What's new arround internet
| Src | Date (GMT) | Titre | Description | Tags | Stories | Notes |
| 2017-05-22 18:04:42 | Video: How to survive the global cyberwar (lien direct) | Dr. Kenneth Geers, senior research scientist at Comodo and NATO Cyber Center Ambassador, explains #WannaCry and the steps business should take to protect critical assets during the next cyberattack. | Wannacry | |||
| 2017-05-22 17:54:54 | News in brief: Bitcoin price bubbles up; Uber uses AI to boost its take; WannaCry \'hero\' censures tabloids (lien direct) | Your daily round-up of some of the other stories in the news |
Wannacry Uber | |||
| 2017-05-22 17:05:29 | EternalRocks Worm Spreads Seven NSA SMB Exploits (lien direct) | A worm called EternalRocks has been spreading seven Windows SMB exploits leaked by the ShadowBrokers, including EternalBlue, which was used to spread WannaCry. | Wannacry | |||
| 2017-05-22 16:31:10 | Health Care and Ransomware: A Marriage Made in Hades (lien direct) | A widespread ransomware attack such as WannaCry can cause problems for any business. For a health care organization, it can cause an utter catastrophe. | Wannacry | |||
| 2017-05-22 15:52:41 | After WannaCry, EternalRocks digs deeper into the NSA\'s exploit toolbox (lien direct) | WannaCry may be behind us, but fears that the crooks might create new malware from the NSA's stash of exploits seem to be coming true |
Wannacry | |||
| 2017-05-22 14:10:17 | North Korea Denies Involvement in WannaCry Ransomware Outbreak (lien direct) | On Friday, North Korea denied allegations that it was somehow responsible for the WannaCry ransomware outbreak that affected over 240,000 computers in nearly 200 countries across the globe. [...] | Wannacry | |||
| 2017-05-22 14:08:25 | Meet the 22-year-old saviour who stopped the WannaCry ransomware attack (lien direct) | Marcus Hutchins: The 'Accidental Hero' Who Saved The World From The WannaCry Ransomware The world last week witnessed one of the most widespread cyberattacks in history that brought more than 2,30,000 computers running Windows operating system in 150 countries to a standstill. The biggest unprecedented ransomware attack could have got even worse had it not [...] | Wannacry | |||
| 2017-05-22 13:59:59 | A week in security (May 15 – May 21) (lien direct) |
 A compilation of notable security news and blog posts from the 15th of May to the 21st. We covered WannaCry, Privacy Awareness week, and what to do when you suspect stolen personal data.
Categories:
Security world
Week in security
Tags: biohacketernalrocksprivacy awareness weekssd vulnerabilitystolen dataWannaCryweekly blog roundupwikileaks
(Read more...)
A compilation of notable security news and blog posts from the 15th of May to the 21st. We covered WannaCry, Privacy Awareness week, and what to do when you suspect stolen personal data.
Categories:
Security world
Week in security
Tags: biohacketernalrocksprivacy awareness weekssd vulnerabilitystolen dataWannaCryweekly blog roundupwikileaks
(Read more...)
|
Wannacry | |||
| 2017-05-22 13:40:31 | North Korea denies link to WannaCry ransomware attack (lien direct) |  Some security researchers have found similarities between WannaCry and malware previously written by a hacking group linked to North Korea.
Read more in my article on the Hot for Security blog. Some security researchers have found similarities between WannaCry and malware previously written by a hacking group linked to North Korea.
