significance of timely incident response and the imperative of constructing a detailed timeline of events, this blog embarks on an exhaustive journey, delineating a systematic approach fortified with best practices and indispensable tools tailored for the acquisition of volatile data within the Linux ecosystem.
Conceptually, volatile data serves as a mirror reflecting the real-time operational landscape of a system. It embodies a dynamic tapestry of insights, ranging from system settings and network connectivity to program execution and user interactions. However, the transient nature of this data necessitates proactive measures to capture and analyse it before it evaporates into the digital void.
In pursuit of elucidating this intricate process, we delve into a meticulous exploration, elucidating each facet with precision and clarity. Through a curated synthesis of established methodologies and cutting-edge tools, we equip forensic practitioners with the requisite knowledge and skills to navigate the complexities of volatile data acquisition in live Linux environments.
Join us as we unravel the intricacies of digital forensics, embark on a journey of discovery, and empower ourselves with the tools and techniques necessary to unlock the secrets concealed within live Linux systems.
Before proceeding, it\'s vital to grasp what volatile data encompasses and why it\'s so important in investigations:
System Essentials:
Hostname: Identifies the system ·
Date and Time: Contextualizes events ·
Timezone: Helps correlate activities across regions
Uptime: Reveals system state duration
Network Footprint:
Network Interfaces: Active connections and configurations
Open Ports: Potential entry points and services exposed
Active Connections: Shows live communication channels
Process Ecosystem:
Running Processes: Active programs and their dependencies
Process Memory: May uncover hidden execution or sensitive data
Open Files:
Accessed Files: Sheds light on user actions
Deleted Files: Potential evidence recovery point
Kernel Insights
Loaded Modules: Core extensions and potential rootkits
Kernel Ring Buffers (dmesg): Reveals driver or hardware events
User Traces
Login History: User activity tracking
Command History: Executed commands provide insights
Before diving into the acquisition process, it\'s essential to equip yourself with the necessary tools and commands for gathering volatile data effectively, for purpose of demonstration I will be using Linux Mint:
Hostname, Date, and Time:
hostname: Retrieves the system\'s hostname.
 date: Displays the current date and time.
date: Displays the current date and time.
|
Tool Technical | ★★★ | ||
| 2024-04-30 09:00:40 | Détection et réponse gérées en 2023 Managed Detection and Response in 2023 (lien direct) |
Le rapport couvre les tactiques, les techniques et les outils le plus souvent déployés par les acteurs de la menace, la nature des incidents détectés et leur distribution entre les clients MDR.
The report covers the tactics, techniques and tools most commonly deployed by threat actors, the nature of incidents detected and their distribution among MDR customers. |
Tool Threat | ★★ | ||
| 2024-04-30 08:16:53 | Conjuguer innovation, cybersécurité, IA et lancement de produit (lien direct) | La cybersécurité est incontestablement un sujet stratégique pour l'ensemble des entreprises et des structures publiques. Dans ce contexte, les concepteurs de technologies de cybersécurité se doivent d'innover en continu pour proposer des outils efficaces et évolutifs qui permettent à leurs clients d'évoluer dans une sphère de confiance. Custocy, éditeur toulousain spécialisé en IA appliquée à la cybersécurité, livre un retour d'expérience sur les actions qu'une start-up du secteur est amenée à mettre en (...) - Points de Vue | Tool | ★★ | ||
| 2024-04-30 03:02:40 | DMARC - La prochaine étape de l'hygiène et de la sécurité des e-mails DMARC - The Next Step in Email Hygiene and Security (lien direct) |
En 1971, Ray Tomlison a développé le premier service de courrier électronique tout en travaillant à la Defense Advanced Research Projects Agency (DARPA).Cette évolution a changé la façon dont nous avons communiqué.Cependant, même s'il s'agissait d'un outil exceptionnel, il n'était pas très convivial, obligeant les utilisateurs à avoir des logiciels spécifiques installés sur leurs ordinateurs.En 1996, Sabeer Bhatia a fondé Hotmail, ce qui en fait le premier service de messagerie électronique en ligne.Un an exactement après que Microsoft a acquis Hotmail, j'ai ouvert mon premier compte de messagerie.Je me souviens encore du sentiment d'euphorie qui venait de recevoir une réponse virtuelle au ...
