What's new arround internet
| Src | Date (GMT) | Titre | Description | Tags | Stories | Notes |
| 2021-07-14 10:00:00 | Meaningful security metrics (lien direct) | Security metrics are vital for you as a security leader to track the progress of your security program and have effective risk-focused conversations with business and operations stakeholders. Security metrics pave the way for security initiatives, facilitate resource, help communicate resource allocation and help communicate results with relevant stakeholders throughout the organization. Today security functions are expected to plan and track contributions to the business to enable strategic alignment to win and retain customers. Security metrics should help you do your job better and demonstrate to business leadership that you’re doing a good job of managing security. You can hone your existing security metrics so that they are more meaningful and demonstrate actual value to business stakeholders. Despite growing interest in meaningful security metrics, organizations globally continue to find it a challenging task. CISO’s can find it challenging to define security metrics, as there are no off-the-shelf standard metrics that would suit every organization. There are no established standard templates on what should be measured. Principles for enhancing existing security metrics You may reach out to Cybersecurity consulting organizations for help implementing industry standards and vertical-specific requirements, along with their experience in establishing and growing information security risk management combined with security metric reporting. Your consultant can review existing information security metrics so that existing / defined information security metrics align with the current technical landscape and threat environment considering the following principles. Review categorization of metrics for comprehensiveness: Examine the current functional categorization for comprehensiveness and framework alignment considering security and compliance requirements (e.g. PCI, HIPAA, FRB), in the light of current applicable regulatory, legislative and industry best practices. Consider metrics concerning the chosen framework for security management. Review individual metrics for holistic risk representation: Review existing metrics for suitable attributes such as effectiveness, efficiency, coverage, compliance, timing, cost, and process maturity. This step would help the stakeholder understand the specific risk exposure and quantifiably measure each security metric. For meaningful insight, each metric should have an appropriate unit of measurement. Measurement can be qualitative, quantitative, or binary depending upon the kind of metric. Review security metrics lifecycle: Review existing metrics for their continued relevance at least annually. In areas where metrics have been successful in driving maturity, recommendations should be made to modify metrics or enhance the thresholds. Determine whether metrics need to be modified based upon change in overall program maturity, changes in underlying technologies, threats, risks and/or regulations. Review security metrics for context, reliability, and credibility: Use metrics to provide the necessary context, reliability, and credibility by looking into the availability of supporting data and explanatory notes where needed. You should also clearly articulate the definition of the metric– your audience needs to understand what is being measured, its business impact, and the meaning of the metric (quantitative/qualitative) - and not just present data in isolation, leaving the audience to interpret the measure or what is the risk / exposure involved. Review action orientation of metrics: Don’t just rely on numbers. Interpret insights to help provide actionable recommendations. If the required actions are not made explicit, reporting will not serve its purpose. Be sure that metrics provide adequate information to | Threat Guideline | |||
| 2021-07-13 10:00:00 | Best practices for a secure ecommerce website (lien direct) | This blog was written by an independent guest blogger. Ecommerce is a popular business model. Many people are getting into this business and looking for ways to secure early retirement from typical 9 to 5 jobs. With the right ideas and execution, there is a good chance that this will happen, but making it in eCommerce isn’t that easy as it was in the past. Yes, there are more options than ever in terms of delivery, logistics, storage, and creating an online store. However, there is a lot more competition, and everyone is looking for new ways to enhance their services and bring in more customers. Online businesses are also dealing with increased cybersecurity threats. In fact, it’s been argued that 29% of traffic on ecommerce sites are people with malicious intentions. It’s an issue you must tackle if you want to achieve your business goals. Luckily, there are a lot of ways you can boost your security. Find a reliable ecommerce platform When starting an ecommerce site, the first thing you notice is that there are many ecommerce platforms available. However, many people don’t even consider security when choosing their platform or hosting provider. Both the platform and the host you choose have a significant impact on your site’s security. They use a variety of security measures and features that make your store safer. In general, they should at least offer protection from SQL injections and malware since they are common attacks. Take the time to look at what different platforms and hosts have to offer. Choose HTTPS and SSL HTTPS is short for “Hypertext Transfer Protocol Secure”, and this protocol is designed for establishing secure communications online. HTTPS sites are considered secure and unique because they have certification. In other words, a site that has the “green lock” is authentic, and it isn’t a fake page. For HTTPS to be enabled, a site needs an SSL certificate or Secure Socket Layer. This system helps protect the data going between a buyer and your ecommerce store. Apart from improving security, SSL also brings in more customers as many people avoid stores without it. Do regular backups Accidents and attacks are sometimes unavoidable, but backups help you get your site back online quickly. Whether an update has created an issue with your site or someone has used malicious software – you can’t let your store stay offline. Even the best cybersecurity experts can’t guarantee that your website will be 100% secure. That’s why regular backups are necessary – backing up your site means downloading your whole site and creating a duplicate. If something happens, you can upload this duplicate and get your site back online. Ideally, your hosting provider should offer daily backups as well. Get PCI compliant Lots of people are reluctant to give their bank or credit card details online. They have the right to be sceptical because there have been many cases of this information falling into the wrong hands. That’s why ecommerce websites should attain PCI compliance. | Malware Vulnerability | |||
| 2021-07-12 10:00:00 | Back to the office… (lien direct) | As the world is starting to move out of lockdown, businesses are moving some of their workforce back into the office environment. Whilst their focus may be on the logistics of this and making the office environment ‘Covid-Safe’ for their employees, they also need to be cognisant of the potential security challenges facing them. Some areas that businesses should start to focus on are: Currency of critical security patches Any relaxation of endpoint administrative rights Identification of unauthorised network scans The problem During the pandemic, most corporate assets (laptops) have in effect been residing on home office networks, those being home or public Wi-Fi, with only their EDR solution and VPN protecting them from attack. For the last 18 months or so, these assets have been sharing their local network with potentially un-patched devices, being operated by individuals who may have been more concerned with the latency of MineCraft and downloading the latest gaming ‘feature packs’ from non-salubrious websites, than good cybersecurity hygiene. Combine this with the necessity of some IT Depts having had to relax their Corporate Policy on Remote Patching (due to bandwidth limitations of VPN) and Administration Rights on local assets (in order to install ‘that home printer driver’), if not revisited and reverted, can leave a significant exposure. Early stakeholder buy-in This is essential, as without stakeholder support, any efforts to address these challenges will stall very quickly. The pandemic has put constraints on operating budgets for many businesses, so it is essential to be able to articulate these security challenges and ways in which to mitigate, clearly to stakeholders. Without this insight, it will be an uphill struggle to focus on these additional security requirements and obtain the budget to support them. Hopefully this article will provide the narrative to assist with that dialogue and highlight some of the concerns that pose a real threat to businesses. The human element Moving away from technology for a moment, and an area that is often overlooked by businesses, is how the employee has been managing their security hygiene, in the absence of localised IT support. In effect, they could have been making security decisions for over a year, as remote workforce. They have lacked the ability to prevent potential ‘odd behaviour on endpoints’ with peers. That ‘security pop-up’ message that they just clicked ‘yes’ to, or the attachment they opened, that appeared to ‘do nothing’, all of which can be the precursor activity of an attack. Threat actors have taken full advantage of this exposure, and there has been a marked increase in attacks focussed on Business Email Compromise (BEC) and phishing scams to name a few. A recent report by Gartner talks about how these threat actors have taken advantage of the changing working environments, both during and post pandemic, targeting the remote workforce with email and SMS campaigns pertaining to be from their local IT Support. Any breach in endpoint security of your remote workforce may be amplified exponentially once they return to the office and the threat actors are then able to get a foothold on the corporate network and start profiling internal architecture, in advance of for example, ransomware deployment. Businesses can start to address these risks as part of their return to office planning by taking a number of tactical steps. Controlled introduction Just like the way a business would rollout a new technology, it is always advisable to address any outstand | Ransomware Malware Vulnerability Threat Patching Guideline | |||
| 2021-07-07 10:00:00 | (Déjà vu) Cybersecurity and government (lien direct) |
 Photo by Katie Moum on Unsplash
In May, after many months of dedicated effort, our compliance team received word that a U.S. Federal Risk and Authorization Management Program (FedRAMP) moderate certification was granted for the AT&T Threat Detection and Response for Government solution. FedRAMP is a program coordinated by the US General Services Administration and the Department of Homeland Security (DHS) that inspects cloud-based solutions for compliance with 325 distinct security controls. AT&T Threat Detection and Response for Government is purpose-built in the AWS GovCloud (U.S.). and meets the FedRAMP requirements for cloud service providers operating at the Moderate Impact Level.
This was an important achievement as it allows our field sales teams to work better with government organizations, taking client conversations beyond a common issue: “Is your offer FedRAMP certified?” The ability to answer “yes” to the challenge means that the client does not have to research and produce the certification documentation themselves (an enormous task) to place TDR for Government into an approved production environment.
The inclusion of AT&T Threat Detection and Response on the Approved Products List (APL) maintained by DHS and GSA for Continuous Diagnostics and Mitigation (CDM) is further evidence of the solution’s ability to strengthen the cybersecurity posture of federal, state and local government networks and systems.
It is very satisfying to observe customers as they spin up an instance of our USM platform-based products for the first time. Within just a few minutes of the final configuration steps, the customer dashboard will start to come to life with counts of discovered devices, counts of events, and maybe even an alert that requires attention.
Our first AT&T Threat Detection and Response for Government customer was immediately relieved to learn that mandatory reporting of log management activities is automated for him with the solution. Rather than chasing down the details of log aggregation and log management for each distinct technology deployed in the environment, he can rely on the AT&T Threat Detection and Response for Government dashboards to provide him at-a-glance data. He can utilize our library of pre-prepared reports to fulfill monthly audit requirements for FISMA and NIST compliance. Relief from this mundane work is just one of the many benefits that he and the CISO quickly realized.
Also in May, President Biden issued an Executive Order encouraging all agencies of the Federal Government to improve the nation’s cybersecurity. Amongst the many
Photo by Katie Moum on Unsplash
In May, after many months of dedicated effort, our compliance team received word that a U.S. Federal Risk and Authorization Management Program (FedRAMP) moderate certification was granted for the AT&T Threat Detection and Response for Government solution. FedRAMP is a program coordinated by the US General Services Administration and the Department of Homeland Security (DHS) that inspects cloud-based solutions for compliance with 325 distinct security controls. AT&T Threat Detection and Response for Government is purpose-built in the AWS GovCloud (U.S.). and meets the FedRAMP requirements for cloud service providers operating at the Moderate Impact Level.
This was an important achievement as it allows our field sales teams to work better with government organizations, taking client conversations beyond a common issue: “Is your offer FedRAMP certified?” The ability to answer “yes” to the challenge means that the client does not have to research and produce the certification documentation themselves (an enormous task) to place TDR for Government into an approved production environment.
The inclusion of AT&T Threat Detection and Response on the Approved Products List (APL) maintained by DHS and GSA for Continuous Diagnostics and Mitigation (CDM) is further evidence of the solution’s ability to strengthen the cybersecurity posture of federal, state and local government networks and systems.
It is very satisfying to observe customers as they spin up an instance of our USM platform-based products for the first time. Within just a few minutes of the final configuration steps, the customer dashboard will start to come to life with counts of discovered devices, counts of events, and maybe even an alert that requires attention.
Our first AT&T Threat Detection and Response for Government customer was immediately relieved to learn that mandatory reporting of log management activities is automated for him with the solution. Rather than chasing down the details of log aggregation and log management for each distinct technology deployed in the environment, he can rely on the AT&T Threat Detection and Response for Government dashboards to provide him at-a-glance data. He can utilize our library of pre-prepared reports to fulfill monthly audit requirements for FISMA and NIST compliance. Relief from this mundane work is just one of the many benefits that he and the CISO quickly realized.
Also in May, President Biden issued an Executive Order encouraging all agencies of the Federal Government to improve the nation’s cybersecurity. Amongst the many |
Threat | ★★★★★ | ||
| 2021-07-07 10:00:00 | AT&T Threat Detection and Response for Government (lien direct) |
 Photo by Katie Moum on Unsplash
In May, after many months of dedicated effort, our compliance team received word that a U.S. Federal Risk and Authorization Management Program (FedRAMP) moderate certification was granted for the AT&T Threat Detection and Response for Government solution. FedRAMP is a program coordinated by the US General Services Administration and the Department of Homeland Defense that inspects cloud-based solutions for compliance with 325 distinct security controls. AT&T Threat Detection and Response for Government is purpose-built in the AWS GovCloud (U.S.). and meets the FedRAMP requirements for cloud service providers operating at the Moderate Impact Level.
This was an important achievement as it allows our field sales teams to work better with government organizations, taking client conversations beyond a common issue: “Is your offer FedRAMP certified?” The ability to answer “yes” to the challenge means that the client does not have to research and produce the certification documentation themselves (an enormous task) to place TDR for Government into an approved production environment.
The inclusion of AT&T Threat Detection and Response on the Approved Products List (APL) maintained by DHS and GSA for Continuous Diagnostics and Mitigation (CDM) is further evidence of the solution’s ability to strengthen the cybersecurity posture of federal, state and local government networks and systems.
It is very satisfying to observe customers as they spin up an instance of our USM platform-based products for the first time. Within just a few minutes of the final configuration steps, the customer dashboard will start to come to life with counts of discovered devices, counts of events, and maybe even an alert that requires attention.
Our first AT&T Threat Detection and Response for Government customer was immediately relieved to learn that mandatory reporting of log management activities is automated for him with the solution. Rather than chasing down the details of log aggregation and log management for each distinct technology deployed in the environment, he can rely on the AT&T Threat Detection and Response for Government dashboards to provide him at-a-glance data. He can utilize our library of pre-prepared reports to fulfill monthly audit requirements for FISMA and NIST compliance. Relief from this mundane work is just one of the many benefits that he and the CISO quickly realized.
Also in May, President Biden issued an Executive Order encouraging all agencies of the Federal Government to improve the nation’s cybersecurity. Amongst the many elements of the
Photo by Katie Moum on Unsplash
In May, after many months of dedicated effort, our compliance team received word that a U.S. Federal Risk and Authorization Management Program (FedRAMP) moderate certification was granted for the AT&T Threat Detection and Response for Government solution. FedRAMP is a program coordinated by the US General Services Administration and the Department of Homeland Defense that inspects cloud-based solutions for compliance with 325 distinct security controls. AT&T Threat Detection and Response for Government is purpose-built in the AWS GovCloud (U.S.). and meets the FedRAMP requirements for cloud service providers operating at the Moderate Impact Level.
This was an important achievement as it allows our field sales teams to work better with government organizations, taking client conversations beyond a common issue: “Is your offer FedRAMP certified?” The ability to answer “yes” to the challenge means that the client does not have to research and produce the certification documentation themselves (an enormous task) to place TDR for Government into an approved production environment.
The inclusion of AT&T Threat Detection and Response on the Approved Products List (APL) maintained by DHS and GSA for Continuous Diagnostics and Mitigation (CDM) is further evidence of the solution’s ability to strengthen the cybersecurity posture of federal, state and local government networks and systems.
It is very satisfying to observe customers as they spin up an instance of our USM platform-based products for the first time. Within just a few minutes of the final configuration steps, the customer dashboard will start to come to life with counts of discovered devices, counts of events, and maybe even an alert that requires attention.
Our first AT&T Threat Detection and Response for Government customer was immediately relieved to learn that mandatory reporting of log management activities is automated for him with the solution. Rather than chasing down the details of log aggregation and log management for each distinct technology deployed in the environment, he can rely on the AT&T Threat Detection and Response for Government dashboards to provide him at-a-glance data. He can utilize our library of pre-prepared reports to fulfill monthly audit requirements for FISMA and NIST compliance. Relief from this mundane work is just one of the many benefits that he and the CISO quickly realized.
Also in May, President Biden issued an Executive Order encouraging all agencies of the Federal Government to improve the nation’s cybersecurity. Amongst the many elements of the |
Threat | |||
| 2021-07-06 10:00:00 | Lazarus campaign TTPs and evolution (lien direct) |
Executive summary
AT&T Alien Labs™ has observed new activity that has been attributed to the Lazarus adversary group potentially targeting engineering job candidates and/or employees in classified engineering roles within the U.S. and Europe. This assessment is based on malicious documents believed to have been delivered by Lazarus during the last few months (spring 2021). However, historical analysis shows the lures used in this campaign to be in line with others used to target these groups.
The purpose of this blog is to share the new technical intelligence and provide detection options for defenders. Alien Labs will continue to report on any noteworthy changes.
Key Takeaways:
Lazarus has been identified targeting defense contractors with malicious documents.
There is a high emphasis on renaming system utilities (Certutil and Explorer) to obfuscate the adversary’s activities (T1036.003).
Background
Since 2009, the known tools and capabilities believed to have been used by the Lazarus Group include DDoS botnets, keyloggers, remote access tools (RATs), and drive wiper malware. The most publicly documented malware and tools used by the group actors include Destover, Duuzer, and Hangman.
Analysis
Several documents identified from May to June 2021 by Twitter users were identified as being linked to the Lazarus group. Documents observed in previous campaigns lured victims with job opportunities for Boeing and BAE systems. These new documents include:
Rheinmetall_job_requirements.doc: identified by ESET Research.
General_motors_cars.doc: identified by Twitter user @1nternaut.
Airbus_job_opportunity_confidential.doc: identified by 360CoreSec.
The documents attempted to impersonate new defense contractors and engineering companies like Airbus, General Motors (GM), and Rheinmetall. All of these documents contain macro malware, which has been developed and improved during the course of this campaign and from one target to another. The core techniques for the three malicious documents are the same, but the attackers attempted to reduce the potential detections and increase the faculties of the macros.
First iteration: Rheinmetall
The first two documents from early May 2021 were related to a German Engineering company focused on the defense and automotive industries, Rheinmetall. The second malicious document appears to include more elaborate content, which may have resulted in the documents going unnoticed by victims.
The Macro has base64 encoded files, which are extracted and decoded during execution. Some of the files are split inside the Macro and are not combined until the time of decoding. One of the most distinctive characteristics of this Macro is how it evades detections of a MZ header encoded in base64 (TVoA, TVpB, TVpQ, TVqA, TVqQ or TVro), by separating the first two characters from the rest of the content, as seen in Figure 1.
 Figure 1: Concealing of MZ header, as captured by Alien Labs.
The rest of the content is kept together in lines of 64 characters, and because of this, YARA rules can be used to detect other, typical executable content encoded in base64 aside of the MZ header. In this case, up to nine different YARA rules alerted to suspicious encoded strings in our Alien Labs analysis, like VirtualProtect, GetProcAddress, IsDe
Figure 1: Concealing of MZ header, as captured by Alien Labs.