Read more in my article on the Hot for Security blog.
|
Wannacry | |||
| 2017-05-22 13:11:33 | 98% of WannaCry victims were running Windows 7, not XP (lien direct) | New data from Kaspersky Lab shows that almost all of the WannaCry/WannaCrypt ransomware worm victims were running some version of Windows 7. | Wannacry | |||
| 2017-05-22 13:01:34 | Windows 7 Most Hit by WannaCry Ransomware (lien direct) | Most of the computers affected by the WannaCry ransomware outbreak were running Windows 7, security researchers have revealed. | Wannacry | |||
| 2017-05-22 13:00:54 | Jaya Baloo on WannaCry and Defending Against Advanced Attacks (lien direct) | Jaya Baloo, CISO of KPN, the Netherlands' leading telecommunications provider, talks to Mike Mimoso about the WannaCry ransomware outbreak and how large network providers and enterprises must contend with advanced attacks. | Guideline | Wannacry | ||
| 2017-05-22 12:00:34 | Keys for Crysis released, as decryption efforts of WannaCryptor files continue (lien direct) | ESET have prepared a new Crysis decrypting tool. Victims who still have their encrypted files can now download the decryptor from its utilities page. | Wannacry | |||
| 2017-05-22 09:51:29 | Newly Found Malware Uses 7 NSA Hacking Tools, Where WannaCry Uses 2 (lien direct) | A security researcher has identified a new strain of malware that also spreads itself by exploiting flaws in Windows SMB file sharing protocol, but unlike the WannaCry Ransomware that uses only two leaked NSA hacking tools, it exploits all the seven.
Last week, we warned you about multiple hacking groups exploiting leaked NSA hacking tools, but almost all of them were making use of only two
|
Wannacry | |||
| 2017-05-22 07:56:08 | WannaCry – Le bilan total est à 420 000 victimes dans le monde (lien direct) |  Petit point de bilan sur WannaCry après le weekend. Les principaux chiffres de statistique fourni par les grandes firmes spécialisées dans la sécurité informatique indiquent que le nombre de victimes infectées s'élève à 420 000 et que Windows 7 représente 98% des machines concernées. Petit point de bilan sur WannaCry après le weekend. Les principaux chiffres de statistique fourni par les grandes firmes spécialisées dans la sécurité informatique indiquent que le nombre de victimes infectées s'élève à 420 000 et que Windows 7 représente 98% des machines concernées. |
Wannacry | |||
| 2017-05-22 07:45:19 | Middle East largely unscathed after WannaCry cyber attack (lien direct) | The impact of WannaCry on the Middle East was reduced due to the attack falling on a weekend, but it is a stark warning | Wannacry | |||
| 2017-05-22 07:00:00 | Windows 7 accounts for most WannaCry infections (lien direct) | Statistics show that computers running Windows 7 accounted for the biggest proportion of machines infected with the WannaCry ransomware, while NHS suppliers are blamed for hampering patching by NHS trusts | Wannacry | |||
| 2017-05-21 03:01:12 | Ces attaques informatiques qui ont ébranlé le web (lien direct) | En bloquant des centaines de milliers de machines dans le monde, le ver WannaCry a marqué un nouveau jalon dans l'histoire des plus grandes attaques informatiques. Rétrospective.  |
Wannacry | ★★ | ||
| 2017-05-20 15:00:00 | Free WannaCry Ransomware Decryption Tool Released (lien direct) | No need to pay ransomware; WannaCry decryption tool is available for free on GitHub Researchers have finally been able to create a decryptor for the WannaCry ransomware that has affected more than 3,00,000 computers in 150 nations since its attack on computers running the Microsoft Windows operating system last Friday. For those unfamiliar, the WannaCry [...] | Wannacry | |||
| 2017-05-20 11:19:56 | The Week in Ransomware - May 19th 2017 - Uiwix, WannaCry Imitators, and Wallet Decrypted (lien direct) | From new ransomware and WannaCry imitations to decryption keys being released, ransomware developers continue to keep us busy.. This article will keep you up-to-date on the latest news and developments in ransomware. [...] | Wannacry | |||
| 2017-05-20 04:15:09 | Over 98% of All WannaCry Victims Were Using Windows 7 (lien direct) | Numbers released by Kaspersky Lab on Friday reveal that over 98% of all documented WannaCry infections were running versions of the Windows 7 operating system. [...] | Wannacry | |||
| 2017-05-20 02:12:06 | SMBv1 isn\'t safe (lien direct) | Long before WannaCry used a recently patched Microsoft vulnerability to exploit machines, the recommendation was to disable SMBv1. Disabling old protocols isn’t sexy. Â You’re breaking things, and not introducing new features. Â You’re fixing theoretical future attacks. Â Perhaps the willingness to take on this challenge is a good measure of the maturity level of ... Continue reading ‘SMBv1 isn’t safe’ » | Wannacry | |||
| 2017-05-19 20:11:28 | WannaDecrypt your files? The WannaCry solution, for some (lien direct) |
 A decryptor (Wanakiwi) that has been developed for WannaCry/WannaCrypt/wCrypt. There is a catch though, it only works for some operating systems.