In 1971, Ray Tomlison developed the first email service while working at The Defense Advanced Research Projects Agency (DARPA) . This development changed how we communicated. However, even though this was an exceptional tool, it was not very user-friendly, requiring users to have specific software installed on their computers. In 1996, Sabeer Bhatia founded Hotmail, making it the first web-based email messaging service. Exactly one year after Microsoft acquired Hotmail, I opened my first email account. I still remember the feeling of euphoria that came from receiving a virtual response to the... |
Tool | ★★★ | ||
| 2024-04-29 22:01:20 | Android malware hacks bancs comptes bancs avec de fausses invites à la mise à jour chromée Android Malware Hacks Bank Accounts With Fake Chrome Update Prompts (lien direct) |
Security researchers have discovered a new Android banking trojan that can steal users’ sensitive information and allow attackers to remotely control infected devices. “Brokewell is a typical modern banking malware equipped with both data-stealing and remote-control capabilities built into the malware,” Dutch security firm ThreatFabric said in an analysis published on Thursday. According to ThreatFabric, Brokewell poses a significant threat to the banking industry, providing attackers with remote access to all assets available through mobile banking. The malware was discovered by the researchers while investigating a fake Google Chrome web browser “update” page, commonly used by cybercriminals to lure victims into downloading and installing malware. Looking at prior campaigns, the researchers found that Brokewell was used to target a popular “buy now, pay later” financial service and an Austrian digital authentication application. The malware is said to be in active development, with new commands added almost daily to capture every event on the device, from keystrokes and information displayed on screen to text entries and apps launched by the victim. Once downloaded, Brokewell creates an overlay screen on a targeted application to capture user credentials. It can also steal browser cookies by launching its own WebView, overriding the onPageFinished method, and dumping the session cookies after the user completes the login process. “Brokewell is equipped with “accessibility logging,” capturing every event happening on the device: touches, swipes, information displayed, text input, and applications opened. All actions are logged and sent to the command-and-control server, effectively stealing any confidential data displayed or entered on the compromised device,” the ThreatFabric researchers point out. “It\'s important to highlight that, in this case, any application is at risk of data compromise: Brokewell logs every event, posing a threat to all applications installed on the device. This piece of malware also supports a variety of “spyware” functionalities: it can collect information about the device, call history, geolocation, and record audio.” After stealing the credentials, the attackers can initiate a Device Takeover attack using remote control capabilities to perform screen streaming. It also provides the threat actor with a range of various commands that can be executed on the controlled device, such as touches, swipes, and clicks on specified elements. ThreatFabric discovered that one of the servers used as a command and control (C2) point for Brokewell was also used to host a repository called “Brokewell Cyber Labs,” created by a threat actor called “Baron Samedit.” This repository comprised the source code for the “Brokewell Android Loader,” another tool from the same developer designed to bypass restrictions Google introduced in Android 13 and later to prevent exploitation of Accessibility Service for side-loaded apps (APKs). According to ThreatFabric, Baron Samedit has been active for at least two years, providing tools to other cybercriminals to check stolen accounts from multiple services, which could still be improved to support a malware-as-a-service operation. “We anticipate further evolution of this malware family, as we’ve already observed almost daily updates to the malware. Brokewell will likely be promoted on underground channels as a rental service, attracting the interest of other cybercriminals and sparking new campaigns targeting different regions,” the researchers conclude. Hence, the only way to effectively identify and prevent potential fraud from malware families like the newly discovered Brokewell is to use a comprehensive | Malware Tool Threat Mobile | ★★ | ||
| 2024-04-29 20:07:15 | De ransomware icedid à Dagon Locker en 29 jours From IcedID to Dagon Locker Ransomware in 29 Days (lien direct) |
## Instantané
Le rapport DFIR fournit un compte rendu détaillé d'une intrusion sophistiquée qui a commencé avec une campagne de phishing utilisant PromEthEustDS pour distribuer des logiciels malveillants icedid en août 2023.
## Description
Le malware icedid a établi la persistance, communiqué avec les serveurs C2 et a abandonné une balise de frappe de cobalt, qui a été utilisée pour le mouvement latéral, l'exfiltration des données et le déploiement des ransomwares.L'acteur de menace a également utilisé une suite d'outils tels que Rclone, NetScan, NBTScan, Anydesk, Seatt Libt, Sharefinder et Adfinind.L'intrusion a abouti au déploiement de ransomwares Dagon Locker après 29 jours.
Les acteurs de la menace ont utilisé diverses techniques pour obscurcir le fichier JavaScript et le coquille de cobalt grève, échapper à la détection, maintenir la persistance et effectuer des activités d'énumération du réseau.Les activités de l'acteur de menace comprenaient l'abus de fonctionnalités de mouvement latérale telles que le psexec et le protocole de bureau à distance (RDP), l'exfiltration des fichiers, le dumping et l'exfiltration des journaux d'événements de sécurité Windows et l'utilisation des commandes PowerShell exécutées à partir de la grève de Cobaltbalise.
De plus, l'acteur de menace a utilisé plusieurs techniques d'exfiltration, y compris l'utilisation de RClone et AWS CLI pour exfiltrer les données de l'infrastructure compromise.Le déploiement du ransomware Dagon Locker a été facilité par l'utilisation d'un script PowerShell personnalisé, AWScollector et un module Locker, avec une commande PowerShell spécifique exécutée à partir d'un contrôleur de domaine pour déployer le ransomware à différents systèmes.L'impact de cet incident a permis à tous les systèmes d'être affectés par les ransomwares Dagon Locker.