The rest of the content is kept together in lines of 64 characters, and because of this, YARA rules can be used to detect other, typical executable content encoded in base64 aside of the MZ header. In this case, up to nine different YARA rules alerted to suspicious encoded strings in our Alien Labs analysis, like VirtualProtect, GetProcAddress, IsDe |
Malware Threat Guideline Medical | APT 38 APT 28 | ||
| 2021-07-06 10:00:00 | How to protect your site against lethal unauthorized code injections (lien direct) | This blog was written by an independent guest blogger. Lethal unauthorized code injections like XXS (cross site scripting) attacks are some of the most dynamic cyber-attacks. They are often very difficult to detect and can result in credit card theft, fraud, and endpoint data breaches, having a huge impact on small to medium sized businesses. In a recent AT&T cybersecurity survey, 88% of respondents reported that they had experienced at least one security incident within the past year. A CSP (content security policy) can be a great solution for defending sites from lethal code injections, especially when used in conjunction with additional layers of security to protect users' most sensitive data. The standardized set of directives that can be enforced by a CSP tells the browser what sources are trustworthy and which ones to block. This technique has the ability to eliminate many common injection vectors and also can significantly reduce XSS attacks. While CSPs are powerful against XSS and other client-side attacks, website admins should continue to follow security best practices and utilize tools that help to minimize JavaScript vulnerabilities. How CSPs help prevent malicious attacks When implemented as a part of your website standards, a CSP (or ISP - Information Security Policy - as it is sometimes called) tells the browser to enforce policies that restrict which scripts can be loaded on any given website. You can specify which domains are allowed to run scripts, which are blocked, and which ones get reported but can still be viewed. This not only helps you to narrow your vulnerability, but also can help you discover where malicious attacks are likely to come from in the future. When there are multiple CSPs specified, the browser will default to using the most restrictive directive in order to thwart a malicious attack. For example, to prevent cybercriminals from injecting embedded images with malicious code, an e-commerce site admin might want to limit the domains from which images are allowed to load from. A content security policy should be a mainstay for any web admin and IT team security protocol. Any other cyber protection that you use will be stabilized by the CSP and create a fortress to protect your website data. Layers of security Organizations both large and small should be concerned about hackers and data breaches, although the spotlight has been focused on advances in technology, giving a false sense of security. Instances of cybercrime were up again by 37% last year, costing businesses nearly $4.5 million. Cybersecurity strategies that can adapt to the changing techniques that cybercriminals employ to exploit businesses and their customers are more important than ever before as we continue to expand the internet of things and our connectivity capabilities. While a CSP provides a thick layer of protection, hackers only have to target a single allowed domain that you are not protected against in order to execute an attack that could possibly result in catastrophic data loss, loss of trust from your customers, and loss of revenue. In order to add another layer of security, website admins need an additional layer of JavaScript-based monitoring that is able to analyze script behavior at the granular level. Sensors that are created for JavaScript have the ability to collect all kinds of behavior signals from scripts that are running on the page while flagging anomalies that have the potential to be malicious code injection | ||||
| 2021-06-29 10:00:00 | Empowering women in the field of ethics and compliance (lien direct) | This blog was written by an independent guest blogger. Ethics and compliance is becoming a burgeoning industry as an increase in government regulations in areas such as sustainability, diversity, and data privacy make compliance an important focus for companies. It’s especially important in tech companies as the ever-growing risk of cybersecurity breaches requires that security teams be vigilant in protecting sensitive data. Any breach of regulations can result in legal headaches and customer distrust, making a solid compliance department a wise investment in any business. Ethics is another vital concern for companies who want to cultivate and maintain a positive public image. Corporations want their clients to see that they are doing the right thing, regardless of what the law dictates. As people increasingly look to their favorite brands to express support for social justice causes, ensuring that a company is on the right side of important public issues can be empowering as well as lucrative. In this growing industry, many women have made their mark, influencing global corporations and guiding them in their approaches towards ethics and compliance. Let’s dig into the increasing importance of ethics and compliance in tech and some opportunities for inclusion and gender equality in this growing field. Critical compliance With the host of laws and regulations in various industries, such as HIPAA in the healthcare industry or state-by-state privacy laws in tech, compliance can be a very complex and daunting field. It is crucial in any business, and particularly in tech, but sometimes the field does not get the recognition it deserves. What’s more, the tech industry has a well-known reputation for being dominated by men, and women techies often don’t get the recognition they deserve either. In the fintech industry for example, on average only 37% of the workforce is female, with a mere 19% holding C-Suite positions. In such male-dominated fields, it’s important to celebrate the accomplishments of women and focus on ways to get more women involved in the industry. Ethics and compliance is one area where we are seeing more women breaking into the industry. This field is booming as technology like artificial intelligence (AI) and the Internet of Things (IoT) make their way into almost every aspect of our personal and professional lives. For example, the rapidly growing popularity of IoT devices can result in tech companies rushing production of new technology, sometimes at the expense of adequate cybersecurity. It was formerly common for vulnerabilities to remain undiscovered until their use was widespread, leaving users and companies exposed to cyber threats. Companies sometimes downplayed these issues to avoid affecting sales, and the ethics and compliance field is trying to turn this around. This issue led to the passing of the IoT Cybersecurity Improvement Act of 2020, which established rules regarding the cybersecurity of the software used by the American government. While the regulations only affected companies with contracts with the federal government, their purchasing power was large enough that it became a governing standard for the tech industry. Such regulations are particularly important in industries that handle financial data like the payment card industry. But even with regulations such as | Guideline | |||
| 2021-06-28 10:00:00 | Asset management in the age of digital transformation (lien direct) | Over the past year or so, organizations have rapidly accelerated their digital transformation by employing technologies like cloud and containers to support the shift to IoT and address the expanding remote workforce. Visibility Matters: This digital shift calls for a new approach to asset visibility as traditional asset administration responsibilities like inventory, software support, and license oversight are often the purview of IT and addressed with IT inventory-focused tools. Along the way, many organizations have lost control over their IT asset inventory as they rush to adopt new transformation technologies that have blurred the boundaries of their traditional network perimeters. This lack of visibility into an IT environment undermines the foundations of enterprise security and compliance infrastructure and puts an organization at serious risk of a breach. What you don't know can hurt you! Fundamentally, security teams need to monitor IT asset health from a cybersecurity perspective to help detect security tool blind spots and responding to exposures quickly. It isn't easy to secure something in the world of cybersecurity if you don't know it exists. That's why cybersecurity asset management (or CSAM) is a critical component of the foundation of cybersecurity operations across businesses of all types. By providing a security team a real-time directory of IT assets and their associated security risks, CSAM is one of the building blocks of a proactive, end-to-end security strategy. Asset inventory challenges: Overall, the process of getting asset inventory can be cumbersome and time-consuming for an organization, but a few immediate challenges are: Collecting data from multiple sources, especially in a large, distributed environment. Over the past year, organizations have rapidly accelerated their digital transformation by utilizing technologies such as cloud and container that support the shift to IoT and a remote workforce. Many organizations have lost control over their IT asset inventory as they rush to adopt these new strategies that have blurred the boundaries of their network perimeters. Testing/validating compliance More and more compliance / best practices frameworks are moving towards a risk-based or maturity-focused goal. This requires organizations to know where they stand concerning control objectives, not "at some point in time" but rather "at any point in time." Without a comprehensive and almost real-time inventory of all assets within an organization, it is nearly impossible to validate compliance in a programmatic fashion. Implementing cyber asset inventory management To maintain a complete, detailed, and continuously updated inventory of all your IT assets, wherever they reside (on-premises, in cloud instances, or mobile endpoints), you need an automated, cloud-based system that gives you the following capabilities It needs to provide complete visibility of your IT environment – all IT assets include hardware and software It needs to perform continuous and automatic updates of the IT and security data It needs to be rapidly scalable without the need for additional hardware It needs to help highlight and rank the criticality of assets It needs interactive and customizable reporting features so you can slice/dice the data as required and ensure the reporting is consumable across multiple audiences. Cybersecurity is a team sport. Having the ability to identify tooling that can consolidate workloads and meet cross-organizational functional requirements can be a massive win for the organization. Asset management crucial to Zero T | Tool | |||
| 2021-06-24 10:00:00 | A mid-year update for Cybersecurity – 4 trends to watch (lien direct) | This blog was written by an independent guest blogger. It is nearing the mid-year point of 2021, and already it can be characterized as” the year of the breach.” Many companies and institutions saw their security perimeters pierced by hackers including the mega-breaches of Solar Winds and the Colonial Pipeline. The scale of penetration and exfiltration of data by hackers and the implications are emblematic of the urgency for stronger cybersecurity. Although there are a variety of trends emerging in the first six months, below are four that stand out as barometers of what lies ahead. 1. Ransomware attacks are taking center stage as Cyber-threats There is ample evidence that ransomware has become a preferred method of cyber-attack choice by hackers in 2021. As of May 2021, there has been a 102% surge in ransomware attacks compared to the beginning of 2020, according to a report from Check Point Research. Hackers have found ransomware ideal for exploiting the COVID-19 expanded digital landscape. The transformation of so many companies operating is a digital mode has created many more targets for extortion. One office with 4,000 employees has become 4,000 offices. In addition to an expanding attack surface, hackers are more active than before because they can get paid easier for their extortion via cryptocurrencies that are more difficult for law enforcement to trace. Criminal hacker groups are becoming more sophisticated in their phishing exploits by using machine learning tools. They are also more coordinated among each other sharing on the dark web and dark web forums. In 2020, according to the cybersecurity firm Emsisoft, ransomware gangs attached more than 100 federal, state, and municipal agencies, upwards of 500 health care centers, 1,680 educational institutions and untold thousands of businesses. As a result of the Colonial Pipeline Ransomware attack and others, the U.S. Department of Justice and the FBI have prioritized investigating and prosecuting hackers who deploy ransomware. The impact for the rest of 2021 will be more ransomware attacks against institutions and corporations who are less cyber secure, especially to targets that cannot afford to have operations impeded such as health care, state & local governments, educational institutions, and small and medium sized businesses. See: The New Ransomware Threat: Triple Extortion - Check Point Software Why Ransomware is So Dangerous and Difficult to Prevent | Manufacturing.net 2. Cyber-attacks are a real threat to commerce and economic prosperity So far this year, cyber-attacks have grown in number and sophistication, repeating a trend of the last several years. The recent cycle of major industry and governmental cyber breaches is emblematic of growing risk. The attacks are also becoming more lethal and costly to industry. A new NIST report was released on the economic impact to the U.S. economy by breaches, and it is alarming. The report suggests that the U.S. Loses hundreds of billions to cybercrime, possibly as much as 1 % to 4 % of GDP annually. The beach stats are part of a bigger global trend. The firm Cybersecurity Ventures predicts that global cybercrime damages will reach $6 trillion annually by this end of this year. The firm’s damage cost estimation is based on historical cybercrime figures including recent year-over-year growth, a dramatic increase in hostile nation-state sponsored and organized crime gang hacking activities, and a cyberattack surface. In both the public and private sectors, there is a | Ransomware Malware Tool Threat | |||
| 2021-06-23 10:00:00 | (Déjà vu) Stories from the SOC - Office 365 account compromise and credential abuse (lien direct) |
Stories from the SOC is a blog series that describes recent real-world security incident investigations conducted and reported by the AT&T SOC analyst team for AT&T Managed Threat Detection and Response customers.
Executive Summary
Credential abuse and compromised user accounts are serious concerns for any organization. Credential abuse is often used to access other critical assets within an organization, subsidiaries, or another partner corporation. Once an account is compromised, it can be used for data exfiltration, or to further promote the agenda of a threat actor. Threat actors often compromise the internal email accounts of legitimate organizations for many reasons including to send internal users phishing links leading to additional compromise, to send malicious emails to external users for later compromise, or create inbox rules to forward confidential emails to the threat actor’s account outside of the organization. Monitoring for events surrounding internal, inbound, and outbound email activity is important.
The AT&T Managed Threat Detection and Response (MTDR) analyst team received several alarms in response to a user attempting to send an excessive number of emails, resulting in these emails being blocked within Microsoft Office 365. Upon reviewing the user's login behavior, it was observed that this user was seen logged in from foreign IPs which were outside of the user's typical logon behavior. Further analysis of events surrounding the user concluded that this incident was contained. An investigation was created with attached events, artifacts, and login activity to quickly engage the customer and remediate the compromise before the attack could be elevated.
Investigation
Initial Alarm Review
Indicators of Compromise (IOC)
There were three alarms generated from events involving Credential Abuse, Anomalous User Behavior, and Security Policy Violation from Office 365 activity from both a foreign country and the United States.
 Credential abuse
Expanded Investigation
Events Search
The initial Credential Abuse alarm (image 1) for suspicious login activity was generated in response to 12 events related to successful logins from a foreign country and the United States within a 24 hour period. After expanding the events surrounding this user, it was discovered that this user has never logged in from countries outside the United States.
The team then used Open Source Intelligence (OSINT) tools to research the foreign IPs and discovered that these were IP addresses belonging to a foreign telecommunications company and were previously blacklisted. Utilizing OSINT during an investigation is imperative to determine ownership, location, history of abuse, and malicious activity surrounding an IP address or domain.
Credential abuse
Expanded Investigation
Events Search
The initial Credential Abuse alarm (image 1) for suspicious login activity was generated in response to 12 events related to successful logins from a foreign country and the United States within a 24 hour period. After expanding the events surrounding this user, it was discovered that this user has never logged in from countries outside the United States.
The team then used Open Source Intelligence (OSINT) tools to research the foreign IPs and discovered that these were IP addresses belonging to a foreign telecommunications company and were previously blacklisted. Utilizing OSINT during an investigation is imperative to determine ownership, location, history of abuse, and malicious activity surrounding an IP address or domain.
 IP Blacklist check
The Anomalous User Behavior alarm (image 3) pertaining to Outlook 365 email activity was generated due to the excessive number of outbound emails. According to logs, there were fifty-three outbound emails sent from the foreign IP in 24 hours, which is a 1000% increase for this user. Due to the suspicious activity that was occurring, the Intrusion Prevention System (IPS) restricted the user's ability to send emails and generated an additional alarm for review. The implementation of an IPS is important in this instance, because it prevented data exfiltration from the compromised email account.
IP Blacklist check
The Anomalous User Behavior alarm (image 3) pertaining to Outlook 365 email activity was generated due to the excessive number of outbound emails. According to logs, there were fifty-three outbound emails sent from the foreign IP in 24 hours, which is a 1000% increase for this user. Due to the suspicious activity that was occurring, the Intrusion Prevention System (IPS) restricted the user's ability to send emails and generated an additional alarm for review. The implementation of an IPS is important in this instance, because it prevented data exfiltration from the compromised email account.
|
Threat Guideline | |||
| 2021-06-23 10:00:00 | Stories from the SOC - Office 365 Account Compromise and Credential Abuse (lien direct) |
Stories from the SOC is a blog series that describes recent real-world security incident investigations conducted and reported by the AT&T SOC analyst team for AT&T Managed Threat Detection and Response customers.
Executive Summary
Credential abuse and compromised user accounts are serious concerns for any organization. Credential abuse is often used to access other critical assets within an organization, subsidiaries, or another partner corporation. Once an account is compromised, it can be used for data exfiltration, or to further promote the agenda of a threat actor. Threat actors often compromise the internal email accounts of legitimate organizations for many reasons including to send internal users phishing links leading to additional compromise, to send malicious emails to external users for later compromise, or create inbox rules to forward confidential emails to the threat actor’s account outside of the organization. Monitoring for events surrounding internal, inbound, and outbound email activity is important.
The AT&T Managed Threat Detection and Response (MTDR) analyst team received several alarms in response to a user attempting to send an excessive number of emails, resulting in these emails being blocked within Microsoft Office 365. Upon reviewing the user's login behavior, it was observed that this user was seen logged in from foreign IPs which were outside of the user's typical logon behavior. Further analysis of events surrounding the user concluded that this incident was contained. An investigation was created with attached events, artifacts, and login activity to quickly engage the customer and remediate the compromise before the attack could be elevated.
Investigation
Initial Alarm Review
Indicators of Compromise (IOC)
There were three alarms generated from events involving Credential Abuse, Anomalous User Behavior, and Security Policy Violation from Office 365 activity from both a foreign country and the United States.
 Credential abuse
Expanded Investigation
Events Search
The initial Credential Abuse alarm (image 1) for suspicious login activity was generated in response to 12 events related to successful logins from a foreign country and the United States within a 24 hour period. After expanding the events surrounding this user, it was discovered that this user has never logged in from countries outside the United States.
The team then used Open Source Intelligence (OSINT) tools to research the foreign IPs and discovered that these were IP addresses belonging to a foreign telecommunications company and were previously blacklisted. Utilizing OSINT during an investigation is imperative to determine ownership, location, history of abuse, and malicious activity surrounding an IP address or domain.
Credential abuse
Expanded Investigation
Events Search
The initial Credential Abuse alarm (image 1) for suspicious login activity was generated in response to 12 events related to successful logins from a foreign country and the United States within a 24 hour period. After expanding the events surrounding this user, it was discovered that this user has never logged in from countries outside the United States.
The team then used Open Source Intelligence (OSINT) tools to research the foreign IPs and discovered that these were IP addresses belonging to a foreign telecommunications company and were previously blacklisted. Utilizing OSINT during an investigation is imperative to determine ownership, location, history of abuse, and malicious activity surrounding an IP address or domain.
 IP Blacklist check
The Anomalous User Behavior alarm (image 3) pertaining to Outlook 365 email activity was generated due to the excessive number of outbound emails. According to logs, there were fifty-three outbound emails sent from the foreign IP in 24 hours, which is a 1000% increase for this user. Due to the suspicious activity that was occurring, the Intrusion Prevention System (IPS) restricted the user's ability to send emails and generated an additional alarm for review. The implementation of an IPS is important in this instance, because it prevented data exfiltration from the compromised email account.