Categories:
Cybercrime
Malware
Tags: Anti-RansomwaredecryptormalwareransomwareWana DecrptorWanaCrypt0rWanaKiwiWannaCryWannaCryptWannaCryptorWannakeyWCrypt
(Read more...)
A decryptor (Wanakiwi) that has been developed for WannaCry/WannaCrypt/wCrypt. There is a catch though, it only works for some operating systems.
Categories:
Cybercrime
Malware
Tags: Anti-RansomwaredecryptormalwareransomwareWana DecrptorWanaCrypt0rWanaKiwiWannaCryWannaCryptWannaCryptorWannakeyWCrypt
(Read more...)
|
Wannacry | |||
| 2017-05-19 19:36:05 | Gallery: 10 major organizations affected by the WannaCry ransomware attack (lien direct) | The WannaCry ransomware attack of the past week has been brutal, and while it has been temporarily stopped experts say it will probably come back. Here's a list of some of the biggest victims so far. | Wannacry | |||
| 2017-05-19 19:25:27 | North Korea Denies Role in Global Cyberattack (lien direct) | North Korea on Friday angrily dismissed reports linking its isolated regime to the global cyberattack that held thousands of computers to virtual ransom. Up to 300,000 computers in 150 countries were hit by the WannaCry worm, which seizes systems and demands payment in Bitcoin to return control to users. | Wannacry | |||
| 2017-05-19 19:17:05 | Stealth Backdoor Abused NSA Exploit Before WannaCrypt (lien direct) | In the aftermath the WannaCry ransomware outbreak, security researchers discovered numerous attacks that have been abusing the same EternalBlue exploit for malware delivery over the past several weeks. | Wannacry | |||
| 2017-05-19 19:00:00 | Diversity in Recent Mac Malware (lien direct) |
In recent weeks, there have been some high-profile reports about Mac malware, most notably OSX/Dok and OSX.Proton.B. Dok malware made headlines due to its unique ability to intercept all web traffic, while Proton.B gained fame when attackers replaced legitimate versions of HandBrake with an infected version on the vendor’s download site. Another lower profile piece of Mac malware making the rounds is Mac.Backdoor.Systemd.1.
Figure 1: Systemd pretending to be corrupted and un-runnable.
 There have been no public reports as to who is behind these attacks and only little information about their targets. OSX/Dok is reported to have targeted European victims, while users of HandBrake were the victims of Proton.B. One corporate victim of Proton.B was Panic, Inc. which had its source code stolen and received a ransom demand from the attackers.
Each of these malware variants is designed to take advantage of Macs, but analysis shows that they are actually drastically different from each other, showing just how diverse the Mac malware space has grown. Let’s dive into some of the technical details (but not too technical ;) of each piece of malware to learn more about what they do and how they work.