## Les références
[https://thedfirreport.com/2024/04/29/from-iced-to-dagon-locker-ransomware-in-29 days/-IDIDID-to-dagon-locker-ransomware en 29 jours /)
## Snapshot The DFIR report provides a detailed account of a sophisticated intrusion that began with a phishing campaign using PrometheusTDS to distribute IcedID malware in August 2023. ## Description The IcedID malware established persistence, communicated with C2 servers, and dropped a Cobalt Strike beacon, which was used for lateral movement, data exfiltration, and ransomware deployment. The threat actor also utilized a suite of tools such as Rclone, Netscan, Nbtscan, AnyDesk, Seatbelt, Sharefinder, and AdFind. The intrusion culminated in the deployment of Dagon Locker ransomware after 29 days. The threat actors employed various techniques to obfuscate the JavaScript file and the Cobalt Strike shellcode, evade detection, maintain persistence, and perform network enumeration activities. The threat actor\'s activities included the abuse of lateral movement functionalities such as PsExec and Remote Desktop Protocol (RDP), exfiltration of files, dumping and exfiltration of Windows Security event logs, and the use of PowerShell commands executed from the Cobalt Strike beacon. Additionally, the threat actor employed multiple exfiltration techniques, including the use of Rclone and AWS CLI to exfiltrate data from the compromised infrastructure. The deployment of the Dagon Locker ransomware was facilitated through the use of a custom PowerShell script, AWScollector, and a locker module, with a specific PowerShell command run from a domain controller to deploy the ransomware to different systems. The impact of this incident resulted in all systems being affected by the Dagon Locker ransomware. ## References [https://thedfirreport.com/2024/04/29/from-icedid-to-dagon-locker-ransomware-in-29-days/](https://thedfirreport.com/2024/04/29/from-icedid-to-dagon-locker-ransomware-in-29-days/) |
Ransomware Malware Tool Threat Technical | ★★★ | ||
| 2024-04-29 16:05:58 | Faits saillants hebdomadaires, 29 avril 2024 Weekly OSINT Highlights, 29 April 2024 (lien direct) |
## Snapshot Last week\'s OSINT reporting reveals a diverse range of cyber threats targeting organizations globally. The articles highlight various attack vectors, including phishing emails with malware payloads (SSLoad, [Cobalt Strike](https://security.microsoft.com/intel-profiles/fd8511c1d61e93d39411acf36a31130a6795efe186497098fe0c6f2ccfb920fc)), ransomware variants (KageNoHitobito, DoNex), and mobile banking malware (Brokewell) distributed through fake domain schemes and overlay attacks. Threat actors behind these campaigns range from financially motivated ransomware groups to sophisticated state-sponsored actors like Sandworm ([Seashell Blizzard](https://sip.security.microsoft.com/intel-profiles/cf1e406a16835d56cf614430aea3962d7ed99f01ee3d9ee3048078288e5201bb)) and UAT4356 ([Storm-1849](https://sip.security.microsoft.com/intel-profiles/f3676211c9f06910f7f1f233d81347c1b837bddd93292c2e8f2eb860a27ad8d5)). Targetted organizations span Europe, Asia, and the Americas and targetted industries include critical infrastructure and IT. ## Description 1. **[Ongoing FROZEN#SHADOW Phishing Campaign](https://security.microsoft.com/intel-explorer/articles/e39d9bb3)**: The FROZEN#SHADOW campaign utilizes phishing emails to distribute SSLoad malware, alongside [Cobalt Strike](https://security.microsoft.com/intel-profiles/fd8511c1d61e93d39411acf36a31130a6795efe186497098fe0c6f2ccfb920fc) and ConnectWise ScreenConnect for extensive persistence and remote access. The victim organizations, predominantly in Europe, Asia, and the Americas, are targeted via JavaScript file downloads and MSI installers connecting to attacker-controlled domains. 2. **[Insights on KageNoHitobito and DoNex Ransomware](https://security.microsoft.com/intel-explorer/articles/ff848e92)**: KageNoHitobito and DoNex are ransomware variants with distinct encryption methods and ransom note presentations. While KageNoHitobito prompts victims to negotiate through a TOR site, DoNex terminates specific services and processes, deletes shadow copies, and may be linked to DarkRace ransomware. 3. **[Brokewell Mobile Banking Malware](https://security.microsoft.com/intel-explorer/articles/99a5deee)**: Brokewell poses a significant threat to the banking industry, utilizing overlay attacks, spyware functionalities, and remote control capabilities to steal credentials and device information. The malware\'s active development and promotion on underground channels indicate a growing interest among cybercriminals targeting different regions. 4. **[Malvertising Campaign Targeting IT Teams with MadMxShell](https://security.microsoft.com/intel-explorer/articles/ffa6ca10)**: A sophisticated threat actor distributes the MadMxShell backdoor through fake domains, using Google Ads to push them to the top of search results. MadMxShell employs complex evasion techniques, including multi-stage injection and DNS tunneling for C2 communication, indicating an interest in targeting IT professionals for unauthorized access. 5. **[ArcaneDoor Campaign by UAT4356 (Storm-1849)](https://security.microsoft.com/intel-explorer/articles/a0cf0328)**: UAT4356 (tracked by Microsoft as [Storm-1949](https://sip.security.microsoft.com/intel-profiles/f3676211c9f06910f7f1f233d81347c1b837bddd93292c2e8f2eb860a27ad8d5)) targets perimeter network devices like Cisco Adaptive Security Appliances (ASA) with backdoors "Line Runner" and "Line Dancer" for reconnaissance and malicious actions. The campaign showcases a state-sponsored actor\'s advanced tradecraft, with deliberate efforts to evade forensics and exploit 0-day vulnerabilities. The initial access vector used in this campaign remains unidentified, but two vulnerabilities ([CVE-2024-20353](https://security.microsoft.com/intel-explorer/cves/CVE-2024-20353/description) and[CVE-2024-20359](https://security.microsoft.com/intel-explorer/cves/CVE-2024-20359/description)) were exploited. 6. **[Kapeka Backdoor Linked to Sandworm (Seashell Blizzard)](https://security.microsoft.com/intel-explorer/articles/364efa92)**: Kapeka (tracked by Microsoft as K | Ransomware Malware Tool Vulnerability Threat Mobile Industrial | ★★★ | ||
| 2024-04-29 11:59:47 | Comment nous avons combattu de mauvaises applications et de mauvais acteurs en 2023 How we fought bad apps and bad actors in 2023 (lien direct) |