IP Blacklist check
The Anomalous User Behavior alarm (image 3) pertaining to Outlook 365 email activity was generated due to the excessive number of outbound emails. According to logs, there were fifty-three outbound emails sent from the foreign IP in 24 hours, which is a 1000% increase for this user. Due to the suspicious activity that was occurring, the Intrusion Prevention System (IPS) restricted the user's ability to send emails and generated an additional alarm for review. The implementation of an IPS is important in this instance, because it prevented data exfiltration from the compromised email account.
|
Threat Guideline | |||
| 2021-06-21 10:00:00 | How data poisoning is used to trick fraud detection algorithms on ecommerce sites (lien direct) | This blog was written by an independent guest blogger. Artificial intelligence (AI) and machine learning (ML) systems have become the norm for using client data to provide recommendations to customers. As more people are working from home and conducting business online, it is imperative that fraud detection software is used to protect user information. But these protective systems also utilize ML to automate the process and understand when a potential attack is taking place. Unfortunately, all systems that utilize ML could be subjected to a data poisoning attack. Most of the time, a data poisoning attack will end up having a greater effect on online businesses and ecommerce sites because companies are commonly unaware of the malicious software’s existence in the first place. This means it is important for all users to be aware of what data poisoning is and how to protect personal data from attacks that may be difficult to detect. What is data poisoning? ML algorithms rely on data to teach them what to look for and how to respond in different situations. The algorithm “learns” based on past information and then generates future decisions accordingly. Online businesses have become increasingly reliant on data generated in this manner for their marketing and customer outreach, to the point that a majority of online business owners have cited data collection and utilization as their single most important priority. Data privacy protection is absolutely essential for online businesses using customer information for their analytics and algorithms. One of the biggest threats to customer data privacy, however, is data poisoning. Data poisoning is a type of cyber-attack that causes an algorithm to produce improper results for the data that it reads. In essence, these attacks change the way that algorithms read and react to data inputs, tricking them into generating incorrect results. This can cause business operations to become slow or unproductive, but it can also cause significant financial repercussions to a company as well. For one thing, it could cause a consumer data breach, reducing trust in the company from existing customers. But it could also result in a big price tag. The cost for retraining an algorithm is very high, so even if the attack is detected, it could ruin a business trying to fix the issue. For these reasons, it is critical that businesses learn how to prevent data poisoning attacks. Fraud protection Making decisions concerning your technology can be stressful, but making the right cybersecurity choices is key to protecting yourself from fraud. Ecommerce companies use many vendors and products to collect, process, and analyze user data, and each of those vendors could have different privacy terms. If these outside companies are using AI to provide their services (which they most likely are), you need to be cognizant of their efforts towards data privacy in ML in addition to your own. When a user agrees to work with an online company, they may also be agreeing to share their data with the other businesses that support that company. If a data poisoning attack takes place in one of those, the attack could potentially go undetected and data could easily be used for malicious purposes. Humans lean towards creating communities a | ||||
| 2021-06-18 10:00:00 | Risk-based security now more important than ever for Energy and Utilities! (lien direct) | This is the third of three blogs in a series to help the energy and utility industries. You can read the first blog on Ransomware and Energy and Utilities and the second blog on Threat Intelligence and Energy and Utilities as well. Convergence of IT/OT is now a reality: Whether intentional or accidental, IT and operational technology (OT) are converging to support business outcomes of reducing costs and taking advantage of efficiencies. IT assets are being used in OT environments and with the transformation of Industry 4.0 for utilizing IoT. Given the convergence and increased attack surface, NSA has issued guidance around stopping malicious cyber activity against OT. CSA_STOP-MCA-AGAINST-OT_UOO13672321.PDF (defense.gov) Security First mindset There is a need for a mindset shift in protecting OT assets given the ineffective traditional approaches and priorities regarding how IT assets are protected. Legacy infrastructure has been in place for decades and is now being combined as part of the convergence of IT and OT. This can be challenging for organizations that previously used separate security tools for each environment and now require holistic asset visibility to prevent blind spots. Today's cybercriminals can attack from all sides, and attacks are laterally creeping across IT to OT and vice versa. Beyond technology, focus on risk and resilience It can be all too easy to deploy security technology and think you've mitigated risk to your business. Still, sadly technology investment is no guarantee of protection against the latest threats. It is critical to take a risk-based approach to security. This means that to decrease enterprise risk, leaders must identify and focus on specific elements of cyber risk to target. More specifically, the many components of cyber risk must be understood and prioritized for enterprise cybersecurity efforts. Organizations are increasingly aiming to shift from cybersecurity to cyber resilience. This means they must understand the threats they face, measure the potential financial impact of cyber exposures, compare this against the company's risk appetite level, and proactively manage cyber risks by having clear action plans based on their capabilities and capacities to protect against cybercrime. Focus on a risk-based approach The risk-based approach does two critical things at once. First, it designates risk reduction as the primary goal. This enables the organization to prioritize investment, including in implementation-related problem solving based squarely on a cyber program's effectiveness at reducing risk. Second, the program distills top management's risk-reduction targets into specific, pragmatic implementation programs with precise alignment from senior executives to the front line. Following the risk-based approach, a company will no longer "build the control everywhere"; rather, the focus will be on building the appropriate controls for the worst vulnerabilities to defeat the most significant threats that target the business' most critical areas. The risk-based approach to cybersecurity is thus ultimately interactive and a dynamic tool to support strategic decision-making. Focused on business value, utilizing a common language among the interested parties, and directly linking enterprise risks to controls, the approach helps translate executive decisions about risk reduction into control implemen | Ransomware Tool Threat Guideline | |||
| 2021-06-16 10:00:00 | How Zero Trust architecture improves the organization\'s network security (lien direct) | This blog was written by an independent guest blogger. In the cybersecurity field, Zero Trust is becoming a widely used model. Data breaches taught organizations to stay cautious regarding security, especially when it comes to information protection - and a Zero Trust model may be the best option. Nobody, including clients inside the firewall, should be trusted, per Zero Trust. Internal threats are a huge concern. And for many attackers, penetrating the barrier is a simple operation, thanks to easy access to leaked credentials. Information is the heart of Zero Trust; when security controls fail, organizations with insight into their information and the surrounding activities can spot unusual behavior. Zero Trust is a security paradigm. Organizations mandate users to be authentic and validated with the appropriate privacy configuration before accessing apps and information. Zero Trust presupposes there is no traditional network boundary. Networks can be regional, cloud-based, or a blend of both, with assets and employees located anywhere. Several corporate standards, like NIST800-207, characterize Zero Trust architecture as the best solution to managing security risks. Conventional network security follows the “believe yet validate” strategy. It’s replaced with the Zero Trust model. The traditional method implicitly trusts individuals and end devices inside the corporations’ fence, exposing the organization to dangerous inner attackers and rogue identities, granting illegitimate profiles access. With cloud migration of corporate transformational activities, this approach grew outdated. Zero Trust mandates enterprises to constantly analyze and verify that users and their devices have authorization. It requires the company to have insights into all services and be able to impose restrictions on access. Organizations must validate user requests thoroughly before granting access to either corporate or cloud resources. Therefore, Zero Trust relies on real-time insight into user credentials and features, like: the credentials’ and devices’ usual connections firmware versions user identity and type of credential operating system versions and patch levels applications installed on an endpoint Corporations should carefully evaluate the network architecture and access rights to prevent possible threats and minimize the impact of a breach. Separation of device type, authenticity, and group activities are examples of this. For example, unusual interfaces to the domain controller, such as RDP or RPC, must always be questioned or limited to certain privileges. Value of the Zero Trust model The internet of today is an unfriendly environment. Organizations’ information can be exposed to hackers to acquire, damage, or keep confidential information (Personally Identifiable Information (PII), Intellectual Property (IP), and Financial Information). It’s arguable that no network security is ideal and cyberattacks always exist, but Zero Trust decreases security risks and restricts the target area. Amongst the most efficient approaches for corporations to manage access to their network systems, services, and information is to use Zero Trust. To restrain intruders and restrict their rights in a data breach, it employs a variety of preventative approaches such as: | Ransomware Threat | |||
| 2021-06-15 13:30:00 | Palo Alto Networks teams with AT&T to deliver managed SASE (lien direct) | Remote workforces accessing applications and data that are located anywhere is the “new normal.” Across the globe, organizations of all sizes are struggling to modernize their infrastructures to accommodate this new reality while accelerating their digital transformation initiatives. As a result, today’s overly fragmented environments and markets make this transformation complicated, leaving many organizations unable to address the secure access needs of their customers or employees. Legacy networking and security architectures don’t cut it Traditionally, companies have deployed multiple products to address their secure remote workforce needs, such as web gateways, next-generation firewalls, secure virtual private networks, cloud access security broker (CASB) solutions, SD-WANs and more. These disparate products come with their own policy management and logging, creating a complexity that increases the administrative cost and can lead to gaps in the overall company’s security posture. With organizations demanding uninterrupted, secure access for their users, no matter where they are located, a new approach for networking and security is needed. This new approach is the secure access service edge (SASE). SASE converges software-defined wide area networking (SD-WAN) and security services— firewall as a service (FWaaS), secure web gateway (SWG), CASB, and Zero Trust Network Access (ZTNA) — into a single cloud-delivered service. SASE solves the challenge of delivering consistent, secure access no matter where users, applications or devices live. Because it is a single service, SASE dramatically reduces complexity and cost. However, the overhead and effort required to deploy a solution like SASE may be more than some organizations are able to undertake. This is where a strong service provider, with the right networking and security platform, can help by engaging with organizations and designing an approach aligned to their business requirements and needs. Palo Alto Networks teams with AT&T to deliver a managed SASE solution Palo Alto Networks and AT&T are collaborating together to deliver a comprehensive managed SASE offering, consisting of Palo Alto Networks’ Prisma Access cloud-delivered security with application-defined, autonomous and ML-powered Prisma SD-WAN. Prisma Access helps secure all users and applications with consolidated, best-in-class security capabilities (such as FWaaS, SWG, CASB, ZTNA and more) while Prisma SD-WAN enables the cloud-delivered branch with the industry’s first next-generation SD-WAN. AT&T SASE with Palo Alto Networks combines a global high-performance network with next-gen SD-WAN to simplify the delivery of consistent security at scale while ensuring optimal work from anywhere experience. The three main principles behind SASE: Application-defined, network-performance optimization and intelligent traffic steering at the network edge. Guaranteed security for all users directly accessing applications over the internet in public or private clouds. Consistent experience for all users across devices and locations grante | Threat Guideline | |||
| 2021-06-10 10:00:00 | Threat Intelligence and Energy and Utilities (lien direct) | This is the second in a blog series dedicated to the energy and utility industries. Read the first blog in the series here. Introduction It is increasingly common to hear about cyber threats to energy and utility industries. These are malicious acts by adversaries that target our data, intellectual property, or other digital assets. All too often it seems as though energy and utility companies are put in a defensive position to battle it out with these cyber intruders. How can the industry switch to a more offensive position when it comes to understanding these threats? Threat intelligence is a way to make sure your cybersecurity teams can minimize the impact of a threat against your assets. Let’s take a look at how threat intelligence can be an effective source of information for energy and utilities. What is threat intelligence? If you have an adversary threatening your system, it is a good idea to learn who they are, why they want to attack you, and where they are most likely to attack. You also want to know if they have ever been undetected on your network or in your applications, if they are currently there, or if it is likely they will try to breach your business. Threat intelligence is a way to collect that information and make informed and data-driven decisions on how to prepare for an attack, prevent an attack, and identify cyber threats. All of this helps to make your business more resilient so you can remain operational during and after a cyber incident, with a goal of every cyber incident not being catastrophic. Who uses threat intelligence? Cybersecurity is a business enabler. And, having insight into the psyche and rationale of those who want to inflict harm on your business is a good idea for a variety of stakeholders. Albeit, the technical details for each stakeholder will vary. Users of threat intelligence for energy and utility companies may include: SOC analysts IT analysts IT operations teams Incident response teams Development and quality assurance teams C-suites including CISO Boards of Directors Executives use threat intelligence to understand business risk, communicate with functional team leaders, and quickly deploy funding where appropriate to manage threats or bring on experts to assist. Practitioners use threat intelligence to help set priorities in managing threats, identify vulnerabilities, and act proactively. Threat intelligence data is useful and beneficial beyond the team of cybersecurity professionals. Effective use of threat intelligence helps to remove often deeply engrained silos in organizations. How can energy and utilities benefit from threat intelligence? Think of threat intelligence as the data that helps to inform the decisions in managing the risk an organization is willing to take. Organizations can create their own threat intelligence feeds or purchase a feed specific to their vertical market or geographic location. Automating threat intelligence helps reduce human error, increases fidelity through pattern matching, and delivers results more quickly. Using automated threat intelligence means the right stakeholders can receive relevant and actionable information more quickly. Overall, threat intelligence can help energy and utility organizations: Prevent catastrophic disruptions to services Reduce costs associated with the impact of a breach Reduce the risk of a cyber incident to steal data Increase collaboration and cross-functional work of the IT, development, security, and the rest of the organization With the increase in numbers and growing determination of cyber adversaries, energy and utility organizations need to be more resi | Threat Guideline | |||
| 2021-06-09 10:00:00 | Are fraudsters using automation to execute mass cyber-attacks? (lien direct) | This blog was written by an independent guest blogger. As our digital world turns toward advances in automated technology to increase efficiency and productivity, cybercriminals are also learning how to execute mass automated cyber-attacks. According to the 2021 AT&T Cybersecurity Insights Report, most people are concerned about the security of various applications and 52% believe that these threats challenge the integrity of networks. With the increase in remote work and more tasks taking place online, there are more opportunities than ever before to become a victim of a cyber scam. Digitisation is pushing forward at a rapid pace which means leaving outdated security measures behind. Using automated security protocols can greatly improve your chances of recovering from a malicious attack. Detecting attacks is becoming more tedious and it requires a more advanced understanding of how cyber criminals and fraudsters execute mass cyber-attacks. Learning how to protect yourself from this kind of attack and use automated technology to your advantage is critical for personal networks, small businesses and large enterprises as more scammers are beginning to use new tactics. Why basic security may leave you vulnerable Bare minimum security efforts are often not enough to protect against a cyber-attack. It is common to take a reactive approach to cybersecurity, but mistakes like this only leave the door wide open for a major attack. Many people also believe that smartphones and other devices are not as susceptible to being attacked, but the reality is quite the opposite. Protecting all of your devices and not just your computer or network can make you less vulnerable to an attack. Small businesses and large corporations are both susceptible to being victims of a cyber-attack. And with remote work becoming somewhat the norm, more people are using their devices that could potentially put proprietary data at risk. There are many ways that small businesses can prepare themselves for a potential attack, and that starts with actively enforcing cybersecurity practices. Things as seemingly unimportant as strong passwords can have a big impact on the strength of your security efforts. If your company still uses on-premise hardware and software to back up important files instead of using the cloud, then that customer data could be more vulnerable to major malicious attacks. And with the rise in ecommerce, more personal payment data is being stored by companies. If this kind of information gets into the wrong hands, then not only are customers affected, but the reputation of your business could be ruined. It is also imperative that companies test their security protocols. Many businesses lack a proactive approach to cybersecurity. One quick and efficient solution to get around this is to rely on Dynamic Application Security Testing, or DAST testing, which is designed to scan your applications for vulnerabilities while they are running. Detecting attacks Cybercriminals and fraudsters use automated attacks similar to how legitimate businesses use automation to increase productivity. In order to make the most money and scam the highest number of people, automated technology is used to send out mass attacks that cast a wide net across many demographics and types of internet users. Detecting malicious activity was much easier in the past when there were less devices connected to the internet and computing was still very much about manual input. Now, hackers and scammers are better at covering their tracks, and better at using automation for harmfu | ||||
| 2021-06-08 10:00:00 | Magic in Cybersecurity: Magic links to replace the password (lien direct) | This blog was written by an independent guest blogger. These days, magic links are in the air. They are becoming an intriguing means to strengthen digital security without inconveniencing users. This article discusses magic links, their magical function, and their potential benefits for a corporation. Magic links Magic links are authorized URLs that carry a token which grants accessibility to a particular user. They enable users to register or log in to a website, as well as make online transactions. When the user clicks on the URL, they get verified instantly. Magic links usually have a short life and are one-of-a-kind. Magic links form a digital authentication technique that can use both a passwordless and a multi-factor authentication system. Why use magic links In a digital world, magic links are useful in passwordless and multi-factor authentication. Passwordless authentication refers to a security system that doesn't use passwords. Users authenticate using a magic link, eliminating the need for passwords. They only require inputting an email address or contact number to get the URL to click. Multi-factor authentication (MFA) is a method of user authentication in various stages. Two or more authentication methods increase the steps the user must take. However, magic links provide the minimum complexity since users only need to click the URL to complete the procedure. How magic links work Magic links consist of three steps: On a sign-in page, the user inputs their email address. If the user has a registered email address, they will receive an email containing a magic link. To finish the sign-in cycle, the user selects and clicks the magic link. Conversely, at the time of registration, the user can also get a live link for authentication later on. This technique is comparable to a password reset process, in which a user receives a hidden link that enables them to update their password. Magic links function in the same way as password resets do, whereas the user doesn't need to type a password to navigate to their profile. Magic link security concerns One of several security issues users may face comes from the email provider. When email providers label magic link emails as spam, a significant email redirects to infrequently used spam folders. Users can require a link over a link without knowing they route to spam. The trick is to choose a reliable email provider with an IP address that traditional spam detection identifies as effective. Organizations can improve security of their magic links implementation. If an application delivers a magic link and the client seeks another, does the first link lapse? Users can become irritated if they have to click on several links to find the recent one. Magic links that expire leave the login process with minimal loopholes but give the user fewer options to sign in. Organizations need to consider this balance. Likewise, certain websites prevent users from utilizing magic links beyond the browser session in which the magic link was provided. When you close your window an | Spam | ★★★★ | ||
| 2021-06-07 10:00:00 | 7 Challenges in modern Cybersecurity and how to fix them (lien direct) | This blog was written by an independent guest blogger. Cybersecurity is a leading concern for any business today. While this trend has made IT security a secure and potentially lucrative field, modern cybersecurity professionals also face growing challenges. If you hope to keep your business safe amid rising threats, you’ll have to overcome these obstacles. In that spirit, here are seven of the top challenges in modern cybersecurity and how you can solve them. 1. Staffing shortages As more businesses become aware of the need for cybersecurity, demand has risen, but there aren’t enough workers to meet it. A recent survey revealed that 61% of cybersecurity teams are understaffed. If you haven’t already, you may soon encounter difficulty finding enough talent to handle your increasing workload. Specialty occupation visa programs may help you find talent internationally to help fill the gaps. Alternatively, you can turn to automation to artificially expand your workforce. By automating some tasks like network monitoring, you can accomplish more with fewer workers. 2. Skills gaps The same survey found that 50% of teams say their applicants are underqualified. The labor shortage, along with increasingly complex cyberattacks, has created a growing skills gap. Even when companies can find potential workers, they may not find anyone with appropriate experience or skills. You can fix this issue by cultivating talented workers instead of looking for them. Your seasoned employees can help train new hires, creating a skilled workforce out of less experienced candidates. Similarly, you can run internship programs that you then hire out of, creating a skilled worker pipeline. 3. Rising cybercrime One of the more obvious challenges of modern cybersecurity is that cybercrime is becoming a more severe issue. On average, security breaches cost businesses $3.86 million in 2020. Cyberattacks are becoming more frequent and damaging, and cybersecurity professionals must rise to the challenge. Companies need to make cybersecurity a priority in both budget and operations amid these rising threats. Cybersecurity professionals should also be more vigilant than ever, scrutinizing activity more closely and thoroughly. Zero-trust networks may be a necessity to manage the sheer volume of attacks some companies see. 4. Remote worker security Securing today’s increasingly distributed workforce can be a challenge. Many tools that remote workers rely on come with new vulnerabilities. For instance, Amazon Cloud Drive does not offer at-rest encryption, and Zoom has notorious security flaws. Managing people on different networks on potentially unsecured devices is rarely straightforward, too. Thankfully, there’s a growing number of remote monitoring platforms you can use to watch remote workers’ traffic. Stricter access controls like two-factor authentication can prevent criminals posing as remote workers from getting into a system. Segmenting your network can further secure remote access and mitigate the impact of a breach. 5. Growing attack surfaces As businesses adopt more connected technologies, network attack surfaces grow. Rising IoT adoption has made companies more agile and transparent, but they also create cybersecurity vulnerabilities. IT security professionals now have more entry points to manage, which can be challenging. One of the best ways to secure new potential entry points is network segmentation. Every device should only have access to the parts of the network it need | Guideline | |||
| 2021-06-04 10:00:00 | SentinelOne Advanced AlienApp (lien direct) |
Opening Statement
In today’s threat landscape there is no escape from having a 360° view to protect crucial organization assets. The criticality of the matter is greatly amplified in these times where working remotely has become vastly common among Enterprises and SMBs alike. An ideal security solution would combine threat detection & response on cloud resources as well as on the endpoint level, providing extensive, real-time and impactful coverage customers desperately need.