OSX/Dok
OSX.Proton.B
Mac.BackDoor.System.1
Functionality
HTTP(S) proxy
Credential theft (potentially other RAT functionality)
Backdoor/RAT
Language
Objective-C (with heavy use of shell commands)
Objective-C (with heavy use of shell commands)
C++ (with a handful of shell commands)
Persistence
Launch Agent
Launch Agent
Launch Agent
Launch Daemon
Startup Item
Uses chflags to make files read-only
Distribution
Phishing emails
Compromised software download
(presumably) Phishing
Anti-Analysis
None
Anti-debugger (PT_DENY_ATTACH)
Closes Terminal and Wireshark Windows
None
Binary Obfuscation
Newer variants are packed with UPX
Password protected zip archive
Encrypted configuration file
Encrypted configuration file
XOR encrypted strings in binary
Detection Avoidance
Signed App bundle
Installs trusted root certificate
Modifies sudo settings to prevent prompting
Checks for security software
Infected legitimate software
Use of “hidden” dot files
Uses chflags to hide files from UI
Use of “hidden” dot files
C2
MiTM proxy (no separate C2)
HTTPS
Custom 3DES
Functionality
Dok is very basic in its functionality – it reconfigures a system to proxy web traffic through a malicious h
There have been no public reports as to who is behind these attacks and only little information about their targets. OSX/Dok is reported to have targeted European victims, while users of HandBrake were the victims of Proton.B. One corporate victim of Proton.B was Panic, Inc. which had its source code stolen and received a ransom demand from the attackers.
Each of these malware variants is designed to take advantage of Macs, but analysis shows that they are actually drastically different from each other, showing just how diverse the Mac malware space has grown. Let’s dive into some of the technical details (but not too technical ;) of each piece of malware to learn more about what they do and how they work.
OSX/Dok
OSX.Proton.B
Mac.BackDoor.System.1
Functionality
HTTP(S) proxy
Credential theft (potentially other RAT functionality)
Backdoor/RAT
Language
Objective-C (with heavy use of shell commands)
Objective-C (with heavy use of shell commands)
C++ (with a handful of shell commands)
Persistence
Launch Agent
Launch Agent
Launch Agent
Launch Daemon
Startup Item
Uses chflags to make files read-only
Distribution
Phishing emails
Compromised software download
(presumably) Phishing
Anti-Analysis
None
Anti-debugger (PT_DENY_ATTACH)
Closes Terminal and Wireshark Windows
None
Binary Obfuscation
Newer variants are packed with UPX
Password protected zip archive
Encrypted configuration file
Encrypted configuration file
XOR encrypted strings in binary
Detection Avoidance
Signed App bundle
Installs trusted root certificate
Modifies sudo settings to prevent prompting
Checks for security software
Infected legitimate software
Use of “hidden” dot files
Uses chflags to hide files from UI
Use of “hidden” dot files
C2
MiTM proxy (no separate C2)
HTTPS
Custom 3DES
Functionality
Dok is very basic in its functionality – it reconfigures a system to proxy web traffic through a malicious h |
Wannacry APT 32 | |||
| 2017-05-19 18:55:42 | The WannaCry Missing: Federal Systems, Consumers (lien direct) | In-brief: One week after the WannaCry ransomware knocked out hospitals in the UK and subway fare systems in Germany, the malware is as notable for who it didn’t affect for who it did. Among those spared WannaCry’s wrath:Â federal IT systems in the U.S. as well as consumers. But why? The WannaCry ransomware that began spreading a week...Read the whole entry... _!fbztxtlnk!_ https://feeds.feedblitz.com/~/326538366/0/thesecurityledger -->»Related StoriesReport: UK Hospitals among Victims of Massive Ransomware AttackWannaCry: What's in a name? Confusion | Digital GuardianFatal Flaw Slows WannaCry Ransomware Spread, but Threats Remain | Wannacry | |||
| 2017-05-19 18:30:11 | New SMB Worm Uses Seven NSA Hacking Tools. WannaCry Used Just Two (lien direct) | Researchers have detected a new worm that is spreading via SMB, but unlike the worm component of the WannaCry ransomware, this one is using seven NSA tools instead of two. [...] | Wannacry | |||
| 2017-05-19 17:17:21 | WannaCry Does Not Fit North Korea\'s Style, Interests: Experts (lien direct) | Some experts believe that, despite malware code similarities, the WannaCry ransomware is unlikely to be the work of North Korea, as the attack does not fit the country's style and interests. | Wannacry | |||