Posted by Steve Kafka and Khawaja Shams (Android Security and Privacy Team), and Mohet Saxena (Play Trust and Safety) A safe and trusted Google Play experience is our top priority. We leverage our SAFE (see below) principles to provide the framework to create that experience for both users and developers. Here\'s what these principles mean in practice: (S)afeguard our Users. Help them discover quality apps that they can trust. (A)dvocate for Developer Protection. Build platform safeguards to enable developers to focus on growth. (F)oster Responsible Innovation. Thoughtfully unlock value for all without compromising on user safety. (E)volve Platform Defenses. Stay ahead of emerging threats by evolving our policies, tools and technology. With those principles in mind, we\'ve made recent improvements and introduced new measures to continue to keep Google Play\'s users safe, even as the threat landscape continues to evolve. In 2023, we prevented 2.28 million policy-violating apps from being published on Google Play1 in part thanks to our investment in new and improved security features, policy updates, and advanced machine learning and app review processes. We have also strengthened our developer onboarding and review processes, requiring more identity information when developers first establish their Play accounts. Together with investments in our review tooling and processes, we identified bad actors and fraud rings more effectively and banned 333K bad accounts from Play for violations like confirmed malware and repeated severe policy violations. Additionally, almost 200K app submissions were rejected or remediated to ensure proper use of sensitive permissions such as background location or SMS access. To help safeguard user privacy at scale, we partnered with SDK providers to limit sensitive data access and sharing, enhancing the privacy posture for over 31 SDKs impacting 790K+ apps. We also significantly expanded the Google Play SDK Index, which now covers the SDKs used in almost 6 million apps across the Android ecosystem. This valuable resource helps developers make better SDK choices, boosts app quality and minimizes integration risks. Protecting the Android Ecosystem Building on our success with the App Defense Alliance (ADA), we partnered with Microsoft and Meta as steering committee members in the newly restructured ADA under the Joint Development Foundation, part of the Linux Foundation family. The Alliance will support industry-wide adoption of app security best practices and guidelines, as well as countermeasures against emerging security risks. Additionally, we announced new Play Store transparency labeling to highlight VPN apps that have completed an independent security review through App Defense Alliance\'s Mobile App Security Assessment (MASA). When a user searches for VPN apps, they will now see a banner at the top of Google Play that educates them about the “Independent security review” badge in the Data safety section. This helps users see at-a-glance that a developer has prioritized security and privacy best practices and is committed to user safety. | Malware Tool Threat Mobile | ★★★ | ||
| 2024-04-28 19:22:00 | Okta met en garde contre une augmentation sans précédent des attaques de rembourrage des diplômes axés sur la procuration Okta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks (lien direct) |
Le fournisseur de services de gestion de l'identité et de l'accès (IAM), Okta, a mis en garde contre un pic dans la "fréquence et l'échelle" des attaques de bourrage d'identification destinées aux services en ligne.
Ces attaques sans précédent, observées au cours du dernier mois, seraient facilitées par "la grande disponibilité des services de proxy résidentiel, des listes d'identification précédemment volées (\\ 'Listtes combo \') et des outils de script," les outils de script "
Identity and access management (IAM) services provider Okta has warned of a spike in the "frequency and scale" of credential stuffing attacks aimed at online services. These unprecedented attacks, observed over the last month, are said to be facilitated by "the broad availability of residential proxy services, lists of previously stolen credentials (\'combo lists\'), and scripting tools," the |
Tool | ★★★ | ||
| 2024-04-26 22:25:37 | Plate-forme de cybersécurité Cybersecurity Platformization (lien direct) |
> La plate-forme présente l'occasion de moderniser et de simplifier la sécurité en effectuant un examen de tous les outils de cybersécurité et en recherchant des moyens de consolider.
>Platformization presents an opportunity to modernize and simplify security by doing a review of all cybersecurity tools and looking for ways to consolidate. |
Tool | ★★ | ||
| 2024-04-26 19:12:08 | Todckat APT Group Honne les tactiques d'expiltration des données, exploite les outils légitimes ToddyCat APT Group Hones Data Exfiltration Tactics, Exploits Legitimate Tools (lien direct) |