Users of all types should be extra careful as hackers’ attacks on company resources soar through the roof and they try to get access to sensitive information. A complete security solution should include a high-end Endpoint Detection and Response (EDR) with a Next Generation threat detection and response platform that will not let attacks fall through the cracks and will protect the company’s interests from intentional or unintentional user (internal or external) behavior.
USM Anywhere brings this story together in the form of a unique integration approach with a world-class, award-winning EDR solution – SentinelOne-tying together cloud and endpoint detection and response. AT&T is excited to introduce the advanced AlienApp for SentinelOne.
 The Advanced AlienApp for SentinelOne capitalizes the SentinelOne API first approach that helped us build one of the richest apps we’ve ever built. All a customer needs to do is configure their SentinelOne credentials within the app and USM Anywhere will take it from there.
The Advanced AlienApp for SentinelOne capitalizes the SentinelOne API first approach that helped us build one of the richest apps we’ve ever built. All a customer needs to do is configure their SentinelOne credentials within the app and USM Anywhere will take it from there.
 The Advanced AlienApp for SentinelOne provides customers with a comprehensive toolset for threat detection and response including:
Threat ingestion
Asset & Vulnerability Discovery
Rich Orchestration and Response engine
Reports & Dashboard
Auditing
Advanced Hunting Abilities and more…
In addition, utilizing the SentinelOne state-of-the-art rogue feature, customers can detect assets even if the SentinelOne agent isn’t deployed on those assets.
The Advanced AlienApp for SentinelOne provides customers with a comprehensive toolset for threat detection and response including:
Threat ingestion
Asset & Vulnerability Discovery
Rich Orchestration and Response engine
Reports & Dashboard
Auditing
Advanced Hunting Abilities and more…
In addition, utilizing the SentinelOne state-of-the-art rogue feature, customers can detect assets even if the SentinelOne agent isn’t deployed on those assets.
 USM Anywhere can pull the asset inventory from SentinelOne and compare it to the existing asset inventory within USM Anywhere based on a unique identifier to track the asset even if it changed IPs. This process updates existing assets with any new information from the agent and new assets will be added. The asset lifecycle is fully automatic.
USM Anywhere can pull the asset inventory from SentinelOne and compare it to the existing asset inventory within USM Anywhere based on a unique identifier to track the asset even if it changed IPs. This process updates existing assets with any new information from the agent and new assets will be added. The asset lifecycle is fully automatic.

 Having deep visibility on all company’s endpoints is monumental to the company’s safety. This can be a personal or company laptop or widely used as a company server regardless if it’s a physical or virtual. The ability to collect logs and correlate those among potentially millions of assets helps separate secured organizations from vulnerable ones. The Advanced AlienApp for SentinelOne can provide those security insights at a glance.
Having deep visibility on all company’s endpoints is monumental to the company’s safety. This can be a personal or company laptop or widely used as a company server regardless if it’s a physical or virtual. The ability to collect logs and correlate those among potentially millions of assets helps separate secured organizations from vulnerable ones. The Advanced AlienApp for SentinelOne can provide those security insights at a glance.
 Customers can get even more security insights as the app can also generate new SentinelOne reports or download existing ones with a click. Customers can generate different types of reports to be downloaded ad hoc or scheduled.
Customers can get even more security insights as the app can also generate new SentinelOne reports or download existing ones with a click. Customers can generate different types of reports to be downloaded ad hoc or scheduled. |
Vulnerability Threat | |||
| 2021-06-04 05:01:00 | Digital transformation explained (lien direct) |
This article was written by an independent guest author.
No matter what sector your organization does business in, you’ve probably heard the term digital transformation. In every industry, digital transformation is going to be critical to remain competitive and resilient.
But what does digital transformation mean? And how does cybersecurity fit in? Today’s organizations are facing an increasingly complex environment of securing everything attached to the network; applications, data, and endpoints.
What is digital transformation?
At its most basic definition, digital transformation (or DX) is the process of improving your business by leveraging the latest technologies and solutions.
Digital transformation harnesses third platform technologies - think cloud and data analytics, and acceleration technologies - think IoT and mobile apps to transform business operations.
The primary goals of digital transformation are to increase agility for customer responsiveness, flexibility to accommodate new ways of working, and scalability to help your business do more.
What’s driving digital transformation?
The main drivers of digital transformation are:
Skyrocketing data transmission speeds
Increased storage capacities
Expansion of mobile functionality
All these signs point to a rapid decrease of on-premises computing and storage.
With the cloud, the amount of time and resources spent on hardware maintenance and upkeep is drastically reduced because you no longer need to own, maintain, and upgrade these resources in your own data center.
Rebuffing the maintenance mindset, the preference for most IT departments is to spend more on innovation vs. the traditional “keep the lights on” tasks. However, because “turning the lights off” isn’t feasible, the bulk of IT budgets continue to be allocated to maintenance. A 2020 Deloitte Inisights report underscores the reality: the average IT department allocates over half its budget on maintenance but only 19 percent on innovation.
And according to a 2021 State of IT Spiceworks Ziff Davis study, updating outdated IT infrastructure is the number one factor driving IT budget increases — cited by 56% of organizations planning on growing IT spend.
Also driving cloud adoption is the need to address disaster recovery (DR). While DR has not been typically cost-effective for small to mid-sized businesses, many cloud vendors and providers offer DR solutions like DRaaS (Disaster Recovery as a Service) that address those challenges.
But perhaps the greatest driver of cloud adoption today is COVID-19. The pandemic’s disruption to the business landscape forced organizations to consider advanced technologies. The work from home or remote work model is here to stay, and the demand for software-as-a-service (SaaS) applications that allow teams to collaborate from anywhere is steadily increasing.
The main spheres of digital transformation
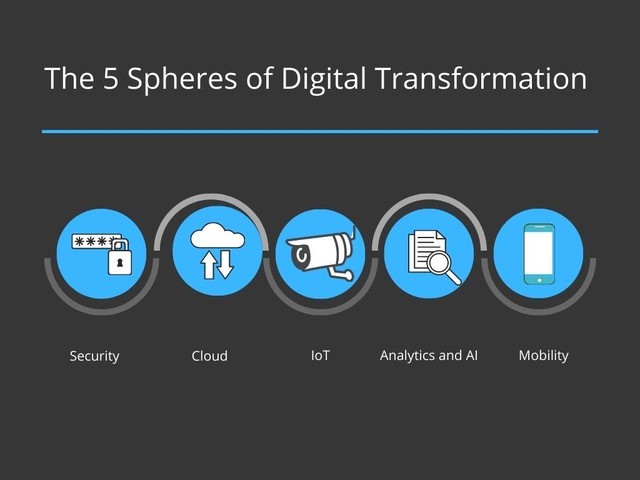 While one can argue that the components of digital transformation are numerous, we are highlighting five important spheres.
Security
As network access moves beyond the office perimeter to meet the demands of a remote workforce, robust security measures are required to maintain the confidentiality, integrity, and availability of corporate and customer data.
While one can argue that the components of digital transformation are numerous, we are highlighting five important spheres.
Security
As network access moves beyond the office perimeter to meet the demands of a remote workforce, robust security measures are required to maintain the confidentiality, integrity, and availability of corporate and customer data. |
Data Breach Threat | Deloitte | ||
| 2021-06-03 10:00:00 | (Déjà vu) Ransomware and Energy and Utilities (lien direct) | This is a blog series focused on providing energy and utility industries with helpful insights and practical, helpful information on cybersecurity. Intro The exponential growth of IoT devices in the energy and utilities industry has greatly increased focus on cybersecurity. Focus on cybersecurity across industries has increased recently, no doubt due to factors like COVID-19 forcing a jump in remote work. In 2020, we saw cybersecurity move from being a technical problem to a business issue. Along with the recognition that businesses really need to lead with a security-first mindset to be resilient, the CISO was elevated to a seat at the proverbial table as a true C-suite leader and trusted board advisor. Energy and utilities face unique challenges compared to other industries. According to McKinsey: “In our experience working with utility companies, we have observed three characteristics that make the sector especially vulnerable to contemporary cyberthreats. First is an increased number of threats and actors targeting utilities: nation-state actors seeking to cause security and economic dislocation, cybercriminals who understand the economic value represented by this sector, and hacktivists out to publicly register their opposition to utilities’ projects or broad agendas. The second vulnerability is utilities’ expansive and increasing attack surface, arising from their geographic and organizational complexity, including the decentralized nature of many organizations’ cybersecurity leadership. Finally the electric-power and gas sector’s unique interdependencies between physical and cyber infrastructure make companies vulnerable to exploitation, including billing fraud with wireless “smart meters,” the commandeering of operational-technology (OT) systems to stop multiple wind turbines, and even physical destruction.” Let’s look at one type of common and profitable attack that could impact energy and utility companies – ransomware. What is ransomware? Ransomware is exactly as the name implies – something valuable to your business is being kept from you until a ransom is paid for its return. In simple terms, ransomware is extortion. Ransomware, a form of malicious software, blocks you from accessing your computer systems or files until you pay the cyber adversary to allow you access to your information. The ransom is typically requested in crypto currency because of its anonymity and ease of online payment – this translates to no tracing of the origin or destination of the funds, a common tactic of cyber criminals. Knowingly infecting a system with ransomware and requesting payment to unlock the system is a crime. Law enforcement agencies recommend not paying the ransom associated with ransomware. The thought is that if the ransom is paid, you as the victim of ransomware are then identified as an easy target for further cybercrime and the ransomware attack is perpetuated against others. Who is the target of ransomware? Cyber criminals seek the path of least resistance in their targets and strike against businesses that are easy targets. Ransomware is a business and the perpetrators, like any good businessperson, are looking for a strong ROI. The C | Ransomware Malware Tool Vulnerability Guideline | Deloitte | ||
| 2021-06-03 10:00:00 | Ransomware and energy and utilities (lien direct) | This is a blog series focused on providing energy and utility industries with helpful insights and practical, helpful information on cybersecurity. Intro The exponential growth of IoT devices in the energy and utilities industry has greatly increased focus on cybersecurity. Focus on cybersecurity across industries has increased recently, no doubt due to factors like COVID-19 forcing a jump in remote work. In 2020, we saw cybersecurity move from being a technical problem to a business issue. Along with the recognition that businesses really need to lead with a security-first mindset to be resilient, the CISO was elevated to a seat at the proverbial table as a true C-suite leader and trusted board advisor. Energy and utilities face unique challenges compared to other industries. According to McKinsey: “In our experience working with utility companies, we have observed three characteristics that make the sector especially vulnerable to contemporary cyberthreats. First is an increased number of threats and actors targeting utilities: nation-state actors seeking to cause security and economic dislocation, cybercriminals who understand the economic value represented by this sector, and hacktivists out to publicly register their opposition to utilities’ projects or broad agendas. The second vulnerability is utilities’ expansive and increasing attack surface, arising from their geographic and organizational complexity, including the decentralized nature of many organizations’ cybersecurity leadership. Finally the electric-power and gas sector’s unique interdependencies between physical and cyber infrastructure make companies vulnerable to exploitation, including billing fraud with wireless “smart meters,” the commandeering of operational-technology (OT) systems to stop multiple wind turbines, and even physical destruction.” Let’s look at one type of common and profitable attack that could impact energy and utility companies – ransomware. What is ransomware? Ransomware is exactly as the name implies – something valuable to your business is being kept from you until a ransom is paid for its return. In simple terms, ransomware is extortion. Ransomware, a form of malicious software, blocks you from accessing your computer systems or files until you pay the cyber adversary to allow you access to your information. The ransom is typically requested in crypto currency because of its anonymity and ease of online payment – this translates to no tracing of the origin or destination of the funds, a common tactic of cyber criminals. Knowingly infecting a system with ransomware and requesting payment to unlock the system is a crime. Law enforcement agencies recommend not paying the ransom associated with ransomware. The thought is that if the ransom is paid, you as the victim of ransomware are then identified as an easy target for further cybercrime and the ransomware attack is perpetuated against others. Who is the target of ransomware? Cyber criminals seek the path of least resistance in their targets and strike against businesses that are easy targets. Ransomware is a business and the perpetrators, like any good businessperson, are looking for a strong ROI. The C | Ransomware Malware Tool Vulnerability Guideline | Deloitte | ||
| 2021-06-02 10:00:00 | Introducing AT&T USM Anywhere Advisors (lien direct) | As environments evolve and cybercriminals become more sophisticated, threat detection and response is becoming increasingly complex. While some organizations are turning to a fully managed detection and response solution, many others with established internal security teams are looking for additional support and expert guidance, while still keeping their program in-house. Our new service, AT&T USM Anywhere Advisors, is the middle-ground solution customers are looking for. USM Anywhere Advisors By combining USM Anywhere, our industry-leading threat detection and response solution, with AT&T USM Anywhere Advisors, companies gain centralized visibility into their entire environment and reactive security support from our expert AT&T Cybersecurity Consultants when additional assistance is needed. Basically, AT&T USM Anywhere Advisors serve as an extension of your in-house staff, providing reactive security support and helping with day-to-day operations while allowing your security team to learn industry best practices and the latest techniques for threat detection and incident response from our cybersecurity experts. The AT&T USM Anywhere Advisors’ reactive incident response services help to identify and triage potential security incidents within your environment. Based on their security expertise, the team evaluates your environment for signs of suspicious activity that have been missed by existing security controls and that could potentially impact confidentiality, integrity, and availability of your environment. When an incident occurs, the team is available to help investigate and deliver an analysis of findings and recommendations for remediation or further investigation. This solution allows you to maintain control of your environment, while gaining a comprehensive security platform for threat detection and response and support for your staff from a team of cybersecurity experts, without having to onboard multiple tools or new employees. With this service, we can help take some of the burden off your existing security team without the cost and complexity of bringing on additional staff. How does it work? AT&T USM Anywhere Advisors work with your internal team to help improve your security posture and help you get the most out of USM Anywhere. The reactive support is available for a pre-defined set of hours each month, ranging from 4-40 hours. When support is needed, your team can call or send an email to engage the team. The hours can be used to help with a range of security operation activities from platform tuning to incident investigation and response. Platform onboarding and tuning includes general tuning, sensor deployment, enabling asset discovery, AlienApp configuration, and more. During an investigation, the USM Anywhere Advisors will investigate your environment for indicators of compromise to determine if rogue users or malicious actors have gained a foothold in your environment. The team will begin each investigation by evaluating all actionable alarms and events in USM Anywhere and creating a specific hypothesis. If all of the required information is not available, they will work with your team to identify any additional systems, applications, and networks to include in the scope of the investigation. The team will utilize the Investigations feature in USM Anywhere to track all investigative activities, including initial detection and response, data collection, data analysis, and impact analysis and reporting. Gain a trusted advisor Our USM Anywhere Advisors team consists of highly trained AT&T Cybersecurity Consultants with over 90 industry-recognized security certifications among them. AT&T Cybersecurity Consulting has a heritage of delivering quality technology and business consulting to companies of all sizes and across industries. Based on their experience, these consultants deliver a vast catalog of services, including strategic planning, architecture and design, and integration and | Threat Guideline | Heritage Heritage | ||
| 2021-05-28 10:00:00 | Asymmetrical threats in Cybersecurity (lien direct) | Security and defense theory are inextricably entwined. Consider medieval castles. They were designed as a defensive mechanism that provided security to those within, most of whom were simply civilians hiding behind the walls for protection from invaders. Within cybersecurity, multiple concepts from defense and war theory can be applied to better address the cyber risks facing organizations. In fact, the term Bastion Host refers to a Bastion which has very militaristic connotations. In previous posts, the concepts of security cycle theory, attacker motivations, and threat adaptation have been explored. Another critical concept is that of asymmetric threats. The terms Asymmetrical Warfare or Asymmetrical Threats can be summarized simply as the asymmetry that exists between two adversaries and the tactics used by the weaker adversary to render the strengths of the stronger adversary moot. It is rare, though mathematically possible, to have parity between adversaries. Consider team sports, as an example. While not security nor defense related, there are indeed two adversaries playing a game against each other. Each side will have advantages and disadvantages. Within security and defense, it is a bit more profound. Consider the US Military for a moment. Since the end of World War II, which is often thought of as the start of US hegemony, the United States has arguably fielded the most powerful conventional military in the history of the world. Despite this fact, the US has struggled in conflicts in Vietnam, Somalia, and most recently in Iraq, and Afghanistan. In each of these theaters it was groups of lesser trained, less well-equipped insurgents that created significant challenges to the US military. The US is not alone in this dubious distinction of struggling against militarily weaker opponents. The powerful Prussian military was defeated by a much weaker opponent, France, under the command of Napoleon, and in 1989, the Soviet Union was defeated by the Afghanistan resistance movement after 10 years of bloody guerilla war. If Prussia and the USSR were militarily superior to their foes, how did they end up losing their respective wars? The losses were largely due to the application of what we now term asymmetrical warfare. In a basic sense Asymmetrical Warfare applies to the strategies and tactics employed by a militarily weaker opponent to gain advantage of vulnerabilities in the stronger opponent therefore rendering the advantages moot. As an example, few military forces on the planet would face the US military in open combat in a Mahanian naval battle or with the US in a linear, kinetic tank battle. As can be seen by the US routing of the Iraqis tank forces during the Battle of Medina Ridge in Desert Storm, doing so would lead to near certain defeat. If an inferior military opponent cannot fa | Ransomware Vulnerability Threat Patching Guideline | |||