| 2017-05-19 17:05:33 | Hackers Are Trying to Reignite WannaCry With Nonstop Botnet Attacks (lien direct) |  The "sinkhole" domain that's held the ransomware in check is coming under repeated denial-of-service attacks. The post Hackers Are Trying to Reignite WannaCry With Nonstop Botnet Attacks The "sinkhole" domain that's held the ransomware in check is coming under repeated denial-of-service attacks. The post Hackers Are Trying to Reignite WannaCry With Nonstop Botnet Attacks |
Wannacry | |||
| 2017-05-19 17:04:27 | Available Tools Making Dent in WannaCry Encryption (lien direct) | Tools are beginning to emerge that can be used to begin the process of recovering files encrypted by WannaCry on some Windows systems. | Wannacry | |||
| 2017-05-19 16:03:11 | Video: How a cyberweapon developed by the NSA infected machines around the world (lien direct) | Protonmail CEO Andy Yen explains how government backdoors and zero day exploits made the British hospital system, SMBs, and enterprise organizations vulnerable to the WannaCry exploit. | Wannacry | |||
| 2017-05-19 15:47:21 | WannaCry: could something similar happen to Android? (lien direct) | If WannaCry blazed through Windows machines like wildfire, how safe are Android devices from ransomware? |
Wannacry | |||
| 2017-05-19 14:15:13 | WannaCry: The Definitive Litmus Test For Taking Security Seriously (lien direct) | The ISBuzz Post: This Post WannaCry: The Definitive Litmus Test For Taking Security Seriously | Wannacry | |||
| 2017-05-19 14:00:45 | How did the WannaCry Ransomworm spread? (lien direct) |
 Security researchers have had a busy week since the WannaCry ransomware outbreak that wreaked havoc on computers worldwide. How did it all happen?
Categories:
Cybercrime
Exploits
Malware
Tags: botnetDoublePulsarEternalBlueexploitJaff ransomwaremalspammalwareNecurs botnetNSAransomwareShadowBrokersspamWannaCryWannaCrypt
(Read more...)
Security researchers have had a busy week since the WannaCry ransomware outbreak that wreaked havoc on computers worldwide. How did it all happen?
Categories:
Cybercrime
Exploits
Malware
Tags: botnetDoublePulsarEternalBlueexploitJaff ransomwaremalspammalwareNecurs botnetNSAransomwareShadowBrokersspamWannaCryWannaCrypt
(Read more...)
|
Wannacry | |||
| 2017-05-19 13:00:19 | Threatpost News Wrap, May 19, 2017 (lien direct) | Mike Mimoso and Chris Brook discuss WannaCry, Microsoft's response, the killswitches, a potential link with Lazarus Group, and what the future holds for the ShadowBrokers. | Medical | Wannacry APT 38 | ||
| 2017-05-19 13:00:00 | Alien Eye in the Sky 18th May, 2017 (lien direct) |
 WannaCry
We should start by addressing the elephant in the room. In the past week WannaCry has dominated the news and still looks to be the topic on the tips of everyone’s tongues.
There’s probably not much to add without repeating much of what has already been said.
A Twitter moment capturing much of the early and subsequent commentary on WannaCry
Making sense of WannaCry
Ongoing WannaCry vulnerability spreading through SMB vulnerability
Microsoft: TechNet's Coverage?
SOCs are maturing, but need more automation
According to a new SANS survey, it appears as if security operation centres (SOCs) are getting better.
The survey indicates that SOCs need more automation, particularly for prevention and detection.
There are two sides to automation. One part is to understand the workflows that are needed, in other words what is the playbook to follow once certain events occur. The second part is around having technology that is tightly integrated so that the automation can occur across the IT stack. Neglecting one at the cost of the other can greatly reduce effectiveness.
Building a SOC on a budget
Practitioners guide to a SOC
Data keeps getting stolen
Getting media attention when there’s a data breach is a great thing. However, some days it feels as if fatigue has set in and breaches are reported and shoulders are shrugged as if it was a normal an occurrence as the bus being late.
Despite growing regulation, and better technologies, companies seem to repeat the same errors repeatedly, resulting in huge data losses.
Such as the case of a hacker that stole millions of users accounts from education platform Edmodo, which includes usernames, email addresses, and password hashes.