#### Targeted Geolocations - Oceania - Southeast Asia - South Asia - East Asia - Central Asia #### Targeted Industries - Government Agencies & Services - Defense ## Snapshot Kaspersky reports the APT group ToddyCat has been observed targeting governmental organizations, particularly defense-related ones in the Asia-Pacific region, with the goal of stealing sensitive information on an industrial scale. ## Description They employ various tools and techniques, including traffic tunneling and the creation of reverse SSH tunnels, to maintain constant access to compromised infrastructure. The attackers utilize disguised OpenSSH private key files, execute scripts to modify folder permissions, create SSH tunnels to redirect network traffic, and employ the SoftEther VPN package to potentially facilitate unauthorized access and data exfiltration. Additionally, they use various files and techniques, such as concealing file purposes, copying files through shared resources, and tunneling to legitimate cloud providers, to gain access to victim hosts and evade detection. The threat actors initially gain access to systems by installing servers, modifying server settings, and utilizing tools like Ngrok and Krong to redirect C2 traffic and create tunnels for unauthorized access. They also employ the FRP client, a data collection tool named "cuthead", and a tool called "WAExp" to search for and collect browser local storage files containing data from the web version of WhatsApp. The attackers demonstrate a sophisticated and evolving approach to data collection and exfiltration, utilizing multiple tools and techniques to achieve their objectives. ## Recommendations Microsoft recommends the following mitigations to reduce the impact of Information stealer threats. - Check your Office 365 email filtering settings to ensure you block spoofed emails, spam, and emails with malware. Use [Microsoft Defender for Office 365](https://learn.microsoft.com/microsoft-365/security/office-365-security/defender-for-office-365?ocid=magicti_ta_learndoc) for enhanced phishing protection and coverage against new threats and polymorphic variants. Configure Microsoft Defender for Office 365 to [recheck links on click](https://learn.microsoft.com/microsoft-365/security/office-365-security/safe-links-about?ocid=magicti_ta_learndoc) and [delete sent mail](https://learn.microsoft.com/microsoft-365/security/office-365-security/zero-hour-auto-purge?ocid=magicti_ta_learndoc) in response to newly acquired threat intelligence. Turn on [safe attachments policies](https://learn.microsoft.com/microsoft-365/security/office-365-security/safe-attachments-policies-configure?ocid=magicti_ta_learndoc) to check attachments to inbound email. - Encourage users to use Microsoft Edge and other web browsers that support SmartScreen, which identifies and blocks malicious websites, including phishing sites, scam sites, and sites that host malware. - Turn on [cloud-delivered protection](https://learn.microsoft.com/microsoft-365/security/defender-endpoint/configure-block-at-first-sight-microsoft-defender-antivirus?ocid=magicti_ta_learndoc) in Microsoft Defender Antivirus, or the equivalent for your antivirus product, to cover rapidly evolving attacker tools and techniques. Cloud-based machine learning protections block a majority of new and unknown variants. - Enforce MFA on all accounts, remove users excluded from MFA, and strictly [require MFA](https://learn.microsoft.com/azure/active-directory/identity-protection/howto-identity-protection-configure-mfa-policy?ocid=magicti_ta_learndoc) from all devices, in all locations, at all times. - Enable passwordless authentication methods (for example, Windows Hello, FIDO keys, or Microsoft Authenticator) for accounts that support passwordless. For accounts that still require passwords, use authenticator apps like Microsoft Authenticator for MFA. [Refer to this article](https://learn.microsoft.com/azure/active-directory/authentic | Ransomware Spam Malware Tool Threat Industrial Cloud | ★★ | ||
| 2024-04-26 18:33:10 | Accélération de la réponse aux incidents en utilisant une AI générative Accelerating incident response using generative AI (lien direct) |
Lambert Rosique and Jan Keller, Security Workflow Automation, and Diana Kramer, Alexandra Bowen and Andrew Cho, Privacy and Security Incident Response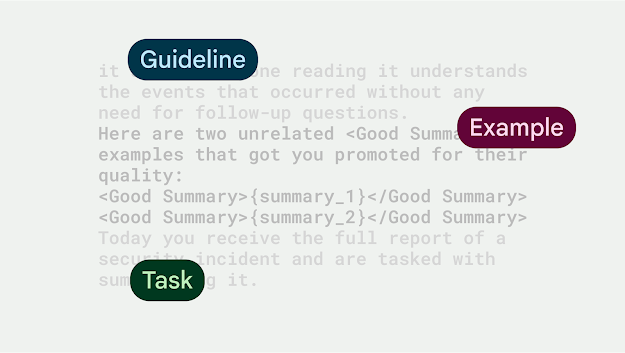 IntroductionAs security professionals, we\'re constantly looking for ways to reduce risk and improve our workflow\'s efficiency. We\'ve made great strides in using AI to identify malicious content, block threats, and discover and fix vulnerabilities. We also published the Secure AI Framework (SAIF), a conceptual framework for secure AI systems to ensure we are deploying AI in a responsible manner. Today we are highlighting another way we use generative AI to help the defenders gain the advantage: Leveraging LLMs (Large Language Model) to speed-up our security and privacy incidents workflows. IntroductionAs security professionals, we\'re constantly looking for ways to reduce risk and improve our workflow\'s efficiency. We\'ve made great strides in using AI to identify malicious content, block threats, and discover and fix vulnerabilities. We also published the Secure AI Framework (SAIF), a conceptual framework for secure AI systems to ensure we are deploying AI in a responsible manner. Today we are highlighting another way we use generative AI to help the defenders gain the advantage: Leveraging LLMs (Large Language Model) to speed-up our security and privacy incidents workflows. |
Tool Threat Industrial Cloud | ★★★ | ||
| 2024-04-26 17:23:14 | Ransomware Roundup - KageNoHitobito and DoNex (lien direct) | #### Géolocations ciblées - Chili - Chine - Cuba - Allemagne - L'Iran - Lituanie - Pérou - Roumanie - Royaume-Uni - États-Unis - Taïwan - Suède - Belgique - Tchéchie - Italie - Pays-Bas ## Instantané La recherche sur les menaces Fortiguard Labs fournit un aperçu des variantes de ransomware Kagenohitobito et Donex.Kagenohitobito a émergé fin mars 2024 et chiffre les fichiers victimes de victimes, tandis que Donex est un groupe de ransomware à motivation financière qui crypte les fichiers sur les lecteurs locaux et les parts de réseau.Les méthodes d'infiltration initiales utilisées par les acteurs de la menace ne sont pas spécifiées. ## Description Kagenohitobito affiche une note de rançon sur le bureau de la victime et demande aux victimes de visiter un site Tor pour les négociations de rançon, tandis que Donex ajoute un identifiant de victime comme extension de fichier aux fichiers affectés, modifie