| 2021-05-27 10:00:00 | Ways to setup Squid proxy server and helpful tips (lien direct) | This blog was written by an independent guest blogger. A squid proxy server has two major functions. First, it is an intermediary proxy. Second, it provides cache services for popular network protocols including HTTP and FTP. The use of proxies and cache services makes up a better internet user experience. Proxies provide added layers of security and cache services that make loading processes faster. Obviously, getting both services from a single provider is highly efficient. What is a Squid proxy server? Squid is a Unix-based proxy server that can do both caching and proxying. It can cache any web content to the user or requestor that is from a closer data storage point. It frequently caches large media files and web pages to reduce bandwidth congestion. Thus it decreases loading periods. Squid supports several caching protocols, such as hypertext caching protocols (HTCP), internet cache protocol (ICP), cache array routing protocol (CARP), and web cache communication protocol (WCCP). It also processes caching requests from Domain Name Server (DNS) lookups and Secure Sockets Layer (SSL). You wouldn’t want to miss enjoying the benefits of Squid proxy servers. Here are some ways to set the server up along with tips to maximize your use out of it. Ways to setup a Squid proxy server Squid proxy servers are usually installed in a separate server from the servers with the original content. The first thing to do is to update your server to install the squid proxy server. Check if the server is running by checking its status in the code, before starting to configure the system. Adding allowable sites In the configuration process, you sift through the sites that are allowable through the intermediary web proxy. These sites are considered as part of your ACL or access control list. These are the only sites that the Squid server will proxy and cache data for. Go through the list of acceptable websites and input in the code. Once all of these are encoded in, restart the proxy and check the status afterward. It’s safe to include an open port in the control list. The open port acts as the passageway for the other sites that were not defined and placed under the list. Blocking websites As much as you can configure the server to include sites to process, you can also block access to several websites. In order to carry out this requirement, create a folder under the access command list that will hold all the restricted sites. Limiting internet access is one of the prominent uses of proxy servers, in general. After listing the blocked or restricted sites, a prompt will appear in the code. Aside from blocked sites, you can also create a list of blocked keywords. Many companies configure their proxies to block access to several social networking sites, such as Facebook, Twitter, and Instagram. Once the list is finalized, make sure to save the file and restart the proxy to confirm. Configuring additional authentication To install an added layer of protection in your Squid proxy, install httpd-tools. This lets you create a password for the proxy. Make sure to assign the proxy server as the file owners. Otherwise, your access will be restricted as well. You can also add a pxuser using htpasswd utility. This calls for a different and much stronger password. Make sure not to forget this username and password. This will be used to authorize all proxy connections later on. Helpful tips to note First of all, every time you change or configure the components of the proxy server, make a copy of the original f | Guideline | |||
| 2021-05-26 10:00:00 | SASE as a Service: The role of managed services in the world of network security convergence (lien direct) | The next iteration in the history of technology convergence emerged with Gartner’s Secure Access Service Edge (SASE). Networking and security vendors have been integrating capabilities for decades, and market adoption of these integrations has only accelerated due to innovations such as virtualization and cloud computing. From a networking perspective, routing of traffic extends far beyond IP and MAC addresses to now include application steering and transport-agnostic overlay networks. From a security perspective, the next-generation firewall brought together a full stack solution capable of inspecting packets, URLs, and macro address information with unified threat management (UTM). SASE brings together these two areas in a manner which revolutionizes the way IT, network, and security organizations will manage their respective domains as well as interoperate cross-functionally. With revolution comes disruption to standard operating procedures; and, that disruption can bring confusion, complexity, and cost in the near term to achieve long-term savings and scalability. That said, transformation does not have to occur in a vacuum. Bringing in an expert, such as a managed services provider (MSP) to assist with the adoption and transition to SASE, can help achieve organizational success throughout the convergence of networking and security solutions. Historical precedent This makes sense when you think about the role MSPs have played throughout the internet era. Early networks were a foreign concept that some even considered a fad, and those disruptive enough to embrace them at the time were faced with complex management of costly systems. Dedicated teams were stood up to manage mainframes that became the first IT organizations. Eventually as these teams became more skilled, businesses emerged loaded with these experts with the acumen to help other organizations build out their own networks. By doing this, these early MSPs sped up the adoption of networking technologies by flattening the learning curve required to turn up a solution and scale their acumen to others as they completed builds for new companies. Noticeably absent (in hindsight) from these early networks was security, which was not even a consideration based on the initial framework of the ARPANET. Network security first started to take shape in 1988 after a student at Cornell University launched the first computer worm to access other connected devices. This resulted in the establishment of the Computer Emergency Response Team (CERT) at Carnegie Mellon University, the world’s first security operation center (SOC), to prevent these sorts of attacks from occurring in the future. As networking technologies evolved over time—along with the need to secure them—the MSPs managing legacy equipment adapted to these evolutions quickly, and helped organizations transform their infrastructures as well. In parallel, the role of the SOC expanded and network security technologies such as the firewall, intrusion detection system, and web application firewall emerged to help combat these threats. Managed security services providers (MSSPs) were spun up to manage these technologies as well as enable them to help protect other businesses. By taking on these evolving technologies, the onus for quickly understanding the evolution fell to network and security MSPs rather than on the organizations they served. The migration to SASE follows this precedent. Managed network and security providers have adept background in their respective domains and the ability to rapidly understand how technologies and architecture must evolve as the areas converge | Threat | |||
| 2021-05-25 10:00:00 | Cryptocurrency trading bots: Strengthening Cybersecurity and minimizing risks (lien direct) |
This blog was written by an independent guest blogger.
 A staggering $1.9 billion in cryptocurrency was stolen by criminals in 2020, a recent report by Finaria reveals. Fortunately, despite the growth of the crypto market, crypto crime has decreased by 57% since 2019, dropping to $1.9 billion. The widespread recent implementation of stronger security measures also means crypto-criminals stole 160% more in value in 2019 than in 2020, despite the similar number of crimes. Now, crypto trading bots have become popular in the cryptocurrency world: software that automatically trades on exchanges on your behalf. Strengthening cybersecurity when using trading bots is key to protecting your accounts and money from hackers.
API security
While trading bots could just use your PC interface to make trades, having access to an API (short for Application Program Interface) key means they can directly access specific trades, which allows them to act quicker. The API key is basically a password your trading bot needs access to in order to operate, use your account, and make cryptocurrency orders. Most exchanges will need you to make an API key, but the exact steps involved vary on each platform. Additionally, you’ll need to make a secret key, which you must keep secret: if someone gains access to your API key and secret key, they’ll be able to trade on your behalf. API keys also have different configuration options that you’ll need to select, such as trade permissions, view permissions, and withdrawal options. You can enhance security levels by always deleting API keys once you stop using a trading bot.
Make sure your trading bot is secure and reliable
It’s important to research different trading bots to make sure the one you use is reliable and secure. Using a bot with bad software or an inadequately-coded algorithm has the potential to cost you money. Additionally, your chosen service should function smoothly; if it goes offline or stops working, you’ll again lose money. Research various bots and read reviews to find out how reputable they are. For example, Coinrule is known to include robust security features to protect data. Every user is given a private key with bank-level encryption, which is stored on a server located in segregated data storage for tighter security. Also, be careful never to allow your trading bot to withdraw currency. If criminals get hold of your API keys, this means they’ll be able to take money out of your bank account. Ensuring your bot isn’t able to make withdrawals means criminals will be limited to only being able to make bad trades.
Use multi-factor authentication
Using two-factor authentication (or 2FA) is an essential step that gives you an extra layer of security to protect against any potential hackers and attacks. When logging into your exchange with your username and password, two-factor authentication will require you to also enter a One-Time Password (OTP). This One-Time-Password will be promptly sent to your smartphone so you can finish the login process. Your One-Time-Password will either be HMAC-based (HOTP) or Time-based (TOTP). A HOTP password is
A staggering $1.9 billion in cryptocurrency was stolen by criminals in 2020, a recent report by Finaria reveals. Fortunately, despite the growth of the crypto market, crypto crime has decreased by 57% since 2019, dropping to $1.9 billion. The widespread recent implementation of stronger security measures also means crypto-criminals stole 160% more in value in 2019 than in 2020, despite the similar number of crimes. Now, crypto trading bots have become popular in the cryptocurrency world: software that automatically trades on exchanges on your behalf. Strengthening cybersecurity when using trading bots is key to protecting your accounts and money from hackers.
API security
While trading bots could just use your PC interface to make trades, having access to an API (short for Application Program Interface) key means they can directly access specific trades, which allows them to act quicker. The API key is basically a password your trading bot needs access to in order to operate, use your account, and make cryptocurrency orders. Most exchanges will need you to make an API key, but the exact steps involved vary on each platform. Additionally, you’ll need to make a secret key, which you must keep secret: if someone gains access to your API key and secret key, they’ll be able to trade on your behalf. API keys also have different configuration options that you’ll need to select, such as trade permissions, view permissions, and withdrawal options. You can enhance security levels by always deleting API keys once you stop using a trading bot.
Make sure your trading bot is secure and reliable
It’s important to research different trading bots to make sure the one you use is reliable and secure. Using a bot with bad software or an inadequately-coded algorithm has the potential to cost you money. Additionally, your chosen service should function smoothly; if it goes offline or stops working, you’ll again lose money. Research various bots and read reviews to find out how reputable they are. For example, Coinrule is known to include robust security features to protect data. Every user is given a private key with bank-level encryption, which is stored on a server located in segregated data storage for tighter security. Also, be careful never to allow your trading bot to withdraw currency. If criminals get hold of your API keys, this means they’ll be able to take money out of your bank account. Ensuring your bot isn’t able to make withdrawals means criminals will be limited to only being able to make bad trades.
Use multi-factor authentication
Using two-factor authentication (or 2FA) is an essential step that gives you an extra layer of security to protect against any potential hackers and attacks. When logging into your exchange with your username and password, two-factor authentication will require you to also enter a One-Time Password (OTP). This One-Time-Password will be promptly sent to your smartphone so you can finish the login process. Your One-Time-Password will either be HMAC-based (HOTP) or Time-based (TOTP). A HOTP password is |
||||
| 2021-05-24 10:00:00 | AWS IAM security explained (lien direct) | Executive summary AWS Policies are a key foundation in good cloud security, but they are often overlooked. In this blog, we take a quick look on some AWS Policies, particularly for Identity and Access Management (IAM), that could become problematic if not properly managed. We'll discuss how they can be used against us to generate attacks like: Ransomware, data exfiltration, credential abuse, and more. Finally, we'll suggest some Open Source tools for cloud policy assessment and pentesting. Analysis The first step in achieving good security is having effective policies to regulate what can and cannot be done in an environment, both physical devices and cloud infrastructure. These regulatory policies are frequently hard to define and keep up-to-date, especially in a fast-paced environment using infrastructure-as-a-service (IaaS). This blog looks at some changes in policies which can reduce success in some common attack types involving: exfiltration, ransomware, credential abuse, and more. For that reason, AT&T Alien Labs is sharing an easy ‘what to look for’ list in order to detect some red flags in AWS policy changes. It is our hope that this list will be helpful for security analysts and forensic investigators. Policies are spoiler alert, defined by AWS Policies, which define permissions for identities and resources. Every time AWS Identity and Access Management makes a request of any kind to a resource, a policy determines if the IAM is allowed or denied access to that specific resource under the policies for the involved parties. A full understanding of AWS policies (types, creation, enforcement, etc.) is outside the scope of this blog, but it can be found in AWS documentation. People implementing AWS policies should have knowledge of the organization, adapting policies to needs of the business. Afterwards, detection rules should be generated for red flags in CloudTrail or other security tools. By doing this, we are avoiding policy changes in a generic manner, for example using ‘*’ to cover the whole Principal without setting any Conditions to it (MFA, IP, usernames, etc.). The problem resides in changes occurring on a daily basis to the policies, which are often overlooked by analysts. The impact that these changes could have is as big as any other event or alert investigated. In order to classify all AWS actions involving a policy change that could be used by attackers, we’ll sort them based on the potential final attack type. Most of the following techniques would fall under Modify Cloud Compute Infrastructure (T1578) but we have attempted to classify them outside of their specific Cloud technique - as if the activity was happening in a traditional environment. Denial of Service (DoS) Endpoint Denial of Service (T1499): Adversaries may perform Endpoint DoS attacks to degrade or block the availability of services to users. This blockage could be used as an additional impact on top of Data Encrypted for Impact (T1486) to avoid or slow down recovery efforts in a ransomware attack. In this scenario, attackers could be trying to block access to several AWS resources like: S3, EC2 through EFS or EBS, or backups between others. | Ransomware Tool Threat Guideline | |||
| 2021-05-20 10:00:00 | What is a trusted advisor? …and why do I need one? (lien direct) | Organizations today, even those not related to "tech", all have a need for cybersecurity. Regardless of your industry vertical, if you have email, a website, a phone system, or even just have people using computers, cybersecurity is needed at some level or another to protect your ability to do business. Strategy first What is your cybersecurity strategy? Every organization has unique needs, regulatory requirements, budgets, and priorities. Every organization needs to go through the process to understand each of these and create a roadmap for how they are going to protect themselves. There are many varieties of security products/technologies out there. Understanding what your organization needs is a daunting task. And just buying the technology doesn't suddenly make your organization protected. It needs to be implemented and maintained, it needs to integrate with other technologies and processes, and it needs to address your organization's needs without itself becoming an impediment to doing business. Do you outsource or do this in-house? Planning your next 2-3 years means you are making purchasing decisions and process changes that are aligned together to build a solid program and lowering the risk that your organization will be in the headlines for the wrong reasons. This is where using trusted advisors can help. What is a trusted advisor? Trusted advisors come in many different roles depending on your needs. They might be: An assessor that comes in and helps identify gaps (e.g. lack of consistent patching on servers) and helps you determine how to close them. Someone that helps you get your organization aligned to specific security frameworks or regulations (e.g. HIPAA/HITRUST, PCI, ISO 27002, NIST CSF) for compliance and the ability to win contracts from Fortune 500 companies. An individual that supports a CISO or Director of Security helping out as a sounding board to flesh out ideas and help identify costs and risks. They may even help you write the business case and draft the initial presentation you give to your board or manager to ensure adequate funding. Someone who acts as an educator and can help you prepare for an external audit, review and enhance training curriculum, and help people understand their roles, especially in organizations where people wear many hats (e.g., help define expectations) Unlike a technologist (someone who helps implement a technology, e.g., install and maintain a firewall), a trusted advisor works holistically to help align technologies and a cybersecurity program: That firewall needs to be updated; do you need a documented process? Should you send out an email to users that their login screen will look a little different? Is now a good time to change the architecture and move into the cloud? The value of trusted advisors is that they are people that have done it before and bring experience to the table. They have already seen the bumps and potholes and help you anticipate and navigate around them. They have worked with organizations of all sizes and have multiple tools in their toolkit to help innovate, administer and coordinate your security program to fit your organization. How do you choose a trusted advisor? These are features of a trusted advisor that you should consider: Ability to utilize other subject matter experts. No single individual will have an unlimited skillset. Your Trusted Advisor should have resources available to them to help provide deep knowledge. They should be working in your best interests. While vendors have fantastic advisors for sizing and implementing their product, there may be some concern that a recommendation is likely to benefit their organization more than yours. For an advisor to be trusted, you should feel confident that their recommendations are based solely on your needs. Ability to learn about and understand you | Patching | |||
| 2021-05-19 10:00:00 | Stalkerware: What is being done to protect victims as the number of cases rises (lien direct) | This blog was written by an independent guest blogger. People are increasingly becoming aware of the threats posed by hackers who infiltrate devices using viruses, spyware and malware. However, it may be time to shine the spotlight on “stalkerware”, a completely different type of cyber security threat that nevertheless has lasting negative repercussions. In this article, we will talk about this malicious software, which allows a remote user to surveil all activities on another user’s device. We’ll specifically focus on the implications of this particular type of cybercrime and how it ties in to domestic violence, stalking and harassment. We’ll also talk about how agencies are working together to end the use of stalkerware and how we can all be more informed and improve protection and detection of this type of malicious software. What is stalkerware? Recent studies by the Kaspersky Institute have revealed the United States, along with Russia and Brazil, are among the top countries affected by “stalkerware” last year. Especially of note is the corresponding increase in victims of spyware coinciding with coronavirus lockdowns and remote work, indicating that opportunists and cyber criminals are taking advantage of an increasingly technologically connected society. Having the ability to stay connected with friends and family through technology is a gift, but it also opens up a door for receiving unwanted attention. We live in a society where most people save their most precious moments, intimate interactions and heavily guarded secrets on their phones, tablets and laptops in the form of photos, text messages, notes and more. Because of this, we are seeing an increase in software that enables other users to spy on people through their digital devices. All of this surveillance occurs without the other person even realizing it is happening, making this software even more powerful. This is the reason why the cyber security industry has rapidly expanded over the past few years, as their importance in the lives of companies and individuals has grown. In computing, an application programming interface (API) is an interface that defines interactions between multiple software applications. “APIs tend to expose endpoints that handle object identifiers, creating a wide attack surface Level Access Control issue,” according to the security analysts at Cloud Defense. “Object level authorization checks should be considered in every function that accesses a data source using an input from the user.” Cyber criminals can use APIs to intercept events in targeted apps, thus surveilling the affected user. Unfortunately, “stalkerware” is available to anyone who has access to the internet and the intent to seek it out. The Coalition Against Stalkerware seeks to raise awareness about this new cyber security threat and the ways in which it poses serious concerns for those who fall victim to it. According to the Coalition, stalkerware is most commonly used in situations of domestic violence or stalking. How is stalkerware applied? Fortunately, there is some good news when it comes to stalkerware. Physical access to the device being monitored is required to install stalkerware on a vi | Threat Studies | |||
| 2021-05-18 10:00:00 | Stories from the SOC -SSH brute force authentication attempt tactic (lien direct) |
Stories from the SOC is a blog series that describes recent real-world security incident investigations conducted and reported by the AT&T SOC analyst team for AT&T Managed Threat Detection and Response customers.