But even that pales in comparison to where breaches can affect entire countries. With reports of Indian biometric system data being leaked that could impact over 130m people.
GDPR
Before WannaCry hijacked all security conversations this past week, GDPR has remained a popular topic. While it is good to see awareness of the upcoming regulation, it also invites a lot of uninformed commentary. Many claims are made about the implications, and frankly hijacking the conversation to suit an InfoSec and technology narrative.
GDPR rubbish
Artificial Intelligence
AI continues to be touted and discussed wide and far, with many potentially interesting security applications.
Apple acquired a data mining and machine learning company called Lattice.io at an estimated c
WannaCry
We should start by addressing the elephant in the room. In the past week WannaCry has dominated the news and still looks to be the topic on the tips of everyone’s tongues.
There’s probably not much to add without repeating much of what has already been said.
A Twitter moment capturing much of the early and subsequent commentary on WannaCry
Making sense of WannaCry
Ongoing WannaCry vulnerability spreading through SMB vulnerability
Microsoft: TechNet's Coverage?
SOCs are maturing, but need more automation
According to a new SANS survey, it appears as if security operation centres (SOCs) are getting better.
The survey indicates that SOCs need more automation, particularly for prevention and detection.
There are two sides to automation. One part is to understand the workflows that are needed, in other words what is the playbook to follow once certain events occur. The second part is around having technology that is tightly integrated so that the automation can occur across the IT stack. Neglecting one at the cost of the other can greatly reduce effectiveness.
Building a SOC on a budget
Practitioners guide to a SOC
Data keeps getting stolen
Getting media attention when there’s a data breach is a great thing. However, some days it feels as if fatigue has set in and breaches are reported and shoulders are shrugged as if it was a normal an occurrence as the bus being late.
Despite growing regulation, and better technologies, companies seem to repeat the same errors repeatedly, resulting in huge data losses.
Such as the case of a hacker that stole millions of users accounts from education platform Edmodo, which includes usernames, email addresses, and password hashes.
But even that pales in comparison to where breaches can affect entire countries. With reports of Indian biometric system data being leaked that could impact over 130m people.
GDPR
Before WannaCry hijacked all security conversations this past week, GDPR has remained a popular topic. While it is good to see awareness of the upcoming regulation, it also invites a lot of uninformed commentary. Many claims are made about the implications, and frankly hijacking the conversation to suit an InfoSec and technology narrative.
GDPR rubbish
Artificial Intelligence
AI continues to be touted and discussed wide and far, with many potentially interesting security applications.
Apple acquired a data mining and machine learning company called Lattice.io at an estimated c |
Wannacry | |||
| 2017-05-19 11:51:34 | WannaCry – Un outil de déchiffrement a été développé pour aider les victimes (lien direct) |  Si vous faites partie des nombreuses victimes du ransomware WannaCry et que votre PC a été infecté, sachez que vous avez désormais une chance de récupérer vos fichiers verrouillés sans payer la rançon de 300 dollars aux cybercriminels. Si vous faites partie des nombreuses victimes du ransomware WannaCry et que votre PC a été infecté, sachez que vous avez désormais une chance de récupérer vos fichiers verrouillés sans payer la rançon de 300 dollars aux cybercriminels. |
Wannacry | |||