leurs icônes et met fin aux processus et services spécifiques en tant que services en tant que services spécifiques en tant que servicesSelon le fichier de configuration défini par l'acteur de menace.L'article suggère également une connexion possible entre les ransomwares Donex et DarkRace, car ils partagent des similitudes dans les notes de rançon et les fichiers de configuration.DOTYX est configuré pour supprimer des copies d'ombre, ce qui rend la récupération du fichier difficile. ## Recommandations Étant donné que la majorité des ransomwares sont livrés via le phishing, Microsoft recommande les atténuations suivantes pour réduire l'impact de cette menace.Vérifiez la carte de recommandations pour l'état de déploiement des atténuations surveillées. - Pilot et déploiement [méthodes d'authentification résistantes au phishing] (https://learn.microsoft.com/en-us/entra/identity/authentication/concept-authentication-methods?ocid=Magicti_TA_Learndoc) pour les utilisateurs. - Configurez Microsoft Defender pour Office 365 à [Rechercher les liens sur Click] (ReCHECK% 20LINKS% 20ON% 20CLICK).Safe Links fournit une analyse et une réécriture des URL des e-mails entrants dans le flux de messagerie et une vérification du temps de clic des URL et des liens dans les e-mails, d'autres applications Microsoft 365 telles que des équipes et d'autres emplacements tels que SharePoint Online.La numérisation des liens sûrs se produit en plus de la [anti-spam] régulière (https://learn.microsoft.com/en-us/defenderofice-365/anti-spam-protection-about?ocid=Magicti_ta_learndoc) et [anti-Malware] (https://learn.microsoft.com/en-us/defender-office-365/anti-malware-protection-about?ocid=magicti_ta_learndoc) Protection dans les messages e-mail entrants dans Microsoft Exchange en ligne Protection en ligne (EOP).La numérisation des liens sûrs peut aider à protéger votre organisation contre les liens malveillants utilisés dans le phishing et d'autres attaques. - Encouragez les utilisateurs à utiliser Microsoft Edge et d'autres navigateurs Web qui prennent en charge [Microsoft Defender SmartScreen] (https://learn.microsoft.com/en-us/deployedge/microsoft-edge-security-smartscreen?ocid=magicti_ta_learndoc), qui s'identifie, qui identifie)et bloque des sites Web malveillants, y compris des sites de phishing, des sites d'arnaque et des sites qui hébergent des logiciels malveillants. - Allumez [protection en livraison du cloud] (https://learn.miqueCouvrir les outils et techniques d'attaque en évolution rapide.Les protections d'apprentissage automatique basées sur le cloud bloquent une majorité de variantes nouvelles et inconnues. - Exécuter [Détection et réponse Endpoint (EDR)] (https://learn.microsoft.com/en-us/defender-endpoint/edr-in-lock-mode?ocid=Magicti_TA_LearnDoc) en mode bloc, de sorte que le défenseur MicrosoftPour le point final, peut bloquer les artefacts malveillants, même lorsque votre antivirus non microsoft ne détecte pas la menace ou lorsque Microsoft Defender Antivirus fonctio | Ransomware Malware Tool Threat | ★★ | ||
| 2024-04-26 16:20:45 | Les outils de suivi du site Web de Kaiser \\ ont peut-être compromis des données sur 13 millions de clients Kaiser\\'s website tracking tools may have compromised data on 13 million customers (lien direct) |
#### Géolocations ciblées - Chili - Chine - Cuba - Allemagne - L'Iran - Lituanie - Pérou - Roumanie - Royaume-Uni - États-Unis - Taïwan - Suède - Belgique - Tchéchie - Italie - Pays-Bas ## Instantané La recherche sur les menaces Fortiguard Labs fournit un aperçu des variantes de ransomware Kagenohitobito et Donex.Kagenohitobito a émergé fin mars 2024 et chiffre les fichiers victimes de victimes, tandis que Donex est un groupe de ransomware à motivation financière qui crypte les fichiers sur les lecteurs locaux et les parts de réseau.Les méthodes d'infiltration initiales utilisées par les acteurs de la menace ne sont pas spécifiées. ## Description Kagenohitobito affiche une note de rançon sur le bureau de la victime et demande aux victimes de visiter un site Tor pour les négociations de rançon, tandis que Donex ajoute un identifiant de victime comme extension de fichier aux fichiers affectés, modifie leurs icônes et met fin aux processus et services spécifiques en tant que services en tant que services spécifiques en tant que servicesSelon le fichier de configuration défini par l'acteur de menace.L'article suggère également une connexion possible entre les ransomwares Donex et DarkRace, car ils partagent des similitudes dans les notes de rançon et les fichiers de configuration.DOTYX est configuré pour supprimer des copies d'ombre, ce qui rend la récupération du fichier difficile. ## Recommandations Étant donné que la majorité des ransomwares sont livrés via le phishing, Microsoft recommande les atténuations suivantes pour réduire l'impact de cette menace.Vérifiez la carte de recommandations pour l'état de déploiement des atténuations surveillées. - Pilot et déploiement [méthodes d'authentification résistantes au phishing] (https://learn.microsoft.com/en-us/entra/identity/authentication/concept-authentication-methods?ocid=Magicti_TA_Learndoc) pour les utilisateurs. - Configurez Microsoft Defender pour Office 365 à [Rechercher les liens sur Click] (ReCHECK% 20LINKS% 20ON% 20CLICK).Safe Links fournit une analyse et une réécriture des URL des e-mails entrants dans le flux de messagerie et une vérification du temps de clic des URL et des liens dans les e-mails, d'autres applications Microsoft 365 telles que des équipes et d'autres emplacements tels que SharePoint Online.La numérisation des liens sûrs se produit en plus de la [anti-spam] régulière (https://learn.microsoft.com/en-us/defenderofice-365/anti-spam-protection-about?ocid=Magicti_ta_learndoc) et [anti-Malware] (https://learn.microsoft.com/en-us/defender-office-365/anti-malware-protection-about?ocid=magicti_ta_learndoc) Protection dans les messages e-mail entrants dans Microsoft Exchange en ligne Protection en ligne (EOP).La