Executive Summary
An SSH Brute Force attack is a form of cybersecurity attack in which an attacker uses trial and error to guess credentials to access a server. Unlike a lot of other tactics used by cybercriminals, brute force attacks aren’t reliant on existing vulnerabilities. Instead, cybercriminals rely on weak or guessable credentials. Brute Force attacks are fairly simple and have a high success rate, with several tools and programs available for attackers to use. Once an attacker correctly guesses valid credentials, they may be able to view, copy, or delete important files or execute malicious code.
The Managed Threat Detection and Response (MTDR) analyst team team received 96 alarms for Brute Force Authentication – SSH Login Failure. The team conducted further analysis and discovered 8,114 failed login attempts involving different usernames in one minute, indicating a legitimate brute force attack. The analysts worked back with customer’s team to block SSH access to the host and prevent any additional logons.
Investigation
Initial Alarm Review
Indicators of Compromise (IOC)
The alarms for this indicator of compromise are part of the weaponization stage, or second stage, of the cyber kill chain. Each individual alarm contained different usernames in each event from a single source IP address. All the alarms originated from different source IP addresses, targeting a public facing host on port 22.

 Expanded Investigation
Events Search
Searching for additional events was started by filtering all failed logon events to the effected host to validate no events were missed in the alarms. There were over 4,000 events when the research began and grew to over 8,000 in under a minute. Each “invalid user” error contained a different username.
Event Deep Dive
The attacker was using multiple IP addresses from different countries, indicating a botnet may have been utilized for this attack. The usernames used in the attack did not match any usernames associated with customer accounts, and there was no additional activity involving these usernames.
Reviewing for Additional Indicators
Any additional events during the time of the attack were reviewed to determine if any other indicators of compromise were detected. The SSH activity in the additional events followed the same pattern as the original alarms attempting to exploit port 22 on this public facing host. All SSH attempts were failed and the host was not compromised.
Response
Building the Investigation
As the alarms and events came into the queue, it was recognized it could be a potential dictionary attack. We reviewed the details of each alarm and events associated with that alarm and determined the usernames used did not match any of the known user accounts. There were no successful logins during this activity as all the usernames were not legitimate. A successful attack would compromise the bastion server and potentially provided access to the rest of the environment. While the alarms were incrementing in the queue, an investigation was created and a report outlining the events was provided to the customer. The event details were added to the Investigation and we provided a recommendation to the customer to review the firewall policy configuration.
Expanded Investigation
Events Search
Searching for additional events was started by filtering all failed logon events to the effected host to validate no events were missed in the alarms. There were over 4,000 events when the research began and grew to over 8,000 in under a minute. Each “invalid user” error contained a different username.
Event Deep Dive
The attacker was using multiple IP addresses from different countries, indicating a botnet may have been utilized for this attack. The usernames used in the attack did not match any usernames associated with customer accounts, and there was no additional activity involving these usernames.
Reviewing for Additional Indicators
Any additional events during the time of the attack were reviewed to determine if any other indicators of compromise were detected. The SSH activity in the additional events followed the same pattern as the original alarms attempting to exploit port 22 on this public facing host. All SSH attempts were failed and the host was not compromised.
Response
Building the Investigation
As the alarms and events came into the queue, it was recognized it could be a potential dictionary attack. We reviewed the details of each alarm and events associated with that alarm and determined the usernames used did not match any of the known user accounts. There were no successful logins during this activity as all the usernames were not legitimate. A successful attack would compromise the bastion server and potentially provided access to the rest of the environment. While the alarms were incrementing in the queue, an investigation was created and a report outlining the events was provided to the customer. The event details were added to the Investigation and we provided a recommendation to the customer to review the firewall policy configuration.
|
Threat | |||
| 2021-05-18 05:01:00 | What is data loss prevention? (lien direct) | This article was written by an independent guest author. DLP security strategies, benefits explained The threat landscape is a constantly evolving challenge for enterprise security professionals – the number of cyberattacks is continuing to rise, data exfiltration is now included in 70% of ransomware attacks, and insiders are responsible for 30% of all data breaches. As a result, enterprises are constantly looking for ways to reduce the risk of sensitive data being leaked outside the company. And with so many potential weak points, it’s necessary for organizations to put controls and solutions in place that not just monitor for inappropriate egress of corporate data, but also mitigate the risks as close to entirely as possible. To do this, the most common solutions enterprises turn to is Data Loss Prevention. What is data loss prevention? In its broadest terms, Data Loss Prevention (DLP) is a set of tools and processes that allow businesses to detect and prevent data breaches, exfiltration, and the malicious destruction or misuse of sensitive data. DLP solutions allow you to monitor and analyze data traffic on your network to spot potential anomalies, this includes inspecting data sent via email or instant messaging, analyzing data streams on your network, checking how data is being used on a managed endpoint, and monitoring data at rest in on-premises file servers or cloud applications and storage. DLP is typically used by organizations in the following scenarios: To protect Personally Identifiable Information (PII) and comply with regulatory requirements specific to the organization’s field of operation To protect Intellectual Property that is critical to the organization Help secure data on cloud systems Help secure an increasingly mobile and disparate workforce Enforce security in Bring Your Own Device (BYOD) environments If a potential violation is found, a DLP solution will trigger a remediation based on policies and rules defined by the organization, for example alerting IT, automatically enforcing encryption of data, or locking down a user to prevent sharing data that could put the organization at risk. DLP solutions will also produce reporting that can help the organization meet regulatory compliance. Explaining data protection complexities and requirements This sounds great in principle, however preventing the inappropriate leakage of sensitive data isn’t a simple process; data types must be established, data must be identified, rules must be defined based on role and data type, implementations must be tested to ensure a balance of security and productivity, and more. So, it’s necessary to ensure that your DLP efforts work to meet your data protection requirements, and that any prospective DLP solution can help you achieve this. SANS provides a rather comprehensive list of key requirements that you need to consider when starting your DLP journey. So, you need ensure any potential vendor includes these: Discovery, Retention, Searching – Analyze your networks for data At Rest (on endpoints, servers, and file shares), In Use, and In Motion (on the network, over email, and in web traffic, as well as any data being copied onto external devices). Monitoring – Discover, identify, correlate, analyze, and log every instance of sensitive data movement or use (removal, modification, or attempted transmission). Alerting – Define and implement actions that ne | Ransomware Threat | |||
| 2021-05-17 10:00:00 | Teaching kids internet safety tips for Zoom parties (lien direct) |
This blog was written by an independent guest blogger.
 Image Source: Pexels
The internet has changed over the years. Kids today are less interested in random chat rooms, and more inclined to connect with their friends via social media. Most recently, Zoom parties have become the norm for kids, especially due to the COVID-19 pandemic.
On paper, Zoom parties can be great ways for kids to stay connected. They can chat with their friends, and even meet people from different parts of the country – or the world! The big difference between Zoom parties and chatrooms of the past is that your child can see the people they’re talking to. While that might make things seem safer, there are still some precautions you, as a parent, should be taking.
Zoom isn’t necessarily 100% safe for kids who might not know the risks. Things like Zoombombing, where “trolls” and scammers hop onto meetings and parties to steal information or cause disruption, have become more prominent. Even cyberbullying or stalking can be a safety issue when your child is spending time on Zoom.
So, what can you do to keep your kid safe when they’re spending more time on Zoom parties and connecting with others?
What you need to know
The more you know about the potential risks of kids using Zoom, the easier it will be to keep your child safe. Educate yourself on the security features Zoom uses as well as any potential threats your child might face when they’re doing virtual learning or attending a “party” on Zoom.
Some of the biggest privacy concerns on the Zoom app include:
Spamming
Messages from random people
Content dropping (users linking pornographic images or other inappropriate content)
Attendee tracking
Vulnerability to hackers
You can certainly customize the privacy settings through Zoom, but unless you’re fully familiar with the app itself, it can be easy for your child to fall into certain traps. So, make sure you know the risks ahead of time and discuss some of them with your child before allowing them to get on the platform.
Walking your child through Zoom
Once you’re ready for your child to use Zoom, walk them through the features. Explain how things work and your expectations. If your child is old enough to use Zoom to connect with their friends, make sure to set up specific rules for them, including:
Not giving away personal information
Adjusting privacy settings as needed
Never joining a meeting with someone they don’t know
Never saying something they might regret later since meetings are often recorded
If you’re concerned about your child getting into a “random” Zoom party, why not help them set one up where they can connect with their friends? You can host the party and receive your own private link. In doing so, you’ll be able to monitor the guest list and ensure that “Zoombombers” don’t hop in and ruin the fun.
Throwing an online party can be a lot of fun when you’re willing to get creative. Feel free to set up a specific theme or plan games for your child and their friends. You’ll be able to foster their friendship and connection while ensuring they all have a safe environment to be themselves.
Image Source: Pexels
The internet has changed over the years. Kids today are less interested in random chat rooms, and more inclined to connect with their friends via social media. Most recently, Zoom parties have become the norm for kids, especially due to the COVID-19 pandemic.
On paper, Zoom parties can be great ways for kids to stay connected. They can chat with their friends, and even meet people from different parts of the country – or the world! The big difference between Zoom parties and chatrooms of the past is that your child can see the people they’re talking to. While that might make things seem safer, there are still some precautions you, as a parent, should be taking.
Zoom isn’t necessarily 100% safe for kids who might not know the risks. Things like Zoombombing, where “trolls” and scammers hop onto meetings and parties to steal information or cause disruption, have become more prominent. Even cyberbullying or stalking can be a safety issue when your child is spending time on Zoom.
So, what can you do to keep your kid safe when they’re spending more time on Zoom parties and connecting with others?
What you need to know
The more you know about the potential risks of kids using Zoom, the easier it will be to keep your child safe. Educate yourself on the security features Zoom uses as well as any potential threats your child might face when they’re doing virtual learning or attending a “party” on Zoom.
Some of the biggest privacy concerns on the Zoom app include:
Spamming
Messages from random people
Content dropping (users linking pornographic images or other inappropriate content)
Attendee tracking
Vulnerability to hackers
You can certainly customize the privacy settings through Zoom, but unless you’re fully familiar with the app itself, it can be easy for your child to fall into certain traps. So, make sure you know the risks ahead of time and discuss some of them with your child before allowing them to get on the platform.
Walking your child through Zoom
Once you’re ready for your child to use Zoom, walk them through the features. Explain how things work and your expectations. If your child is old enough to use Zoom to connect with their friends, make sure to set up specific rules for them, including:
Not giving away personal information
Adjusting privacy settings as needed
Never joining a meeting with someone they don’t know
Never saying something they might regret later since meetings are often recorded
If you’re concerned about your child getting into a “random” Zoom party, why not help them set one up where they can connect with their friends? You can host the party and receive your own private link. In doing so, you’ll be able to monitor the guest list and ensure that “Zoombombers” don’t hop in and ruin the fun.
Throwing an online party can be a lot of fun when you’re willing to get creative. Feel free to set up a specific theme or plan games for your child and their friends. You’ll be able to foster their friendship and connection while ensuring they all have a safe environment to be themselves.
|
||||
| 2021-05-14 10:00:00 | Defending the client-side attack surface (lien direct) | It is strange to think that not that long ago the Internet was a very different place. A place filled with static text content, marked up in HTML, and served up alongside a few included image files; mostly consumed by a small population of persons with specific interests. Today’s Internet consumer demands a vibrant and responsive user experience customized to their individual interests. A localized cornucopia of options from around the globe, available on demand. While many advancements in platforms and networking have contributed to this evolution, the ability to execute script code in the browser is perhaps the most significant both in terms of user functionality and potential for security exposures. A “Client-Side Attack” occurs when a user (the client) downloads malicious code from the server, which is then interpreted and rendered by the client browser. The classic example of such an attack is Cross-Site Scripting, which has been a staple of the OWASP Top Ten since its inception. These flaws are pervasive. A 2019 report from Feroot CX Security and Privacy, the 2019 Feroot User Security and Privacy Report concluded that the hidden activities of third-party tools and scripts expose up to 97% of organizations to theft of customer data. More recently, the 2021 Hacker Report showed significant year over year increases in reported web-related security vulnerabilities and that 96% of hackers are working on hacking web applications. Sadly, these figures are far from surprising. According to that same 2019 Feroot report, modern web applications load an average of 21 third-party scripts as part of the user experience. This integration of third-party code creates a software supply chain that is assembled and executed on the client’s machine in near real time. The risk that one or more of the included scripts has been tampered with by threat actors at any given point in time is real and can have significant consequences as many organizations impacted by “web skimming” or “Magecart” attacks have learned. These attacks occur when an attacker inserts malicious script code, or a reference to include such code, into a payment or other transactional page. The code is downloaded and executed on the client browser which typically sends a copy of the sensitive information to a location of the attacker’s choice. Because of the subtle nature of these campaigns, they can be difficult to detect. For example, Warner Music recently disclosed that a number of the company’s on-line stores had fallen victim to such a campaign that lasted for several months.They are not alone. Many companies have been impacted by such campaigns and given the surge of online transactions as a result of the COVID-19 pandemic, it is no surprise that threat actor groups are increasingly focused on exploitation and monetization of such vulnerabilities. Even in the absence of malicious intent, simple human error can result in security impacting disclosures. If developers are passing sensitive details in the URL parameters or the page title of a web resource, analytics platforms may receive those elements. These may include usernames, credentials, or other information that could be considered Personally Identifiable Information (PII). Legitimate scripts may collect sensitive data from the website for analysis without the full understanding of | Tool Threat | |||
| 2021-05-06 10:00:00 | Password security tips and best practices for enterprises (lien direct) | In honor of World Password Day, we’re doing our part to help keep your business secure by discussing the good, the bad, the ugly and the critical about passwords. Let’s face it: between all the logins we need for work and all the accounts we use in our personal lives, there are too many passwords to remember. So many of us do what seems natural—use the same password for multiple accounts. After all, especially with corporate password policies, most employees use strong passwords with a mix of numbers, lowercase and uppercase letters, and special characters. Still, what about all those sticky notes we have “secretly” hidden in locations probably not far away from our devices? That security risk is only the tip of the iceberg. Because according to a 2019 Lastpass survey, US employees working in mid-sized corporate businesses must manage approximately 75 passwords for work. Unsurprisingly, employees recycle passwords 13 times on average. In other words, employees are using the same passwords over and over. And in many cases, especially for corporate applications and resources that lack strong password requirements, some passwords just aren’t strong enough. Cybercriminals know this, and it’s why breaches happen. If hackers get access to your trusted data, the ramifications can be dire. The costs of a data breach go well beyond financial, and include damage to your company’s brand, trust and reputation. Why do we need stronger and longer passwords? As malware, phishing, and ransomware continue to skyrocket, we must understand that the password is the primary method for attackers to gain access to corporate systems. Phishing passwords may be the easiest method, but passwords can also be cracked. The stronger the password, the harder it is for cybercriminals to decode. In a typical attack—the brute force password attack—attackers will use software that quickly attempts every possible password combination of numbers, letters, and symbols. These software programs get better as computing power increases. For example, an eight-character strong password was not long ago considered secure and difficult to crack. Today, it can be cracked in eight hours. But if we tack on two more characters to make it ten-character, cracking the password can take approximately five years. Why do we need unique passwords for every login? As mentioned above, phishing is one of the simplest ways for hackers to steal our passwords. If you think your company has been victimized by phishing, malware, or ransomware, perhaps you’ve taken steps to reset those passwords. But the security risk here is if employees are using the same passwords for different apps, sites or resources. Have you heard about credential stuffing? With credential stuffing, attackers take username and password combinations they already know (which have been stolen or paid for on the dark web) and try them everywhere they can. Use of credential stuffing is escalating, and businesses of all sizes should take note. This type of attack is only successful if and when employees use the same password for different logins. What about password managers? Managing all those passwords doesn’t have to be complicated. A password management system is software that keeps an up-to-date list of all your passwords and logins, using a master password to access the password “vault”. That master password is the only one you need to remember. What if a hacker accesses your vault? Isn’t that riskier? Sure, there is undoubtedly an element of risk, but it’s critical to think in terms of relative safety. As a general rule, using some type of password | Ransomware Data Breach Hack | LastPass | ||
| 2021-05-05 10:00:00 | 5 IT security strategies that you should think about as employees return to the office (lien direct) | This blog was written by an independent guest blogger. Without a doubt, digital transformation accelerated amid the pandemic and made it possible for employees to work remotely. However, it also intensified the threat landscape created by malicious attackers who jumped on the first opportunity to attack the more vulnerable home networks. As remote working becomes the new norm, it is paramount to have an agile infrastructure and team for security. Companies need to manage and orchestrate appropriate remediation activities carefully. Focus on providing awareness training Industry research has shown a 300% increase in the rate of cyber-crimes since the pandemic began, as malicious attackers leverage the opportunity to attack vulnerable home networks to access sensitive data. Security awareness is the most important thing to teach your employees when moving towards a secure organizational culture. Security awareness training can help everyone get on the same page and understand the depth of the threats to reduce risks and incidents. Awareness is also critical because it can help employees prepare for unforeseen situations and equip them with security knowledge to know what measures to take in case of a problem. On top of general awareness for your employees, remember to facilitate your IT team and developers with application security awareness. This is especially important because as threats and malicious attackers find innovative ways to crack vulnerabilities, your IT team should be equipped to find solutions to new attacks. You can grow your security culture with these teachable moments: Have a conference with your IT department where all employees are given security training For workers working remotely, a security guide should be sent out to them detailing all security attacks, protocols, and preventions to follow Teaching advanced lessons to employees in the R&D department to build secure products and services. Make your employee payment system safer Creating invoices for sales and payment can be time-consuming, not to mention the number of security risks that come with sending payment invoices over emails. Emails go through several networks, including DNS servers, mail servers, and routers, before reaching the intended recipient. Along this route, cybercriminals are patiently waiting to intercept the email, looking for vulnerabilities and private information that they use to commit fraud. Since these emails include personal information such as your bank account number and contact number, it makes your emails highly vulnerable to malicious attacks. You can have all the updated technology and an advanced security team. Still, even if you send out one unencrypted email with an attached invoice, you run the threat of being exposed to cybercriminals. Opt for invoicing software apps such as those with PCI-DSS certification, meaning that all financial data will be kept secure using encryption for both your business and your employees. Implement multi factor authentication Multi factor authentication means adding an extra layer of security that involves asking more than just basic information required in single-factor authentication. It usually consists of a combination of information known only by the user, such as a security question, pin code, or an alternate email. Research | Vulnerability Threat | |||
| 2021-05-04 10:00:00 | New Advanced AlienApps for Fortinet (lien direct) |
Here at AT&T Cybersecurity, we feel strongly that security should fit into your business, not the other way around. We lower the friction security brings to day-to-day operations through automating the essential security operations such as detection and response. By integrating different security products together to form a consolidated security architecture, companies can be protected with less effort.