| 2017-05-19 11:32:00 | Researcher Creates Tool to Unlock WannaCry-Infected Windows XP Files (lien direct) | A security researcher appears to have discovered a flaw in WannaCry that may provide Windows XP victims of the attack with a way to unlock their files. | Wannacry | |||
| 2017-05-19 10:44:39 | McAfee researchers test WannaCry recovery method (lien direct) | Although there is evidence that some victims of the WannaCry ransomware attack on 12 May have paid the attackers, there is no evidence that they are getting their data back | Wannacry | |||
| 2017-05-19 09:57:24 | ValueLicensing reduces the cost of the war on cybercrime (lien direct) | Worried about the WannaCry virus? Don’t let the cost of upgrading your online security reduce you to tears, says ValueLicensing Cyberattacks and data breaches are two of the greatest concerns for modern businesses – but making sure your business has access to greater security needn’t cost the earth, according to one expert. The WannaCry ransomware ... | Wannacry | |||
| 2017-05-19 09:29:56 | Medical Devices Infected With WannaCry Ransomware (lien direct) | 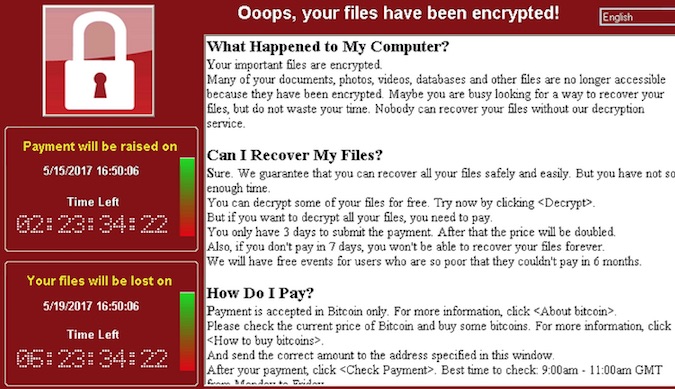
|
Wannacry | |||
| 2017-05-19 07:45:02 | Les autorités françaises réquisitionnent des nÅ“uds Tor liés au ransomware WannaCrypt (lien direct) |  Durant ces derniers jours, l'Office Central de Lutte contre la Criminalité liée aux Technologies de l'Information et de la Communication (OCLCTIC) a saisi pas moins de 3 serveurs servant de relais Tor ayant été en relation avec le cyberattaque WannaCry. Durant ces derniers jours, l'Office Central de Lutte contre la Criminalité liée aux Technologies de l'Information et de la Communication (OCLCTIC) a saisi pas moins de 3 serveurs servant de relais Tor ayant été en relation avec le cyberattaque WannaCry. |
Wannacry | |||
| 2017-05-19 06:52:09 | Weekly update 35 (lien direct) | Sponsored by: Netsparker - Scan your websites & detect SQL Injection, XSS and other vulnerabilities with the dead accurate Netsparker web security scannerHang on - where did my week go?! WannaCry came out of the blue and accosted a big whack of my time starting first thing Saturday. And then, just as it was quietening down, I go and write about not turning off Windows Update and holy shit, did people come | Wannacry | |||
| 2017-05-19 05:59:39 | More Hacking Groups Found Exploiting SMB Flaw Weeks Before WannaCry (lien direct) | Since the Shadow Brokers released the zero-day software vulnerabilities and hacking tools – allegedly belonged to the NSA's elite hacking team Equation Group – several hacking groups and individual hackers have started using them in their own way.
The April's data dump was believed to be the most damaging release by the Shadow Brokers till the date, as it publicly leaked lots of Windows
|
Wannacry | |||
| 2017-05-19 05:13:35 | Detecting WannaCry Ransomware (lien direct) | The ISBuzz Post: This Post Detecting WannaCry Ransomware | Wannacry | |||
| 2017-05-19 04:49:03 | Neustar launches international security council (lien direct) | Sharing information in the face of threats such as WannaCry is crucial for organisations to improve their cyber security capability, according to Neustar, which is making it easier to do | Wannacry | |||
| 2017-05-19 04:15:11 | WannaCry Ransomware Infects Actual Medical Devices, Not Just Computers (lien direct) | Reports have surfaced that the WannaCry ransomware has infected actual medical devices, not just computers at medical facilities. [...] | Wannacry | |||
| 2017-05-19 01:44:14 | WannaCry Ransomware Decryption Tool Released; Unlock Files Without Paying Ransom (lien direct) | If your PC has been infected by WannaCry – the ransomware that wreaked havoc across the world last Friday – you might be lucky to get your locked files back without paying the ransom of $300 to the cyber criminals.
Adrien Guinet, a French security researcher from Quarkslab, has discovered a way to retrieve the secret encryption keys used by the WannaCry ransomware for free, which works on
|
Wannacry |
To see everything:
Our RSS (filtrered)