numérisation des liens sûrs peut aider à protéger votre organisation contre les liens malveillants utilisés dans le phishing et d'autres attaques. - Encouragez les utilisateurs à utiliser Microsoft Edge et d'autres navigateurs Web qui prennent en charge [Microsoft Defender SmartScreen] (https://learn.microsoft.com/en-us/deployedge/microsoft-edge-security-smartscreen?ocid=magicti_ta_learndoc), qui s'identifie, qui identifie)et bloque des sites Web malveillants, y compris des sites de phishing, des sites d'arnaque et des sites qui hébergent des logiciels malveillants. - Allumez [protection en livraison du cloud] (https://learn.miqueCouvrir les outils et techniques d'attaque en évolution rapide.Les protections d'apprentissage automatique basées sur le cloud bloquent une majorité de variantes nouvelles et inconnues. - Exécuter [Détection et réponse Endpoint (EDR)] (https://learn.microsoft.com/en-us/defender-endpoint/edr-in-lock-mode?ocid=Magicti_TA_LearnDoc) en mode bloc, de sorte que le défenseur MicrosoftPour le point final, peut bloquer les artefacts malveillants, même lorsque votre antivirus non microsoft ne détecte pas la menace ou lorsque Microsoft Defender Antivirus fonctio | Tool | ★★★ | ||
| 2024-04-26 13:00:25 | 7 Essentials Chaque gestion de la posture de sécurité des données (DSPM) doit avoir 7 Essentials Every Data Security Posture Management (DSPM) Must Have (lien direct) |
> Un effet secondaire intéressant de la prolifération du développement de logiciels natifs du cloud est les lignes floues entre les rôles des équipes Infosec et DevOps pour protéger les données de l'application et des utilisateurs.Jusqu'à récemment, DevSecops consistait principalement à sécuriser et à protéger le code, les outils utilisés dans le SDLC et l'infrastructure des applications \\ 'contre les vulnérabilités, les fuites et les erreurs de configuration potentiels.Aujourd'hui, les données sensibles ne vit plus dans des bases de données sécurisées et centralisées.Au lieu de cela, il est dispersé dans des instances fluides et amorphes sur diverses plates-formes cloud et hybrides, ce qui rend le problème de la protection des données.Si vous regardez les chiffres, l'état de la sécurité des données aujourd'hui est carrément terrifiant.[& # 8230;]
>An interesting side-effect of the proliferation of cloud-native software development is the blurred lines between the roles of InfoSec and DevOps teams in protecting application and user data. Until recently, DevSecOps was mostly about securing and protecting the code, the tools used in the SDLC, and the applications\' infrastructure from potential vulnerabilities, leaks, and misconfigurations. Today, sensitive data no longer lives in secure and centralized databases. Instead, it\'s scattered in fluid and amorphic instances on various cloud and hybrid platforms, making data protection everyone\'s problem. If you look at the numbers, the state of data security today is downright terrifying. […] |
Tool Vulnerability Cloud | ★★★ | ||
| 2024-04-25 16:43:00 | Menaces de réseau: une démonstration d'attaque étape par étape Network Threats: A Step-by-Step Attack Demonstration (lien direct) |
Suivez cette simulation d'attaque de réseau réelle, couvrant & nbsp; 6 & nbsp; étapes de l'accès initial à l'exfiltration des données.Voyez comment les attaquants restent non détectés avec les outils & nbsp; simples & nbsp; et pourquoi vous avez besoin de plusieurs points d'étranglement dans votre stratégie de défense.
Étonnamment, la plupart des attaques de réseaux ne sont pas exceptionnellement sophistiquées, technologiquement avancées ou dépendent d'outils zéro jour qui exploitent
Follow this real-life network attack simulation, covering 6 steps from Initial Access to Data Exfiltration. See how attackers remain undetected with the simplest tools and why you need multiple choke points in your defense strategy. Surprisingly, most network attacks are not exceptionally sophisticated, technologically advanced, or reliant on zero-day tools that exploit |
Tool Vulnerability Threat | ★★ | ||
| 2024-04-25 14:31:25 | J & J spin-off CISO sur la maximisation de la cybersécurité J&J Spin-Off CISO on Maximizing Cybersecurity (lien direct) |
Comment le CISO de Kenvue, une entreprise de soins de santé grand public, a été transféré de Johnson &Johnson, outils combinés et nouvelles idées pour construire le programme de sécurité.
How the CISO of Kenvue, a consumer healthcare company spun out from Johnson & Johnson, combined tools and new ideas to build out the security program. |
Tool Medical | ★★ | ||
| 2024-04-25 13:59:36 | NDR dans le paysage moderne de la cybersécurité NDR in the Modern Cybersecurity Landscape (lien direct) |
> Par uzair amir
Le rôle de la détection et de la réponse du réseau (NDR) dans la cybersécurité.Apprenez comment les outils NDR permettent aux organisations de lutter contre les menaces évolutives efficacement.
Ceci est un article de HackRead.com Lire le post original: NDR dans le paysage moderne de la cybersécurité
>By Uzair Amir The role of Network Detection and Response (NDR) in cybersecurity. Learn how NDR tools empower organizations to tackle evolving threats effectively. This is a post from HackRead.com Read the original post: NDR in the Modern Cybersecurity Landscape |
Tool | ★★ | ||
| 2024-04-25 11:58:40 | AI-driven cyber attacks to be the norm within a year, say security leaders (lien direct) | Netacea, le spécialiste de la détection et de la réponse des bots, a annoncé aujourd'hui de nouvelles recherches sur la menace des cyberattaques axées sur l'IA.Il constate que la plupart des entreprises voient rapidement «l'IA offensive» devenir rapidement un outil standard pour les cybercriminels, avec 93% des chefs de sécurité s'attendant à faire face à des attaques quotidiennes basées sur l'IA.La recherche, la cybersécurité à l'ère de l'IA offensive, interrogé la sécurité [& # 8230;]
Le message Cyber Attacks dirigés par AI sont la norme dans un an, disons les leaders de la sécurité a>.