Recently, we’ve taken another step on this journey by releasing a new pair of Advanced AlienApps for Fortinet. Our Advanced AlienApps for FortiGate and FortiManager join our suite of existing AlienApps for Fortinet to enable collection of data and security response across the entire Fortinet product suite.
 The FortiGate and FortiManager integrations unlock multiple response actions that make SOC analysts aware of what’s happening with network security and allow them to respond to alarms quickly. Let’s take a look.
FortiGate: Easy Firewall Integration
The easiest, most straightforward integration comes via the FortiGate Advanced AlienApp. This AlienApp allows SOC analysts to send response actions from Alarms or Events directly to your Fortinet firewall. It is intended for use on a single firewall or HA pair of firewalls, and it allows the following response actions:
Add a source or destination address to an Address Group. The most common use case for this integration is shown in the figure 2 – blocking access to a potentially malicious internet destination. This functionality can also be used to unblock addresses once the crisis is resolved.
Add to custom category. If you are using URL filtering categories to block access to inappropriate or potentially dangerous web sites, this method will enable you to add a URL to one of your custom categories. Note that this is useful to block or unblock site
Add address to static URL filter.
The FortiGate and FortiManager integrations unlock multiple response actions that make SOC analysts aware of what’s happening with network security and allow them to respond to alarms quickly. Let’s take a look.
FortiGate: Easy Firewall Integration
The easiest, most straightforward integration comes via the FortiGate Advanced AlienApp. This AlienApp allows SOC analysts to send response actions from Alarms or Events directly to your Fortinet firewall. It is intended for use on a single firewall or HA pair of firewalls, and it allows the following response actions:
Add a source or destination address to an Address Group. The most common use case for this integration is shown in the figure 2 – blocking access to a potentially malicious internet destination. This functionality can also be used to unblock addresses once the crisis is resolved.
Add to custom category. If you are using URL filtering categories to block access to inappropriate or potentially dangerous web sites, this method will enable you to add a URL to one of your custom categories. Note that this is useful to block or unblock site
Add address to static URL filter.
 FortiManager Integration
Integration with FortiManager opens up more use cases. FortiManager typically controls many different firewalls in your environment. Consider the simple use case above – blocking access to a malware command and control. If there is only one way out of your network, then the FortiGate implementation has you covered, but if you have path diversity, with different exits in different parts of the world or with different providers, the FortiManager integration is needed.
FortiManager Integration
Integration with FortiManager opens up more use cases. FortiManager typically controls many different firewalls in your environment. Consider the simple use case above – blocking access to a malware command and control. If there is only one way out of your network, then the FortiGate implementation has you covered, but if you have path diversity, with different exits in different parts of the world or with different providers, the FortiManager integration is needed.
 As with all Advanced AlienApps, we’ve included a rich dashboard for both FortiManager and FortiGate. The FortiManager dashboard above gives a quick look at active users, alert trends, and event types. The FortiGate dashboard includes events
As with all Advanced AlienApps, we’ve included a rich dashboard for both FortiManager and FortiGate. The FortiManager dashboard above gives a quick look at active users, alert trends, and event types. The FortiGate dashboard includes events |
Malware Threat | |||
| 2021-05-03 10:00:00 | The new normal is actually very normal: Punctuated equilibrium, security cycle theory, and the “New Normal” (lien direct) | In 2020, the world was hit with an unexpected pandemic that changed much of life as many had come to know it. Virtually overnight, masks were required, employees were working remotely, children were home from school, and businesses were locked down to stop the spread of Covid19. In reading the news and social media the term “The New Normal” has taken front and center as the image that is being promoted. FBI statistics show that due to the pandemic and the increase in remote workers, cyber fraudsters have taken a much more active role. Other criminals are also taking advantage of the situation. The dire sounding term “The New Normal” seems to suggest that life will be forever changed and we, as humans, will struggle to adapt. What occurred in 2020 was neither “new” nor is it as dire as it sounds. Punctuated equilibrium is a theory originally developed by paleontologists to explain evolutionary biological change. It has since been applied to numerous other areas such as Political Science, social theory, technological change, corporate behavior, and organizational theory. In short, the theory posits that policies generally remain static and only change incrementally due to various constraints such as bounded rationality, cultures, and vested interests. Policy is characterized by long periods of stasis that only change when punctuated by changes in the conditions. History is replete with examples of punctuated equilibrium changing policy and people’s actions and behavior. The impact can be found on both a macro level in which the world, and nations, may change and a micro level in which communities, companies, and people are impacted. In the 14th Century the world was struck by the Bubonic Plague, otherwise known as the “Black Death”, which, per estimates, killed between 25% and 40% of people living in Europe. Until that time France and England were in a near state of perpetual war, and the English were content with the Feudal system. After the plague struck, France and England were forced to agree to a truce to their perpetual warring. It also brought about the end of the English Feudal system and completely changed society and social structures. Unfortunately, those with more sinister ideas used the plague to commit pogroms against certain ethic groups. On June 24, 1914, the heir to the Austrian Throne, Arch Duke Ferdinand was assassinated in the Streets of Sarajevo. While tensions had been brewing within Europe for years, no country wanted to inflame the situation and a state of tense peace remained. The assassination, however, proved to be the proverbial straw that broke the camel’s back and thrust Europe into one of the costliest and deadliest wars in history. This war, in turn, changed the entire world and resulted in new countries being created and others subsumed. While Europe raged with war between 1914 and 1915, the United States maintained an isolationist posture and did not enter the war. Certainly, there were some efforts to provide materials and support, but the US took a laisse fair approach to the War in Europe and did not want to intercede. That all changed on May 7, 1915 when a German U Boat sank | Threat | |||
| 2021-04-29 10:00:00 | The importance of creating a small business Cybersecurity plan (lien direct) | This blog was written by an independent guest blogger. It’s estimated that cyber crime will cost businesses as much as $45,000,000,000 by 2025. Each year, small businesses who haven’t put a cyber security plan in place are at the mercy of hackers who are using ever increasingly sophisticated methods to breach their network, compromise their data - and even hold the business to ransom. In this article, we’ll be looking at the importance of creating a small business Cybersecurity plan, and we’ll also show you which steps you need to take to create one of your own. Why you need a Cybersecurity plan Developing a cyber security strategy means you’re being proactive. You’re staying on top of risk and nipping attacks in the bud. Early detection of threats A Cybersecurity plan allows you to sniff attacks out quickly; while this doesn’t necessarily mean you’ll prevent an attack altogether, it does increase your chances of successfully resolving it. Quick response to threats Once you’ve detected a threat, you can then react quickly. Doing so will invariably save you time, money and hassle. It will also prevent your business from encountering a large-scale crisis that shuts it down completely, at least for a while. Improved operational efficiency On a macro level, a Cybersecurity plan allows your business to continue running efficiently. With procedures in place to thwart attacks automatically, your team can continue performing their jobs, focusing on the core aspects of your business. Creating a small business Cybersecurity plan Choose a firewall Firewalls monitor your incoming and outgoing network traffic, looking out for malicious data packets before blocking them to prevent further problems. They are often your first line of defence against online attacks. However, there are different types of firewalls for different-sized businesses with different needs: Network firewalls are designed to protect multiple computers at the same time. Host-based firewalls defend a single computer. If your system has multiple computers, each one would require its own firewall if you choose this type. Enterprise firewalls are the most expensive. They include VPNs and advanced monitoring, and are aimed at bigger businesses with numerous users and networks. Choose the right Cybersecurity software A Cybersecurity strategy starts with investing in the right tools. Cybersecurity tools are the easiest way to give yourself peace of mind, because you know that you’ve built a second line of defence on top of your firewall. All businesses should make antivirus and anti-malware software a key part of their Cybersecurity plan. However, there are a lot of tools to consider, and each one has its pros and cons, being aimed at different organisations facing different threats. Features to look out for include: Threat intelligence Network and host intrusion detection SIEM security and monitoring Patch management Secure VPN Report generator Multi-layer ransomware protection In 2021, the best software may include Artificial Intelligence (AI). AI in antivirus software is able to detect network anomalies, targeting those that behave suspiciously and preventing a breach. It can also spot new user log-ins and disable them, or at the very least notify you or the system administrator. Put together a cross-functional secu | Ransomware Guideline | |||
| 2021-04-28 10:00:00 | What Docker runtime deprecation means for your Kubernetes (lien direct) | This blog was written by an independent guest blogger. On December 8, 2020, Kubernetes released version 1.20—the third and final release of the popular container orchestration platform in 2020. Kubernetes noted in a blog post that the version contained 42 enhancements. Of those enhancements, 16 entered into alpha, while the remainder moved to beta or graduated to stable at 15 and 11, respectively. That’s not all that was in Kubernetes version 1.20, however. The new release also came with the announcement of dockershim’s forthcoming deprecation. This blog post will discuss what this change means to admins and provide some recommendations on how admins can respond. Before we do that, however, we need to cover the basics of how dockershim relates to Kubernetes and why the platform decided to deprecate the component in the first place. An Overview of Dockershim Dockershim is a module used by the kubelet to support Container Runtime Interface (CRI) for Docker. Released back with Kubernetes version 1.5 in 2016, CRI is a plugin that allows the kubelet to use different container runtimes without recompiling. Those Kubernetes-supported software that are responsible for containers include containerd, CRI-O and Docker for the next few months, at least. The issue with dockershim is that this container runtime predates Kubernetes’ release of CRI. As noted in its documentation, Kubernetes’ early releases offered compatibility with just one container runtime: Docker. That changed as time went on and as cluster operators expressed the desire to interact with other container runtimes. Kubernetes created CRI to help those cluster operators, but as its support of Docker came before CRI, the container orchestration platform had to come up with an adaptor component that helped the kubelet interact with the Docker container runtime as if it were a CRI compatible runtime. This led to the emergence of dockershim. Keeping dockershim around ultimately created problems for Kubernetes, however. The issue here is that the kubelet needs to call another component—dockershim—before it can interact with continerd, CRI-O or another supported CRI. It’s a middle man that complicates container runtimes for the platform as a whole. Indeed, in the words of Kubernetes, “that’s not great, because it gives us another thing that has to be maintained and can possibly break.” Dockershim was only meant to be a temporary solution. Acknowledging that fact, the task of maintaining dockershim had become sufficiently problematic by the end of 2020 that it placed “a heavy burden on the Kubernetes maintainers,” according to the platform. Hence Kubernetes’ decision to deprecate the component. Going forward, Kubernetes will inform administrators of this deprecating issue starting in version 1.20. As explained by StackRox in a blog post: If you currently use a managed Kubernetes service or a distribution like OpenShift, your provide | Uber | |||
| 2021-04-27 10:00:00 | Priority on people - An argument against the excessive use of Cybersecurity technology (lien direct) | Introduction Despite what many advertisements and salespeople would like you to think, you don’t need to (and in many cases shouldn’t) spend a fortune on security tools to achieve a robust cybersecurity program. Some tools are essential, such as a ticketing tool or Security Information and Event Management (SIEM) system, but the best security programs are built off the employees that run the business. Without their support and understanding, even the most secure system or software suite could be brought tumbling down with little effort. Every member of an organization with access to computers or data is a potential source of compromise and a potential source of system failure. Almost every component, system, or workflow, down to the fundamental building blocks of society, rely on the fair and accurate participation of those involved in it. Accordingly, any deviance, whether intentional or not, from this set state can cause significant issues to arise. It is vital that the security team realize that the purpose of security is, foremost, to promote the ability of the business to do business. Excessively complex or costly security measures that do not serve the needs of the organization or support it in its mission are worse than no security at all. Staff over software One of the first categories of people to focus on is your security (or IT) staff. Some technology requires specific skills, knowledge, or time, any one of which your team may lack. Without first considering the available resources needed to implement, use, or even maintain any given software solution, you would be missing a critical component in the evaluation process. Any software or tool is only as good as the person using it, regardless of how expensive or cutting edge it may be. Each software implemented, outside of the standard ‘install and forget’ type, requires planning, reviews, training, and maintenance to be effective. Given the state of most IT and Cybersecurity teams, there is likely not enough hours to go around to properly execute the necessary tasks needed to meet the above requirements. Implementation and maintenance requirements will vary based on the type of software, but it will always be present and should be factored into the overall cost of the solution being considered. The second category is, of course, the employees of the organization. Not all tools will solely reside in the domain of the IT or Security teams and may be rolled out to broad swathes of the organization. As anyone who works in cybersecurity knows, we walk a careful line between security and functionality. The software we pick, therefore, must be secure enough without being overly complex or burdensome. Any solution must be ‘right-sized’ to the institution, both in cost and effectiveness, but also in adoptability. If staff refuse to, or are unable to, use the new tool it serves very little purpose in the overall mission of security. Instead of prioritizing software, it is recommended to focus first on user training on key security issues and on the acceptable use of technology. Part of this training should include active testing such as phishing campaigns or other social engineering endeavors. Focusing on employee training has been seen to lead to a far higher return security-wise when compared to equivalent software solutions. When to use software To be clear, it is not being argued that organizations shouldn’t use any software. In order to have a fully mature and functional security program, there are several critical components that any organization should adopt. Specific requirements will vary per organization, industry, and regulatory requirements, but a general list of ‘must-haves’ is: SIEM software End-point protection software Vulnerability scanning software Mobile Device Management (MDM) software (as needed) Backup software Encryption te | Tool Guideline | |||
| 2021-04-26 10:00:00 | The 5 most crucial Cybersecurity updates for businesses in 2021 (lien direct) | This blog was written by an independent guest blogger. For as long as businesses have used computers, cybersecurity has been crucial. Now, as modern business and data are becoming inseparable, it’s an absolute necessity. As companies start to recover from 2020 losses, they should consider investing in security updates. Cybercrime reached new heights in the past year, with internet crime reports rising 69.4% and costing more than $4.2 billion. Now that more companies are embracing digital services after the pandemic, this trend will likely continue. All businesses, regardless of size or industry, must revisit their cybersecurity. Here are the five most important cybersecurity updates for this year. 1. Implementing a Zero-Trust framework The single most crucial cybersecurity upgrade for businesses this year is adopting a zero-trust security framework. These systems, which rely on network segmentation and thorough user verification, aren’t new but are increasingly crucial. In light of rising cyberthreats, companies can’t afford to trust anything inside or outside their networks without proof. A 2020 survey found that 82% of company leaders plan to let their employees work remotely at least part time after the pandemic. That many people accessing data remotely raises security concerns. Hackers could pose as remote workers to gain access or install spyware, and IT teams wouldn’t know it. Zero-trust models mitigate these threats. Verifying user identity at every step helps guarantee only employees can access mission-critical data. Segmentation ensures that only those who need access can get it, and if a breach occurs, it won’t impact the entire network. 2. Securing machine learning training data Machine learning algorithms are becoming increasingly common among companies in various industries. These models take considerable amounts of data to train, which presents an enticing opportunity for cybercriminals. As more companies rely on machine learning, more threat actors will likely try to poison the training data. By injecting incorrect or corrupt data into the training pool, cybercriminals could manipulate a machine learning system. If companies don’t catch the problem before it’s too late, the algorithms they rely on could influence poor or even harmful business decisions. Given this threat, securing machine learning training data is a must. Businesses should carefully inspect the information they use to train machine learning models. They should also enact stricter access controls over training pools, including activity monitoring. 3. Verifying third-party and partner security Businesses should also look outward when improving their cybersecurity. The growing public awareness of cyberthreats is changing expectations about visibility, and that’s a good thing. It’s no longer sufficient to trust that a business partner or third party has robust data security. Companies must verify it. Third-party data breaches in 2020 exposed millions of records, and major events like the SolarWinds hack have revealed how fragile some systems are. In light of these risks, businesses must ask all potential partners to prove | Data Breach Hack Threat Guideline | |||
| 2021-04-23 10:00:00 | Lessons learned from building an inventory of systems (lien direct) |
IT asset inventory vs an ISI – What’s the difference?
Many frameworks, standards, and regulations require organizations to have an IT Asset Management program in place. However, the understanding of what separates a mature Information System Inventory (ISI) from an IT Asset Inventory and the benefits realized from an ISI are generally less well understood. Naturally this may lead to a higher likelihood of deprioritizing an ISI in favor of what are viewed as more pressing security needs.
 Figure 1. An Information System Inventory (ISI) is a record of Information Systems in an organization and includes information traditionally in an IT Asset Inventory.
But a properly constructed ISI should be prioritized as the foundation on which organizations implement a System Development Lifecycle (SDLC) program, facilitate Security Operations activities, make informed risk management decisions, move towards a more data centric view of security and mature their security posture as a whole. The ISI is an opportunity for an organization to have a core source of intelligence that ties security information across the organization together. Having the ability to view risk at multiple levels (network level, system level, division level, organizational level etc.) is becoming ever more important as organizations implement more complex environments and move away from a traditional network perimeter.
Policy, process & training: Ensuring reliable information
One of the best places to start maturing the ISI is to mature the categorization process. Without measures in place to ensure repeatability and consistency, information may become suspect and of little value. It is critical to implement a process that satisfies the need for stringent accuracy, but that is not so cumbersome it makes efficient use of personnel resources difficult. One of the most effective ways to balance this need for accuracy with the need for agility, is to invest significant time in process creation, documentation, and training. This includes defining and documenting the process itself, definitions for each field and each possible field answer, and the creation of tools such as interview templates and forms.
Utilizing training sessions and tabletop exercises then ensure all interviewers implement the processes in a consistent and accurate manner. As categorizations are conducted on an annual or recurring basis, it is important to continuously update the process documentation, definitions, and training to align with the implemented process.
Figure 1. An Information System Inventory (ISI) is a record of Information Systems in an organization and includes information traditionally in an IT Asset Inventory.
But a properly constructed ISI should be prioritized as the foundation on which organizations implement a System Development Lifecycle (SDLC) program, facilitate Security Operations activities, make informed risk management decisions, move towards a more data centric view of security and mature their security posture as a whole. The ISI is an opportunity for an organization to have a core source of intelligence that ties security information across the organization together. Having the ability to view risk at multiple levels (network level, system level, division level, organizational level etc.) is becoming ever more important as organizations implement more complex environments and move away from a traditional network perimeter.
Policy, process & training: Ensuring reliable information
One of the best places to start maturing the ISI is to mature the categorization process. Without measures in place to ensure repeatability and consistency, information may become suspect and of little value. It is critical to implement a process that satisfies the need for stringent accuracy, but that is not so cumbersome it makes efficient use of personnel resources difficult. One of the most effective ways to balance this need for accuracy with the need for agility, is to invest significant time in process creation, documentation, and training. This includes defining and documenting the process itself, definitions for each field and each possible field answer, and the creation of tools such as interview templates and forms.
Utilizing training sessions and tabletop exercises then ensure all interviewers implement the processes in a consistent and accurate manner. As categorizations are conducted on an annual or recurring basis, it is important to continuously update the process documentation, definitions, and training to align with the implemented process.
 Figure 2. A possible process for categorizing an Information System
It is also important to design the categorization process to allow for documentation of reasoning behind critical fields. Besides the obvious benefit of providing a high level of confidence that the information is accurate and easing the quality assurance process, this also has the added benefit of capturing inevitable grey areas and edge cases not considered in the original process. As the organization continues to mature their ISI and the categorization process evolves, notes on previously categorized systems are also invaluable in backfilling information for newly identified business uses. This reduces re-work required, helps ease maintenance of the ISI, and provides a more accurate picture of current risk.
Figure 2. A possible process for categorizing an Information System
It is also important to design the categorization process to allow for documentation of reasoning behind critical fields. Besides the obvious benefit of providing a high level of confidence that the information is accurate and easing the quality assurance process, this also has the added benefit of capturing inevitable grey areas and edge cases not considered in the original process. As the organization continues to mature their ISI and the categorization process evolves, notes on previously categorized systems are also invaluable in backfilling information for newly identified business uses. This reduces re-work required, helps ease maintenance of the ISI, and provides a more accurate picture of current risk.
 Figure 3. A short list of possible categorization fields and reasoning fields for critical fields.
Figure 3. A short list of possible categorization fields and reasoning fields for critical fields. |
Vulnerability Guideline | |||
| 2021-04-21 10:00:00 | Bridging the Cybersecurity frontier: SaaS (lien direct) | This blog was written by an independent guest blogger. Software as a service (SaaS) is one of the most important parts of the modern digital business. Unfortunately, when it comes to cybercrime, it can also be one of the weakest. The Cybersecurity newsletter, The Hacker News, have highlighted this in detail, noting interest from across the digital industry in addressing the holes created by misconfigured SaaS setups. The use of unsanctioned business software, and the lack of controls and best practices to help assist companies with assurance can create a bad concoction. Addressing this requires a complete overhaul of business processes, starting with addressing the very nature of SaaS usage by the company. Looking at core philosophy SaaS is, according to Forbes, a key disruptor in many global markets. Utilized not just by digitally-focused businesses, this has unfortunately meant that many businesses are keen to get on the bandwagon long before they are prepared. This lack of preparation for the use of SaaS is what creates issues with security in the long run. How can businesses meet this risk and mitigate it? A key part of achieving this is through controlling growth. There is a compelling argument to be made that unbridled growth has caused many of the issues that digital businesses, not just SaaS-focused ones, have. Whether that’s through DDoS attacks, insufficient manpower to staff operations or other situations, demand can exceed capacity. That includes security systems. When considering the advantages of the model, businesses moving into SaaS should therefore also ensure that they have proper capacity to meet the customer demand and ensure a high level of cybersecurity assurance. Building from the base Having a measured growth strategy that is inclusive of the potential demands of the business is a first step that allows a cybersecurity response to be built accordingly. The challenge SaaS poses is in a lack of assurance that users are following cyber protocols. The corridor between business and customer can let in malicious users and malware at any stage of a transaction – leading to a loss of data, revenue, reputational damage, or all three. Defining the risk and managing it is a case of forming ‘quarantine’ points, where businesses and their customers are able to securely store their data without risking it being accessed inappropriately by others. SASE systems Increasingly, businesses are meeting this demand using secure access service edge (SASE) systems, according to the UK's Computer Weekly. Research by Gartner expects 40% of businesses will be using SASE by 2024, and for good reason – it provides a secure environment through which to run SaaS, and all the risks it entails, without creating downtime for customers that could lead to lost revenues. Having this secure corridor also allows for other important business security measures, like data protection and security, to be carried out with a high level of assurance. SASE is not the only protocol to follow, and many businesses are constructing their own proprietary system security for their SaaS plat | Malware Guideline | |||
| 2021-04-20 10:00:00 | Best practices for businesses to stay safe online this tax season (lien direct) |
It’s tax time again. Typically, the deadline for federal tax filing in the United States is April 15, but this year the deadline has been extended to May 17, 2021. However, if you think your business will be receiving a refund, the IRS encourages you to file as early as possible.
Filing taxes can be stressful. Adding to the potential stress is the increasing tax scams out there and the ongoing battle to keep your company data protected and secure.
But staying safe online when filing taxes does not have to be stressful.
We’ve come up with some tips and suggestions to help and have organized them into three categories: how to secure your device, best practices when online, and how to work with your tax preparer or accountant.
 Your device
Whether it’s your smartphone, tablet or desktop, you’ll want to provide that the device you use to file taxes is as secure as possible.
The first step involves passwords. Not only should your password be more of a pass phrase (like 2dogswalkingInthe^^park), but the password you use for anything concerning taxes should be completely different from passwords used for other accounts. Sure, remembering different passwords for separate logins is difficult, but password managers can be very helpful, for tax season and for regular password management.
Next, it’s highly recommended to use multi-factor authentication (MFA). If you’re doing online banking, you’re probably familiar with MFA, which provides an additional layer of security by sending you a unique one-time code via email or text message. Most online tax services offer this optional, but more secure and recommended, method of authentication.
Securely logging in is only the beginning. Before you even log in and start using any tax-related software, you’ll need to make sure that all the software is up to date—not just the tax software but the operating system as well, whether that’s Windows, iOS, Android, or Mac OS. Running the latest version of the software means any security issues will be addressed and up to date, and that system performance is optimized.
When it comes to devices, the final piece of the security puzzle is where you are when you file your taxes. Especially when such confidential and sensitive information is being transferred over the internet, a secure network is crucial. If at all possible, avoid using public wi-fi. If you must use public wi-fi, ensure that you’re using a VPN.
Your online behavior
Tax season can be stressful, and when we’re stressed, it’s much harder to be vigilant about our online behavior and security. But how you react to messages and people online will play a key role in keeping secure.
Perhaps the most important takeaway of this entire article is this: never provide sensitive information to anyone online, over text, or over the phone unless you can verify they the person or agency on the other end is legitimate.
Whenever you receive a call, text, or email that asks you to provide valuable financial or personal information, it is most likely a scam. By providing this data to thieves, you may lose money or even your identity.
Always be suspicious.
But how can you tell if it’s a scam?
If the message claims to be from the Internal Revenue Service (IRS), know that the first method of contact for the IRS is carried out through the U.S. Postal Service. Only if you’ve responded in some way to their communication through physical mail will they follow up with a phone call.
Plus, The IRS will never insist that payment must be made to anyone other than the U.S. Treasury.
Be especially skeptical of calls claiming to be from federal agencies that use what may appear to be a legitimate caller ID. Many of these calls are scams. If yo
Your device
Whether it’s your smartphone, tablet or desktop, you’ll want to provide that the device you use to file taxes is as secure as possible.
The first step involves passwords. Not only should your password be more of a pass phrase (like 2dogswalkingInthe^^park), but the password you use for anything concerning taxes should be completely different from passwords used for other accounts. Sure, remembering different passwords for separate logins is difficult, but password managers can be very helpful, for tax season and for regular password management.
Next, it’s highly recommended to use multi-factor authentication (MFA). If you’re doing online banking, you’re probably familiar with MFA, which provides an additional layer of security by sending you a unique one-time code via email or text message. Most online tax services offer this optional, but more secure and recommended, method of authentication.
Securely logging in is only the beginning. Before you even log in and start using any tax-related software, you’ll need to make sure that all the software is up to date—not just the tax software but the operating system as well, whether that’s Windows, iOS, Android, or Mac OS. Running the latest version of the software means any security issues will be addressed and up to date, and that system performance is optimized.
When it comes to devices, the final piece of the security puzzle is where you are when you file your taxes. Especially when such confidential and sensitive information is being transferred over the internet, a secure network is crucial. If at all possible, avoid using public wi-fi. If you must use public wi-fi, ensure that you’re using a VPN.
Your online behavior
Tax season can be stressful, and when we’re stressed, it’s much harder to be vigilant about our online behavior and security. But how you react to messages and people online will play a key role in keeping secure.
Perhaps the most important takeaway of this entire article is this: never provide sensitive information to anyone online, over text, or over the phone unless you can verify they the person or agency on the other end is legitimate.
Whenever you receive a call, text, or email that asks you to provide valuable financial or personal information, it is most likely a scam. By providing this data to thieves, you may lose money or even your identity.
Always be suspicious.
But how can you tell if it’s a scam?
If the message claims to be from the Internal Revenue Service (IRS), know that the first method of contact for the IRS is carried out through the U.S. Postal Service. Only if you’ve responded in some way to their communication through physical mail will they follow up with a phone call.
Plus, The IRS will never insist that payment must be made to anyone other than the U.S. Treasury.
Be especially skeptical of calls claiming to be from federal agencies that use what may appear to be a legitimate caller ID. Many of these calls are scams. If yo |
||||
| 2021-04-19 20:38:00 | Introducing AT&T\'s Managed Endpoint Security with SentinelOne (lien direct) | With 5G, edge solutions, and digital transformation all around us, every enterprise should be taking a closer look at their endpoint security and evaluate options that will be able to keep pace with this dynamic new environment.The newly introduced AT&T Managed Endpoint Security with SentinelOne™ offer brings world class managed services with comprehensive endpoint security. SentinelOne brings best-of-breed Endpoint Protection Platform (EPP) and Endpoint Detection and Response (EDR) with deep integration into the AT&T Unified Security Management (USM) platform and Alien Labs Open Threat Exchange (OTX). This deep integration, along with AT&T’s 500+ partner integrations, can provide businesses Extended Detection and Response (XDR) capabilities from the endpoint to the network to the cloud. Plus, through the AT&T Security Operations Center, businesses can rely on world class monitoring and management of their endpoints. Here are the unique benefits it can bring to enterprises: Industry leading technology Joining forces with the best of the best is crucial especially when it comes to endpoint security. AT&T has teamed up with SentinelOne who provides next-generation endpoint security combining antivirus, EPP, and EDR into one agent. SentinelOne has been highly recognized in the industry and was number 1 in the 2020 MITRE ATT&CK test - APT 29 for most total detections and most correlated alerts through comprehensive storyline technology. This autonomous agent utilizes Artificial Intelligence (AI) and machine learning (ML) to help protect against known and unknown threats and eliminates reliance on external factors for protection. This faster, “machine-speed” detection & response provides continuous protection, even when offline. And, in the event of an attack, the SentinelOne agent can perform 1-click remediation and rollback with no custom scripting or re-imaging required. Deep integration with AT&T’s USM platform and Alien Labs OTX AT&T Cybersecurity and SentinelOne bring one of the most unique combinations in the market via the deep integrations between the SentinelOne platform and the AT&T USM platform. This deep integration allows for orchestrated and automated incident response on the endpoints. Additionally, deep integrations were built between the world’s largest open threat intelligence community, AT&T Alien Labs Open Threat Exchange (OTX), and the SentinelOne agent. The AT&T Alien Labs OTX encompasses over 145,000 security professionals submitting over 20 million threat indicators per day. Additional context is provided from the USM sensor network with an additional 20 million threat observations per day and AT&T’s Chief Security Office analyzing over 446 PB of traffic from 200 countries and territories. By correlating the incidents of compromise from AT&T Alien Labs OTX, AT&T is able to deliver added context that allows for faster responses. These same AT&T Alien Labs detections and threat intelligence also informs threat hunting on SentinelOne’s EDR data to help yield richer insights and easier detection of evasive threats. Expert management As one of the world's top MSSPs, AT&T Cybersecurity employs highly experienced and industry certified individuals for the Managed Endpoint Security with SentinelOne offering. AT&T brings over 25 years of experience in delivering managed security services and knows what it takes to keep pace with the dynamic threat landscape. To stay ahead, AT&T’s security analysts maintain security certifications including GSE, CISSP, CEH, and more. For the Managed Endpoint Security with SentinelOne offering, AT&T | Data Breach Threat Guideline | APT 29 | ||
| 2021-04-19 10:00:00 | Digital transformation moves application security to the top of mind list! (lien direct) | Here are some insights from AVP, Cybersecurity Todd Waskelis as we discussed cybersecurity and application security in focus. How has COVID changed the game for application security? Shift Left, Shift Right, and Shift everywhere? 2020 had several significant events around application security, including the move of applications to the cloud, the expansion of remote workers using cloud accessed applications, and an increase in the number of vulnerabilities reported in code. I think if we look at the basic lifecycle of Design, Develop, Test, and Deployment/Maintenance, we tend to focus today on the latter two stages – Test and Maintenance. Traditionally we address those with one-time preproduction testing, which, when issues are discovered, push the cycle backward to development. But once deployed, those identified vulnerabilities become more difficult to address and require either investment in additional infrastructure to ensure controls or, more commonly, prolonged exposure of that vulnerability due to limited resources (time, money, people) to address the issue. Shifting left leads with the idea of ensuring security is at the table during the design discussions not only from a technology perspective but also from a regulatory/legislative view. Knowing what controls will need to be cared for, commensurate with the data being processed, stored, and transacted. It also drives awareness to the developers early that security is a critical component and highlights their responsibilities in that commitment. o Secondly, and just as critical, is integrating frequent and (when possible) automated security testing into the development stage. This reduces the number of vulnerabilities when we move to test, thereby increasing deployment speed and reducing the time to market. o A large portion of the vulnerabilities we see are specific to a custom code or to highly intricate custom configurations. In this way, almost every vulnerability detected in an application can be considered a zero-day vulnerability. o With these recent types of trends, we expect an increased focus on application security during development, that shift left will become more important in the coming year. o One example is cross-site scripting. It is a purely technical class of vulnerabilities that stems from improper coding of web pages, and plays a major part in large cybercrime campaigns, such as the Mage cart web skimming campaign. Other vulnerability types do not stem from a technical problem, but, rather, from a failure to recognize and enforce business logic which is where we need to rely on the involvement in the design phase. How is the importance of secure code in application security tie into digital trust, risk, and resilience? o Secure code is more critical today than ever before and that is driven by a number of things, remote workforce, cloud native applications, explosion of mobile devices, emerging technologies like 5G and really the fact that everything is becoming a connected endpoint. o This focus on application security is nothing new, however the threats have grown, the risks have greatly changed the attack surface is much larger now, it's not within the four walls of your enterprise. o The customer experience is moving more and more to purely digital out of convenience, and eventually, that will shift to be the consumer's expectation. If you fail just once and that Digital Trust between you and your client breaks down, you risk significant loss of business and brand loyalty, and market share. o To put this into perspective, let's simplify with a banking example. Someone walks into a branch office of Bank of Todd and robs the | Vulnerability Guideline | |||
| 2021-04-16 10:00:00 | Considerations for performing IoMT Risk Assessments (lien direct) | What are Internet of Medical Things (IoMT) products? Internet of Medical Things (IoMT) products refer to a combination of medical applications and devices connected to healthcare information technology systems through an online computer network or a wireless network. IoMT devices rely heavily on biosensors, critical in detecting an individual's tissue, respiratory, and blood characteristics. Non-bio sensors are also used to measure other patient characteristics such as heart and muscle electrical activity, motion, and body temperature. IoMT product classifications One needs to gain insight into what makes a device a medical device. In the U.S., the sale of medical devices is regulated by the Food and Drug Administration (FDA). As required by the FDA, medical devices are classified as being Class I, Class II, or Class III based on the risk posed by the device. Therefore, one must understand the risk level of a medical device and its intended use and indications of use. IoMT layers and the threat-driven approach to security Like IoT, IoMT has several layers, including the business, application, application, middleware, network, and perception layers. Notably, the perception layer in IoMT is tasked with the transfer of medical data acquired from sensors to the network layer. Medical things types that fall under the perception layer can be classified as: wearable (muscle activity sensors, pressure and temperature sensors, smartwatches); implantable (implantable cardioverter defibrillators (ICD); swallowable (camera capsule); ambient (vibration and motion sensors), and; stationary devices (surgical devices, CT scan). Likewise, IoMT devices are subject to attacks based on their architecture or application. That is, IoMT devices can suffer layer-specific attacks. While hackers can target any layer for an attack, they typically focus on either the perception or network layer attacks. Perception layer attacks focus on devices that acquire data from sensors. Hackers use perception layer attacks to defeat the device administrator's ability to track the sensor and discover that it has been cloned or otherwise tampered with. Conversely, at the network layer, IoMT devices can be subject to DoS attacks, Rogue access, Man-in-the-Middle (MiTM), replay, and Eavesdropping. Common IoMT vulnerabilities arise from the challenges experienced during IoMT device development, such as the lack of a threat-driven approach to security. The threat-driven approach to security corresponds to modeling the relationship between threats, the risk to the asset, and the security controls that should govern them. For example, Bluetooth Low Energy (BLE) technology, whose applications range from home entertainment to healthcare, is associated with many threats such as network communication decryption, replay attacks, and Man-in-the-Middle attacks. Primary considerations in performing IoMT Risk Assessments Threat modeling is the tool best fitted for addressing perception and network-layer threats. Cybersecurity practitioners commonly use the STRIDE threat modeling technique to help solve IoMT-related security challenges at both layers. STRIDE is a threat model suitably fitted for helping cybersecurity practitioners identify and analyze threats in an IoMT environment. More specifically, STRIDE is the most adept tool for answering the question 'what can go wrong in the IoMT environment that can adversely affect patient safety?' The STRIDE model allows cybersecurity practitioners to determine what threat is a violation of a desirable property for an IoMT system. Desirable properties preserve privacy, data protection and contribute to the security of an IoMT asset. Desirable properties align with the STRIDE model as illustrated below: | Tool Threat |
To see everything:
Our RSS (filtrered)