Netacea, the bot detection and response specialist, today announced new research into the threat of AI-driven cyberattacks. It finds that most businesses see “offensive AI” fast becoming a standard tool for cybercriminals, with 93% of security leaders expecting to face daily AI-driven attacks. The research, Cyber security in the age of offensive AI, surveyed security […] The post AI-driven cyber attacks to be the norm within a year, say security leaders first appeared on IT Security Guru. |
Tool Threat | ★★ | ||
| 2024-04-24 19:34:05 | Arcaneroor - Nouvelle campagne axée sur l'espionnage a trouvé des dispositifs de réseau de périmètre ciblant ArcaneDoor - New Espionage-Focused Campaign Found Targeting Perimeter Network Devices (lien direct) |
## Instantané
Cisco Talos rend compte de la campagne ArcaneDoor, attribuée à l'acteur parrainé par l'État UAT4356 (suivi par Microsoft en tant que Storm-1849), cible les appareils de réseau périmètre de plusieurs fournisseurs, en particulier les appareils de sécurité adaptatifs Cisco (ASA).
Microsoft suit cet acteur en tant que Storm-1849, [en savoir plus ici.] (Https://sip.security.microsoft.com/intel-profiles/f3676211c9f06910f7f1f233d81347c1b837bddd93292c2e8f2eb860a27ad8d5)
## Description
Ces appareils sont cruciaux pour le flux de données dans et hors des réseaux, ce qui les rend idéaux pour les campagnes axées sur l'espionnage.L'UAT4356 a déployé deux baignoires, "Line Runner" et "Line Dancer", pour mener des actions malveillantes telles que la modification de la configuration, la reconnaissance, la capture / exfiltration du trafic réseau et les mouvements potentiellement latéraux.Le vecteur d'accès initial utilisé dans cette campagne reste non identifié, mais deux vulnérabilités (CVE-2024-20353 et CVE-2024-20359) ont été exploitées.
L'acteur a démontré un accent clair sur l'espionnage et une connaissance approfondie des dispositifs ciblés, indiquant une activité sophistiquée parrainée par l'État.Le calendrier de la campagne suggère que l'infrastructure contrôlée par l'acteur était active au début de novembre 2023, la plupart des activités se déroulant entre décembre 2023 et début janvier 2024.
L'implant "Line Dancer", un interprète ShellCode résident à la mémoire, permet aux adversaires de télécharger et d'exécuter des charges utiles de shellcode arbitraires sur les périphériques ASA compromis.Il permet aux acteurs de menace de désactiver les commandes syslog, exécuter et exfiltrater, créer et exfiltrater les captures de paquets et exécuter les commandes CLI, entre autres actions.
La porte dérobée "Line Runner", en revanche, maintient la persistance sur les appareils ASA compromis en tirant parti d'une capacité héritée qui permet la précharge de clients VPN et de plugins.
L'UAT4356 a pris des mesures délibérées pour prévenir la capture médico-légale des artefacts malveillants, y compris les capacités anti-forensiques et anti-analyse.Le niveau élevé de la campagne, le développement des capacités et l'exploitation des vulnérabilités de 0 jour indiquent un acteur parrainé par l'État.
## Recommandations
Microsoft recommande les atténuations suivantes pour réduire l'impact de l'activité associée au Storm-1849.
- durcir les actifs orientés Internet et identifier et sécuriser les systèmes de périmètre que les attaquants pourraient utiliser pour accéder à votre réseau.
- Encouragez les utilisateurs à utiliser Microsoft Edge et d'autres navigateurs Web qui prennent en charge SmartScreen, qui identifie et bloque des sites Web malveillants, y compris des sites de phishing, des sites d'arnaque et des sites contenant des exploits et hébergent des logiciels malveillants.
- Allumez la protection livrée par le cloud dans Microsoft Defender Antivirus ou l'équivalent pour que votre produit antivirus couvre des outils et techniques d'attaquant en évolution rapide.Les protections d'apprentissage automatique basées sur le cloud bloquent une majorité de variantes nouvelles et inconnues.
## Les références
[https://blog.talosintelligence.com/arcaneroor-new-espionage-foccused-campaign-found-targeting-perimeter-network-devices/-Campaign-Found-Targeting-Périmètre-Network-Devices /)
## Snapshot Cisco Talos reports on the ArcaneDoor campaign, attributed to the state-sponsored actor UAT4356 (Tracked by Microsoft as Storm-1849), targets perimeter network devices from multiple vendors, particularly Cisco Adaptive Security Appliances (ASA). Microsoft tracks this actor as Storm-1849, [read more about them here.](https://sip.security.microsoft.com/intel-profiles/f3676211c9f06910f7f1f233d81347c1b837bddd93292c2e8f2eb860a27ad8d5) # |
Malware Tool Vulnerability Threat | ★★★ | ||
| 2024-04-24 14:51:27 | Falcon Fund in Focus: Nagomi aide les clients à maximiser leurs investissements en cybersécurité Falcon Fund in Focus: Nagomi Helps Customers Maximize Their Cybersecurity Investments (lien direct) |
Les violations évitables sont un problème courant.Selon des recherches de Nagomi, un leader dans le domaine naissant de l'évaluation automatisée du contrôle de la sécurité, 80% des organisations violées avaient déjà un outil en place qui aurait pu l'empêcher.Une solution consiste à maximiser l'utilisation des outils de sécurité qu'ils ont déjà.De nombreuses entreprises se débattent avec inefficaces [& # 8230;]
Preventable breaches are a common problem. According to research by Nagomi, a leader in the nascent field of automated security control assessment, 80% of breached organizations already had a tool in place that could have prevented it. One solution is to maximize the use of security tools they already have. Many enterprises grapple with ineffective […] |
Tool | ★★ |
To see everything:
Our RSS (filtrered)
